Solution Overview
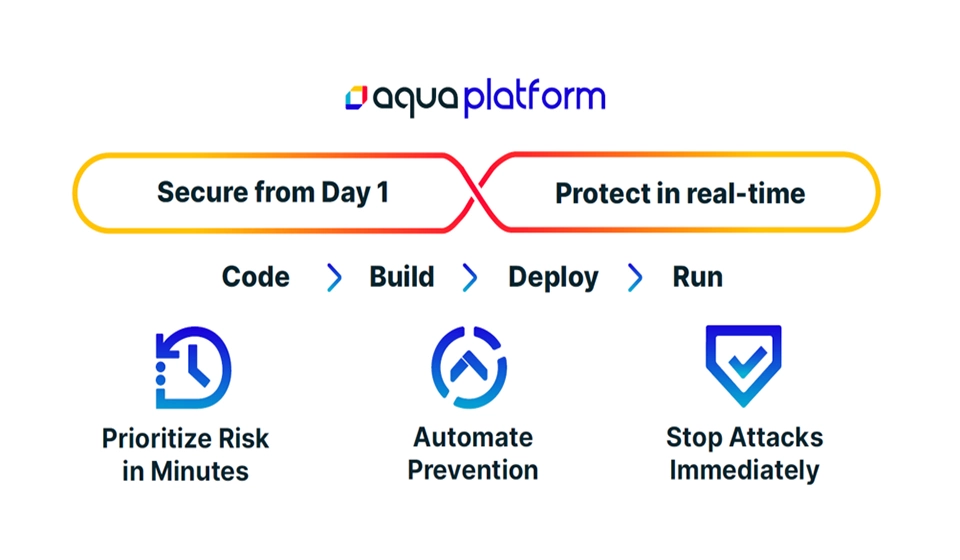
Aqua Security enables Alibaba Cloud customers to securely build, scale and automate cloud native applications as well as ensure that controls, configurations and account settings across their environments conform to security best practices and compliance requirements.
Aqua facilitates security and DevOps collaboration for the cloud native journey, embeds security and assurance into Alibaba Cloud build and artifact pipelines, validates and remediates Alibaba Cloud infrastructure configurations, and protects workloads at runtime - including detecting malware, unauthorized changes to images, code injection and supply chain attacks.
Solution Highlight
-
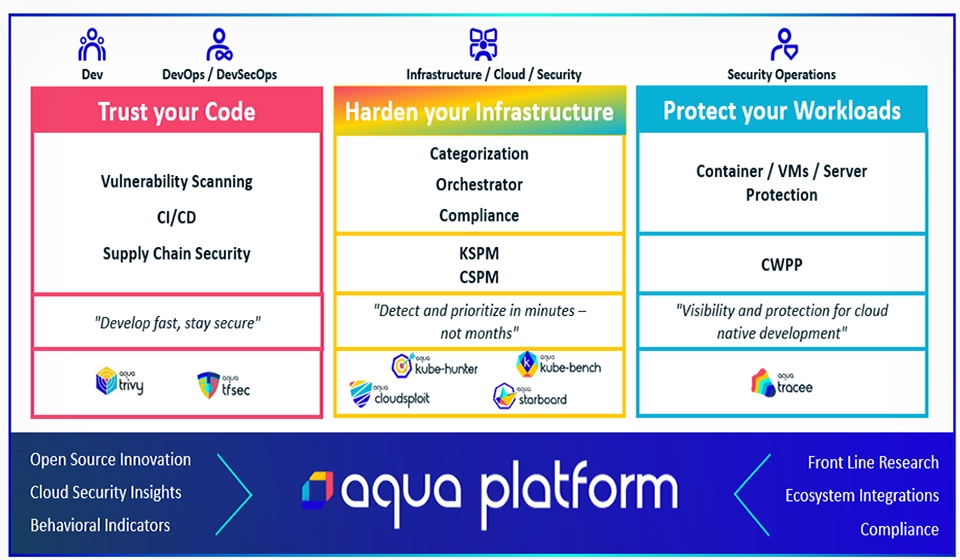
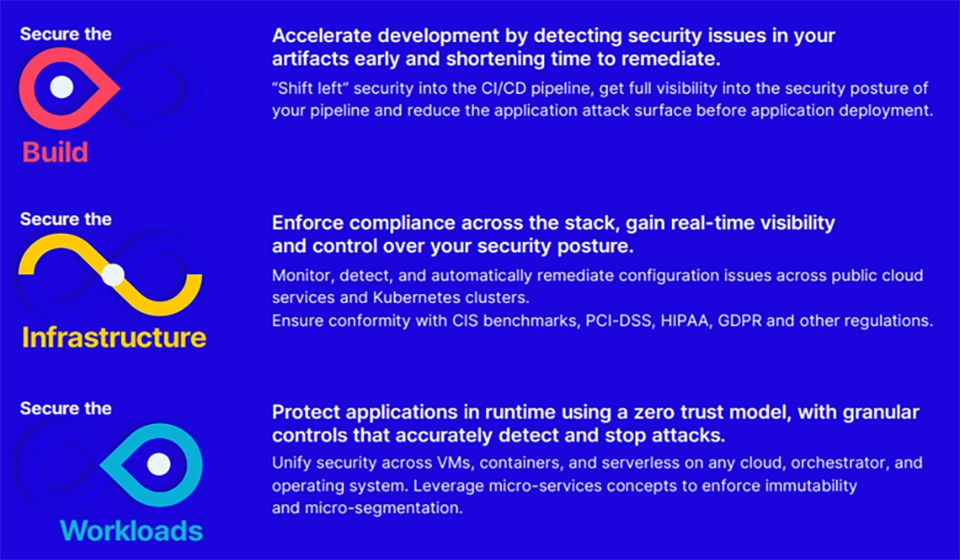
Secure the Build
Release and update software at DevOps speed with security automation. Detect vulnerabilities and malware early and fix them fast, and allow only safe artifacts to progress through your CI/CD pipeline.
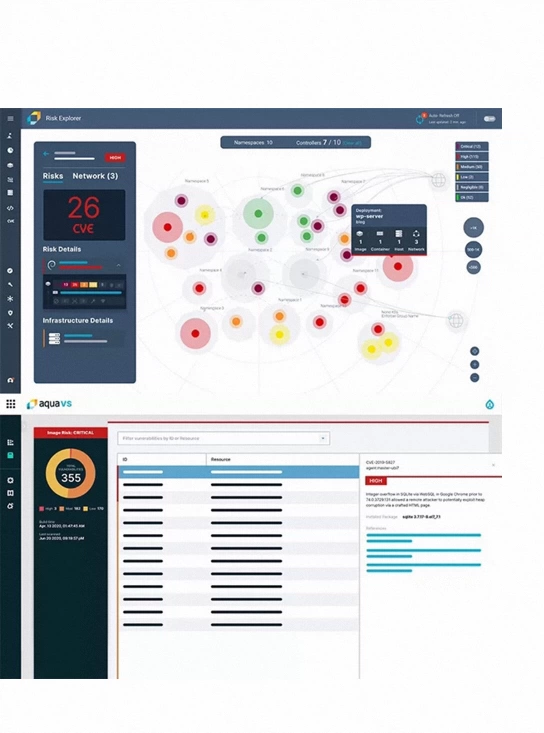
•Vulnerability Scanning
•Dynamic Threat Analysis (DTA)
•Automating DevSecOps
•Supply Chain Security (Secure SBOM) -
Secure the Infrastructure
Deploy your cloud native applications on any infrastructure while ensuring that cloud services, orchestration and hosts are securely configured and in compliance.
•Cloud Security Posture Management (CSPM)
•Kubernetes Security Posture Management (KSPM)
•Compliance and Risk: reporting and remediation
•Admission Control and zero-trust enablement -
Secure the Workloads
Detect and block policy violations in your workloads using granular controls that are natively architected to provide the optimal response, at scale.
•Container / Serverless / VM Security
•Drift-prevention without profiling
•Cloud Workload Protection (CWPP)
•Cloud Native Detection and Response (CNDR)
Customer Reference
Kakaku.com Improves Security and Operational Efficiency with Aqua
Kakaku.com, with headquarters in Tokyo, Japan, offers internet services that enhance online access to information. Kakaku.com serves a diverse group of clients with product offerings supporting multiple markets.
Problem Overview
• Needed to increase speed of delivery through use of containers and cloud services without sacrificing security.
• Needed to support Kubernetes on-premise as well as in cloud environments (hybrid cloud).
• Threats were bypassing static container scanning and could still emerge in runtime post deployment
Solution
With Aqua, Kakaku.com had the perfect solution for their Kubernetes environments:
• Works seamlessly with their CI/CD pipeline
• Provides automated security
• Scans for any vulnerabilities during the build phase
• Ensures container image integrity in their operating environment
• Deploys easily on Kubernetes clusters for runtime security
• Secures Linux and Windows environments
• Realizes support through a local certified Aqua partner
Benefits

Improve operational efficiency 6x

Provide a robust and consistent security response

Employ security that is effective and easier to manage

Confidently detect vulnerabilities in images

Ensure security throughout Operations

Eliminate human error when addressing security tasks
Disclaimer
- Please note that all solutions and marketing contents presented on this page are provided by Aqua and Alibaba Cloud is not liable to or responsible for their accuracy, condition, quality, durability, performance, reliability, merchantability or fitness for a particular purpose, or non-infringement.