HTTP flood protection is enabled by default when you add a website to Web Application Firewall (WAF). It inspects all incoming requests and blocks HTTP flood attacks, returning a 405 Method Not Allowed error when an attack is detected. If you observe slow response times or abnormal traffic indicators during an attack, you can switch to a more aggressive protection mode.
Prerequisites
Before you begin, ensure that you have:
A WAF instance
A website added to WAF (see Tutorial)
Set the protection mode
Log on to the WAF console.
In the top navigation bar, select the resource group and the region where your WAF instance is deployed. Valid values: Chinese Mainland and Outside Chinese Mainland.
In the left-side navigation pane, choose Protection Configurations > Website Protection.
At the top of the Website Protection page, select the domain name you want to configure from the Switch Domain Name drop-down list.

On the Access Control/Throttling tab, locate the HTTP Flood Protection section and configure the following parameters.
Parameter Description Status Enable or disable HTTP flood protection. Protection is enabled by default after you add a website to WAF. When enabled, all requests to your website are inspected. To exempt specific requests from inspection, create an Access Control/Throttling whitelist rule. For more information, see Configure a whitelist for Access Control/Throttling. Mode The protection mode. Two modes are available:
Prevention — Blocks only suspicious requests and keeps false positives low. Use this mode when traffic is normal. If an active attack is not stopped and you observe slow response times or abnormal traffic, CPU, or memory indicators, switch to Protection-emergency.
Protection-emergency — Blocks HTTP flood attacks aggressively. This mode has a high false positive rate and applies to web pages and HTML5 pages only. Do not use this mode for APIs or native applications, as it causes a large number of false positives. For API and native application traffic, create a custom protection policy instead. For more information, see Create a custom protection policy.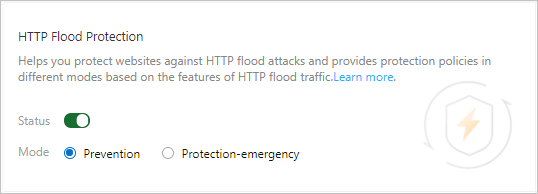
What's next
If Protection-emergency mode does not stop a large volume of attacks, check whether the attack traffic originates from WAF's back-to-origin IP addresses. If your origin server is being attacked directly, restrict inbound traffic to WAF's back-to-origin IP addresses only. For more information, see Configure protection for an origin server.
To strengthen protection while keeping false positives low, use a custom protection policy. For more information, see Create a custom protection policy.