After you add a website to Web Application Firewall (WAF), you can configure a whitelist for Bot Management to allow trusted access requests of the website to bypass the detection of Bot Threat Intelligence, Data Risk Control, Intelligent Algorithm, and App Protection. This whitelist is used to allow access requests that are blocked by mistake.
Prerequisites
A WAF instance that meets the following requirements is purchased:
The instance uses the subscription billing method.
Bot Management is enabled.
Your website is added to WAF. For more information, see Tutorial.
Background information
Bot Management protects web applications, native applications, and APIs from malicious crawlers. It provides the following detection modules:
Intelligent Algorithm
After the preceding detection modules but Allowed Crawlers are enabled, normal access requests may be blocked by mistake. In this case, you can configure a whitelist to allow trusted access requests to bypass the detection of a specific module in Bot Management.
We recommend that you specify rules for the whitelist as precisely as possible to ensure that only trusted access requests are allowed.
Procedure
Log on to the WAF console.
In the top navigation bar, select the resource group and the region in which the WAF instance is deployed. You can select Chinese Mainland or Outside Chinese Mainland.
In the left-side navigation pane, choose .
In the upper part of the Website Protection page, select the domain name for which you want to configure protection from the Switch Domain Name drop-down list.

Click the Bot Management tab, find the Fine-grained Configuration section, and then click Settings.
Create a whitelist for Bot Management.
On the Bot Management - Whitelist page, click Create Rule.
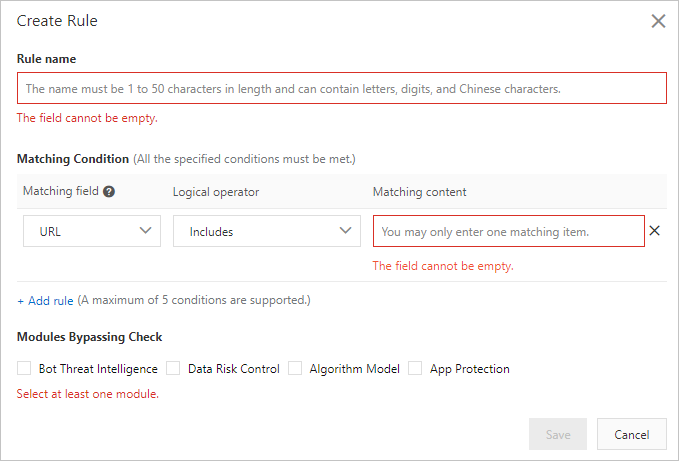
In the Create Rule dialog box, configure the following parameters.
Parameter
Description
Rule name
Specify a name for the rule.
Matching Condition
Specify match conditions for the rule. Click Add rule to add more match conditions. A maximum of five match conditions are allowed. If you specify multiple match conditions, the rule is triggered only after all the match conditions are met.
For more information about match conditions, see Fields in match conditions.
Bypassed Modules
Select the detection modules to bypass after the match conditions are met. Valid Values:
Bot Threat Intelligence
Data Risk Control
Algorithm Model
App Protection
Click Save.
After you create rules for the whitelist, the rules are automatically enabled. You can view created rules in the rule list. You can also disable, edit, or delete rules as required.