Use this solution to access services in a virtual private cloud (VPC)—such as ApsaraDB RDS, HBase clusters, and Hadoop clusters—from MaxCompute jobs. Supported access methods include MaxCompute SQL, user-defined functions (UDFs), Spark, PyODPS/Mars, foreign tables, and data lakehouse architectures.
This solution automatically creates two security groups for return traffic: MaxCompute-vpc-xxx and MaxCompute-backup-vpc-xxx, where xxx is the VPC ID you provide. Do not modify the rules of these security groups or use them to manage security rules for other components. The platform is not responsible for issues caused by such modifications.
Prerequisites
Before you begin, ensure that you have:
A MaxCompute project. For data lakehouse use cases, set the data type edition to the Hive-compatible data type edition.
A single Alibaba Cloud account that owns the VPC, has access to the MaxCompute project, and administers the target service. All three roles must belong to the same account.
Who needs to be involved:
This procedure spans multiple systems and may require coordination across teams:
MaxCompute project administrator: grants permissions and creates the network connection in the MaxCompute console.
VPC/ECS console administrator: creates and configures the security group.
Target service administrator (ApsaraDB RDS, HBase, or Hadoop): configures access rules on the target service.
Limitations
The security group you create for this connection must be a Basic Security Group. Advanced Security Groups deny outbound traffic by default, which prevents MaxCompute from reaching services in your VPC.
After MaxCompute creates its Elastic Network Interface (ENI) IP addresses, those addresses may change if the MaxCompute configuration is modified. To avoid connectivity disruptions, add the CIDR block of the vSwitch rather than individual ENI IP addresses to any service whitelists.
Do not modify or repurpose the two auto-created security groups (
MaxCompute-vpc-xxxandMaxCompute-backup-vpc-xxx).
Step 1: Grant permissions
Grant the operating user permission to create network connection objects.
The user performing the authorization must be a Project Owner, or hold the tenant-level Super_Administrator or Admin role. For role details, see Role planning. For the authorization procedure, see List of object permissions in a tenant.
Authorize MaxCompute to create ENIs in your VPC.
This authorization lets MaxCompute establish network connectivity by creating Elastic Network Interfaces (ENIs) in your VPC. While logged in to your Alibaba Cloud account, click Authorize.
Step 2: Create a security group for MaxCompute
Create a dedicated Basic Security Group in your VPC. MaxCompute places its ENIs in this group to access services inside the VPC. During connection creation, MaxCompute automatically creates two ENIs based on bandwidth requirements. These ENIs are free of charge.
Set the outbound rules for this security group to control the destination addresses that MaxCompute jobs, which run on ENIs, can access. If you have no special requirements, you can keep the default outbound rules.
All inbound traffic to the ENI is return traffic, so allow all inbound traffic.
Log on to the Virtual Private Cloud (VPC) console.
In the left navigation pane, choose VPC. In the upper-left corner, select a region.
On the VPC page, click the Instance ID/Name of the target VPC.
On the VPC details page, click the Resource Management tab.
In the VPC Resources section, hover over the Security Group value and click Add. For more information, see Create a security group.
Set Security Group Type to Basic Security Group. > Note: A Basic Security Group allows outbound traffic by default. An Advanced Security Group denies outbound traffic by default and cannot be used here.
For Network, select the same VPC used by the connectivity service.
Configure security group rules to allow MaxCompute access. For more information, see Security group application guide and examples.
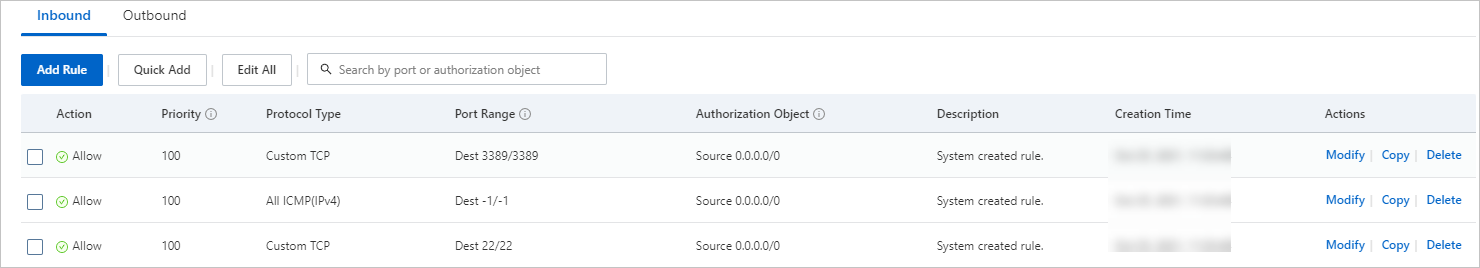
In the Operation column for the new security group, click Manage Rules.
On the Inbound tab in the Access Rules area, click Edit for the target rule and set the following:
Field Value Action Allow Priority 1 Protocol All Traffic Source CIDR block of the VPC or vSwitch containing the target service Destination (Current Instance) ALL(-1/-1)
(HBase only) If HBase does not support adding security groups and only supports IP-based access: log on to the ECS console, and click Elastic Compute Service in the left navigation pane to get the ENI IP address. Because ENI IP addresses can change, add the CIDR block of the vSwitch instead.
Step 3: Create a network connection
An Alibaba Cloud account, or a RAM user with the tenant-level Super_Administrator or Admin role, can create a network connection. For more information, see MaxCompute tenant-level roles.
Log on to the MaxCompute console and select a region in the upper-left corner.
In the left navigation pane, choose Manage Configurations > Network Connection.
On the Network Connection page, click Add Network Connection.
In the Add Network Connection dialog box, configure the parameters and click OK.
ImportantThe first time you add a network connection, you must first grant authorization to allow MaxCompute to request network interface cards. Without this authorization, the connection cannot be created.
Parameter Required Description Connection Name Required A custom name for the connection. Type Required Defaults to Passthrough. Region Required Auto-populated based on the region selected in the upper-left corner. VPC Selected Required The VPC that contains the target service. To create a new VPC, see Create or delete a VPC. Switch Required The vSwitch (subnet) within the VPC. Deploy resources across vSwitches in different zones to protect against single-zone failures. To create a vSwitch, see Create or delete a vSwitch. Security group Required The Basic Security Group you created in Step 2. This group controls which resources MaxCompute's ENIs can reach and which ports can be accessed.
Step 4: Configure access rules on the target service
After the network connection is established, add inbound rules to the target service's security group to allow traffic from the MaxCompute security group (the one created in Step 2). If the target service only supports IP-based access rather than security groups, add the CIDR block of the vSwitch.
Hadoop cluster
Add inbound rules to the Hadoop cluster's security group with the security group created in Step 2 as the authorization object. Open the following ports:
| Component | Port |
|---|---|
| Hive Metastore | 9083 |
| HDFS NameNode | 8020 |
| HDFS DataNode | 50010 |
For example, when connecting to a Hadoop cluster on Alibaba Cloud E-MapReduce, the required security group rules look like this:
For more information, see Create a security group.
HBase cluster
Add the MaxCompute security group or its ENI IP address to the HBase cluster's security group or IP address whitelist.
For an Alibaba Cloud HBase cluster:
Log on to the HBase Management Console and select a region.
In the left navigation pane, click Clusters.
Click the name of the target cluster.
In the left navigation pane, click Access Control.
On the Whitelist Setting and Security Group tabs, click Add Whitelist or Add Security Group. If adding a security group is not supported, add the ENI IP address of MaxCompute on the Whitelist Setting tab. Because ENI IP addresses may change, we recommend that you add the CIDR block of the vSwitch to the whitelist instead.
For more information, see Set whitelists and security groups.
ApsaraDB RDS
Add the MaxCompute security group or its ENI IP address to the RDS security group or IP address whitelist.
For an ApsaraDB RDS instance:
Log on to the RDS console.
In the left navigation pane, click Instances and select a region.
Click Whitelist and SecGroup in the left navigation pane.
On the Whitelist Settings and Security Group tabs, add the vSwitch CIDR block or the MaxCompute security group.
For more information, see Set a security group or Set an IP address whitelist.
Step 5: Access VPC resources from your jobs
SQL and UDFs
Set the network connection per session:
-- Applies to the current session only
SET odps.session.networklink=testLink;For UDF-based access, see Access VPC network resources using a UDF.
For foreign tables, specify the connection in the CREATE TABLE statement:
TBLPROPERTIES('networklink'='<networklink_name>')For data lakehouse access, see Data Lakehouse 2.0 user guide.
Spark
Add the following configuration to your Spark job. For details, see Spark accessing VPC-connected instances.
spark.hadoop.odps.cupid.eni.enable = true
spark.hadoop.odps.cupid.eni.info=regionid:vpc id(Optional) Step 6: Add a server whitelist
If access control is enabled on your server, add the security group created in Step 2 to the server's whitelist.