When expanding businesses globally, enterprises often face threats such as network latency and DDoS attacks. By deploying Global Accelerator (GA) with Anti-DDoS protection products, you can accelerate global user access and effectively defend against DDoS attacks. This ensures high availability and security for your services, improves the user experience, and reduces security risks.
Introduction to GA and DDoS protection products
A DDoS attack is a malicious network attack that targets a system to make its services unavailable. You can select one of the following DDoS protection products based on your security protection requirements:
Protection product | |||
Mitigation capabilities | Low GA is integrated with Alibaba Cloud DDoS protection. You do not need to enable it. It provides up to 5 Gbps of basic DDoS protection for the accelerated IP addresses and public IP addresses of endpoints of GA instances free of charge. The maximum free mitigation capability varies by region. | High Anti-DDoS Origin lets you add GA instances as protected objects. It provides unlimited protection of up to several hundred Gbps for the accelerated IP addresses and public IP addresses of endpoints of GA instances. The maximum mitigation capability varies by region. | High GA can be connected to Anti-DDoS Pro and Anti-DDoS Premium. Based on the capabilities of Alibaba Cloud's global scrubbing centers, it provides mitigation capabilities of up to several Tbps for the secure CNAME (secure accelerated IP address) of the GA instance. |
How it works | Anti-DDoS Basic uses a default scrubbing threshold, which you can also set manually. When traffic meets the conditions for scrubbing, Anti-DDoS Basic filters and scrubs all inbound traffic from the Internet to defend against common network-layer and transport-layer attacks, such as UDP reflection attacks and SYN/ACK Flood attacks. However, Anti-DDoS Basic does not defend against application-layer attacks, such as HTTP Flood attacks and CC attacks. In addition to the BPS and PPS scrubbing thresholds that you configure, Anti-DDoS Basic uses AI-based intelligent analysis. By leveraging the big data capabilities of Alibaba Cloud, Anti-DDoS Basic learns your traffic patterns and uses algorithms to detect attacks. Traffic scrubbing is triggered only when the AI-based intelligent analysis detects a DDoS attack and the inbound traffic reaches the BPS or PPS threshold that you set. This method prevents false positives that can be caused by fixed thresholds, for example, when normal service traffic fluctuations exceed the scrubbing threshold. If inbound traffic exceeds the mitigation capability (the blackhole triggering threshold), the cloud product is subject to blackhole filtering. This prevents DDoS attacks from causing further damage to the cloud product or affecting other assets. Blackhole filtering means that Alibaba Cloud temporarily blocks all inbound traffic from the Internet to the cloud product. For more information, see Blackhole filtering policy of Alibaba Cloud. | Anti-DDoS Origin primarily mitigates Layer 3 and Layer 4 DDoS attacks. When traffic exceeds the default scrubbing threshold, Anti-DDoS Origin automatically triggers traffic scrubbing to mitigate DDoS attacks. Anti-DDoS Origin uses passive scrubbing as its primary mitigation method and active blocking as a supplementary method. It uses standard technologies such as reverse detection, blacklists and whitelists, and packet compliance to mitigate DDoS attacks. This ensures that your protected cloud service can continue to operate normally during an attack. Anti-DDoS Origin works by deploying a DDoS attack detection and traffic scrubbing system at the egress of an Alibaba Cloud data center. This system is deployed in bypass mode. | Based on the forwarding rule that you configure for your service in Anti-DDoS Pro and Anti-DDoS Premium (that is, specify the website domain name and use the secure CNAME of GA as the server address), GA redirects traffic by pointing the DNS domain name resolution or service IP address of the service to the IP address of the Anti-DDoS Pro or Anti-DDoS Premium instance.
|
References |
Use cases
Connect GA to Anti-DDoS Origin
A company's website is deployed on Alibaba Cloud in the US (Silicon Valley) region and serves end users in multiple regions worldwide through a custom domain name. The forwarding port is HTTP port 80. The website currently faces the following issues:
Unstable cross-border public networks that often experience issues such as latency, jitter, and packet loss.
Frequent high-volume DDoS attacks that lead to unstable service responses.
You can solve the problems that are faced by cross-domain website services by deploying GA with Anti-DDoS Origin.
GA: Client access requests can connect to the Alibaba Cloud acceleration network from the nearest acceleration area. GA uses smart routing and automatic network scheduling to forward requests to the origin server in the US (Silicon Valley) region, which effectively improves service access speed. Additionally, you can enable health checks to enhance business reliability and availability and prevent abnormal nodes from affecting the service.
Anti-DDoS Origin: Anti-DDoS Origin lets you add GA instances as protected objects to protect the accelerated IP addresses and public IP addresses of GA endpoints. When traffic exceeds the default scrubbing threshold of Anti-DDoS Origin, traffic scrubbing is automatically triggered to mitigate DDoS attacks.

Limits
Anti-DDoS Origin is available for direct purchase only in the Chinese mainland. To purchase an instance in a region outside the Chinese mainland, contact your account manager for assistance. For more information about how to contact your account manager, see Contact us.
Prerequisites
Your services are deployed on ECS01 and ECS02 servers in the US (Silicon Valley) region. This topic uses Alibaba Cloud Linux 3 as an example and configures an HTTP 80 service using Nginx.
You have configured a DNS record for your custom domain name. You have configured an A record to point the domain name to the public IP addresses of the two backend servers.
If you use a DNS service other than Alibaba Cloud DNS, see your DNS provider's instructions.
To provide services over HTTPS 443, you must create and apply for a certificate or upload a third-party certificate to the SSL Certificate service and bind it to your custom domain name.
You have purchased an Anti-DDoS Origin instance.
Procedure
Step 1: Configure Global Accelerator
This topic uses a pay-as-you-go standard GA instance as an example.
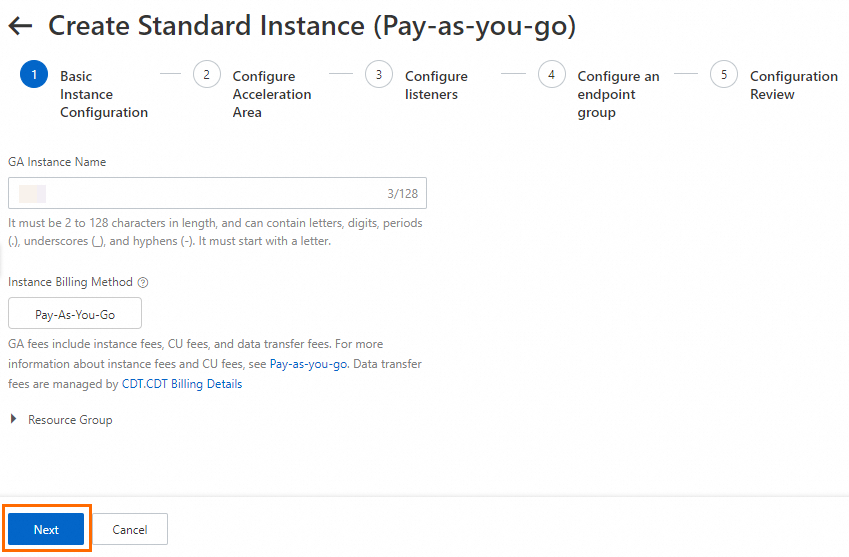
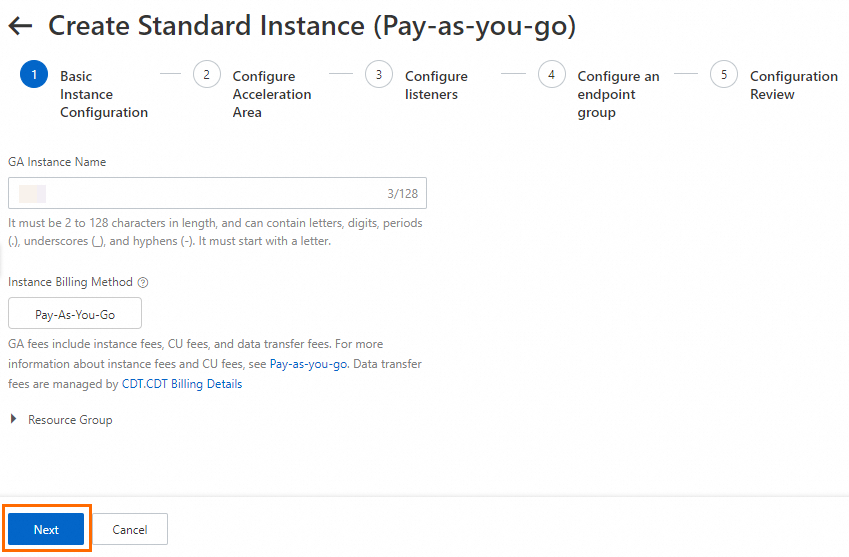
On the page of the GA console, click Create Standard Pay-as-you-go Instance.
In the Basic Instance Configuration step, configure the basic information and click Next.
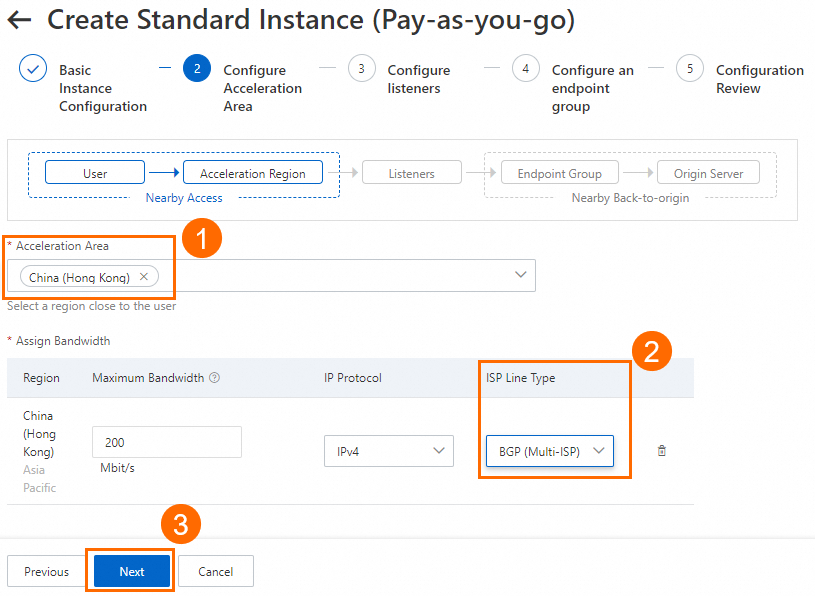
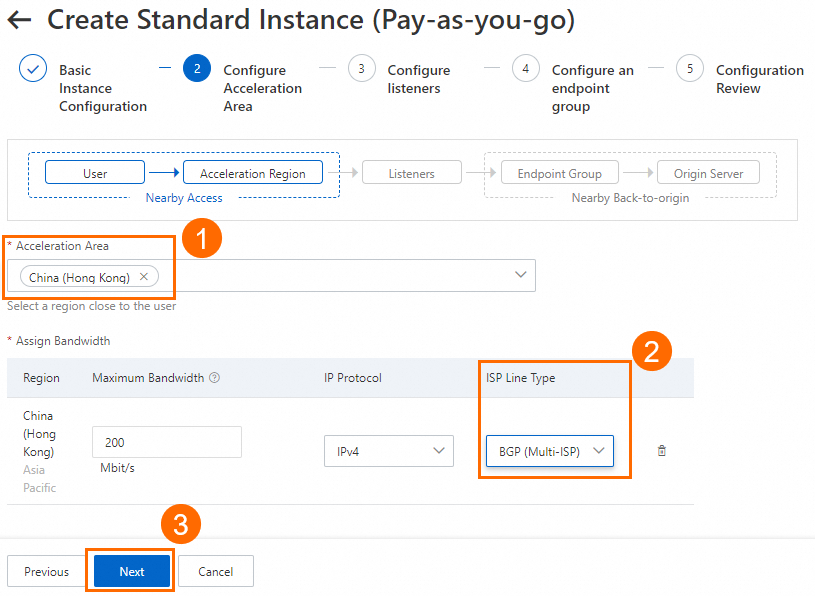
In the Configure Acceleration Area step, add an acceleration region, allocate bandwidth to the region, and then click Next.
In this example, the Acceleration Region parameter is set to China (Hong Kong), and the ISP Line Type parameter is set to BGP (Multi-ISP). You can use the default values for other parameters or modify the parameters based on your business requirements. For more information, see Add and manage acceleration areas.
ImportantIf the acceleration regions include regions in the Chinese mainland, you must apply for an ICP number for the domain name to provide services.
If you specify a small value for the maximum bandwidth, throttling may occur and packets may be dropped. Specify a maximum bandwidth based on your business requirements.
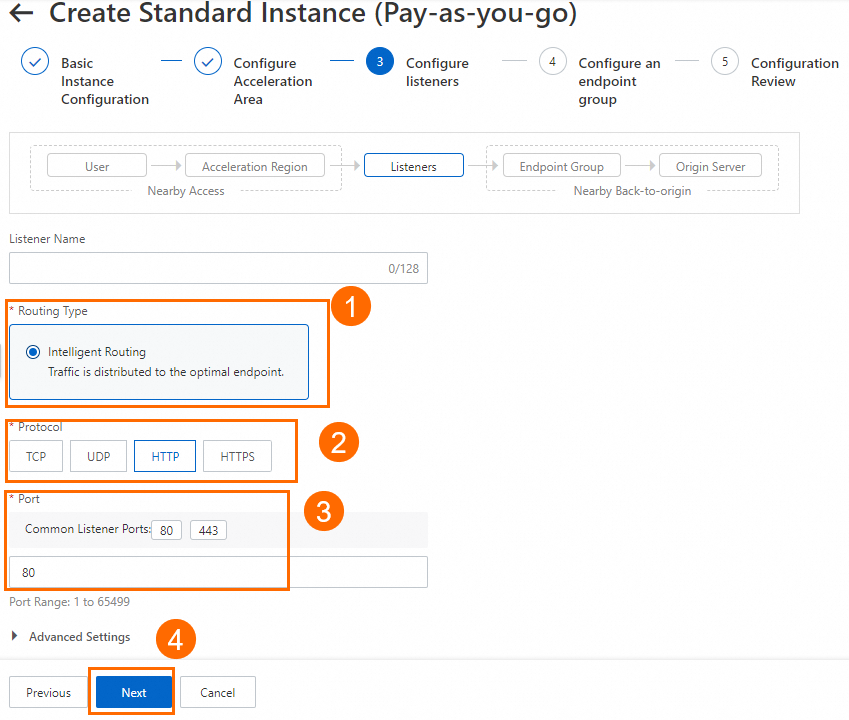
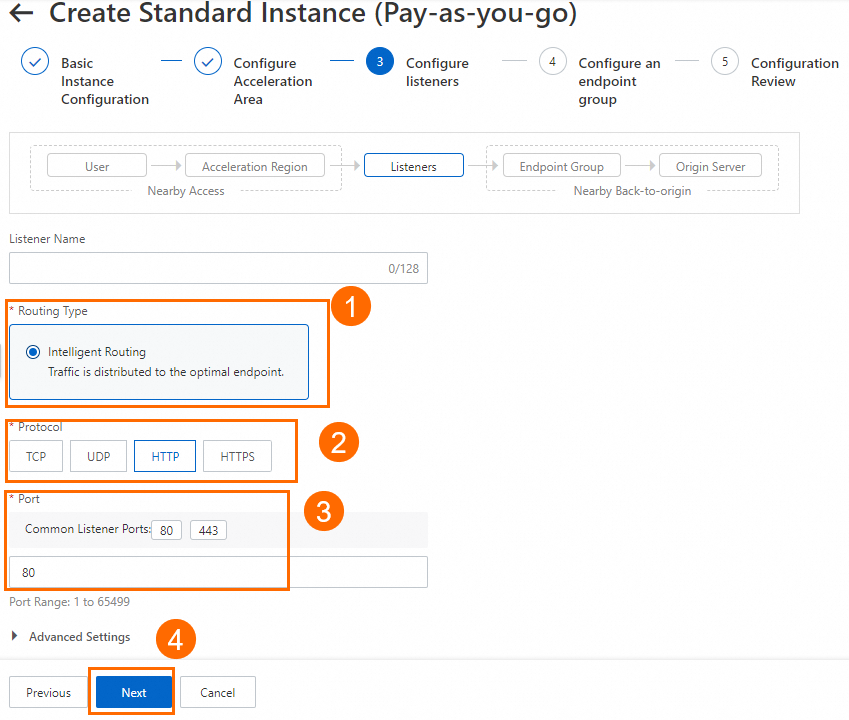
In the Configure listeners step, configure the forwarding protocol and port, and then click Next.
In this example, the Routing Type parameter is set to Intelligent Routing, the Protocol parameter is set to HTTP, and the Port parameter is set to 80. You can use the default values for other parameters or modify the parameters based on your business requirements. For more information, see Add and manage smart routing listeners.
NoteIf you want to use HTTPS 443 to provide external services, you can select HTTPS for Protocol and 443 for Port, associate the created certificate with the listener, and configure the mapping between listener port 443 and the backend service port 80 in the Port Mapping parameter of the endpoint group. This way, users can securely access the HTTP website over HTTPS.
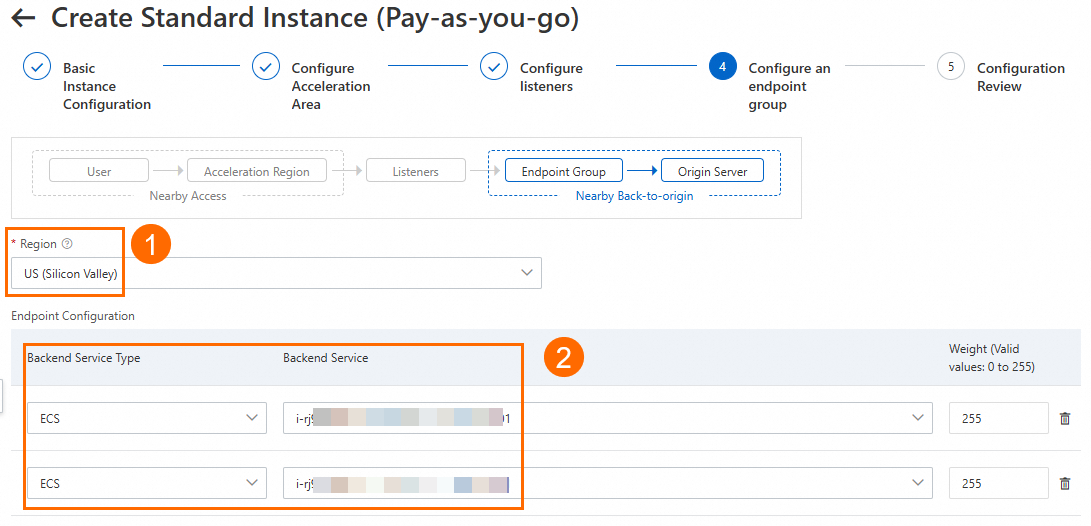
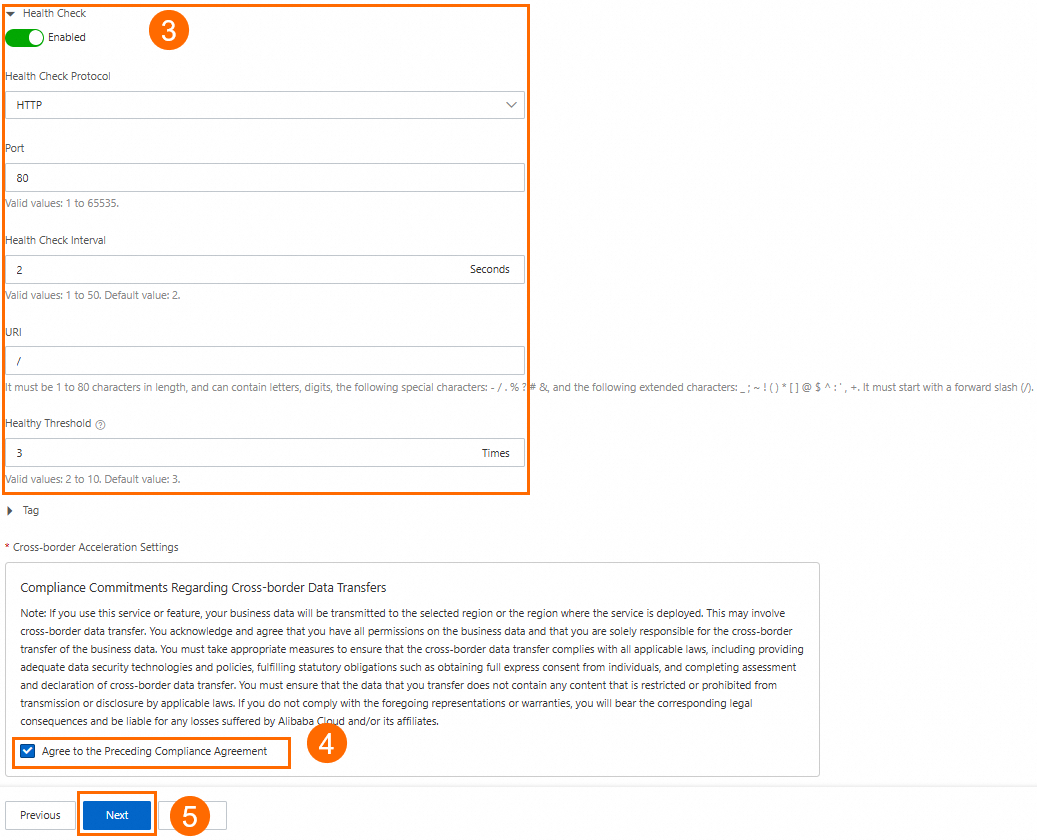
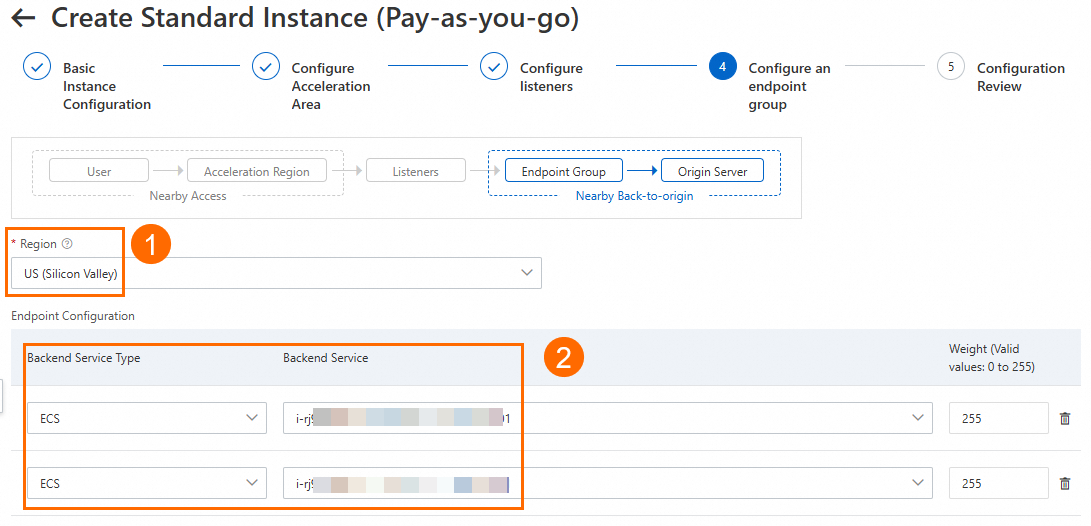
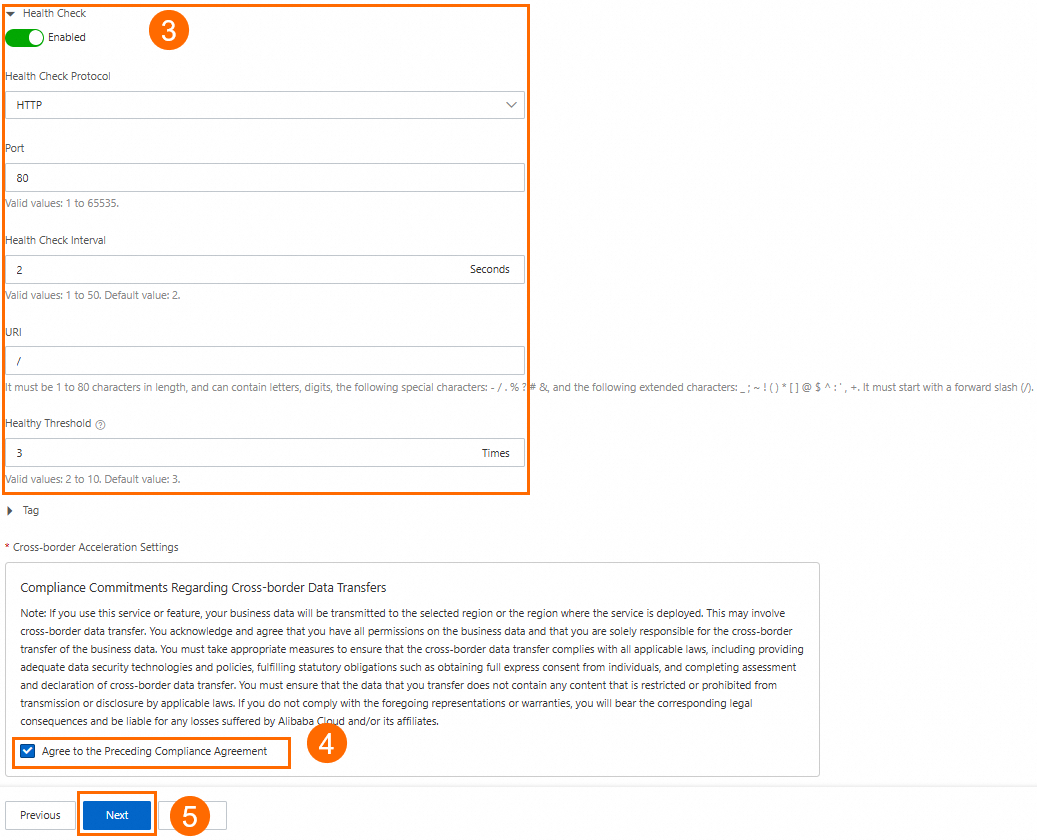
On the Configure Endpoint Group page of the wizard, configure the backend service for the endpoint and click Next.
In this scenario, set the Region to US (Silicon Valley). For Backend Service, configure ECS01 and ECS02 sequentially. Turn on the Health Check switch, then read and select the Cross-border Data Transfer Compliance Commitment. You can keep the default values for other endpoint group parameters or modify them as needed.
In the Configuration Review step, confirm the GA configurations and click Submit.
On the Instances page, find the created GA instance and obtain the CNAME assigned to the GA instance in the CNAME column.
On the backend server, allow the network segment that GA uses to connect to the backend service.
In this scenario, GA connects to the backend ECS servers over a private network. You need to allow its vSwitch CIDR block in the ECS security group and ensure that the number of available private IP addresses in this vSwitch CIDR block is 8 or more.
Step 2: Configure Anti-DDoS Origin
On the Protected Objects page of the Anti-DDoS Origin console, click Add Protected Object to add the GA instance as a protected object.
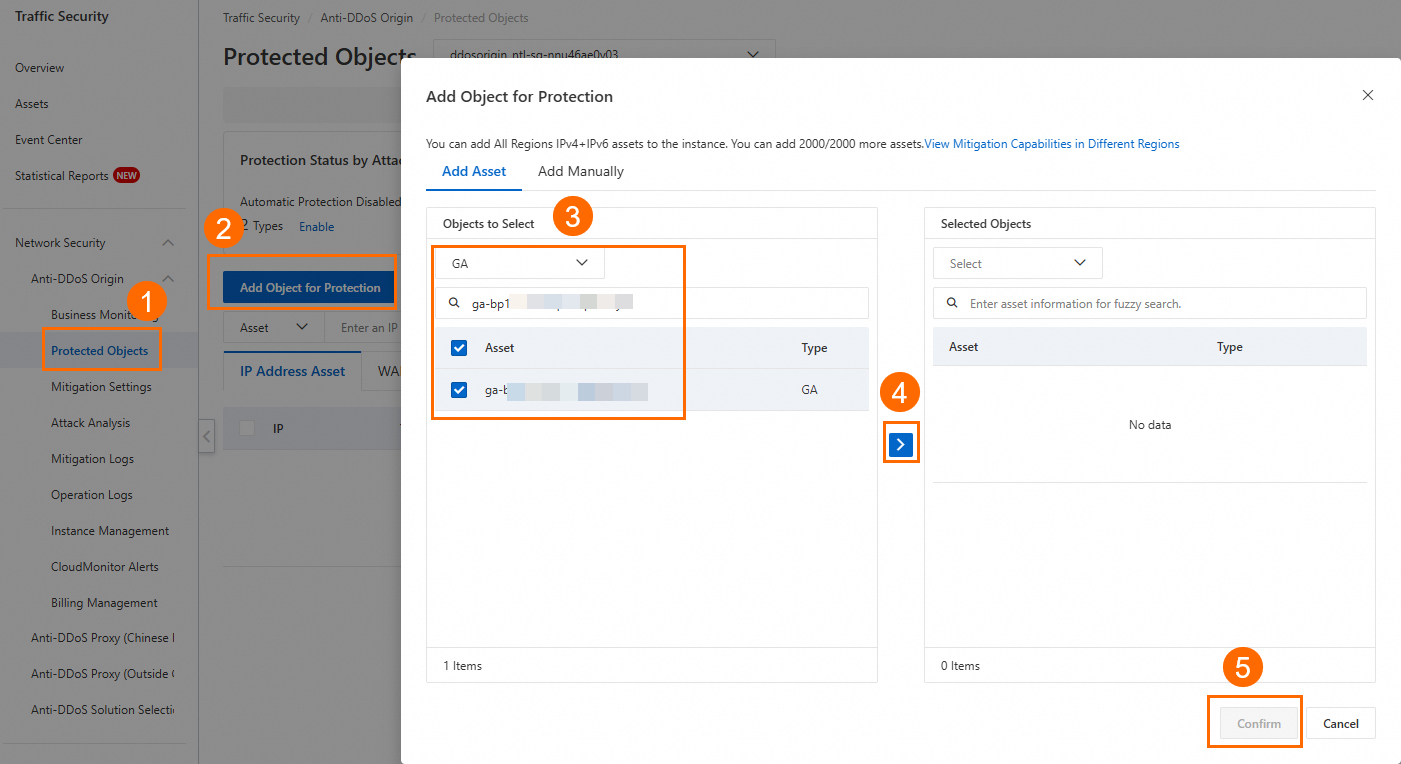
After you add an asset, you can view the protected GA instance on the GA Assets tab of the Protected Objects page. You can also view the protected public IP addresses, including the GA accelerated IP addresses and the public IP addresses of the endpoint group, on the IP Assets tab.
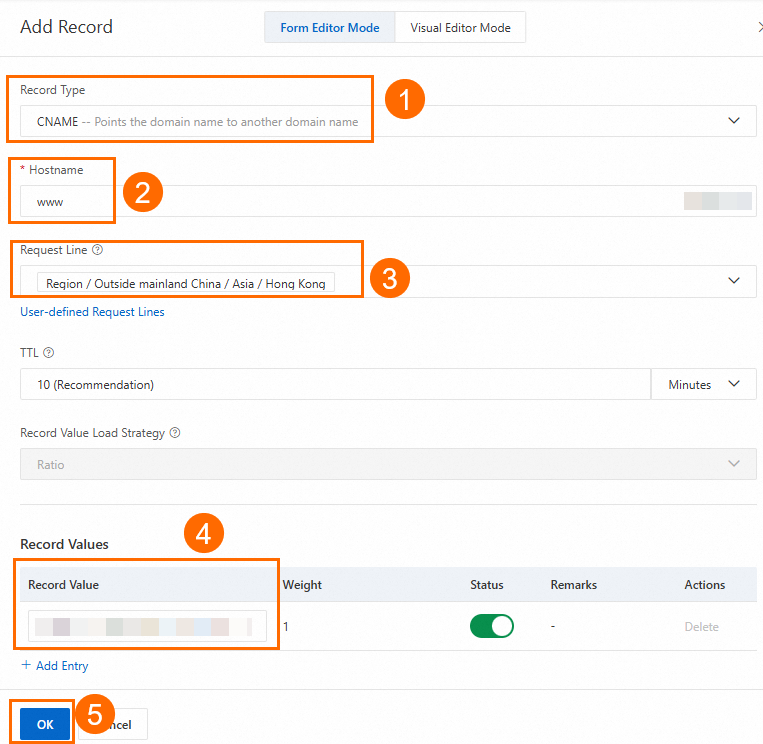
Step 3: Configure a CNAME record
In actual business scenarios, we recommend that you use a custom domain name. You can create a CNAME record to map the custom domain name to the CNAME assigned by GA. This way, business traffic is switched to GA for accelerated access.
In this example, if you already created an A record that points to the backend server, you can specify the China (Hong Kong) region when you add a CNAME record that points to the GA instance. If the CNAME record works as expected, apply the CNAME record to other regions or retain only the CNAME record that points to the GA instance.
On the Authoritative DNS Resolution page, find the domain name that you want to use and click DNS Settings in the Actions column.
NoteFor a domain name that is not registered with Alibaba Cloud, you must add the domain name to the Alibaba Cloud DNS console before you can configure DNS records.
On the DNS Settings page, click Add DNS Record, configure a CNAME record, and then click OK.
In this example, the Record Type parameter is set to CNAME, the Hostname parameter is set to www, the DNS Request Source parameter is set to Asia_Hong Kong, and the Record Value parameter is set to the CNAME of the GA instance. You can use the default values for other parameters or modify the parameters based on your business requirements. For more information, see Add DNS records.
Step 4: Verify the results
Verify the acceleration performance of GA
This topic uses a probe point in Hong Kong (China) as an example. Before and after you configure GA, use a network probe tool to test the custom domain name of the website and check the response time to understand the data latency.
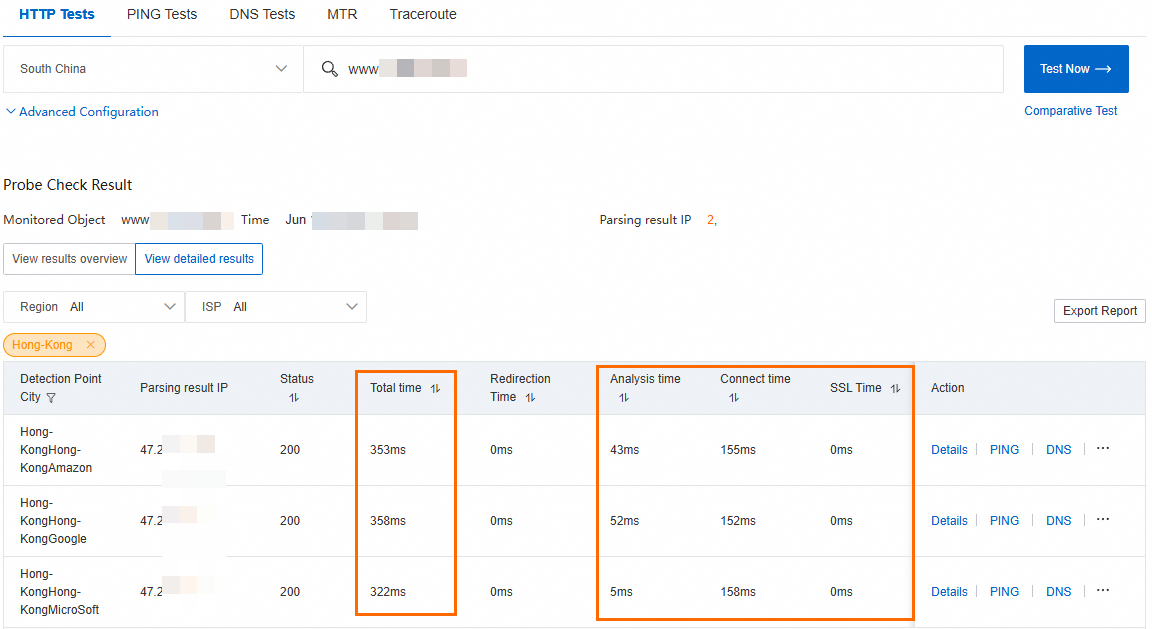
Test the network latency before you configure GA.
You can view information such as the response time. The Resolved IP column shows the public IP address of the ECS instance.
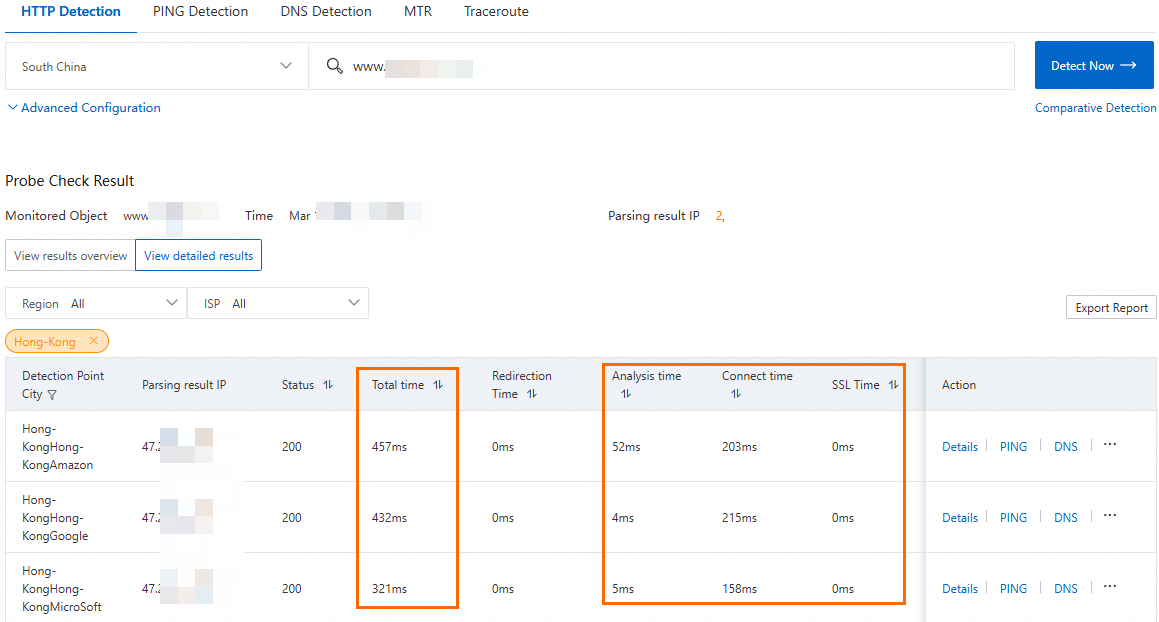
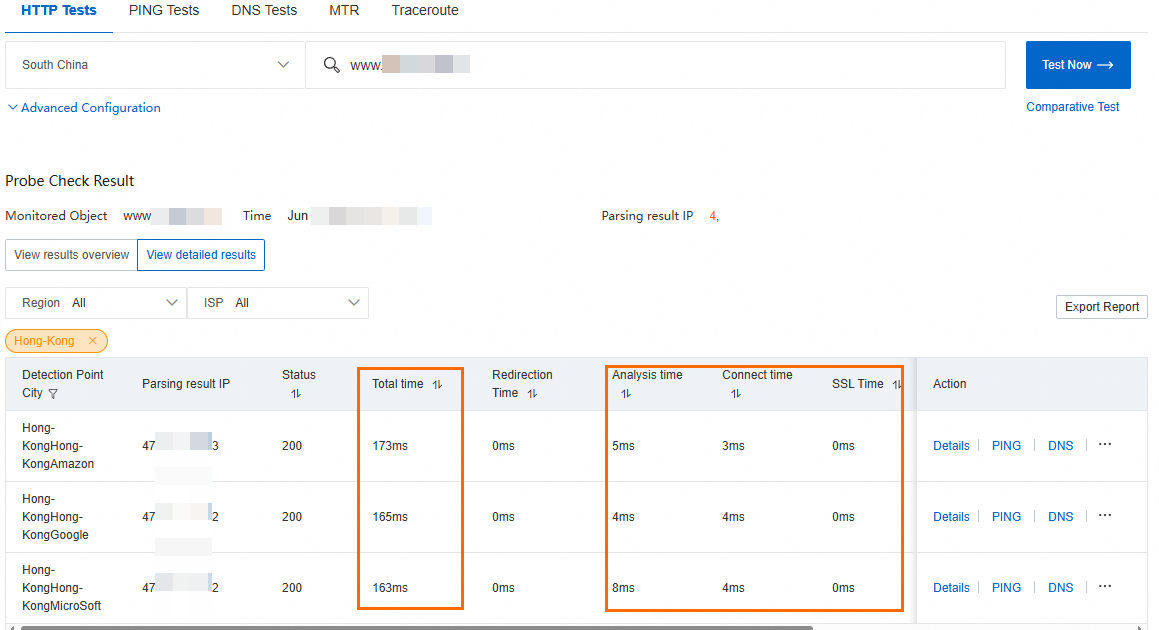
Test the network latency after you configure GA.
You can view information such as the response time. The Resolved IP column shows the accelerated IP address of the GA instance.
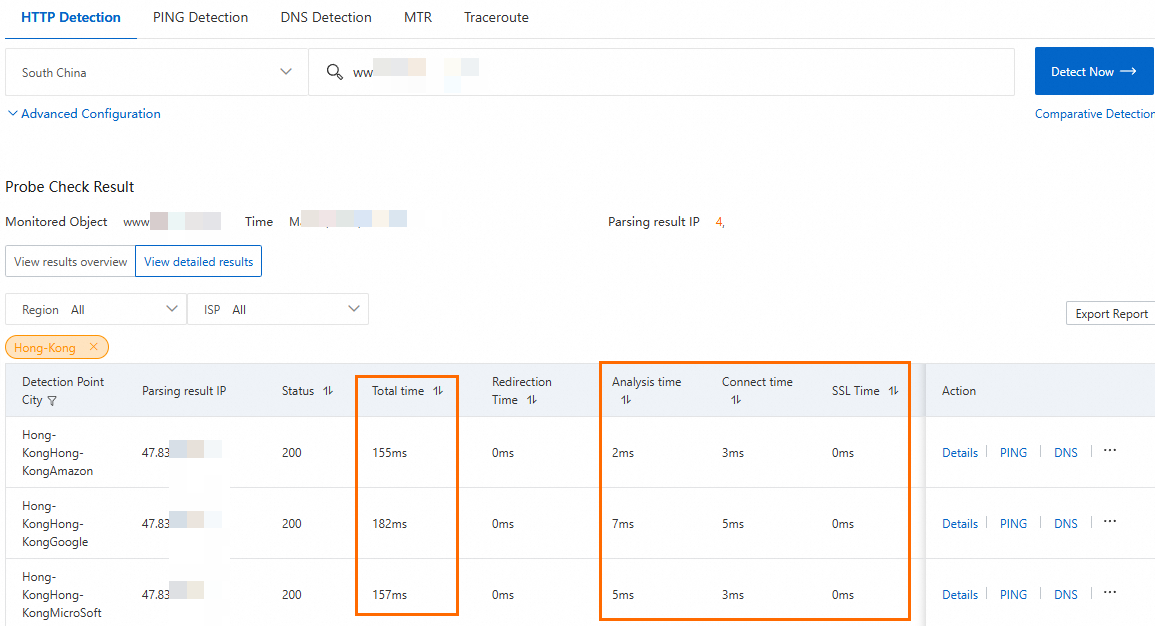
The test result shows that GA reduces the latency for clients in Hong Kong (China) that access services in the US (Silicon Valley) region.
The acceleration performance of GA is subject to the results of your business tests.
Verify the health check feature of GA
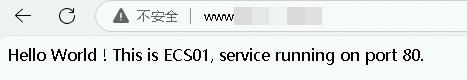
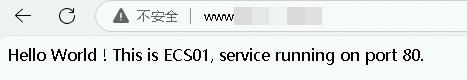
Enter the custom domain name of the website in a browser to access the website that is deployed in the US (Silicon Valley) region.
The test result shows that you can access the website that is deployed in the US (Silicon Valley) region through the custom domain name. After you refresh the browser multiple times, the responding server switches between ECS01 and ECS02.

Simulate a failure: Stop the ECS01 server.
After a while, you can check the Health Check Status on the Endpoint Group tab of the GA instance.
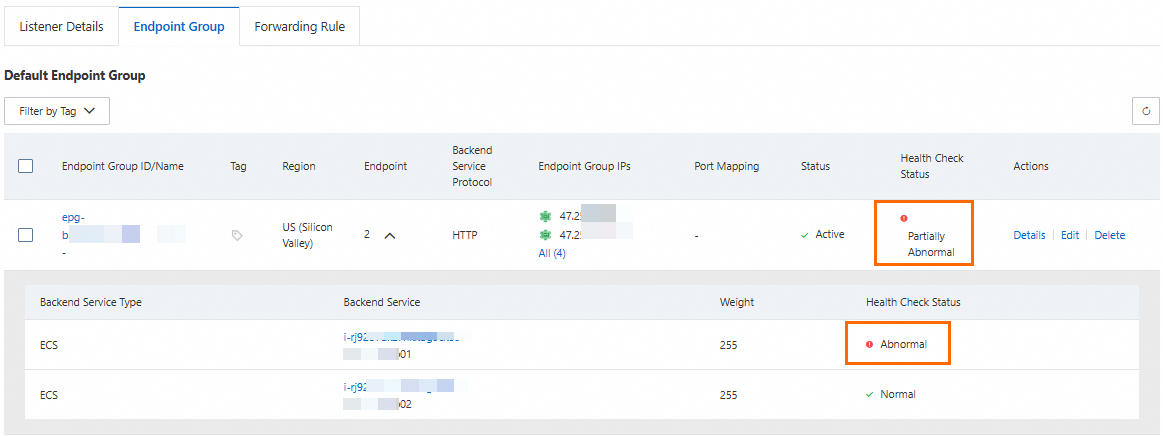
After you refresh the browser multiple times, you can still access the business as normal, but the only responding server is ECS02.

Verify the protection effect of Anti-DDoS Origin
You can use the following features that are provided by Anti-DDoS Origin to check the protection effect.
The Business Monitoring page provides real-time information, such as traffic trends and DDoS attack event records for protected assets.
The Attack Analysis page lets you query and analyze the details of attack events on the Anti-DDoS Origin instance, including the attack type, attack traffic volume, and duration.
The Mitigation Logs page records how Anti-DDoS Origin handles traffic, including detailed information such as attack detection and traffic scrubbing. By analyzing the mitigation logs, you can further verify the effectiveness of the mitigation policies.
Connect GA to Anti-DDoS Pro/Premium
A multinational game is deployed on Alibaba Cloud in the US (Silicon Valley) region and serves players in multiple regions worldwide through a custom domain name. The game currently faces the following issues:
Unstable cross-border public networks that often experience issues such as latency, jitter, and packet loss.
Frequent large-scale DDoS attacks that lead to complete service interruptions.
To solve these problems, the game company plans to deploy GA and connect it to Anti-DDoS Pro and Anti-DDoS Premium:
GA: Client access requests are routed to the nearest Alibaba Cloud acceleration network through a configured acceleration region. The requests are then forwarded to the origin server in the US (Silicon Valley) region using smart routing and automatic network scheduling to effectively improve service access speed. In addition, you can enable health checks to improve the reliability and availability of your services and prevent abnormal nodes from affecting your services.
Anti-DDoS Pro/Premium: After you connect GA to Anti-DDoS Anti-DDoS Pro or Premium, normal traffic is accelerated and sent directly to the origin server through GA without adding latency. During a large-scale DDoS attack, GA uses DNS resolution to reroute traffic to anti-DDoS scrubbing centers for scrubbing. The scrubbed traffic is then accelerated through the secure CNAME (secure accelerated IP address) of GA to the Alibaba Cloud acceleration network and finally forwarded to the server. This ensures stable access to the game server.

Limits
Connecting GA to Anti-DDoS Pro and Anti-DDoS Premium is not available by default. To use this feature, contact your business manager.
To purchase the Premium Edition of Anti-DDoS Pro and Anti-DDoS Premium (the Chinese mainland), or the Sec-MCA 1.0 or Sec-MCA 1.0 (Basic Edition) of Anti-DDoS Pro and Anti-DDoS Premium (outside the Chinese mainland), contact your business manager.
Only pay-as-you-go standard GA instances can be connected to Anti-DDoS Premium. Subscription-based standard GA instances and basic GA instances are not supported.
Prerequisites
Your services are deployed on ECS01 and ECS02 servers in the US (Silicon Valley) region. This topic uses Alibaba Cloud Linux 3 as an example and configures an HTTP 80 service using Nginx.
You have configured a DNS record for your custom domain name. You have configured an A record to point the domain name to the public IP addresses of the two backend servers.
If you use a DNS service other than Alibaba Cloud DNS, see your DNS provider's instructions.
To provide services over HTTPS 443, you must create and apply for a certificate or upload a third-party certificate to the SSL Certificate service and bind it to your custom domain name.
You have purchased an Anti-DDoS Pro or Anti-DDoS Premium instance.
This topic uses an example of an Anti-DDoS Pro or Anti-DDoS Premium (Outside Chinese Mainland) instance with Mitigation Plan and Standard Function purchased for clients accessing the service from the Hong Kong (China) region.
ImportantIf your configured GA acceleration area (client region) includes the Chinese mainland, you also need to purchase an Anti-DDoS Pro or Anti-DDoS Premium (Chinese Mainland) instance and ensure that your custom domain name has completed ICP filing.
Procedure
Step 1: Configure Global Accelerator
On the page of the GA console, click Create Standard Pay-as-you-go Instance.
In the Basic Instance Configuration step, configure the basic information and click Next.
In the Configure Acceleration Area step, add an acceleration region, allocate bandwidth to the region, and then click Next.
In this example, the Acceleration Region parameter is set to China (Hong Kong), and the ISP Line Type parameter is set to BGP (Multi-ISP). You can use the default values for other parameters or modify the parameters based on your business requirements. For more information, see Add and manage acceleration areas.
ImportantIf the acceleration regions include regions in the Chinese mainland, you must apply for an ICP number for the domain name to provide services.
If you specify a small value for the maximum bandwidth, throttling may occur and packets may be dropped. Specify a maximum bandwidth based on your business requirements.
In the Configure listeners step, configure the forwarding protocol and port, and then click Next.
In this example, the Routing Type parameter is set to Intelligent Routing, the Protocol parameter is set to HTTP, and the Port parameter is set to 80. You can use the default values for other parameters or modify the parameters based on your business requirements. For more information, see Add and manage smart routing listeners.
NoteIf you want to use HTTPS 443 to provide external services, you can select HTTPS for Protocol and 443 for Port, associate the created certificate with the listener, and configure the mapping between listener port 443 and the backend service port 80 in the Port Mapping parameter of the endpoint group. This way, users can securely access the HTTP website over HTTPS.
On the Configure an endpoint group page, configure the backend service for the endpoint and click Next.
In this scenario, the Region is set to US (Silicon Valley). For Backend Service, add ECS01 and ECS02 sequentially. Enable the Health Check switch, and then read and select the Compliance Commitments Regarding Cross-border Data Transfers. Keep the default values for other endpoint group parameters or modify them as needed.
In the Configuration Review step, confirm the GA configurations and click Submit.
On the Instances page, find the created GA instance and obtain the CNAME assigned to the GA instance in the CNAME column.
On the backend server, allow the network segment that GA uses to connect to the backend service.
In this scenario, GA connects to the backend ECS servers over a private network. You need to allow its vSwitch CIDR block in the ECS security group and ensure that the number of available private IP addresses in this vSwitch CIDR block is 8 or more.
Step 2: Connect the GA instance to Anti-DDoS Pro or Anti-DDoS Premium
On the page in the Global Accelerator console, find the target GA instance and click in the Actions column.
In the Associate with Anti-DDoS Pro/Premium dialog box, select an Anti-DDoS Pro or Anti-DDoS Premium instance and click OK.
In this scenario, because the GA acceleration area is Hong Kong (China), select an Anti-DDoS Pro or Anti-DDoS Premium (Outside Chinese Mainland) instance. If your configured GA acceleration area (client region) includes the Chinese mainland, you must also select an Anti-DDoS Premium or Anti-DDoS Pro (Chinese Mainland) instance and follow Step 3 to configure Website Config for the instance.
To the right of the instance ID, hover over the Anti-DDoS Pro/Premium icon. In the Anti-DDoS Proxy tooltip, get the Secure GA CNAME.
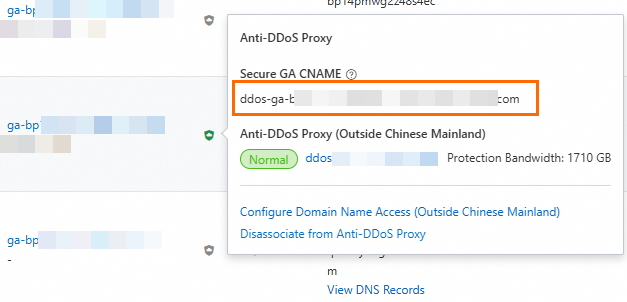 Note
NoteAfter you configure GA to connect to Anti-DDoS Pro and Anti-DDoS Premium, each acceleration area is assigned four accelerated IP addresses. Two of the IP addresses are secure accelerated IP addresses, which correspond to the GA secure CNAME record. When your service is under attack, traffic that is scrubbed by Anti-DDoS Pro and Anti-DDoS Premium is accelerated through the GA secure CNAME (secure accelerated IP address) to the Alibaba Cloud acceleration network.
Step 3: Add a website to Anti-DDoS Pro or Anti-DDoS Premium
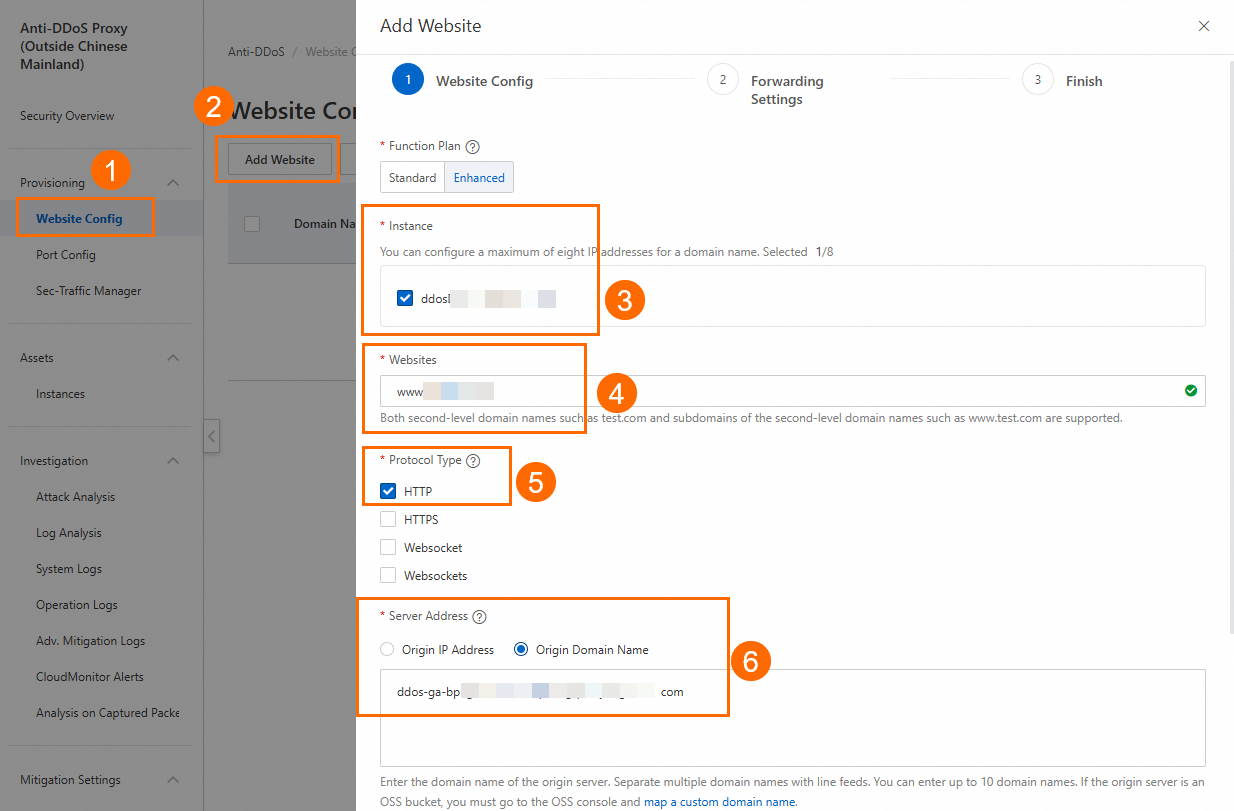
On the Website Config page of the Anti-DDoS Pro Proxy (Outside Chinese Mainland) console, click Add Website.
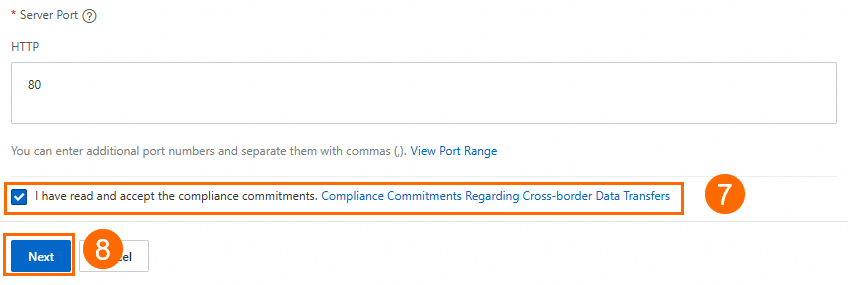
In the Add Website panel, configure the settings in the Website Config wizard, and click Next.
In this scenario, for Instance, select your purchased Anti-DDoS Pro or Anti-DDoS Premium instance. For Websites, enter your custom domain name. For Server Address, select Origin Domain Name and enter the GA secure CNAME from Step 2. The Protocol Type and Server Port must match the GA listener protocol and port (HTTP 80). Then, read and select the Compliance Commitments Regarding Cross-border Data Transfer. You can keep the default values for other website configuration parameters or modify them as needed.
WarningFor the Server Address, select GA secure CNAME instead of the GA CNAME to prevent traffic loops.
In the Forwarding Settings wizard, confirm the configuration and click Next.
In this scenario, you can keep the default configurations.
On the Finish page, click Complete and Return to Domain Name List.
On the origin server, add the back-to-origin IP addresses of Anti-DDoS Pro or Anti-DDoS Premium to the whitelist.
You need to add the back-to-origin IP address ranges of Anti-DDoS Pro and Anti-DDoS Premium to the whitelist of your security software and security groups to prevent back-to-origin traffic from being blocked by mistake.
Step 4: Configure a CNAME record
In actual business scenarios, we recommend that you use a custom domain name. You can create a CNAME record to map the custom domain name to the CNAME assigned by GA. This way, business traffic is switched to GA for accelerated access.
In this example, if you already created an A record that points to the backend server, you can specify the China (Hong Kong) region when you add a CNAME record that points to the GA instance. If the CNAME record works as expected, apply the CNAME record to other regions or retain only the CNAME record that points to the GA instance.
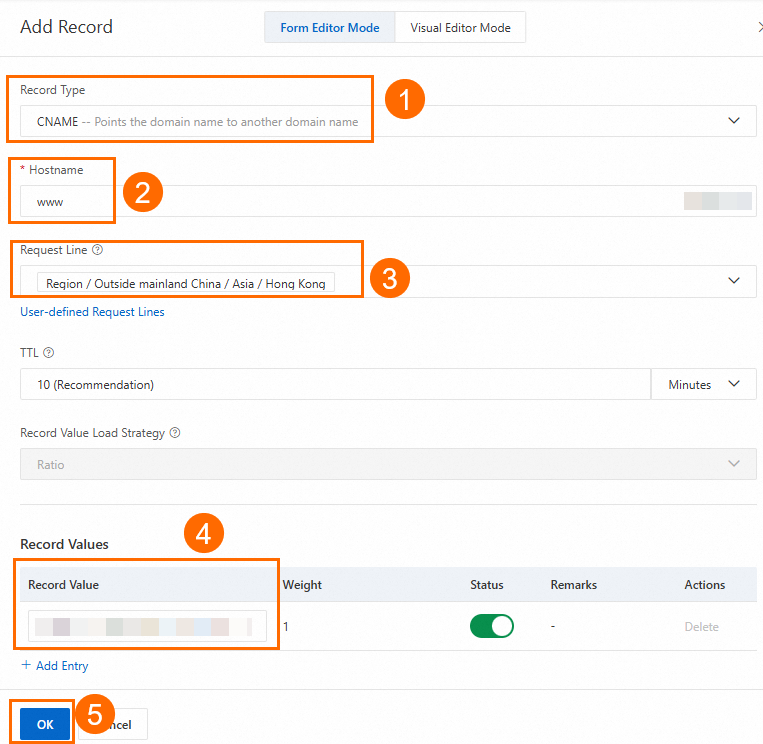
On the Authoritative DNS Resolution page, find the domain name that you want to use and click DNS Settings in the Actions column.
NoteFor a domain name that is not registered with Alibaba Cloud, you must add the domain name to the Alibaba Cloud DNS console before you can configure DNS records.
On the DNS Settings page, click Add DNS Record, configure a CNAME record, and then click OK.
In this example, the Record Type parameter is set to CNAME, the Hostname parameter is set to www, the DNS Request Source parameter is set to Asia_Hong Kong, and the Record Value parameter is set to the CNAME of the GA instance. You can use the default values for other parameters or modify the parameters based on your business requirements. For more information, see Add DNS records.
Step 5: Verify the results
Verify the acceleration performance of GA
This topic uses a probe point in Hong Kong (China) as an example. Before and after you configure GA, use a network probe tool to test the custom domain name of the website and check the response time to understand the data latency.
Test the network latency before you configure GA.
You can view information such as the response time. The Resolved IP column shows the public IP address of the ECS instance.
Test the network latency after you configure GA.
You can view information such as the response time. The Resolved IP column shows the accelerated IP address of the GA instance.
The test result shows that GA reduces the latency for clients in Hong Kong (China) that access services in the US (Silicon Valley) region.
The acceleration performance of GA is subject to the results of your business tests.
Verify the health check feature of GA
Enter the custom domain name of the website in a browser to access the website that is deployed in the US (Silicon Valley) region.
The test result shows that you can access the website that is deployed in the US (Silicon Valley) region through the custom domain name. After you refresh the browser multiple times, the responding server switches between ECS01 and ECS02.

Simulate a failure: Stop the ECS01 server.
After a while, you can check the Health Check Status on the Endpoint Group tab of the GA instance.
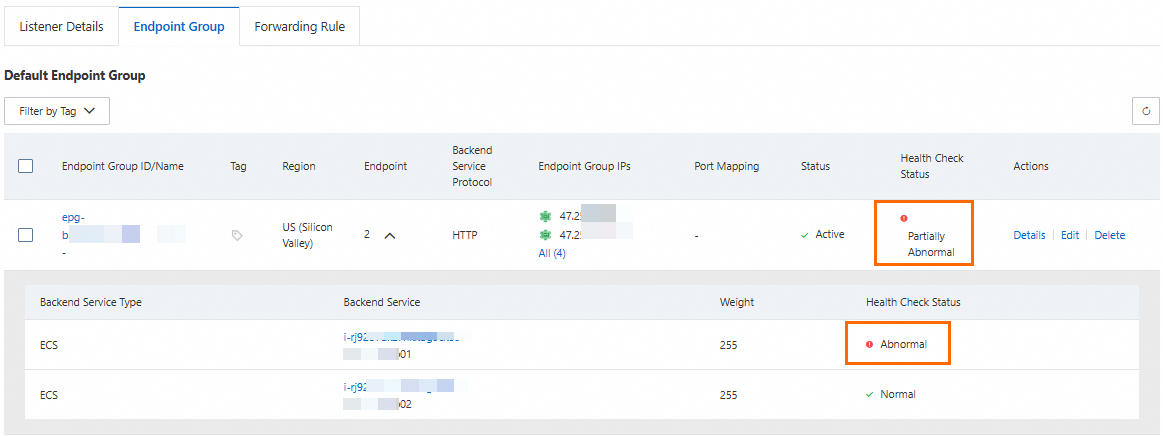
After you refresh the browser multiple times, you can still access the business as normal, but the only responding server is ECS02.

Verify that Anti-DDoS Pro or Anti-DDoS Premium effects
Use the
curlcommand to connect to your custom domain name by specifying the IP address of the Anti-DDoS Pro or Anti-DDoS Premium instance. If the connection is successful, the link between GA and Anti-DDoS Pro or Anti-DDoS Premium is clear. When your service is under attack, GA can reroute traffic to the anti-DDoS scrubbing centers for scrubbing.WarningAfter you connect GA to Anti-DDoS Pro and Anti-DDoS Premium, you must ensure that the following conditions are met to avoid traffic interruptions.
Ensure that you have completed this connectivity test to confirm that the link between GA and Anti-DDoS Pro or Anti-DDoS Premium is clear.
Before you release the GA instance, do not unsubscribe from the Anti-DDoS Pro or Anti-DDoS Premium instance. You must also ensure that the Anti-DDoS Pro or Anti-DDoS Premium instance has not expired to maintain its service status.
curl 170.33.XX.XX -H "Host: <your custom domain name>"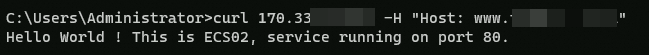
You can use the following features that are provided by Anti-DDoS Pro and Anti-DDoS Premium to view the protection effect or be promptly notified of business anomalies.
The Attack Analysis page lets you view the records and details of attack events on the Anti-DDoS Pro or Anti-DDoS Premium instance.
The Advanced Mitigation Logs page lets you view the usage of advanced mitigation sessions. You must purchase an instance that includes advanced mitigation sessions or an additional global advanced mitigation session to view this information.
The CloudMonitor Alerts page lets you set up alert monitoring and a real-time dashboard. When an anomaly occurs in your Anti-DDoS service, CloudMonitor can promptly send you an alert. This helps you shorten the response time and restore your business as soon as possible. You can also view monitoring details on the real-time dashboard for troubleshooting.
References
GA fees include the GA instance fee, CU fee, and traffic fee.
For cross-border scenarios, premium bandwidth cross-border acceleration is used by default. If you require higher network quality, you can use leased line cross-domain acceleration. For more information, see Acceleration configuration selection.
For more information about Anti-DDoS: