Dynamic desensitization alters only the final displayed query result data without changing the underlying data. It uses rules to manage the data range and the specific desensitization methods. This topic explains how to create and manage dynamic desensitization rules.
Limit
Currently, only Dataphin table fields support desensitization.
Permission
Security administrators and global custom roles with permissions for desensitization rules and data classification management can create and manage dynamic desensitization rules.
Primary directory administrators can configure desensitization rules for the data classifications they oversee.
Owners of desensitization rules can manage the rules they are responsible for, subject to data classification management permissions.
Introduction to desensitization rules
Dynamic desensitization rules are commonly used in scenarios involving queries of sensitive production data. They apply data transformation or encryption to data objects that meet specified conditions, ensuring the protection of sensitive privacy data.
If a field in a table within the associated section or project is marked as sensitive in the selected data classification, it will be desensitized during data writing or querying based on the chosen method and algorithm.
Create dynamic desensitization rules
On the Dataphin home page, in the top menu bar, select Administration > Data Security.
In the navigation pane on the left, select Sensitive Data Protection > Desensitization Rule. On the Desensitization Rule page, click the Dynamic Desensitization Rule tab, then click the + Create Dynamic Desensitization Rule button.
In the Create Dynamic Desensitization Rule dialog box, configure the parameters.
Parameter
Description
Rule Name
Enter the name of the dynamic desensitization rule, such as ID number desensitization.
Rule Desensitization Description
Custom rule desensitization remarks, not exceeding 200 characters. For example, used to read production environment data in the development environment.
Data Class
You can select the data classification you have management permissions for, such as /Personal Information/Basic Personal Information/ID Card.
Associated Section
Supports selecting the data range to be desensitized through the associated section. You can choose All or Enumeration.
Associated Project
Supports selecting the data range to be desensitized through the associated project. You can choose All or Enumeration.
Scenario
Select the application scenario for data desensitization. You can choose Write Into Dev Table or Data Query application scenarios.
Write Into Dev Table: Desensitize the query results of sensitive data from the source table before writing them into the development table to prevent sensitive data from the production environment from being leaked. In special cases, writing the Basic table with a personal account is considered writing to the development table.
Data Query: For data queries that do not participate in production environment scheduling (such as one-time task runs, ad hoc queries, and analysis queries), the query results of the select statement are desensitized before being displayed. This ensures the security of sensitive data as much as possible without affecting the normal operation of production environment tasks.
NoteTo better protect data, it is recommended to enable the Write Into Dev Table and Data Query application scenarios.
To keep the original value of the development data for association analysis, it is recommended to achieve precise control through the desensitization whitelist. Only in specified scenarios can plaintext be written into the data table, and the desensitization method is configured as display desensitization.
Desensitization Method
Desensitization methods include Mask On Query and Mask On Display.
Mask On Query: Desensitization is performed when the data is queried. During the SQL processing, the desensitized result is used, providing better protection for the data.
Mask On Display: Desensitization is performed when the data is finally displayed externally. During the SQL processing, the original text is used, which supports simple conditions such as where/join, making it more user-friendly for business use. Note that if a UDF (user-defined function) is used on sensitive fields (such as substring), it will trigger desensitization downgrade, and the generated field will be uniformly downgraded to ***.
Masking Algorithm
Algorithms marked with
 are advanced algorithms that require the security function to be installed in the project where the data is located to be used. Otherwise, they will be downgraded to the default desensitization method (md5). Desensitization algorithms include Masking, Hashing, Encryption, and Others.Note
are advanced algorithms that require the security function to be installed in the project where the data is located to be used. Otherwise, they will be downgraded to the default desensitization method (md5). Desensitization algorithms include Masking, Hashing, Encryption, and Others.NoteIf the compute engine is Doris, you must use Apache Doris v2.1.x or later to use the Birthday, Mobile Phone, Mobile Phone (Hidden Length), Fixed-line Phone, Fixed-line Phone (Hidden Length), SHA256, SHA384, and SHA512 masking algorithms.
Hashing Desensitization
Algorithms that require desensitization key configuration include Hashing Desensitization - Salted SHA256, Hashing Desensitization - Salted SHA384, Hashing Desensitization - Salted MD5, and Hashing Desensitization - Salted SHA512.
Masking Key: The key is a required parameter for salted hashing algorithms and has no strict format requirements.
Masking
Masking-keyword Replacement
Requires configuration of regular expression and replacement string parameters for the masking mask.
Masking Mask - Custom Mask, Masking Mask -Custom Mask (custom Replacement Value)
Requires configuration of the masking mask parameter group (parameters include the following: desensitization start position, desensitization end position, desensitization replacement content; desensitization parameters can be added or reduced in pairs).
Encryption: When the compute engine is MaxCompute, the encryption desensitization algorithm is supported.
If you select FPE Native Encryption With Format Preservation, you need to configure the encryption dictionary and tweak. If you select FPE Encryption With Format Preservation, you need to configure the encryption range. For more configuration details, see Configure Encryption Transform Widget.
Encryption Dictionary: Symbols used for encrypting characters, supporting System Built-in (including Numbers, Uppercase Letters, Lowercase Letters, Numbers + Uppercase Letters, Numbers + Lowercase Letters, Numbers + Letters, Special Symbols) and Custom.
Tweak: After configuration, the same plaintext can generate different ciphertexts under different circumstances using the same key, improving the uniqueness and security of the ciphertext to some extent. Supports any character.
Encryption Range: Supports encrypting specified character start and end positions or all characters. The encryption and decryption areas must remain consistent; otherwise, the decryption result may not match the raw data.
Abnormal Compatibility: If issues such as plaintext not meeting encryption and decryption algorithm requirements, mismatched encryption and decryption keys, or inconsistent encoding formats occur, the plaintext data will be processed according to the selected policy. Supports selecting Return Empty Value, Return Plaintext, Throw Exception.
No need to configure an encryption key; the system key will be used for encryption to prevent the desensitized data from being decrypted and causing sensitive data leakage.
You can test the effects of the algorithms. For more information, see Test a security algorithm.
For more information about security algorithms, see Security algorithms and Security algorithm examples.
For more information about the data masking algorithms supported by different compute engines, see Data masking methods supported by different compute engines.
Effective Status
Select Enable or Disable to set the effective status of the desensitization rule.
Click OK to complete the creation of the dynamic desensitization rule.
Default desensitization policy
The default desensitization policy serves as the standard sensitive data protection policy, providing unified security protection for sensitive data without the need for separate rules.
Only security administrators can configure the default desensitization rules.
On the Desensitization Rule page, click the Dynamic Desensitization Rule tab, then click the Default Masking Policy button.
In the Default Masking Policy dialog box, configure the parameters.
Parameter
Description
Data Sensitivity Level
The data sensitivity levels, from lowest to highest, are: Public (L1) Or Higher, Internal (L2) Or Higher, Confidential (L3) Or Higher, and Top Secret (L4) Or Higher. To create a new data sensitivity level, see Create a data sensitivity level.
Masking Algorithm
The available masking algorithms are: Return An Empty Value, Return An MD5 Hash Value, Return A Fixed-length String Of Asterisks, and No Masking.
Click OK to finalize the default desensitization policy.
View dynamic desensitization rules
You can view the details of dynamic desensitization rules and perform actions such as editing, changing the owner, or deleting them.
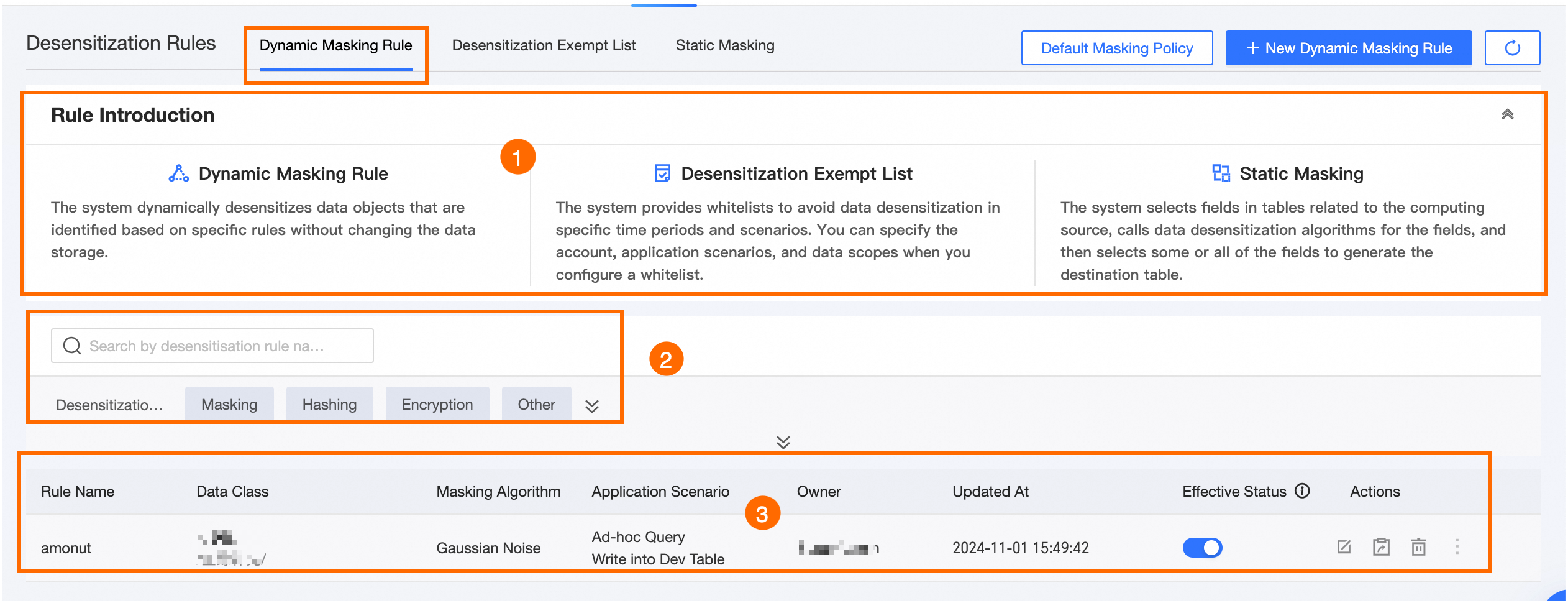
Area | Description |
① Introduction to dynamic desensitization rules | Provides an introduction to dynamic desensitization rules, dynamic desensitization whitelists, and static desensitization rules. |
② Filter and search area | You can perform a fuzzy search by desensitization rule name or data classification. You can also filter precisely by Desensitization Type or Scenario. |
③ Dynamic desensitization rule list | The list shows the name, data classification, desensitization algorithm, application scenario, owner, update time, and status for each desensitization rule. In the Actions column, you can Edit, Change Owner, Delete, View Desensitization Algorithm, and View Desensitization Whitelist.
|