DataWorks uses Alibaba Cloud Resource Access Management (RAM) policies to control both product-level access and management console access. Attach a RAM policy to a RAM user or RAM role to grant the permissions defined in that policy.
Who should read this
Role | Task | Start here |
Alibaba Cloud account holder (root account) | Grant DataWorks management permissions to RAM users | |
RAM administrator | Create custom policies for fine-grained control | |
RAM user | Request permissions if you cannot access DataWorks features | Contact your RAM administrator |
RAM permission types
DataWorks supports two permission scopes, each with two policy approaches:
Scope | Policy type | Approach |
Product-level | System policy | Grant |
Product-level | Custom policy | Deny specific operations (entering the console, calling OpenAPI, or accessing module interfaces) |
Console entity-level | Custom policy | Allow fine-grained operations on workspaces, resource groups, and alert information |
Product-level access control: System and custom policies
By default, only the Alibaba Cloud account (root account) has product-level management permissions for DataWorks. Grant system policies to RAM users to delegate those permissions.
System policies (allowed operations)
Policy name | Scope | What it grants |
| DataWorks services | Extensive DataWorks permissions — the RAM user can manage internal product features on behalf of the root account. Purchase-related operations are excluded. |
| Resource purchasing | The RAM user can view, pay for, and cancel orders in Billing Management, and can purchase resources and renew services in the management console. |
Custom policies (denied operations)
Use custom policies when you need to restrict what RAM users can do. Three types of restrictions are supported:
Restriction | Default behavior | What the custom policy does |
Block all DataWorks access | RAM users can enter the management console, access module interfaces, and call OpenAPI | Prohibits entering the management console, accessing module interfaces, and calling OpenAPI |
Block OpenAPI calls | RAM users with module-level permissions can call the corresponding OpenAPI operations | Blocks all OpenAPI calls for the user |
Block module interface access | All RAM users in the Alibaba Cloud account are DataWorks tenant members and can access all global-level modules and workspace-level modules of any workspace they belong to | Prevents the user from accessing any module interfaces in DataWorks |
To create a custom policy, see Create a custom policy. For the policy document structure, see Product-level control policies.
Fine-grained console access control: Custom policies
DataWorks supports fine-grained access control for the following console entities. To grant these permissions, create a custom policy based on Console entity-level control policies and attach it to the RAM user.
Entity | Supported operations |
Workspace | Create, modify, delete, disable, and enable a workspace |
Resource group | Display exclusive resource groups, display resource group details by name, create an exclusive resource group, and modify an exclusive resource group |
Alert information | List contacts, modify contact information, list alert resources, and set an upper limit for the number of alerts |
Grant permissions to a RAM user
After completing this procedure, the selected RAM user has the system policies or custom policies you attached.
Prerequisites
Before you begin, ensure that you have:
RAM administrator access to the RAM console
The system policies or custom policies you want to grant. If granting a custom policy, create it first
Add permissions
Log on to the RAM console as a RAM administrator.
In the left navigation pane, choose Identity Management > Users.
On the Users page, find the required RAM user and click Add Permissions in the Actions column. To grant permissions to multiple users at once, select them and click Add Permissions at the bottom of the page.

In the Add Permissions panel, add the required permissions. For information about available policies, see Product-level access control: System and custom policies.
For details on parameter settings in this panel, see Manage permissions for a RAM user.
Create a custom policy
Skip this step if you are using only system policies for coarse-grained authorization.
Use your Alibaba Cloud account to create a custom policy in the Resource Access Management console. For the general procedure, see Create a custom policy.
Product-level control policy: Define the policy document based on Product-level control policies.
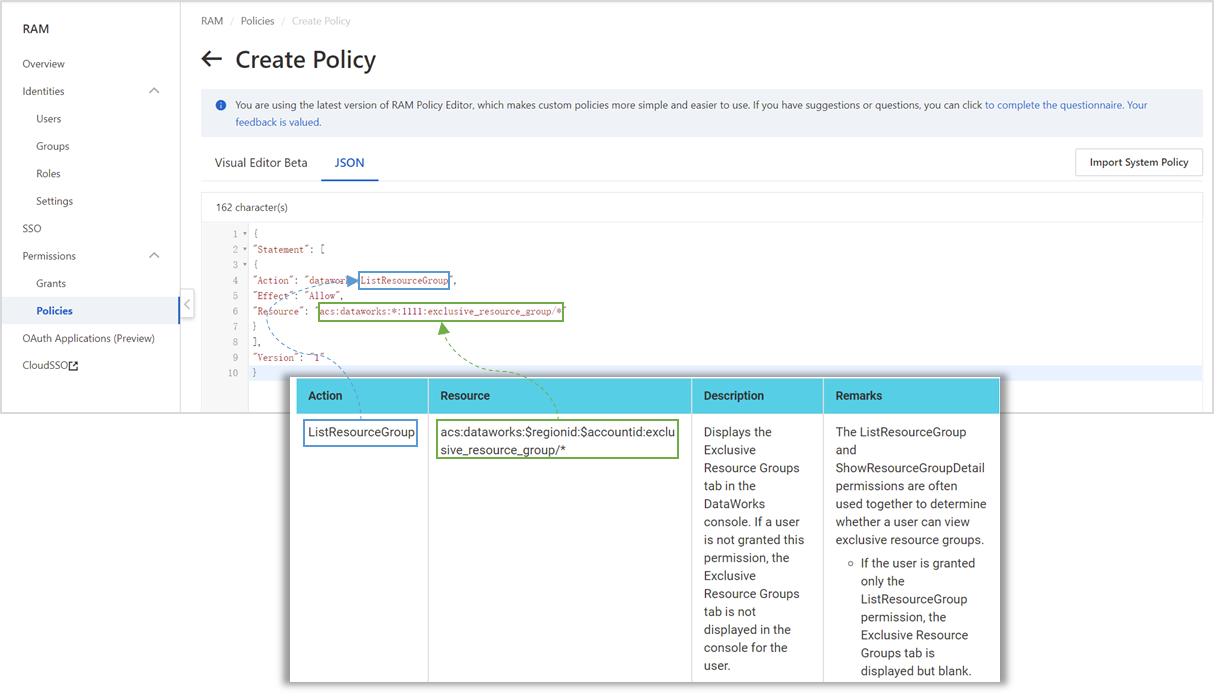
Console entity-level policy: Configure the policy as shown below.
Policy element
How to configure
ActionUse the Action value from the corresponding control item in Console entity-level control policies. The format is shown in the preceding figure.
ResourceUse the Resource value from the corresponding control item in Console entity-level control policies. Replace each
$placeholder with an actual value — for example, replace$regionidwith an actual region ID and$accountidwith the UID of your Alibaba Cloud account. To limit a policy to a specific workspace, replace the wildcardworkspace/*withworkspace/workspaceid.