Platform security diagnostics scans your DataWorks workspace against security best practices — covering identity authentication, permission management, data transmission, and development mode. Each finding is classified by risk level so you can prioritize remediation.
How it works
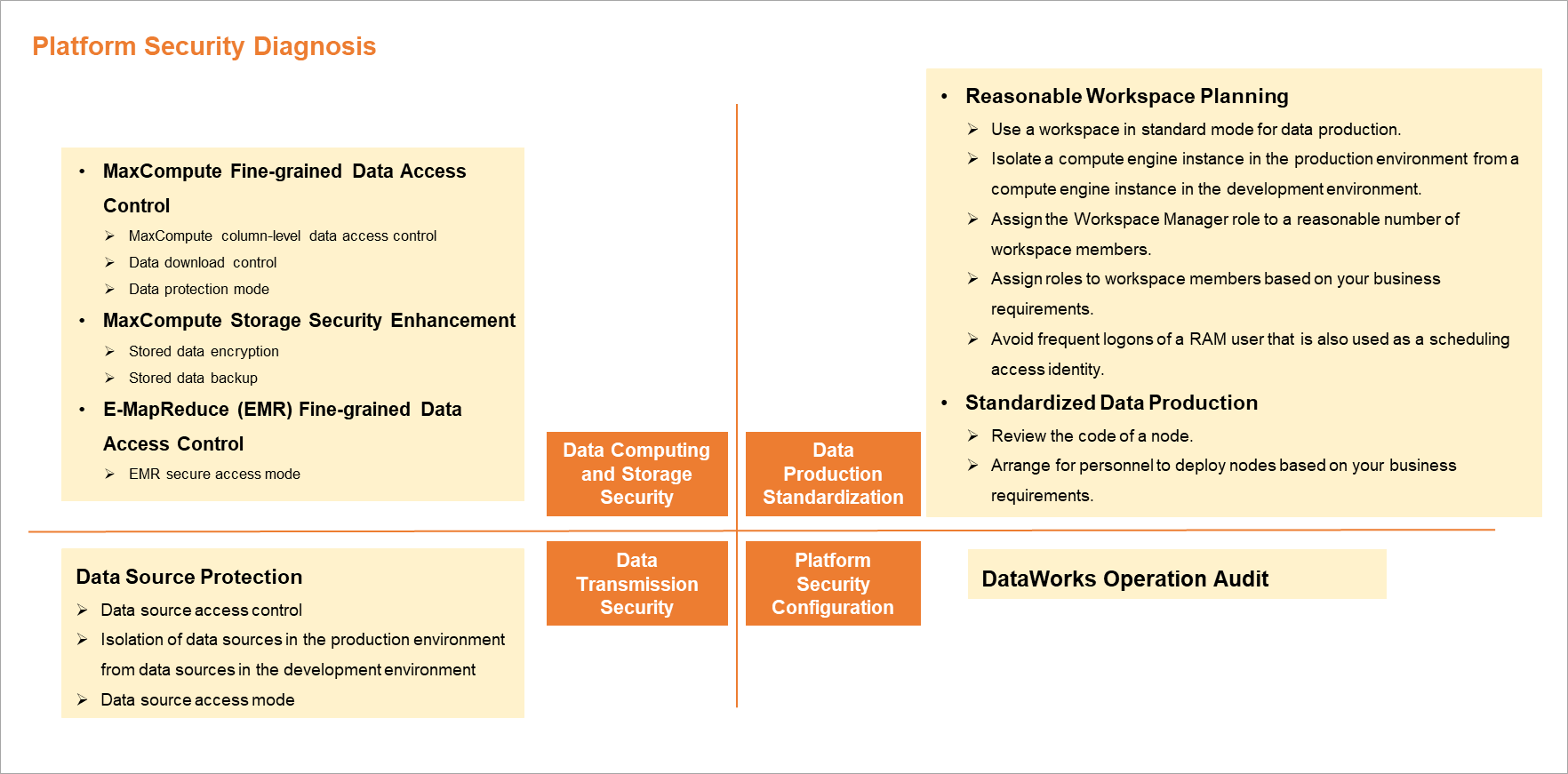
The Platform Security Diagnosis page runs automated checks across four categories:
-
Data computing and storage — Detects permission gaps, missing encryption, and backup configuration issues in your compute resources.
-
Data transmission security diagnostics — Flags unmanaged data source permissions and missing dev/prod isolation that could expose production data.
-
Standardized diagnostics of data production — Checks workspace structure, role assignments, and development workflow compliance.
-
Platform security configuration diagnostics — Verifies that operation audit logging is active.
Each finding is labeled low-risk, medium-risk, or high-risk, and includes a diagnostic result and a suggested remediation action. For details about all diagnostic items across each dimension, see the Appendix: Details of diagnostic items section in this topic.
Open the Platform Security Diagnosis page
-
Log on to the DataWorks console. In the top navigation bar, select the target region. In the left-side navigation pane, choose Data Governance > Security Center, then click Go to Security Center.
-
In the left-side navigation pane, click Platform Security Diagnosis. The page loads all diagnostic items that need remediation in the current region, grouped by category and labeled by risk level.
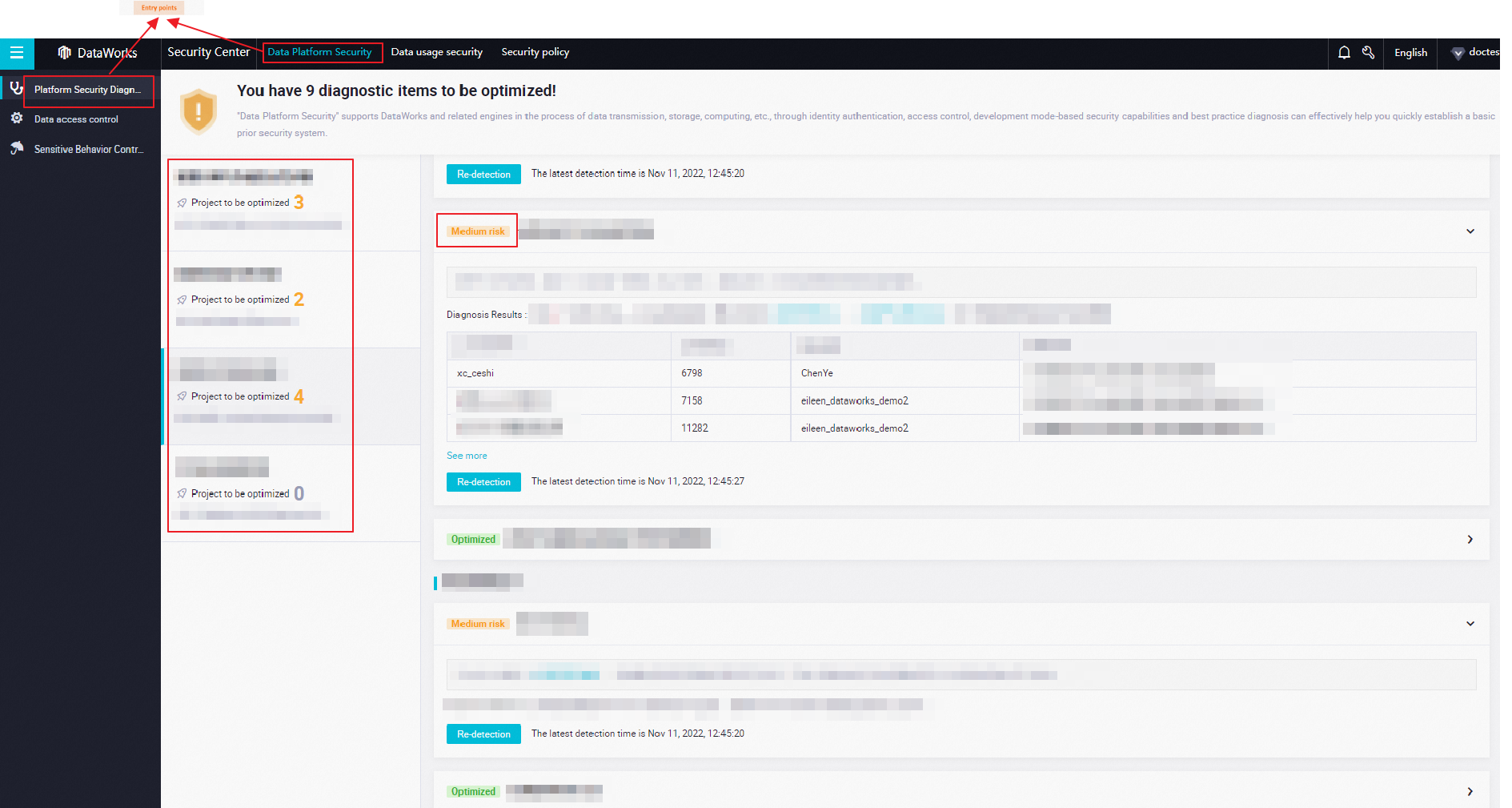
View and act on diagnostic results
Each category shows a count of medium-risk and high-risk items. Click a medium-risk or high-risk item to view the risk details and the suggested fix.
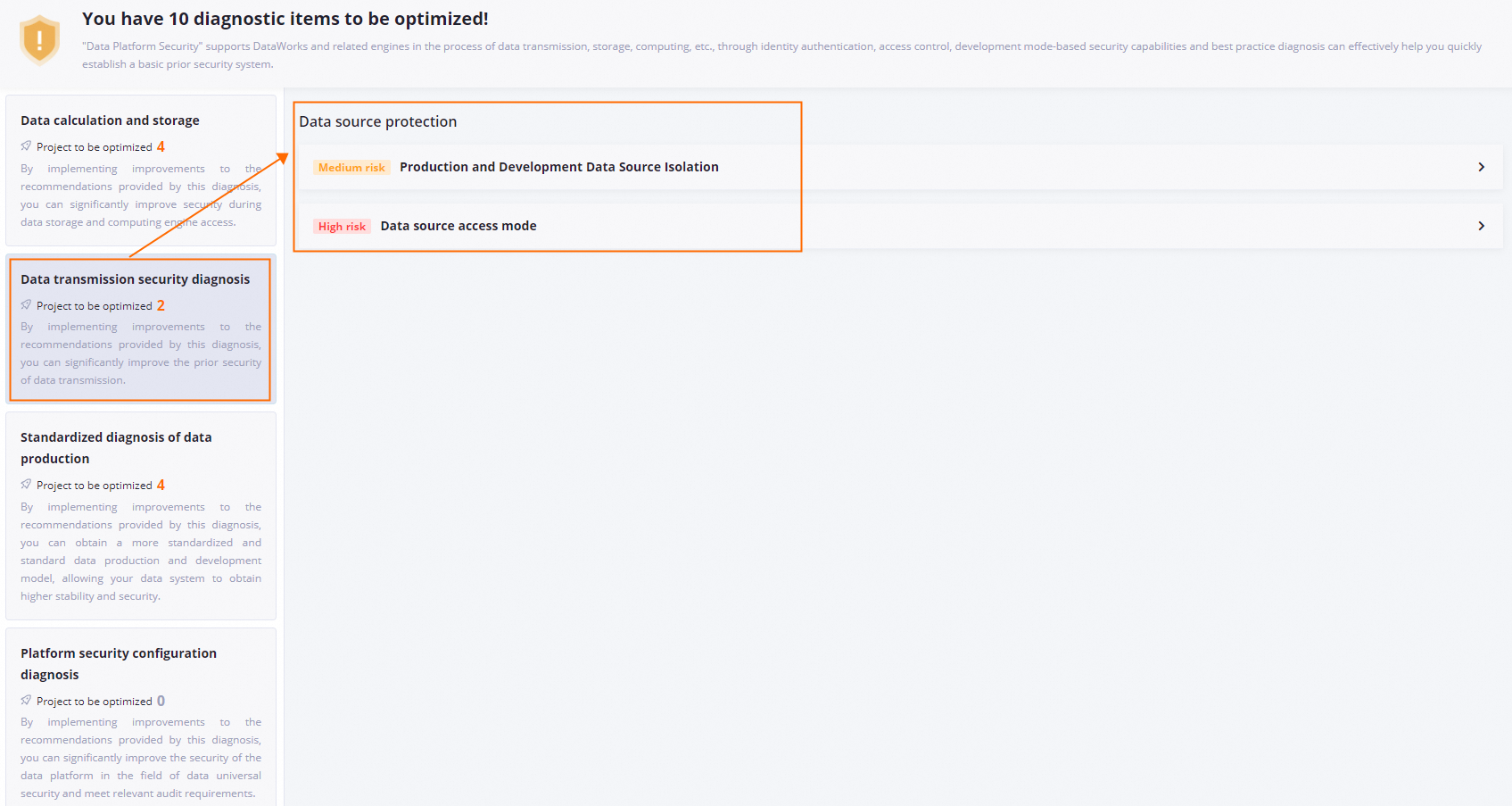
The following example shows a finding in the Data transmission security diagnostics category.
Click the item to see the full diagnostic result and suggestion.
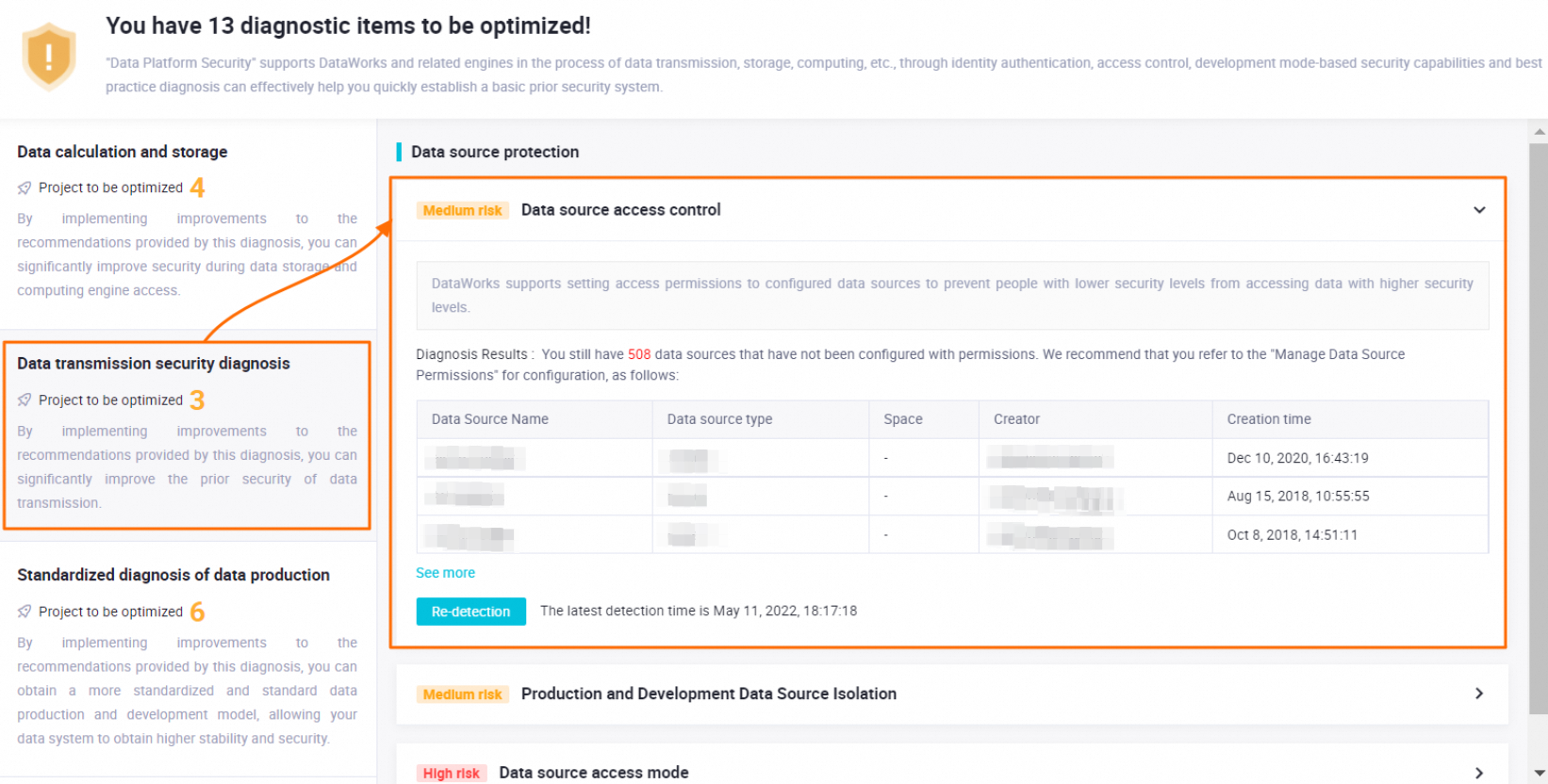
Finding: Data source permissions are not configured, so users with lower security levels can access data at higher security levels.
Suggested fix: Configure access control on your data sources to restrict who can connect to each one.
Appendix: Details of diagnostic items
The following tables list all diagnostic items supported by platform security diagnostics.
The items shown on the page depend on which data sources are added to your workspace and which issues are currently detected.
Data computing and storage
Diagnostic items in this category improve security for data storage and access.
| Diagnostic dimension | Diagnostic item | Diagnostic object | How it checks |
| MaxCompute fine-grained data permission management | MaxCompute column-level permission management Note: The MaxCompute V2.0 permission model provides finer-grained permission control, decentralized project management, and stronger end-to-end identity capabilities — enabling security configurations suited to your actual environment. |
MaxCompute project | Detects MaxCompute projects where the MaxCompute V2.0 permission model is disabled. |
| Data download control Note: Restrict direct data downloads via MaxCompute Tunnel to prevent unintended data leaks from users who don't need that access. |
MaxCompute project | Detects MaxCompute projects where either the MaxCompute V2.0 permission model is disabled, or the model is enabled but download permission management is turned off. For details, see Download control. | |
| Data protection mode Note: The data protection mechanism controls how data flows out of a MaxCompute project. |
MaxCompute project | Checks whether protection mode is enabled for specific or all MaxCompute projects. For details, see Project data protection. | |
| MaxCompute storage security enhancement | Data storage encryption Note: MaxCompute supports storage encryption backed by Key Management Service (KMS), providing static data protection for compliance and security requirements. For details, see Storage encryption. |
MaxCompute project | Detects MaxCompute projects where storage encryption is disabled. To enable encryption for an existing project, submit a ticket. |
| Data storage backup Note: MaxCompute automatically backs up historical data versions and retains them for a set period. During this window, you can restore data to recover from accidental changes. For details, see Backup and restoration. |
MaxCompute project | Enabled by default. Adjust the retention period or restore data as needed. For details, see Backup and restoration. | |
| EMR fine-grained data permission management | E-MapReduce (EMR) secure access mode Note: When an EMR cluster is registered to a DataWorks workspace using Security mode, data permissions are isolated between Alibaba Cloud accounts and RAM users. For details, see Security mode. |
DataWorks workspace | Detects workspaces where EMR clusters are registered using a mode other than Security mode. |
Data transmission security diagnostics
Diagnostic items in this category improve security for data in transit.
| Diagnostic dimension | Diagnostic item | Diagnostic object | How it checks |
| Data source protection | Data source access control Note: DataWorks lets you restrict which users can access each configured data source, preventing lower-privilege users from reaching higher-sensitivity data. |
DataWorks workspace data source | Detects workspaces where access permissions on configured data sources are not managed. For details, see Manage permissions on data sources. |
| Production and development data source isolation Note: In a standard mode workspace, a data source can have separate configurations for the development and production environments, preventing development activity from touching production data. For details, see Isolate a data source in the development and production environments. |
DataWorks workspace data source | Detects standard mode workspaces where a data source shares the same configuration in both the development and production environments. | |
| Data source access mode Note: DataWorks supports RAM role-based access to Object Storage Service (OSS) data sources. This mode avoids storing AccessKey pairs directly and reduces the risk of credential leaks. |
DataWorks workspace data source | Detects workspaces where OSS data sources are configured to use AccessKey mode. Switch to RAM role-based authorization instead. For details, see Use the RAM role-based authorization mode to add a data source. | |
Standardized diagnostics of data production
Diagnostic items in this category improve the stability and security of the data output pipeline.
| Diagnostic dimension | Diagnostic item | Diagnostic object | How it checks |
| Reasonable workspace planning | Use workspaces in standard mode for data production Note: Standard mode workspaces enforce development/production separation, making them more secure than basic mode for production workflows. For a comparison, see Differences between workspaces in basic mode and workspaces in standard mode. |
DataWorks workspace mode | Detects workspaces running in basic mode in the current region. Upgrade with caution — see Upgrade a workspace from basic mode to standard mode. |
| Isolate a compute engine in the production environment from a compute engine in the development environment Note: In standard mode, a compute engine can have separate configurations per environment to prevent development jobs from accessing production resources. |
DataWorks workspace data source | Detects workspaces where a data source has the same configuration in both the development and production environments. | |
| Reasonably specify the number of workspace administrators Note: Too many administrators in a single workspace can lead to inconsistent management. Keep the count to three or fewer. |
DataWorks workspace member management | Detects workspaces with more than three workspace administrators. | |
| Reasonable allocation of workspace member roles Note: Assign each workspace member a single dedicated role to prevent unintended access from overlapping permissions. |
DataWorks workspace member management | Detects workspaces where one member holds multiple roles in the current region. Review role definitions before making changes — see Permissions of built-in workspace-level roles. | |
| Avoid frequent logons of a RAM user that is also used as a scheduling access identity Note: RAM users acting as scheduling access identities for compute engines should not be used for interactive logons, as this exposes key compute engine data to unnecessary access. |
DataWorks workspace management | Detects workspaces where a RAM user configured as a scheduling access identity has also logged on to DataWorks interactively in the past three months. | |
| Standardized data production | Code review Note: DataWorks provides a code review feature. When mandatory code review is enabled in a standard mode workspace, every node must be reviewed and approved before it can be deployed to production. |
DataWorks workspace management | Detects workspaces where the code review feature is disabled or the review scope is not configured. For setup details, see Code review. |
| Arrange for personnel to deploy tasks based on your business requirements Note: In a standard mode workspace, the person who deploys a task should be different from the person who developed it — separating development and deployment responsibilities. |
DataWorks workspace management | Detects tasks that were developed and deployed by the same person in the past 30 days. | |
Platform security configuration diagnostics
Diagnostic items in this category improve overall data security.
| Diagnostic dimension | Diagnostic item | Diagnostic object | How it checks |
| DataWorks operation audit | DataWorks operation audit Note: DataWorks records user operations through ActionTrail, with a delay of about 5 to 10 minutes. For details, see Use ActionTrail to query behavior events. |
DataWorks workspace management | Enabled by default for DataWorks workspaces. After activating ActionTrail, DataWorks operation logs are recorded automatically. |