When a website is added to Web Application Firewall (WAF), all traffic passes through WAF before reaching the origin server. However, if the origin server's public IP address is exposed, attackers can bypass WAF and send requests directly to the origin. To prevent this, configure access control policies on the origin server so that it only accepts traffic from WAF back-to-origin CIDR blocks.
This topic uses an Elastic Compute Service (ECS) instance behind a Server Load Balancer (SLB) instance as the example origin server.
-
Traffic forwarding begins as soon as the website is added to WAF, regardless of whether origin server protection is configured.
-
If the ECS and SLB instances are added to WAF in Transparent Proxy Mode, all traffic on the redirection ports is automatically routed through WAF. Attackers cannot bypass WAF in this mode, so origin server protection is not required.
Risks of origin server access control
Incorrect access control policies can disrupt services. Review these risks before proceeding:
-
All hosted domains must be added to WAF. If any domain hosted on the ECS or SLB instance is not added to WAF, attackers can use that domain to reach the origin server and affect services for all other domains on the same server.
-
WAF cluster failover bypasses access control. If the WAF cluster fails, traffic is forwarded directly to the origin server to maintain service continuity. If security group rules or SLB listener whitelists are configured to allow only WAF traffic, the origin server becomes unreachable during the failover.
-
Back-to-origin CIDR blocks change over time. WAF periodically updates its back-to-origin CIDR blocks. If the new blocks are not added to the security group rules or SLB listener whitelists, HTTP 5XX errors may occur. Check the WAF console regularly for updates and adjust access control policies promptly.
-
Remove access control policies before decommissioning WAF. If WAF is no longer in use, delete all origin server access control policies before switching traffic back to the origin. Otherwise, traffic cannot reach the origin server and services are interrupted.
Prerequisites
Before you begin, make sure that you have:
-
An Alibaba Cloud ECS instance added to an SLB instance as the origin server. For more information, see What is ECS and What is SLB?
-
All domain names hosted on the ECS or SLB instance added to WAF in CNAME record mode. For more information, see Add a domain name to WAF
Check whether the origin server IP address is exposed
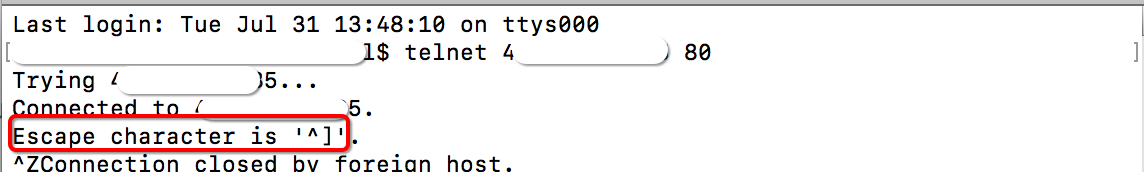
Use Telnet from a host outside Alibaba Cloud to connect to the origin server's public IP address on its service port.
-
Connection succeeds: The IP address is exposed. Attackers who obtain this IP can bypass WAF and send requests directly to the origin.
-
Connection fails: The IP address is not exposed.
Example: Test connectivity to the origin server on ports 80 and 8080. If both connections succeed, the IP address is exposed.
Get the WAF back-to-origin CIDR blocks
WAF back-to-origin CIDR blocks are updated periodically. Monitor update notifications and add new CIDR blocks to security group rules and whitelists promptly to avoid service interruptions.
-
Log on to the WAF console. In the top navigation bar, select the resource group and region (Chinese Mainland or Outside Chinese Mainland) of the WAF instance.
-
In the left-side navigation pane, click Onboarding.
-
On the CNAME Record tab, click Back-to-origin CIDR Blocks.
-
In the Back-to-origin CIDR Block dialog, click Copy.
Configure ECS security group rules
Create two security group rules: one to allow inbound traffic from WAF back-to-origin CIDR blocks, and one to deny all other inbound traffic.
Open the security group settings
-
Log on to the ECS console.
-
In the left-side navigation pane, choose Network & Security > Security groups.
-
In the upper-left corner of the top navigation bar, select the region of the ECS instance.
-
Find the target security group and click Manage Rules in the Operation column.
-
Select a rule direction:
-
Virtual Private Cloud (VPC): Click the Inbound or Outbound tab.
-
Classic network: Click the Inbound, Outbound, Internet Ingress, or Internet Egress tab.
-
Add an allow rule for WAF traffic
-
On the Inbound tab, click Add Rule.
-
Configure the following parameters and click Save.
Parameter
Description
Authorization policy
Select Allow.
Priority
Enter 1 (highest priority).
Protocol Type
Select Custom TCP.
Port number range
Select HTTP (80) and HTTPS (443).
Authorization Object
Paste the WAF back-to-origin CIDR blocks.
Description
Example: Allow inbound traffic from WAF back-to-origin CIDR blocks.
If the origin server communicates with other applications on IP addresses and ports outside the WAF back-to-origin CIDR blocks and standard HTTP/HTTPS ports, add those IP addresses and ports to the security group rules as well.
The allow rule has the highest priority, so all inbound traffic from WAF back-to-origin CIDR blocks is permitted.
Make sure all WAF back-to-origin CIDR blocks are included. Missing CIDR blocks cause access failures.
Add a deny rule for all other traffic
-
On the Inbound tab, click Add Rule.
-
Configure the following parameters and click Save.
Parameter
Description
Authorization policy
Select Deny.
Priority
Enter 100 (lowest priority).
Protocol Type
Select Custom TCP.
Port number range
Select HTTP (80) and HTTPS (443).
Authorization Object
Enter
0.0.0.0/0. This matches all CIDR blocks.Description
Example: Block all inbound traffic.
After both rules are in place, the ECS instance blocks all inbound traffic except requests from WAF back-to-origin CIDR blocks. All service traffic must pass through WAF before reaching the ECS instance.
Configure SLB access control policies
If the origin server is behind an SLB instance, configure a whitelist on the SLB listener to allow only WAF traffic.
The following example uses a Classic Load Balancer (CLB) instance. For an Application Load Balancer (ALB) instance, see Access control and adjust the steps accordingly.
Create an access control list
-
Log on to the CLB console.
-
In the top navigation bar, select the region of the CLB instance.
-
In the left-side navigation pane, choose Classic Load Balancer (CLB) > Access Control.
-
On the Access Control page, click Create ACL.
-
In the Create ACL panel, configure the following parameters and click Create.
Parameter
Description
ACL Name
Enter a name. Example: WAF back-to-origin CIDR blocks.
Add Multiple Addresses/CIDR Blocks and Descriptions
Paste all WAF back-to-origin CIDR blocks, one per line. The copied list uses commas as separators. Replace commas with line breaks before pasting.
Configure listener whitelists
-
In the left-side navigation pane, choose CLB > Instances.
-
On the Instances page, find the target instance and click its ID.
-
On the Listener tab, find the listener to configure. Click the
 icon in the Operation column, then click Configure ACL. Select the listener based on the services protected by WAF:
icon in the Operation column, then click Configure ACL. Select the listener based on the services protected by WAF:-
HTTP services: Select the HTTP listener.
-
HTTPS services: Select the HTTPS listener.
-
Both HTTP and HTTPS services: Select both listeners.
-
-
In the Configure Access Control panel, turn on Enable Access Control and configure the following parameters.
Parameter
Description
Access Control Mode
Select Whitelist: Allows Specified IP Addresses to Access the ALB Instance to allow only specific IP addresses.
Select ACL
Select the ACL created for WAF back-to-origin CIDR blocks.
After the whitelist is applied, the CLB instance only accepts inbound traffic from WAF back-to-origin CIDR blocks.
Verify the configuration
After configuring security group rules or SLB listener whitelists, verify that the configuration is in effect:
-
From a host outside Alibaba Cloud, use Telnet to connect to the origin server on ports 80 and 8080.
-
Check the result:
-
Cannot connect on port 80 or 8080, but the service runs normally: The configuration is in effect. Direct access to the origin is blocked, and all traffic is routed through WAF.
-
Can still connect: Review the security group rules and SLB whitelist configuration for missing entries.
-