DataWorks uses a two-layer permission model: RAM policies control product-level access, and role-based access control (RBAC) manages access within service modules. Grant RAM users the permissions they need based on what they're trying to do.
Permission management overview
The following figure illustrates how the two authorization mechanisms work together.
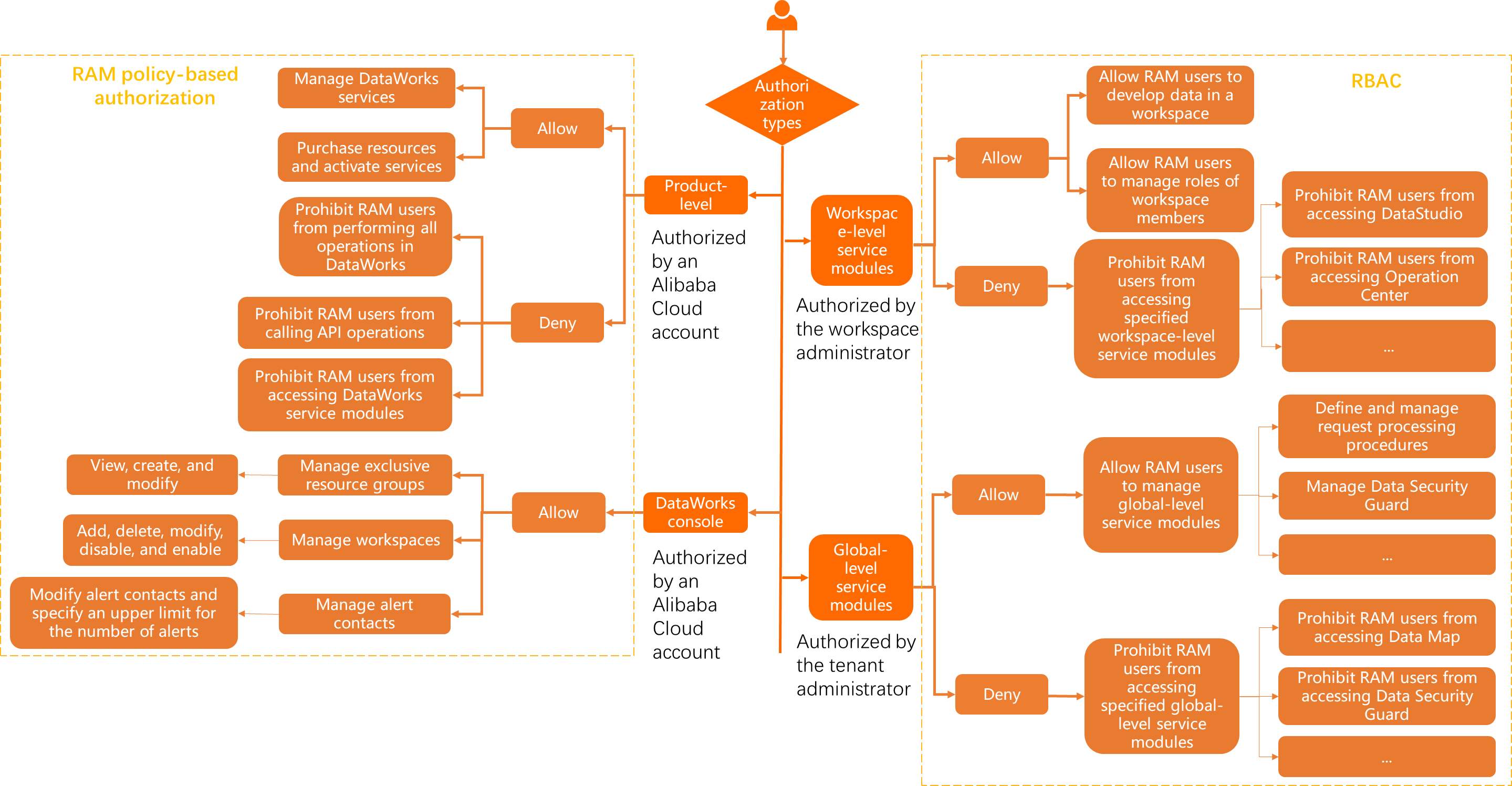
DataWorks organizes permissions into two levels:
-
Product level: Controls whether a RAM user can manage DataWorks services, purchase resources, or is blocked from all operations. Configured using RAM policies in the Resource Access Management (RAM) console.
-
Service module level: Controls what a RAM user can do inside specific service modules — such as data development or O&M operations in a workspace. Configured using RAM policies (for console and resource group operations) or RBAC roles (for workspace and global service modules).
Deny policies take precedence over all other policies configured for RAM users.
The following sections describe each level in detail:
Product-level permissions
Use RAM policies to grant or restrict product-level access to DataWorks.
| Scenario | Description | Steps | Reference |
|---|---|---|---|
| Let a RAM user manage DataWorks services | By default, only the Alibaba Cloud account can manage DataWorks services. Attach AliyunDataWorksFullAccess to let a RAM user manage services on behalf of the account. The RAM user cannot purchase services. |
1. Log on to the RAM console. 2. Attach the AliyunDataWorksFullAccess policy to the RAM user. |
Grant permissions to a RAM user |
| Let a RAM user purchase resources and activate services | By default, only the Alibaba Cloud account can purchase resources and activate services. Attach AliyunBSSOrderAccess to let a RAM user view, pay for, and cancel orders in Billing Management. |
1. Log on to the RAM console. 2. Attach the AliyunBSSOrderAccess policy to the RAM user. |
Grant permissions to a RAM user |
| Block a RAM user from all DataWorks operations | By default, all RAM users in an Alibaba Cloud account are assigned the tenant member role and can access the DataWorks console. Create and attach a custom deny policy to block a RAM user from all console operations, service module access, and API operations. | 1. Log on to the RAM console. 2. Create a custom policy. See Appendix 1: Block all operations. 3. Attach the custom policy to the RAM user. | Create a custom policy and Attach a custom policy to users |
| Block a RAM user from calling API operations | By default, RAM users with service module permissions can call API operations. Create and attach a custom deny policy to block all API calls while preserving console access. | 1. Log on to the RAM console. 2. Create a custom policy. See Appendix 2: Block API operations. 3. Attach the custom policy to the RAM user. | — |
| Block a RAM user from accessing service modules | By default, tenant members can access any service module in workspaces they belong to, and all global-level service modules. Create and attach a custom deny policy to block console access to all service modules. The RAM user can still call API operations if they have the relevant permissions. | 1. Log on to the RAM console. 2. Create a custom policy. See Appendix 3: Block service module access. 3. Attach the custom policy to the RAM user. | — |
Service module-level permissions: console and resource group operations
Use RAM policies to let a RAM user manage workspaces and resource groups in the DataWorks console.
By default, only the Alibaba Cloud account can modify workspace or resource group configurations, or delete a resource group. To grant these permissions to a RAM user, create and attach a custom RAM policy that specifies the exact operations allowed.
The RAM policies required depend on which operations you want the RAM user to perform. For policy examples, see Custom RAM policies: fine-grained permission control for console operations.
Steps:
-
Log on to the RAM console.
Service module-level permissions: workspace and global service modules
Use RBAC roles to control what RAM users can do inside DataWorks service modules. Manage these assignments on the Workspace Management page.
| Scenario | Description | Steps |
|---|---|---|
| Assign workspace-level roles | A RAM user must be a workspace member before performing data development operations. Assign a built-in or custom workspace-level role to control access within specific service modules. Built-in roles include: Development (create tables, execute SQL) and O&M (deploy nodes, perform O&M operations). For details on built-in and custom roles, see Permissions of workspace-level roles. | 1. Go to the User Management page. 2. (Optional) Create a custom workspace-level role. 3. Add the RAM user as a workspace member and assign a role. |
| Assign global-level roles | By default, tenant members can access but not manage global-level service modules. Assign a global-level role to grant management permissions on specific global service modules, or to restrict access to specific modules. For details on built-in and custom global-level roles, see Manage global roles and members. | 1. Go to the Global Member Management page. 2. (Optional) Create a custom global-level role. 3. Add the RAM user and assign a role. |
Appendix 1: Block all operations
Attach this policy to block a RAM user from all DataWorks operations — including console access, service module features, and API calls.
{
"Version": "1",
"Statement": [
{
"Effect": "Deny",
"Action": "dataworks:*",
"Resource": "*"
}
]
}Appendix 2: Block API operations
Attach this policy to block a RAM user from calling all DataWorks API operations. Console access is not affected.
{
"Version": "1",
"Statement": [
{
"Effect": "Deny",
"Action": "dataworks:*",
"Resource": "*",
"Condition": {
"StringEquals": {
"dataworks:Scope": "OpenAPI"
}
}
}
]
}Appendix 3: Block service module access
Attach this policy to block a RAM user from accessing DataWorks service modules in the console.
This policy only blocks console access to service modules. If the RAM user has permissions to call API operations of a service module, those API calls are still allowed.
{
"Version": "1",
"Statement": [
{
"Effect": "Deny",
"Action": "dataworks:*",
"Resource": "*",
"Condition": {
"StringEquals": {
"dataworks:Scope": "Page"
}
}
}
]
}