To route traffic through Microservices Engine (MSE) Ingress gateways in your Kubernetes cluster, grant the required Resource Access Management (RAM) permissions to MSE Ingress Controller. The permission method depends on your cluster type.
Prerequisites
Before you begin, make sure that you have:
An Alibaba Cloud account with RAM administrative privileges
A Container Service for Kubernetes cluster (ACK managed, ACK Serverless, ACK dedicated, or ACS)
Permission methods by cluster type
| Cluster type | Scenario | Permission method |
|---|---|---|
| ACK managed or ACK Serverless | Existing cluster | Install from the Add-ons page |
| ACK managed or ACK Serverless | New cluster | Authorize during cluster creation |
| ACK dedicated | Existing cluster | Attach the AliyunMSEFullAccess policy to the worker RAM role |
| ACS | New cluster | Authorize during cluster creation |
Install MSE Ingress Controller from the Add-ons page
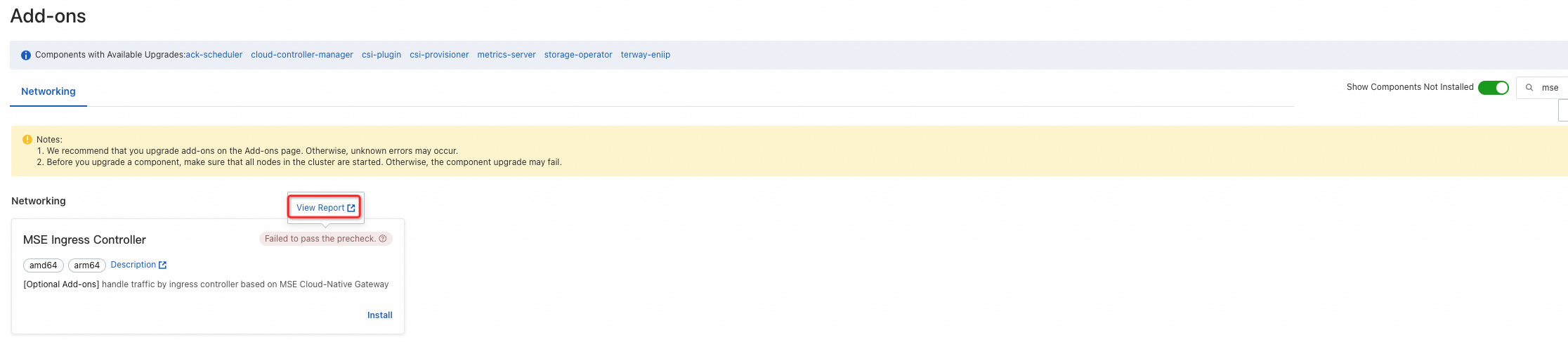
Use this method for an existing ACK managed or ACK Serverless cluster. When you install MSE Ingress Controller on the Add-ons page, permission verification runs automatically. If "Failed to pass the precheck." appears, complete the following steps:
Hover over "Failed to pass the precheck." and click View Report.
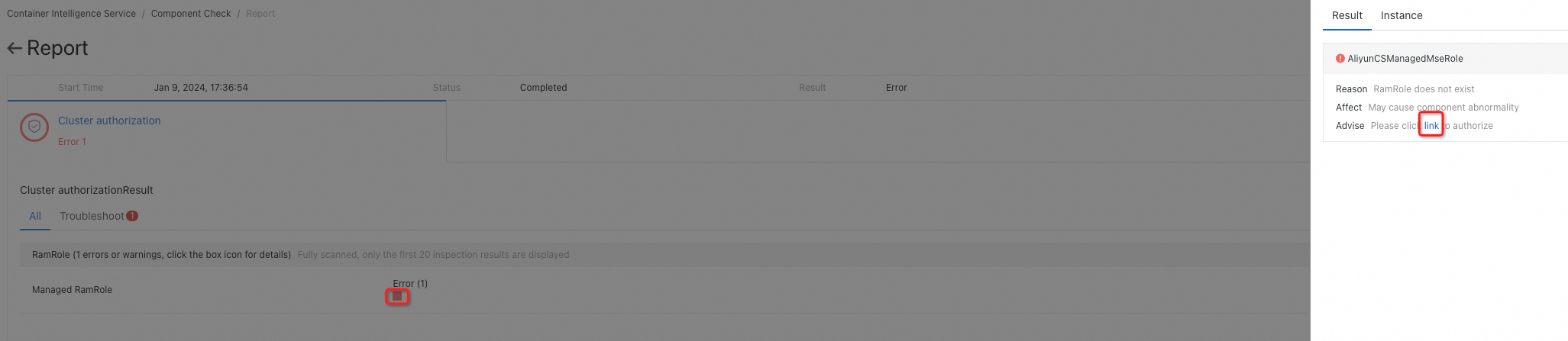
On the Report page, click the red box in the Error column. In the panel that appears, click the authorization link.
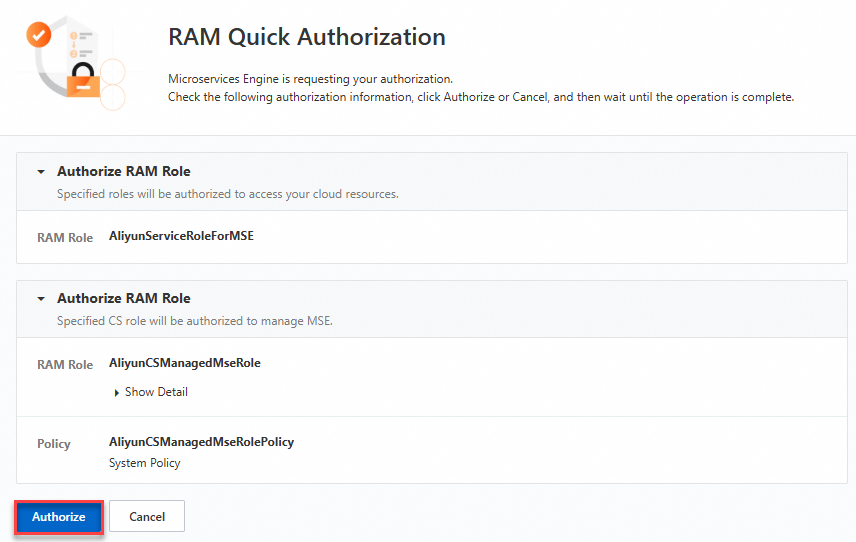
On the RAM Quick Authorization page, click Authorize.
Return to the Add-ons page and reinstall MSE Ingress Controller.
Authorize during ACK managed or ACK Serverless cluster creation
Use this method when you select MSE Ingress Controller while creating a new ACK managed or ACK Serverless cluster.
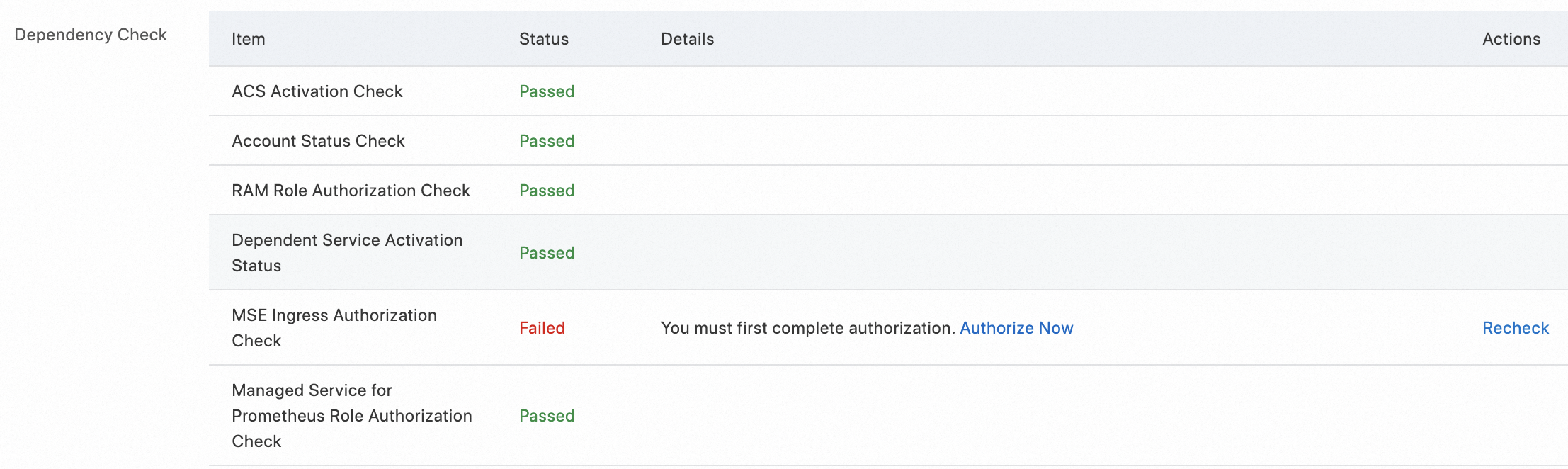
In the Confirm Order step, check the status of MSE Ingress Authorization Check in the Dependency Check section. If the status is Failed, click Authorize Now.
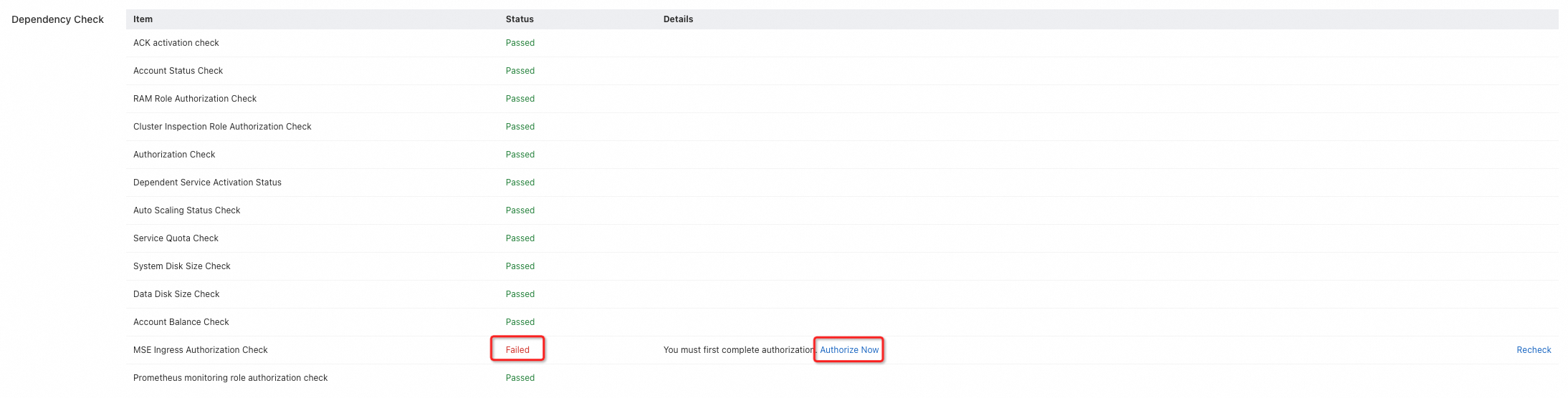
On the RAM Quick Authorization page, click Authorize.
Return to the Confirm Order step and click Re-check. After the check passes, click Create Cluster.
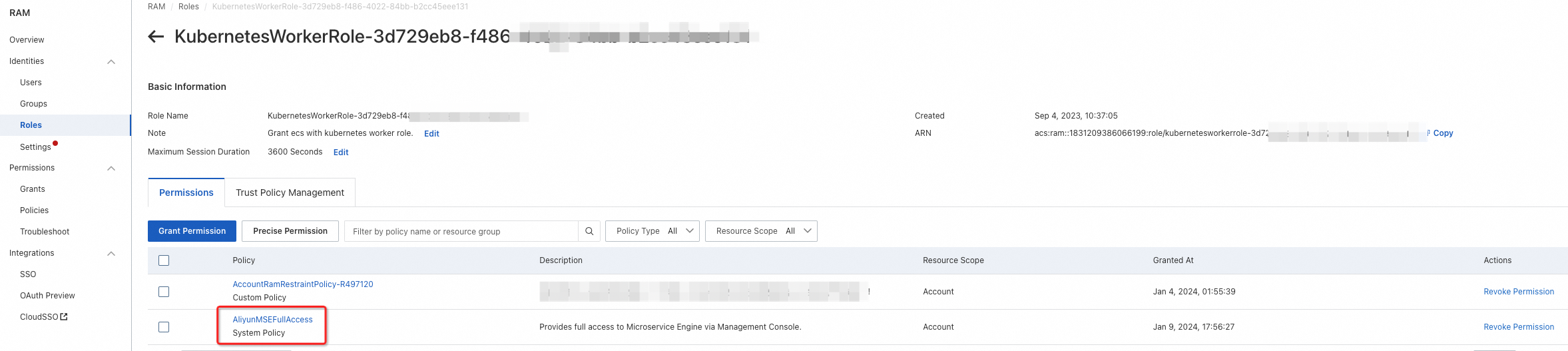
Attach the AliyunMSEFullAccess policy in an ACK dedicated cluster
ACK dedicated clusters use a worker RAM role for node-level permissions. To grant MSE Ingress Controller access, attach the AliyunMSEFullAccess system policy to this role, then redeploy the controller.
Step 1: Attach the policy
Log on to the ACK console.
In the left-side navigation pane, click Clusters, then click the name of the target cluster.
On the Cluster Information page, click the Basic Information tab. In the Cluster Resources section, click the hyperlink next to Worker RAM Role.
On the Permissions tab of the RAM role page, click Grant Permission.
In the Policy section, select System Policy from the policy type drop-down list and search for
AliyunMSEFullAccess.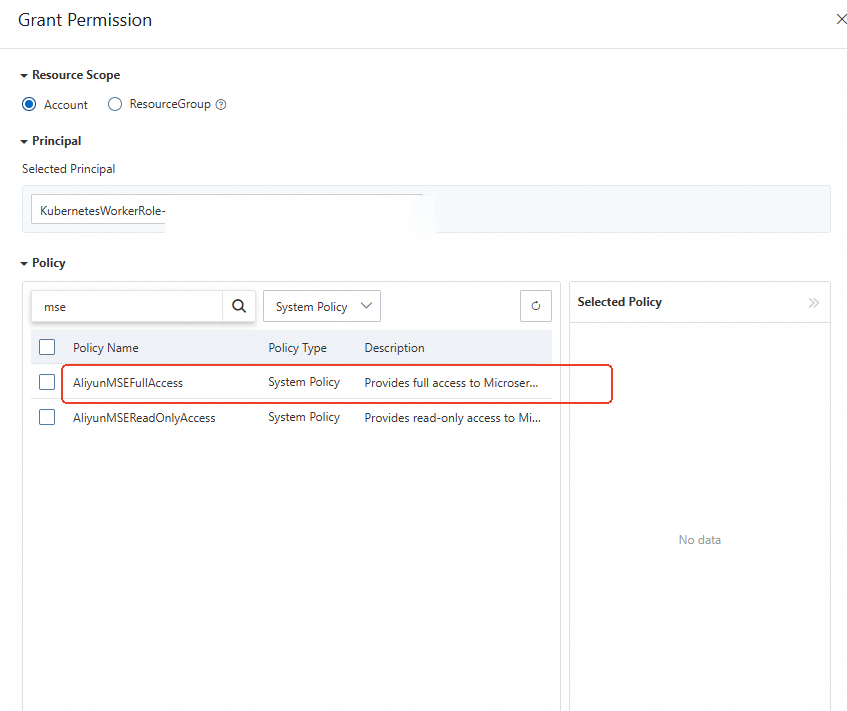
Select AliyunMSEFullAccess, add it to the Selected Policy list, and click Grant permissions.
After the policy is attached, verify that AliyunMSEFullAccess appears in the policy list.
Step 2: Redeploy MSE Ingress Controller
In the cluster, locate the ack-mse-ingress-controller application in the mse-ingress-controller namespace.
In the Actions column, click the menu icon (
 ) and select Redeploy. Click OK to confirm.
) and select Redeploy. Click OK to confirm.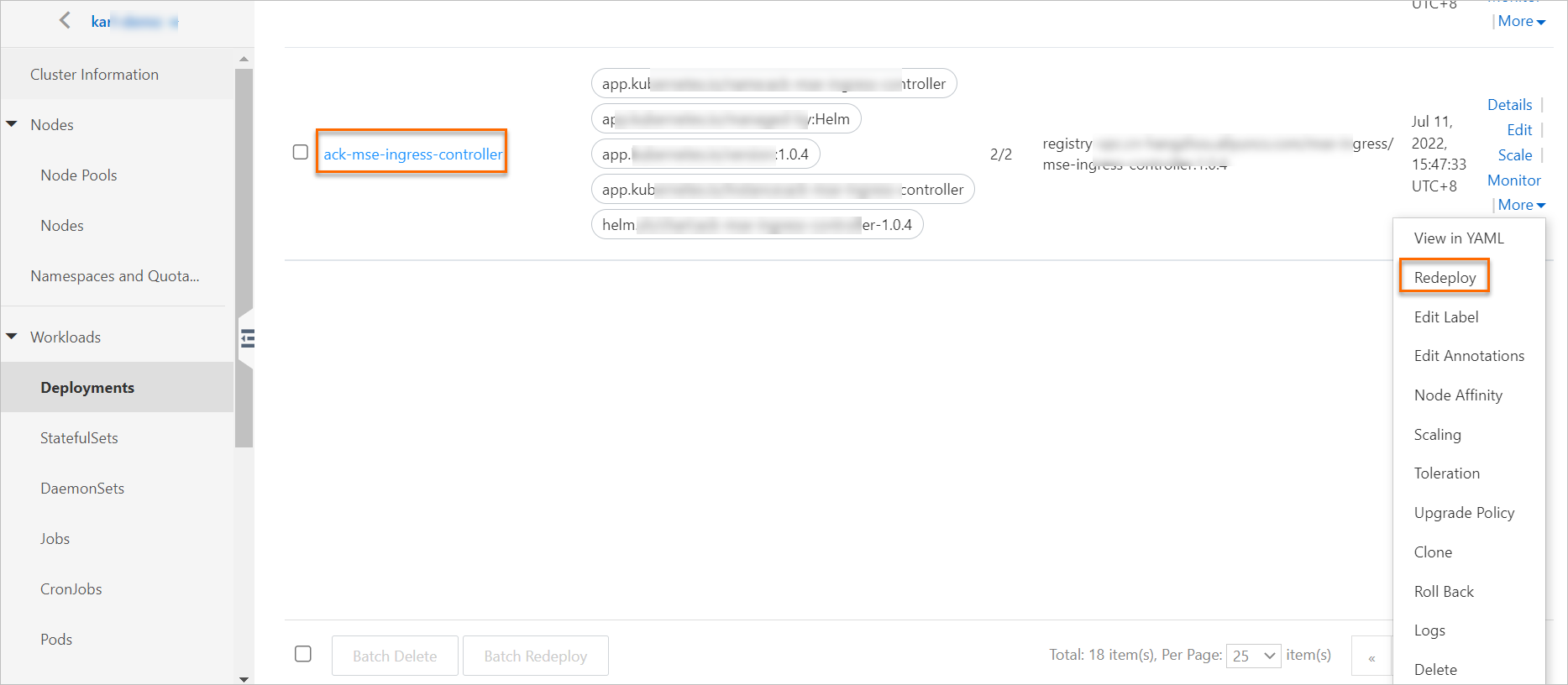
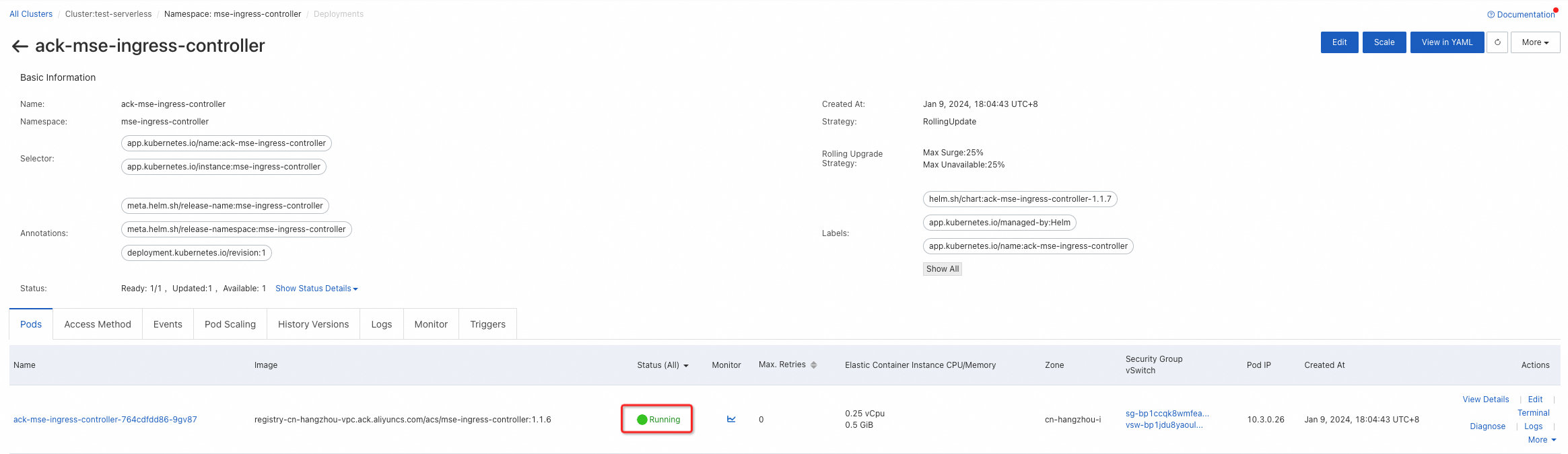
After the redeployment completes, click ack-mse-ingress-controller and confirm that the pod status is Running.
(Optional) Grant Simple Log Service permissions
To activate Simple Log Service for the MSE cloud-native gateway through an MseIngressConfig resource, grant additional Simple Log Service permissions to the worker RAM role.
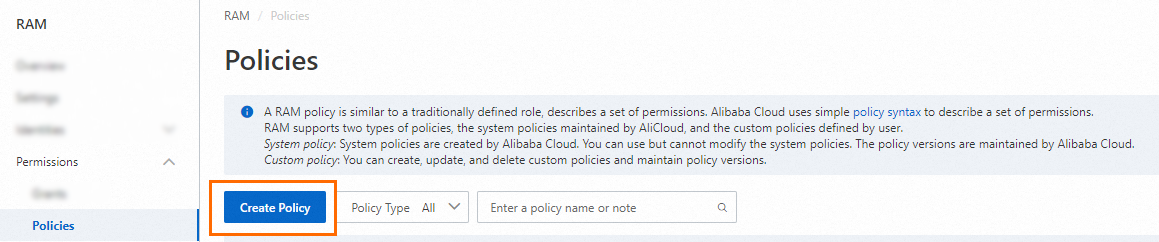
Create a custom policy for Simple Log Service
Log on to the RAM console as a RAM user with administrative privileges.
In the left-side navigation pane, choose Permissions > Policies.
On the Policies page, click Create Policy.
Click the JSON tab and enter the following policy content:
{ "Version": "1", "Statement": [ { "Action": [ "log:CloseProductDataCollection", "log:OpenProductDataCollection", "log:GetProductDataCollection" ], "Resource": [ "acs:mse:*:*:instance/*", "acs:log:*:*:project/*/logstore/mse_*" ], "Effect": "Allow" }, { "Action": "ram:PassRole", "Resource": "acs:ram::*:role/aliyunserviceroleforslsaudit", "Effect": "Allow" }, { "Action": "ram:CreateServiceLinkedRole", "Resource": "*", "Effect": "Allow", "Condition": { "StringEquals": { "ram:ServiceName": "audit.log.aliyuncs.com" } } } ] }Click OK, then specify a Policy Name and Description in the dialog box. Click OK to save the policy.
Attach the custom policy to the worker RAM role
Log on to the ACK console.
In the left-side navigation pane, click Clusters, then click the name of the target cluster.
On the Cluster Information page, click the Basic Information tab. In the Cluster Resources section, click the hyperlink next to Worker RAM Role.
On the Permissions tab, click Grant Permission.
In the Policy section, select Custom Policy from the policy type drop-down list and search for the policy name you specified in the previous section.
NoteThe policy name is the custom name you defined when creating the policy.
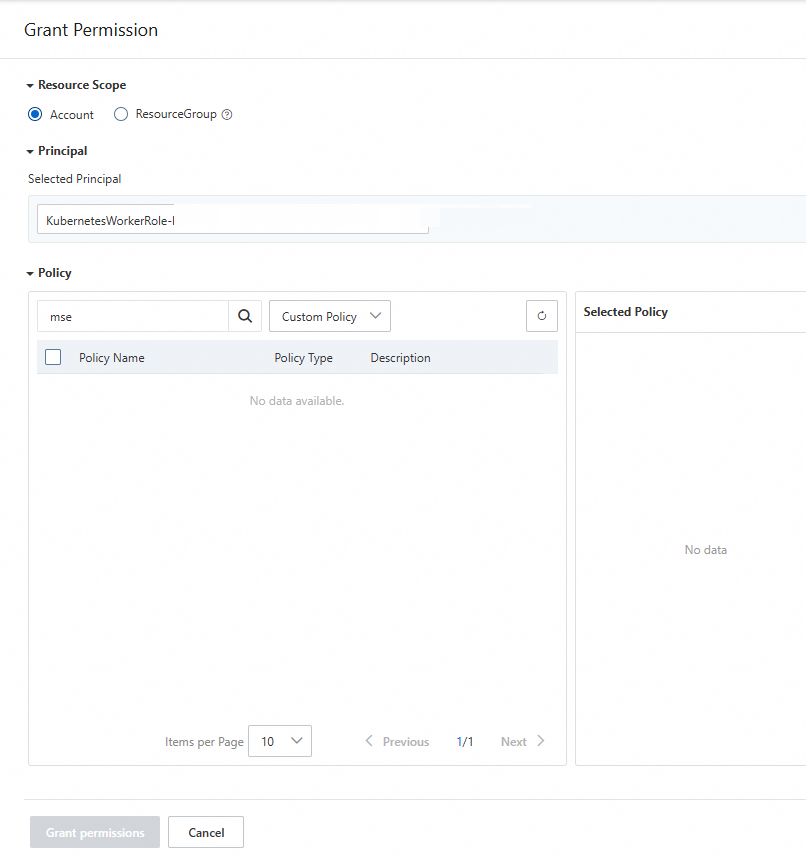
Select the policy, add it to the Selected Policy list, and click Grant permissions.
Authorize during ACS cluster creation
Grant permissions to MSE Ingress Controller when you create an ACS cluster.
In the Confirm Order step, check the status of MSE Ingress Authorization Check in the Dependency Check section. If the status is Failed, click Authorize Now.
On the RAM Quick Authorization page, click Authorize.
Return to the Confirm Order step and click Re-check. After the check passes, click Create Cluster.
What to do next
Set up traffic routing for your cluster. See Use MSE Ingress gateways to access services in ACK clusters and ACS clusters.