Security Center provides integrated container security across your Kubernetes clusters and image repositories. After connecting your container assets, you can view security risks, scan images for vulnerabilities, enable threat detection, and analyze cluster port exposure from a single console.
Edition requirements
Subscription service: Ultimate is required. To upgrade, see Upgrade and downgrade Security Center.
The server's protection edition must be set to Ultimate. For more information, see Attach a protection edition to a server.
Pay-as-you-go service: Host and Container Security must be enabled. To purchase, see Purchase Security Center.
The server protection level must be set to Host and Container Protection. For more information, see Attach a server protection level.
Prerequisites
Before you begin, ensure that you have:
Connected your container assets to Security Center. See Add image repositories and Connect a self-managed Kubernetes cluster
(Optional) Enabled K8s threat detection to view alerts for cluster anomalies. See K8s threat detection for containers
Synchronize assets
Security Center automatically performs a full asset synchronization every morning. For newly added assets, manually trigger a sync before viewing asset data.
Log on to the Security Center consoleSecurity Center consoleSecurity Center consoleSecurity Center console.
In the left navigation pane, choose Assets > Container. In the upper-left corner, select your region: Chinese Mainland or Outside Chinese Mainland.
On the Container page, click the Cluster or Image tab, then click Synchronize Assets.
(Optional) Click Task Management in the upper-right corner. On the Container Asset Synchronization and Synchronize Image Asset tabs, check the progress and status of the sync.
Cluster management
Supported cluster types
Security Center supports the following cluster types:
| Cluster type | Notes |
|---|---|
| ACK managed and dedicated clusters | Alibaba Cloud Container Service for Kubernetes (ACK) managed and dedicated clusters. Security Center performs a full asset sync every morning. New clusters are detected automatically — no manual registration needed. |
| Self-managed Kubernetes clusters | Must be connected manually. See Connect a self-managed Kubernetes cluster. |
View cluster security risks
Log on to the Security Center consoleSecurity Center consoleSecurity Center consoleSecurity Center console.
In the left navigation pane, choose Assets > Container. In the upper-left corner, select your region.
On the Cluster tab, view the number of connected clusters, at-risk clusters, and the full cluster list.
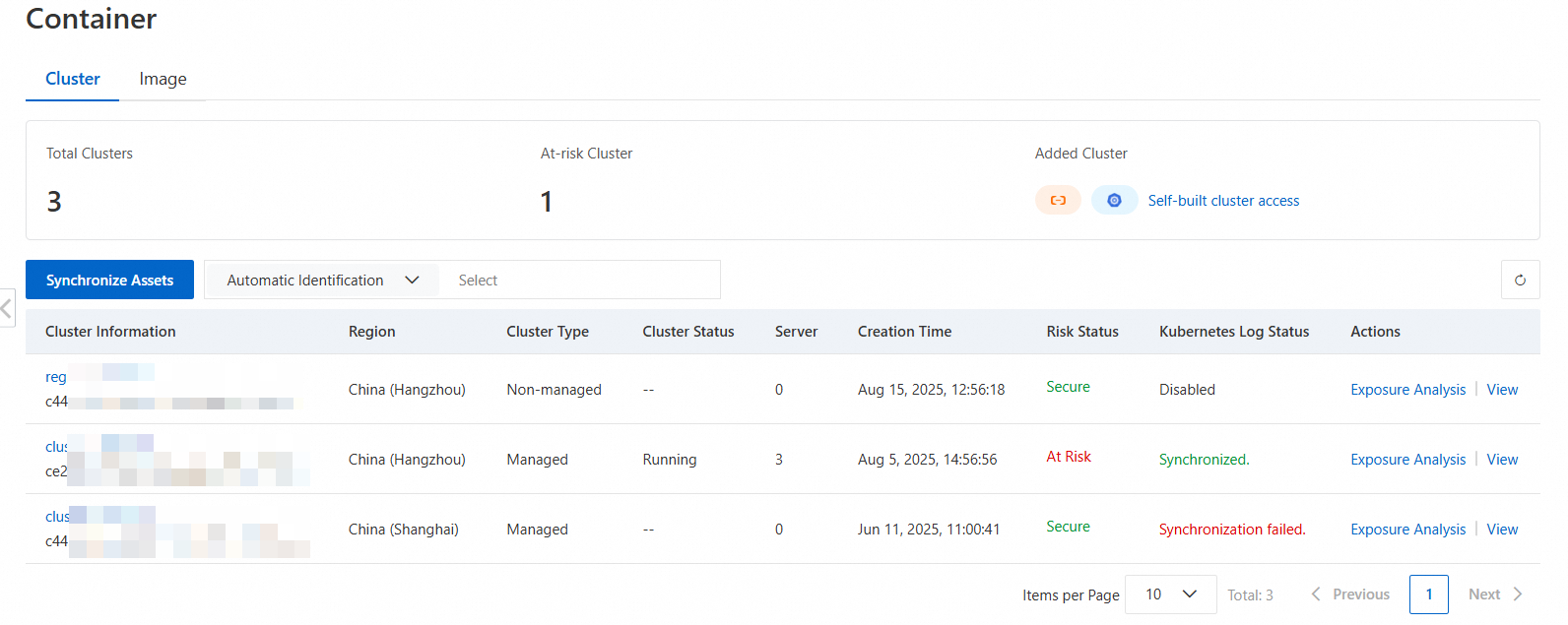
Search for a cluster: Use the search bar to filter by cluster ID, type, or other attributes.
View risk details: Click the cluster name or View in the Actions column to open the risk details page. The page shows statistics and lists for security alerts, vulnerabilities, configuration risks (Kubernetes configuration risks and baseline risks), and container firewall alerts.

Enable K8s log threat detection
K8s log threat detection lets Security Center retrieve cluster log data to identify high-risk operations and attack behaviors, providing deeper security coverage than agent-based detection alone.
For ACK managed and dedicated clusters:
Enable the log audit feature in the Container Service console. See Use the cluster API server audit feature.
Log on to the Container Service Management console. In the left navigation pane, click Clusters.
Click the target cluster name. In the left navigation pane, choose Security Management > Audit.
Follow the on-screen instructions to select a Simple Log Service (SLS) project and enable the feature.
In the Security Center console, enable K8s threat detection for containers.

For self-managed Kubernetes clusters:
See Enable log threat detection.
After enabling the feature, go to the Clusters tab on the Container page. Check the K8s Log Status column for the target cluster to confirm that log threat detection is active.
Analyze cluster port exposure
Exposing container ports to the internet creates attack surfaces for network intrusions and data breaches. Security Center's exposure analysis detects publicly reachable ports across your clusters.
Exposure analysis currently supports ACK managed and dedicated clusters only.
Security Center runs a full exposure analysis on all connected clusters every morning. To run an on-demand analysis, click Exposure Analysis in the Actions column for the target cluster on the Cluster tab.
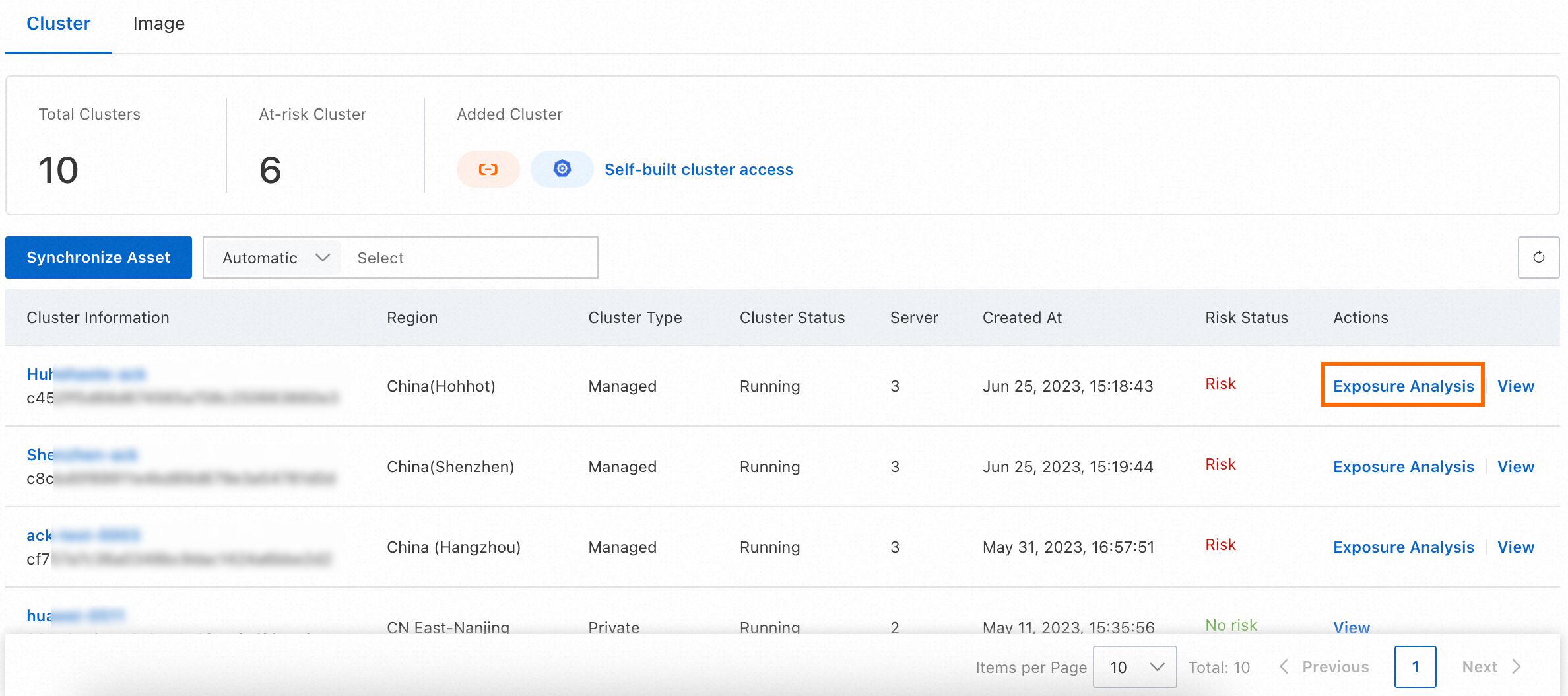
(Optional) Click Task Management in the upper-right corner. On the Container Exposure tab of the Task Management panel, check the progress and details of the exposure analysis.
To view exposure results:
On the Container page, click the target cluster name.
On the cluster details page, click the Container tab and set the Exposed filter to Yes.
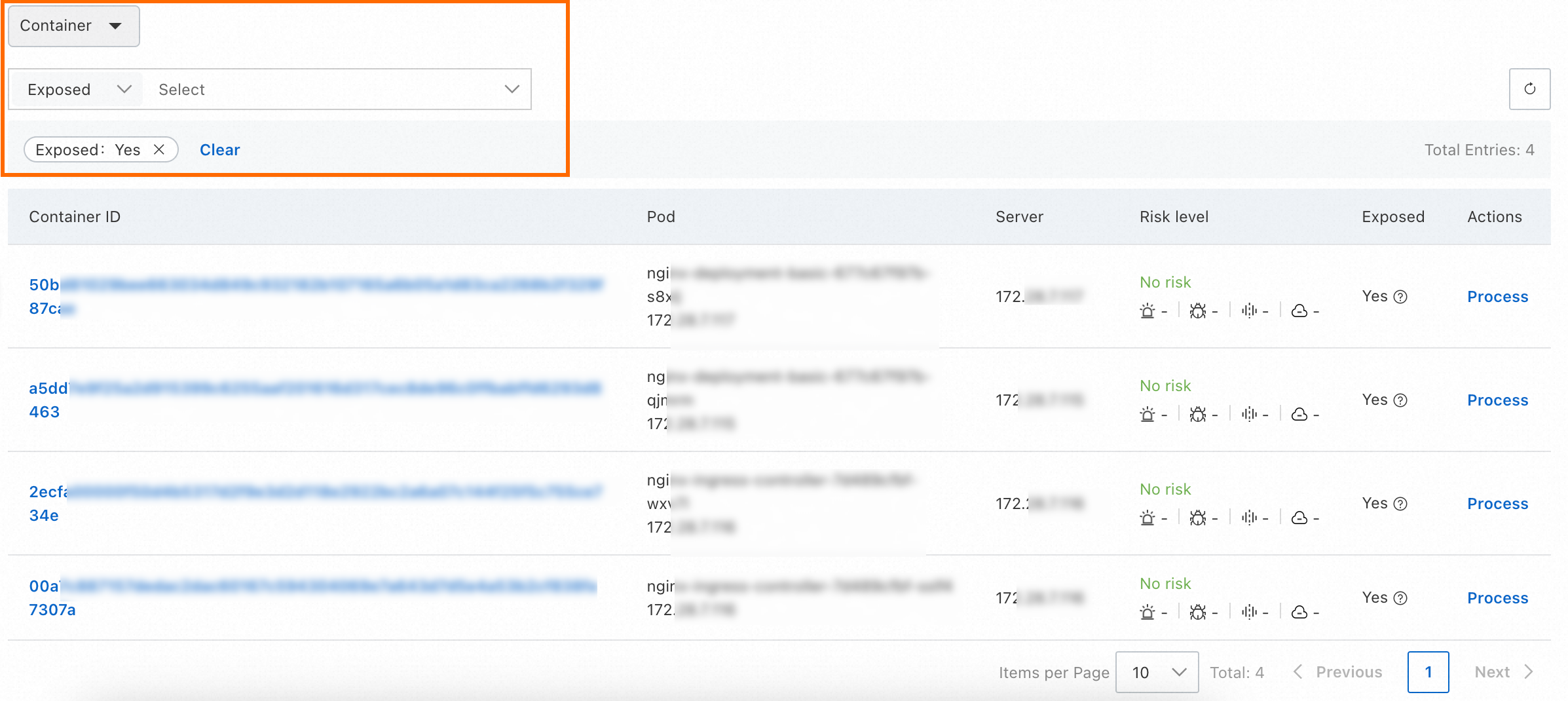
Hover over the
 icon in the Exposed column to see the exposed port details.
icon in the Exposed column to see the exposed port details.
Close any internet-exposed ports that are not in active use to reduce your attack surface.
Image management
View image repositories
Log on to the Security Center consoleSecurity Center consoleSecurity Center consoleSecurity Center console.
In the left navigation pane, choose Assets > Container. In the upper-left corner, select your region.
On the Image tab, view image repository information.

The Overview section shows the number of at-risk images and your Remaining Quota for image security scans.
Increase scan quota: In the Remaining Quota section, click Increase Quota. See Upgrade and downgrade.
Register a private repository: In the Add Third-party Image Repository section, click Add. See Add an image repository.
The repository list shows all repositories connected to Asset Center, including repository name, region, type, and risk status.
Search for a repository: Use the search bar to filter by instance ID, namespace, or other attributes.
View repository details: Click the repository name or View in the Actions column. The details page lists each image with its name, version, size, and risk status. The Created At/Updated At column reflects Security Center's first and most recent sync times, not the local creation and update times of the repository.
View Platform for AI (PAI) image repositories: Apply the Tag > PAI filter in the search bar.
Enable automatic sync for Container Registry Enterprise Edition: Click Synchronize in the Actions column for a repository. Once enabled, assets added to the Container Registry Enterprise Edition instance are automatically synced to the image list in Security Center.
To view or export threat and vulnerability details for a specific image version, go to the repository details page, find the target version, and click Handle in the Actions column.
Scan container images
Image scanning detects vulnerabilities, baseline risks, malicious samples, and sensitive files in your container images.
Log on to the Security Center consoleSecurity Center consoleSecurity Center consoleSecurity Center console.
In the left navigation pane, choose Assets > Container. In the upper-left corner, select your region.
On the Image tab, click Scan Now in the Container Image Scan section.

In the Quick Scan dialog box, select an image type and configure the scan scope, then click OK. For scan scope configuration options, see Perform image security scans.
(Optional) Click Task Management in the upper-right corner. On the Image Scan, Image Risk Fixing, and Container Runtime Image Scan tabs, track scan progress and review repair information.
What's next
Container Asset Overview: View security visualization, asset relationships, and network topology across clusters, containers, images, and applications. See Container Asset Overview.
Container protection settings: Enable K8s threat detection for containers and container escape prevention to protect your runtime environment. See Container protection settings.
Container signing: Sign container images to ensure only trusted images are deployed. See Container signing.
View and fix image risks: Review and remediate system vulnerabilities, application vulnerabilities, baseline risks, and malicious samples detected in your images. See View and fix detected image risks.
Security monitoring: Detect attack behaviors such as malicious image startups, intrusions, container escapes, and high-risk operations. See Use security monitoring.