Security algorithms employ hashing, redaction, encryption, and decryption to protect sensitive data, such as names and account numbers, while preserving the original data format. This topic explains how to access and evaluate the system's integrated security algorithms.
View security algorithms
Navigate to the Dataphin home page, and from the top menu bar, select Administration > Data Security.
In the left-side navigation pane, choose General Configuration > Security Algorithm to open the Security Algorithm page.
Parameter
Description
Algorithm Name
The name of the security algorithm.
Algorithm Type
The type of security algorithm.
Function Description
A description of the security algorithm's functionality.
Desensitization Example
An example demonstrating how the security algorithm masks data.
Implementation Method
The implementation method is categorized into Database Built-in Function and Security Policy Algorithm Package.
Database Built-in Function: Utilizes the database's native functions for data masking, eliminating the need for an algorithm package installation in the project where the task is executed. However, some advanced masking methods may not be supported by this approach.
Security Policy Algorithm Package: Employs Dataphin's integrated algorithm package for masking or encryption and decryption. This requires enabling the security policy and installing the algorithm package in the project where the task is executed. If not installed, the default masking policy will be applied.
Corresponding Function/algorithm
Requires the installation of the security desensitization policy algorithm in the project where the task is executed.
Security algorithm description
The Security Algorithm page lists the algorithms supported by Dataphin, including hash algorithms, redaction masks, and encryption and decryption algorithms. You can review each algorithm's introduction and select the appropriate one for testing. For more information, see test security algorithms.
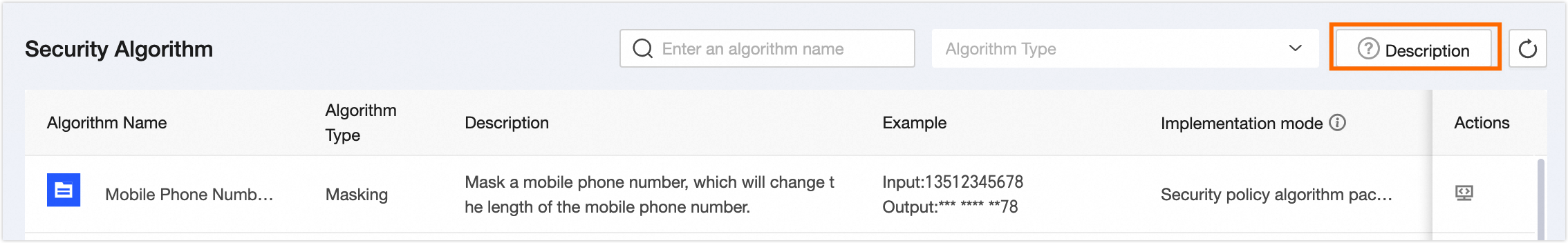
To learn how to use the algorithm functions, click the Description button:
Install Asset Security Policy: Desensitization algorithms are security features within the project. Some engines require the installation of the asset security policy before desensitization can occur. Others use built-in functions and can desensitize data directly. For details, refer to project security policy, desensitization methods supported by different engines.
NoteFor compute engines with built-in functions, such as AnalyticDB for PostgreSQL and Hologres, installing an algorithm package is not necessary.
Select Algorithm: Choose an algorithm based on the scenario requirements. For desensitizing sensitive data, consider redaction or hashing algorithms. For encrypted storage and transmission of data, where retrieval of the original value is necessary, opt for symmetric or asymmetric encryption algorithms. For more details on the various security algorithms, see security algorithm description.
Register Key: For key-requiring algorithms, such as symmetric encryption, register the key in advance through key management. For more information, see key management.
Reference Function: Reference security functions in SQL statements when scripting data processing tasks or conducting ad hoc queries in the development module. You can also select the necessary security functions when configuring desensitization rules.
Test security algorithms
On the Security Algorithm page, click Test in the operation column next to the desired algorithm to initiate a test.
In the Test Security Algorithm dialog box, input the content for testing.
For example, to test a security algorithm for Chinese names: Enter "Zhang San" in the content to be desensitized, click the arrow
 , and observe "*San" as the output value.
, and observe "*San" as the output value.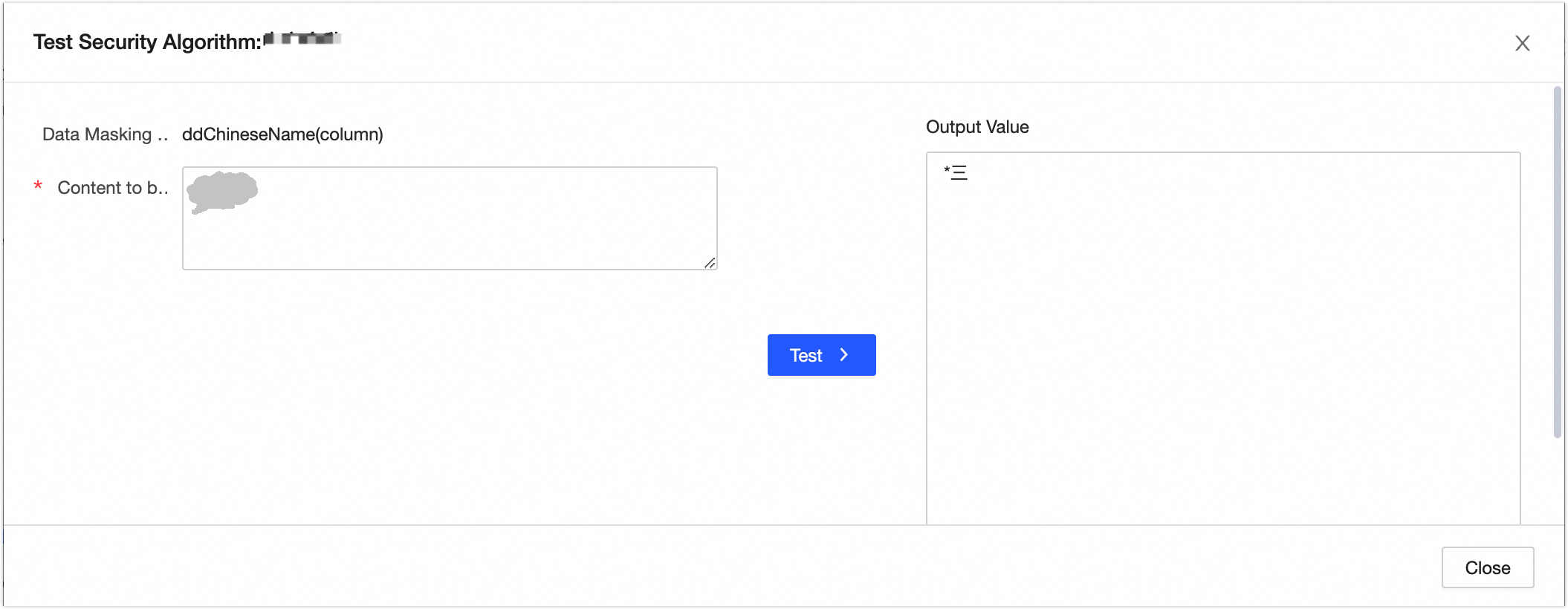
For the DES native encryption algorithm, configure the following parameters:
Plaintext: The input length must be a multiple of 8 bytes.
Key: For encryption components in integration tasks, use the system-managed key without entering the key value to ensure security. When using the algorithm for encryption and desensitization in a code task, directly input the key value. Enhance key security by using the Account Password type of global variable. Accepts 8-digit numeric or character inputs.
Encryption Mode: Supports ECB, CBC, CFB, CTR, OFB modes. Ensure consistency in encryption and decryption settings. For more on encryption and decryption algorithms, see security algorithm example.
Padding: Supports NoPadding, PKCS5Padding, PKCS7Padding. Maintain consistency in encryption and decryption configurations.
Offset: Also known as IV. Different IVs produce distinct encrypted strings. The IV must be an 8-digit number. Use the same IV for both encryption and decryption.
Encoding Format: Convert binary data to a text format for safe transmission, storage, and display across environments. Decode the encoded ciphertext before decryption to restore the original binary data. Supports Base64 and Hex output methods.
Click the arrow
 to view the output value.
to view the output value.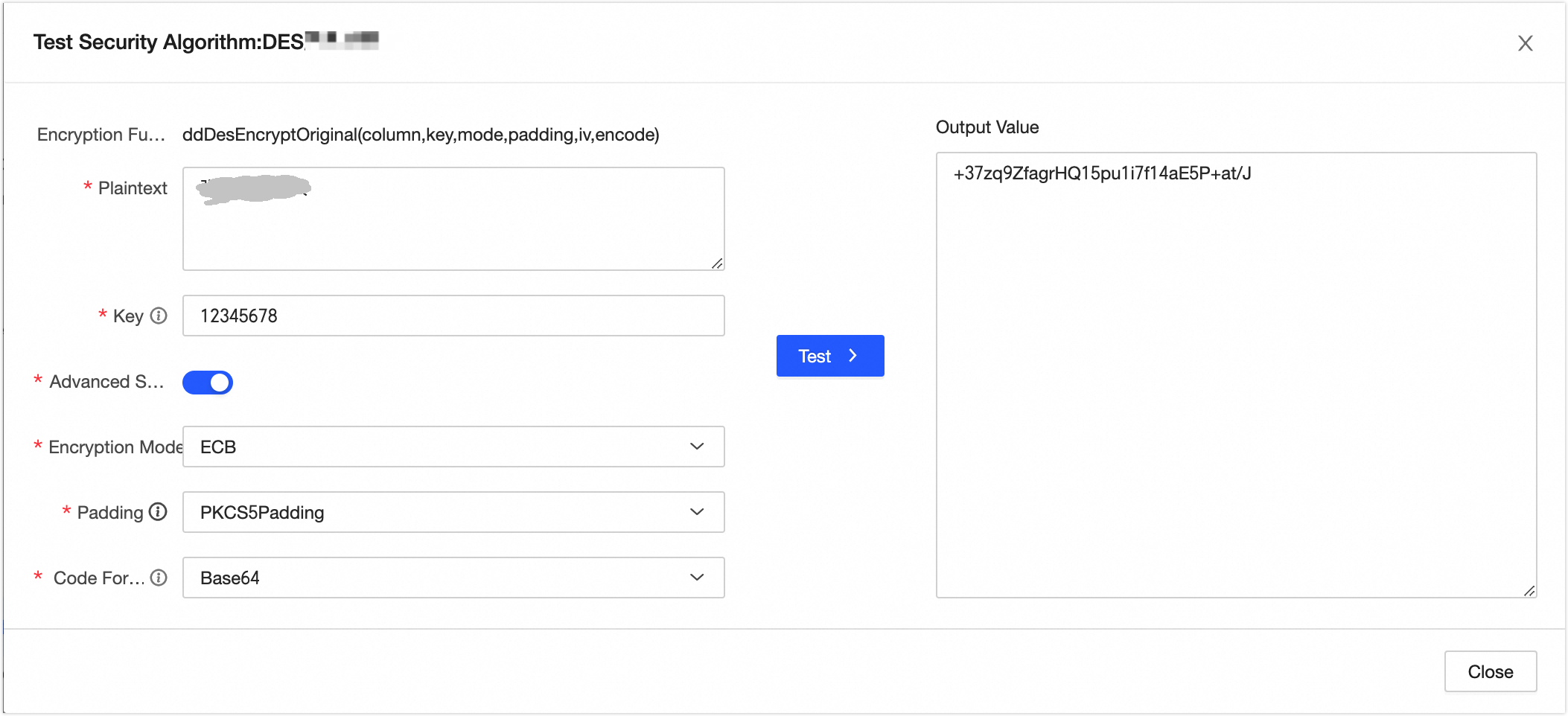
If the test results meet your expectations, select Close.