You can use Anti-DDoS Origin in combination with Anti-DDoS Proxy (Chinese Mainland) to protect your cloud service. If you use Anti-DDoS Origin in combination with Anti-DDoS Proxy (Chinese Mainland) to protect your cloud service, you can experience the benefits of both Anti-DDoS Origin and Anti-DDoS Proxy (Chinese Mainland). For example, Anti-DDoS Origin is cost-effective, protects all assets, and supports transparent deployment without latency. Anti-DDoS Proxy (Chinese Mainland) mitigates volumetric DDoS attacks. This topic describes how to use Anti-DDoS Origin in combination with Anti-DDoS Proxy (Chinese Mainland) to protect your cloud service.
Traffic switchover
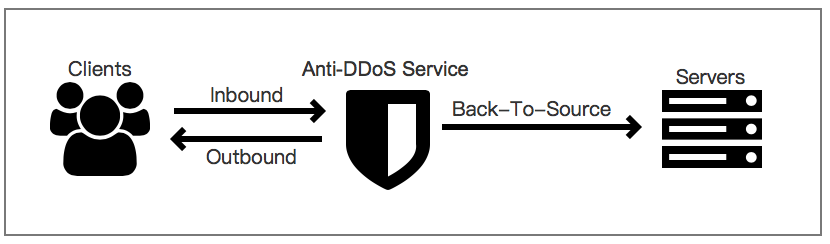
If the volume of DDoS attacks that occur on your cloud service does not exceed the mitigation capabilities of your Anti-DDoS Origin instance, service traffic is automatically forwarded to your cloud service and no latency occurs. If the volume of DDoS attacks that occur on your cloud service exceeds the mitigation capabilities of your Anti-DDoS Origin instance and blackhole filtering is triggered, Sec-Traffic Manager switches the service traffic from your Anti-DDoS Origin instance to your Anti-DDoS Proxy (Chinese Mainland) instance to mitigate the volumetric DDoS attacks. After the DDoS attacks stop, Sec-Traffic Manager switches the service traffic back to your cloud service based on the switchback waiting time. The mitigation capabilities of Anti-DDoS Origin instances vary based on regions. For more information, see Mitigation capabilities.
When blackhole filtering is triggered, Sec-Traffic Manager automatically performs a switchover from Anti-DDoS Origin to Anti-DDoS Proxy (Chinese Mainland) based on DNS records. If the local DNS servers are deployed in the Chinese mainland, the switchover requires 5 to 10 minutes. If the local DNS servers are deployed outside the Chinese mainland, the switchover requires 1 to 3 minutes.
After the attacks stop, the service traffic is not immediately switched back from Anti-DDoS Proxy (Chinese Mainland) to Anti-DDoS Origin. This avoids frequent switchovers due to continuous attacks and ensures service continuity.
Solution overview
You can perform the following operations to deploy Anti-DDoS Origin and Anti-DDoS Proxy (Chinese Mainland):
Purchase and configure an Anti-DDoS Origin instance: Add your cloud service to the purchased Anti-DDoS Origin instance for protection. If the volume of DDoS attacks that occur on your cloud service does not exceed the mitigation capabilities of the Anti-DDoS Origin instance, service traffic is automatically forwarded to your cloud service.
Purchase and configure an Anti-DDoS Proxy (Chinese Mainland) instance: Add your cloud service to the purchased Anti-DDoS Proxy (Chinese Mainland) instance. If the volume of DDoS attacks that occur on your cloud service exceeds the mitigation capabilities of the Anti-DDoS Origin instance and blackhole filtering is triggered, Sec-Traffic Manager switches the service traffic from the Anti-DDoS Origin instance to the Anti-DDoS Proxy (Chinese Mainland) instance. The mitigation capabilities of the Anti-DDoS Proxy (Chinese Mainland) instance vary based on the specifications that you select when you purchase the instance.
Configure Sec-Traffic Manager: If the volume of DDoS attacks that occur on your cloud service exceeds the mitigation capabilities of the Anti-DDoS Origin instance and blackhole filtering is triggered, Sec-Traffic Manager switches the service traffic from the Anti-DDoS Origin instance to the Anti-DDoS Proxy (Chinese Mainland) instance. After the attacks stop, Sec-Traffic Manager switches the service traffic back to your cloud service based on the switchback waiting time.
Change the DNS record: Change the DNS record to allow traffic to be forwarded to the CNAME of Sec-Traffic Manager. This ensures that traffic is properly forwarded.
1 Purchase and configure an Anti-DDoS Origin instance
1.1 Purchase an Anti-DDoS Origin instance
In this topic, an Anti-DDoS Origin 2.0 (Subscription) instance is purchased. For more information, see Purchase an Anti-DDoS Origin instance.
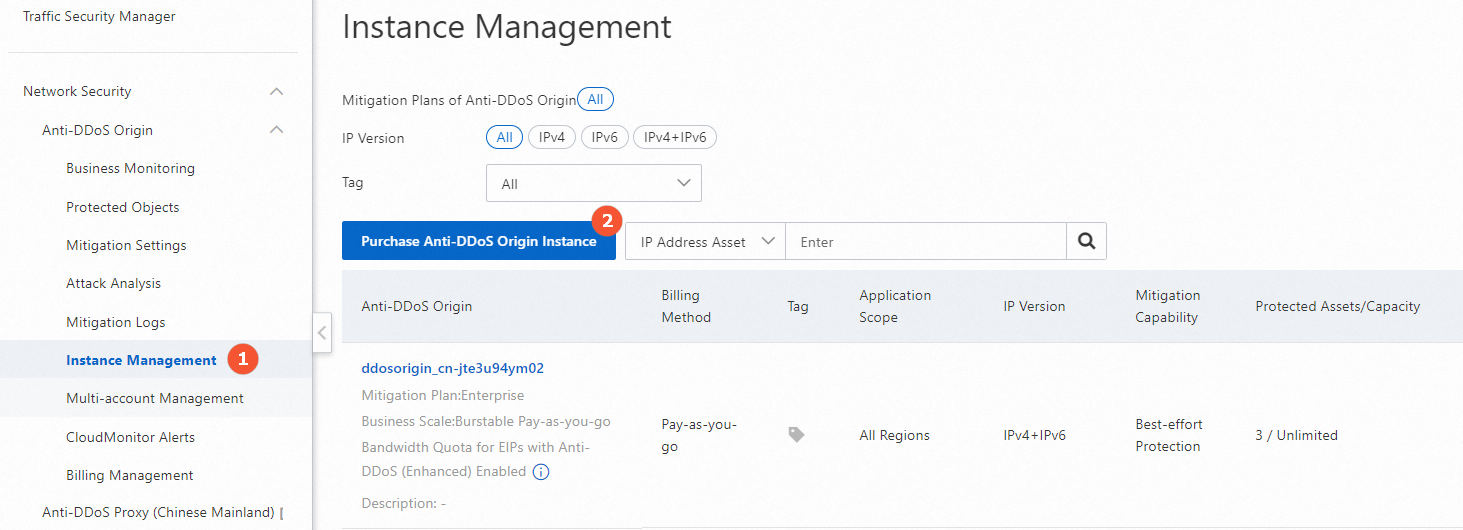
Log on to the Traffic Security console.
On the Instance Management page, click Purchase Anti-DDoS Origin Instance. On the page that appears, set the Edition parameter to Enterprise, configure the parameters, and then complete the payment.
Parameter
Description
Clean Bandwidth
The average network bandwidth of the service that you want to protect.
For more information about how to estimate your business scale, see Anti-DDoS Origin 1.0 (subscription).
IP Addresses
The total number of public IP addresses that you want to protect.
Mitigation Logs
Specifies whether to enable the mitigation logs feature, which provides full log analysis and reports for protected traffic.
Resource Group
The resource group of the instance. A resource group is a group of resources that belong to an Alibaba Cloud account. You can manage members, permissions, and resources in a resource group. You can select an existing resource group or create a resource group.
For more information, see Create a resource group.
1.2 Add the IP address of your origin server to your Anti-DDoS Origin instance for protection
For more information, see Add an object for protection.
In the top navigation bar of the Protected Objects page, select All Regions, select the instance that you purchased, and then click Add Object for Protection.
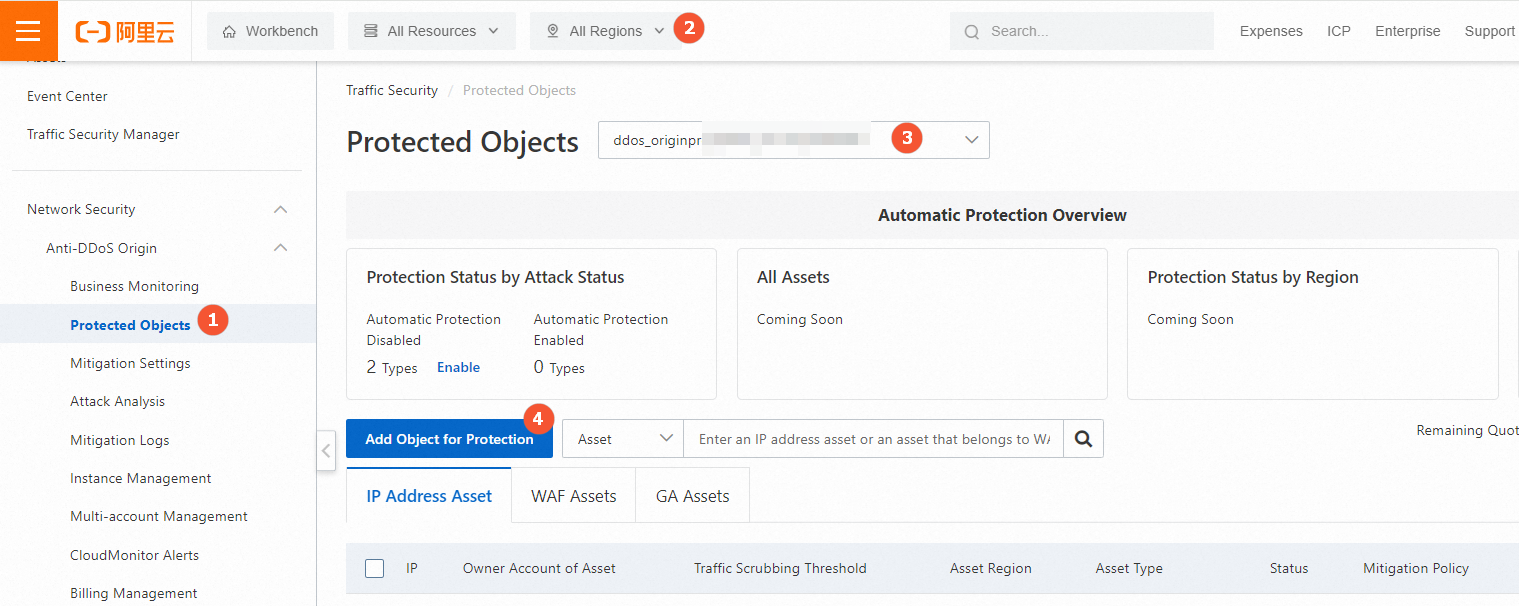
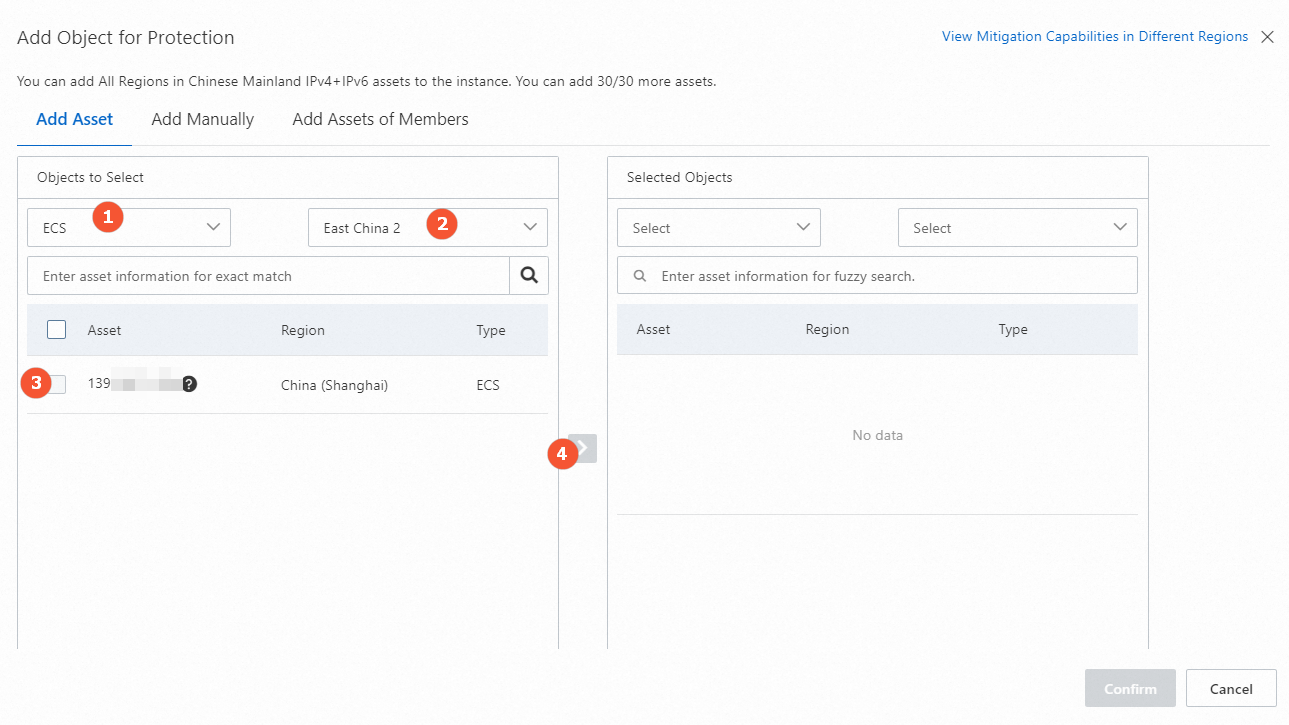
Click the Add Asset or Add Manually tab to add objects for protection. The following figure shows how to add objects for protection on the Add Asset tab.
2 Purchase and configure an Anti-DDoS Proxy (Chinese Mainland) instance
After service traffic is switched over to your Anti-DDoS Proxy (Chinese Mainland) instance, the threshold to trigger blackhole filtering varies based on the maximum mitigation capability of the instance. You can configure both basic bandwidth and burstable bandwidth to reduce the costs of Anti-DDoS Proxy (Chinese Mainland).
2.1 Purchase an Anti-DDoS Proxy (Chinese Mainland) instance
For more information, see Purchase an Anti-DDoS Proxy instance.
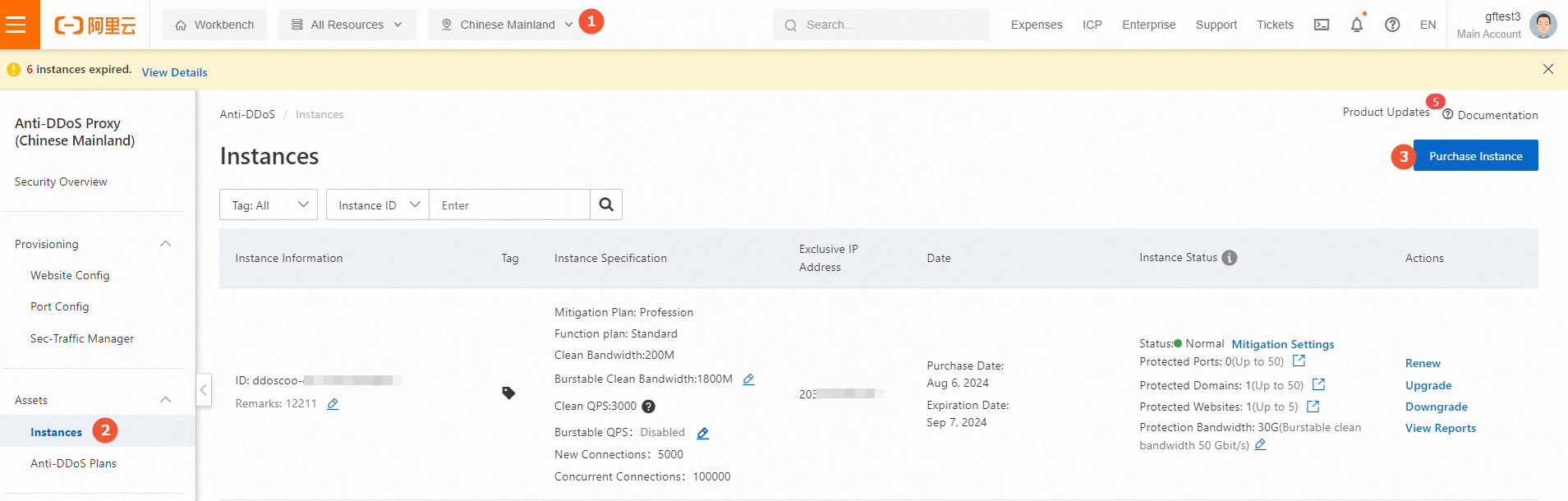
Log on to the Anti-DDoS Proxy console.
In the top navigation bar, select Chinese Mainland. On the Instances page, click Purchase Instance to purchase an instance.
Parameter
Description
IP Version
Select the IP version that is supported by the instance. Valid values: IPv4 and IPv6.
ImportantFor more information about differences between the features of Anti-DDoS Proxy (Chinese Mainland) instances that use IPv4 addresses and Anti-DDoS Proxy (Chinese Mainland) instances that use IPv6 addresses, see Functions and features.
If you use an Anti-DDoS Proxy (Chinese Mainland) instance to forward access requests from clients that use IPv6 addresses, the supported destination varies based on the methods that are used to add your services to the instance. If you add your services by using domains, the access requests are forwarded only to origin servers that use IPv4 addresses. If you add your services by using ports, the access requests can be forwarded to origin servers that use IPv4 addresses or IPv6 addresses.
Mitigation Plan
Select a mitigation plan based on your business requirements. In this example, the Profession mitigation plan is selected.
Basic Bandwidth
Specify the basic protection bandwidth for the instance. The basic protection bandwidth specifies the threshold of attack traffic that the instance can mitigate.
Burstable Bandwidth
Specify the burstable protection bandwidth for the instance. The burstable protection bandwidth specifies the maximum mitigation capacity that is provided by the instance. For more information, see Billing of the burstable protection bandwidth feature.
Clean Bandwidth
Select the clean bandwidth of normal workloads that you want the instance to protect.
WarningIf the bandwidth resources that you specify cannot meet your business requirements, packet loss may occur and your business may be affected. In this case, we recommend that you purchase more bandwidth resources. For more information, see Upgrade an instance.
95th Percentile Burstable Clean Bandwidth
Specify whether to enable the burstable clean bandwidth feature. For more information, see Billing of the burstable clean bandwidth feature. Valid values:
Disable: disables the burstable clean bandwidth feature.
Daily 95th Percentile: enables the burstable clean bandwidth feature and uses the daily 95th percentile metering method.
Monthly 95th Percentile: enables the burstable clean bandwidth feature and uses the monthly 95th percentile metering method.
Function Plan
Select a function plan for the instance. Valid values: Standard Function and Enhanced Function.
For more information, see Differences between the Standard and Enhanced function plans.
Domains
Specify the number of domains that the instance can protect. The value must be an integer multiple of 10.
The domains that are specified for the instance can be subdomains and wildcard domains. The number of unique second-level domains that correspond to the subdomains and wildcard domains cannot exceed "Domains/10".
For an Anti-DDoS Proxy (Chinese Mainland) instance of the Profession mitigation plan, the default value of the Domains parameter is 50. If you use the default value, you can specify only up to five second-level domains. You can also specify subdomains and wildcard domains that correspond to the second-level domains. The total number cannot exceed 50.
If you want to enable protection for aliyundoc.com and aliyun.com, you can specify their subdomains, such as www.aliyundoc.com and abc.aliyun.com. You can also specify the wildcard domains, such as *.aliyundoc.com and *.aliyun.com.
Request Rate
Specify the number of concurrent queries per second (QPS) that the instance can process when no attacks occur. HTTP and HTTPS requests are supported.
For more information about the mappings between the clean QPS and the numbers of connections that are supported, see Purchase an Anti-DDoS Proxy instance.
WarningIf the clean QPS that you specify cannot meet your business requirements, packet loss may occur and your business may be affected. In this case, we recommend that you specify a higher clean QPS or enable the burstable QPS feature.
95th Percentile Burstable QPS
Specify whether to enable the burstable QPS feature. For more information about the billing of the burstable QPS feature, see Billing of the burstable QPS feature. Valid values:
Disable: disables the burstable QPS feature.
Daily 95th Percentile: enables the burstable QPS feature and uses the daily 95th percentile metering method.
Monthly 95th Percentile: enables the burstable QPS feature and uses the monthly 95th percentile metering method.
For more information about the mappings between the clean QPS and the numbers of connections that are supported, see Purchase an Anti-DDoS Proxy instance.
Ports
Specify the number of TCP and UDP ports for which you can configure forwarding rules.
Resource Group
Select the resource group to which the instance belongs in Resource Management. By default, the resource group is Default Resource Group.
For more information about resource groups, see Create a resource group.
2.2 Add domain names to your Anti-DDoS Proxy (Chinese Mainland) instance
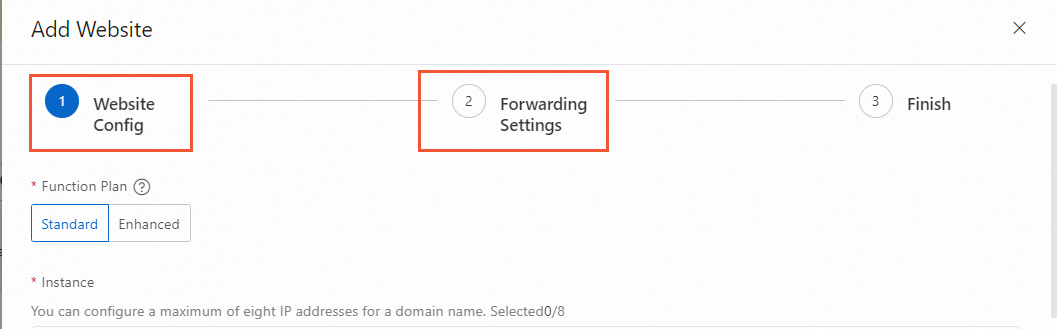
On the Website Config page, click Add Website.
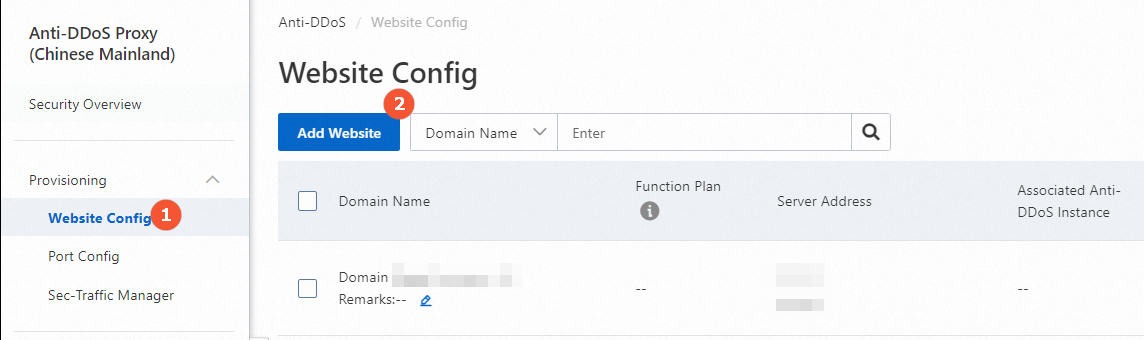
Configure the parameters in the Website Config and Forwarding Settings steps. For more information, see Add one or more websites.
NoteWhen you configure DNS resolution, you must change the record to allow traffic to be forwarded to the CNAME of Sec-Traffic Manager. After you configure the forwarding settings, you do not need to modify the DNS record in the Finish step.
3 Configure Sec-Traffic Manager
You can create a scheduling rule for Sec-Traffic Manager to enable tiered protection. This way, traffic is forwarded to the CNAME of Sec-Traffic Manager. For more information, see Create a tiered protection rule.
Log on to the Anti-DDoS Proxy (Chinese Mainland) console, choose , and then click Add Rule.
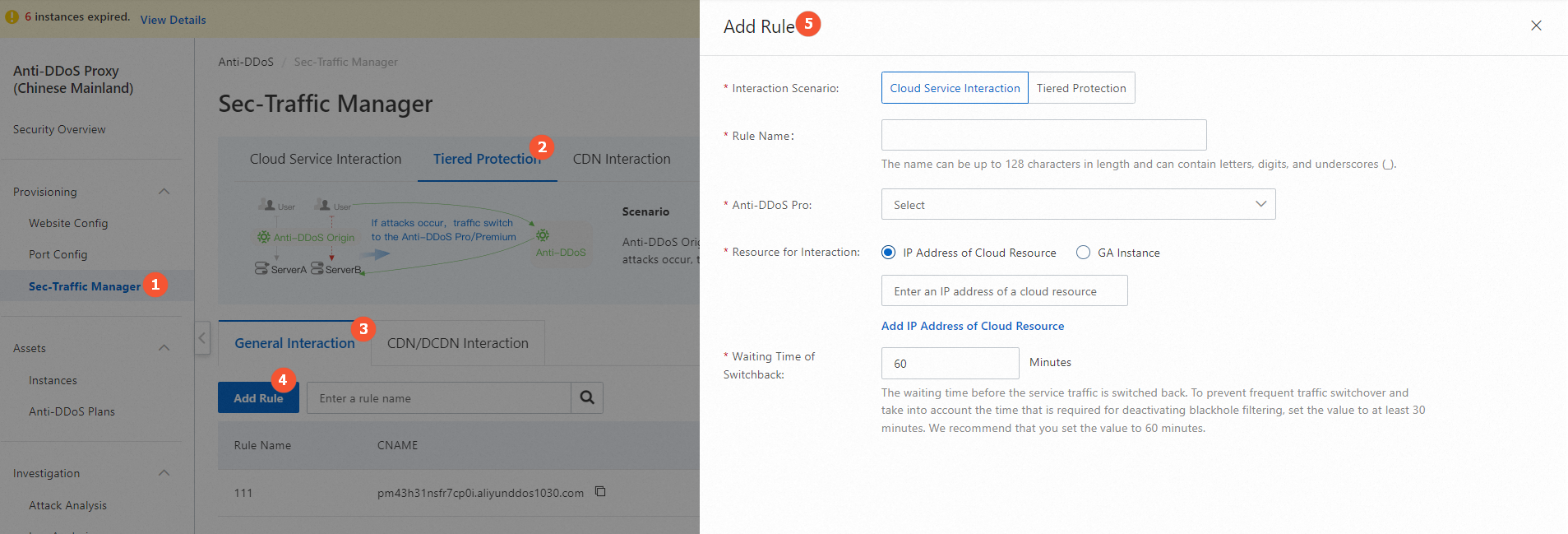
Parameter
Description
Interaction Scenario
Select Tiered Protection.
Rule Name
Enter a name for the rule.
The name can be up to 128 characters in length and can contain letters, digits, and underscores (_).
Anti-DDoS Pro
Select an Anti-DDoS Proxy (Chinese Mainland) instance.
Resource for Interaction
You can click Add IP Address of Cloud Resource to add more IP addresses. You can add up to 20 IP addresses.
NoteAfter you add multiple IP addresses, these IP addresses are associated with the specified Anti-DDoS Proxy instance. If one of the IP addresses is attacked, service traffic is forwarded to other IP addresses. Service traffic is forwarded to the Anti-DDoS Proxy instance only if all IP addresses are attacked. For more information about how to forward traffic to Anti-DDoS Proxy when one of the IP addresses is attacked, see Share one Anti-DDoS Proxy instance among multiple cloud resources.
Waiting Time of Switchback
Specify the waiting time before the service traffic is switched from your Anti-DDoS Proxy instance back to the IP address of a cloud resource. When the attack stops and the waiting time that you specify elapses, the service traffic is automatically switched back to the IP address of the cloud resource.
You can specify a value that ranges from 30 to 120. Unit: minutes. We recommend that you set the value to 60.
NoteIf blackhole filtering is triggered for your Anti-DDoS Proxy instance or before the specified waiting time that starts from the start time of the blackhole filtering event of the instance elapses, the service traffic of a cloud resource cannot be switched to the instance.
If blackhole filtering is triggered for a cloud resource, the service traffic of the cloud resource is automatically switched to your Anti-DDoS Proxy instance for protection. If blackhole filtering is not deactivated for the cloud resource, the service traffic cannot be switched from your Anti-DDoS Proxy instance back to the cloud resource. If blackhole filtering is deactivated for the cloud resource, the service traffic can be immediately switched back to the cloud resource regardless of the specified waiting time.
After you add the rule, obtain the CNAME of Sec-Traffic Manager.
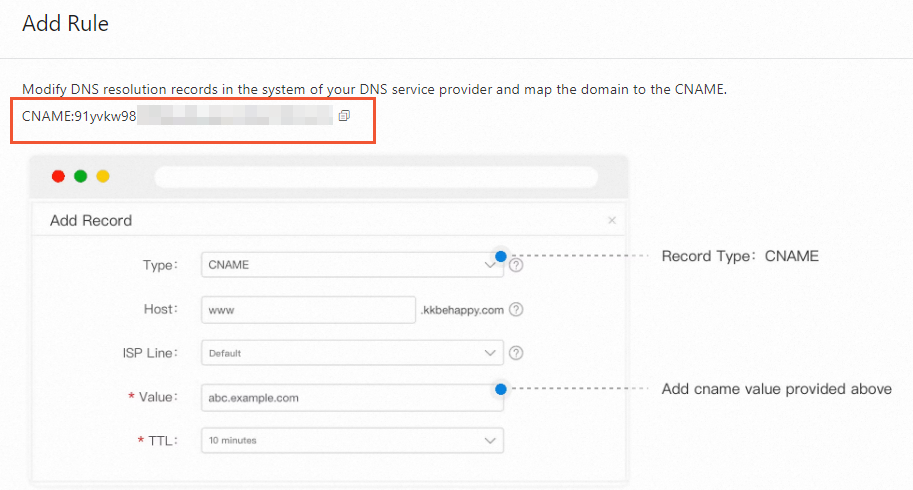
4 Change the DNS record
You can visit the website of your DNS provider and change the DNS record to allow traffic to be forwarded to the CNAME of Sec-Traffic Manager. For more information, see Change the CNAME record to redirect traffic to Sec-Traffic Manager.
In this topic, Alibaba Cloud DNS is used as an example.
Log on to the Alibaba Cloud DNS console.
On the page, click Add Zone.
Change the DNS record based on your business requirements.
Set Record Type to CNAME and Record Value to the CNAME of Sec-Traffic Manager that you obtained.
 For example, you want to add three websites to an instance. The peak of outbound service traffic on each website is 50 Mbit/s or lower. The total bandwidth that is required by the three websites is 150 Mbit/s or lower. In this case, make sure that the clean bandwidth of the purchased instance is higher than 150 Mbit/s.
For example, you want to add three websites to an instance. The peak of outbound service traffic on each website is 50 Mbit/s or lower. The total bandwidth that is required by the three websites is 150 Mbit/s or lower. In this case, make sure that the clean bandwidth of the purchased instance is higher than 150 Mbit/s.