Container file protection monitors directories and files in your containers in real time. When tampering is detected, Security Center generates an alert or blocks the process — preventing attackers from inserting malicious code or hidden links through container vulnerabilities.
Limitations
Edition requirement: Only the Ultimate edition of Security Center supports this feature. For more information, see Purchase Security Center and Upgrade and downgrade Security Center.
Cluster connectivity: Only clusters connected to Security Center are protected. To protect a self-managed Kubernetes cluster, connect it to Security Center first. For more information, see Connect a self-managed Kubernetes cluster to Security Center.
OS and kernel support: The servers hosting your cluster must run a supported operating system and kernel version. For the full compatibility list, see Supported operating systems and kernel versions.
Protected directories per cluster: The number of protected directories to which a pod label is added in a cluster cannot exceed 10 (counting only enabled rules). Exceeding this limit disables the feature for the entire cluster.
Unique pod labels per cluster: All enabled rules in a cluster can reference at most 10 unique pod labels (after deduplication). Exceeding this limit disables the feature for the entire cluster.
Example: Cluster01 has 12 rules (Rule01–Rule12). Rule01 references Label01, Rule02 references Label02, and so on through Rule10 (Label10). Rule11 and Rule12 both reference Label10. After deduplication, that is 10 unique labels, so the feature works normally. If you add Rule13 that references Label10 and Label11, the deduplicated count becomes 11, and the feature becomes unavailable for Cluster01.
A pod label can be referenced in a rule even if no pod in the cluster carries that label.
Prerequisites
Before you begin, ensure that you have:
The Security Center agent installed on all servers that host your cluster. For more information, see Install the Security Center agent
Create a rule
Log on to the Security Center console. In the top navigation bar, select the region of the asset you want to protect: China or Outside China.Log on to the Security Center console.
In the left-side navigation pane, choose Protection Configuration > Container Protection > Container File Protection.
On the Container File Protection page, click Create Rule.
In the Create Rule panel, configure the following parameters, then click Next. For Whitelist and Excluded File Path: each entry must be no longer than 50 characters; separate multiple entries with semicolons (
;); specify up to 10 whitelist processes and 10 excluded file paths per protected directory. How path matching works Rules use wildcard-based, prefix-aware matching. The following examples use/dir1/testto illustrate the behavior. How each parameter applies matching: When configuring Whitelist and Excluded File Path, follow the principle of least privilege: specify only what is required for normal container workloads, and avoid broad wildcard patterns.Protected File Directory
/dir1/test(exact): Only the/dir1/testdirectory itself is protected. If it is deleted or renamed, an alert is generated or the process is blocked. Subdirectories and files inside are not covered.Whitelist
/dir1/test(exact): Processes spawned by the executable/dir1/testcan modify the protected directory without triggering an alert. Processes spawned by/dir1/test/1.htmlare still subject to the rule.Protected File Directory
/dir1/*with Excluded File Path/dir1/test: The/dir1/testdirectory is excluded. Deleting or renaming/dir1/testdoes not trigger the rule, but modifying content inside/dir1/test/1.htmlstill does.
Start with Alert to verify no false positives are generated, then switch to Block. If a blocked process is required for normal workloads, add it to the Whitelist.
Parameter Description Rule Name Enter a name for the rule. The name must be 6–50 characters long, contain only letters, digits, underscores ( _), or hyphens (-), and start with a letter.Protected File Directory Enter the directory to protect. Each entry must start with /and be no longer than 500 characters. Click Add in the Actions column to add up to 10 directories per rule.Whitelist Enter the processes that are allowed to modify the protected directory, or enter the directories that can be modified. When a whitelisted process modifies the directory, no alert is generated and the process is not blocked. Excluded File Path Enter subdirectories or files within the protected directory that are exempt from protection. Modifications to excluded paths do not trigger alerts or blocking. Action Select what Security Center does when tampering is detected: Alert (generate an alert only, no process is blocked) or Block (generate an alert and block the tampering process). Pattern What it matches What it does not match /dir1/test(exact)/dir1/testonly/dir1/test/1.html,/dir1/test/dir1/2.html/dir1/test*(wildcard)/dir1/test,/dir1/test/1.html,/dir1/test1/1.html/dir1/tes/dir1/test/*.html/dir1/test/index.html,/test/dir1/index.html/dir1/test/file.cssIn the cluster list, select the cluster in the Cluster Name column. In the Pod Tag column, select a pod label, then click OK. Use pod labels that start with
app. In Kubernetes, labels are key-value pairs used to organize resources such as pods, Deployments, and Services. Labels prefixed withappgroup resources by application, making scope management more predictable. For more information, see Recommended labels. If no labels appear in the dropdown, type the label directly. To apply the rule to multiple clusters or multiple pod labels, click Add in the Actions column.
Manage rules
On the Container File Protection page, you can perform the following operations on existing rules.
Enable or disable a rule
Find the rule and toggle the switch in the Enable column.
Edit a rule
Find the rule and click Edit in the Actions column to modify its name, configuration, or scope.
Delete a rule
Deleted rules cannot be restored. Confirm you no longer need the rule before proceeding.
Find the rule and click Delete in the Actions column. Click OK in the confirmation dialog.
View alerting results
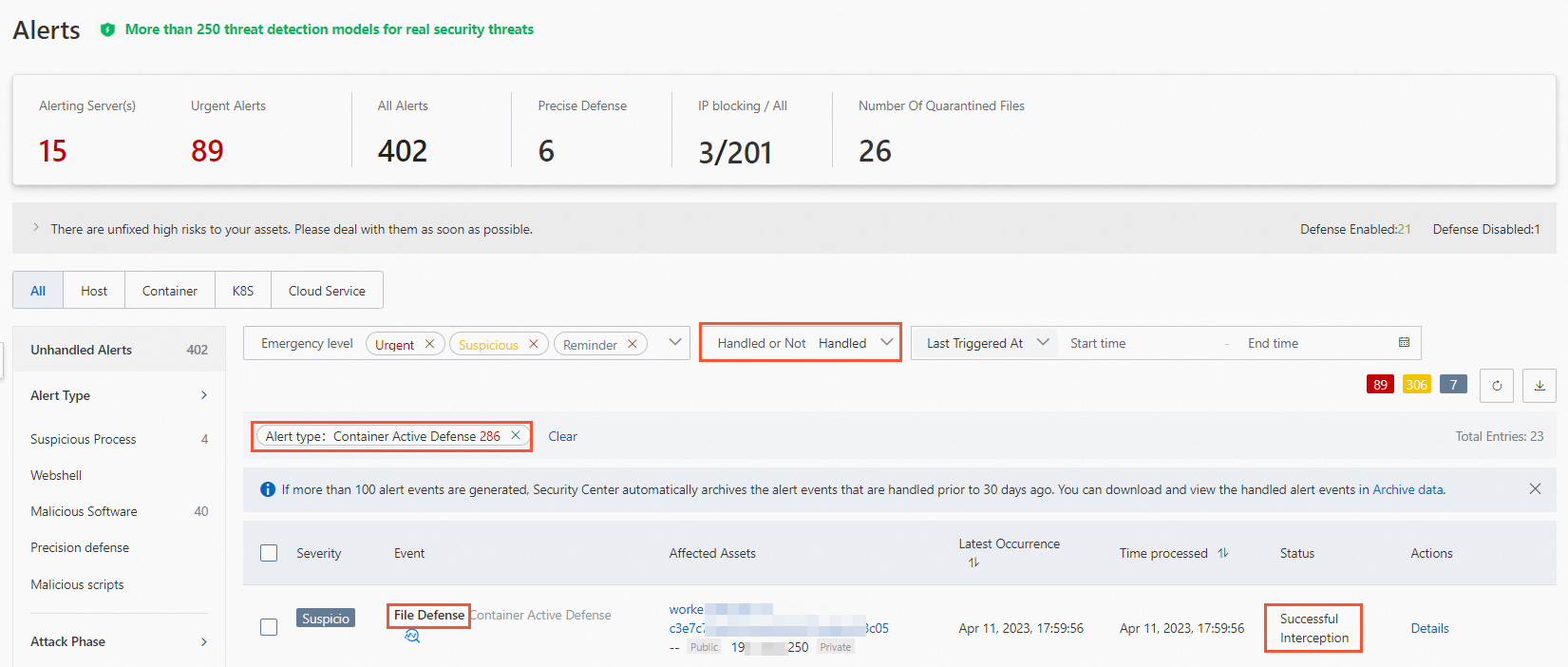
After creating and enabling a rule, go to Detection and Response > Alerts, click the tab, and then set Alert Type to Container Active Defense. Alerts generated by container file protection all start with File Defense.
Alert states vary based on the action configured in the triggering rule:
Alert action: The alert state is Container. Handle these alerts promptly. For more information, see View and handle security alerts.
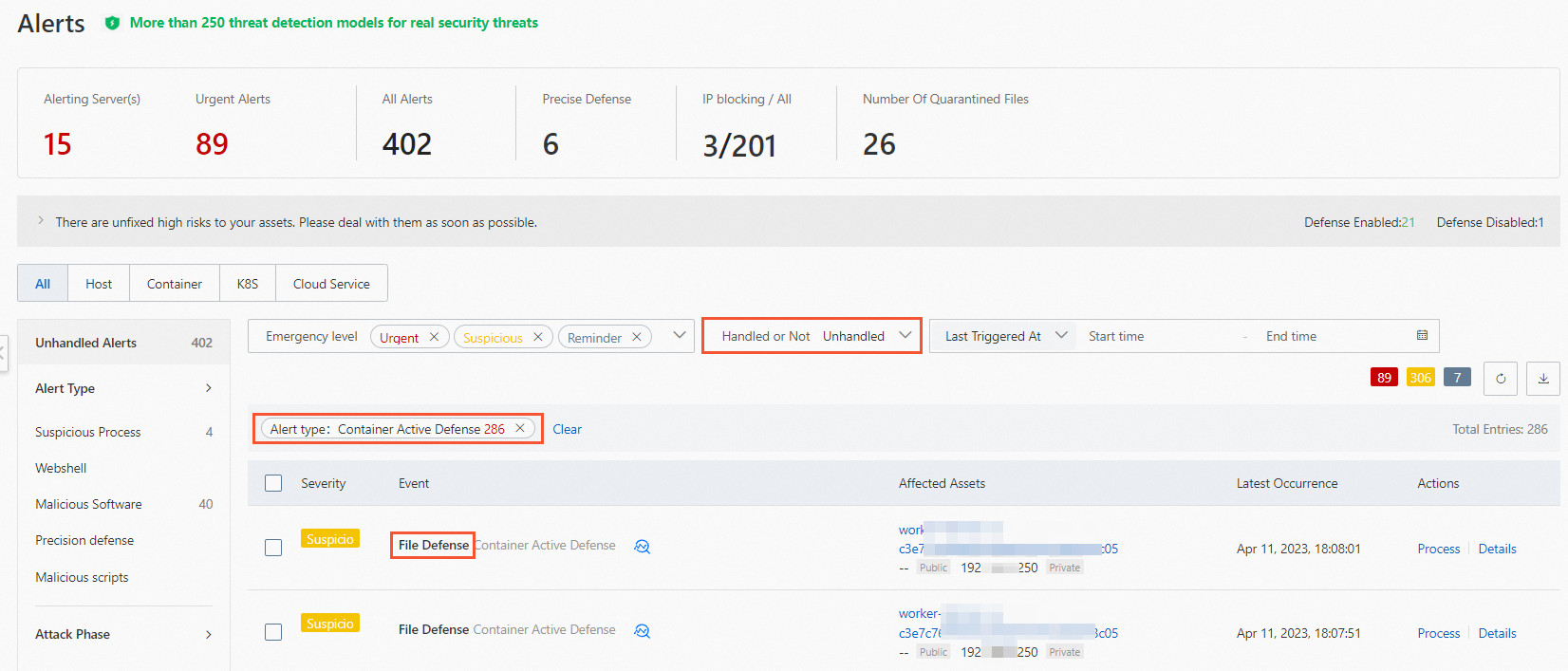
Block action: The alert state is Blocked. Security Center handles these alerts automatically. View them in the list of handled alerts.
Supported operating systems and kernel versions
| Operating system | Kernel version |
|---|---|
| CentOS (64-bit) | 3.10.0-123.9.3.el7.x86_64 3.10.0-229.el7.x86_64 3.10.0-327.10.1.el7.x86_64 3.10.0-327.13.1.el7.x86_64 3.10.0-327.22.2.el7.x86_64 3.10.0-327.36.3.el7.x86_64 3.10.0-327.el7.x86_64 3.10.0-514.10.2.el7.x86_64 3.10.0-514.16.1.el7.x86_64 3.10.0-514.21.1.el7.x86_64 3.10.0-514.26.2.el7.x86_64 3.10.0-514.6.2.el7.x86_64 3.10.0-514.el7.x86_64 3.10.0-693.11.1.el7.x86_64 3.10.0-693.11.6.el7.x86_64 3.10.0-693.17.1.el7.x86_64 3.10.0-693.2.2.el7.x86_64 3.10.0-693.21.1.el7.x86_64 3.10.0-693.5.2.el7.x86_64 3.10.0-693.el7.x86_64 3.10.0-862.11.6.el7.x86_64 3.10.0-862.14.4.el7.x86_64 3.10.0-862.2.3.el7.x86_64 3.10.0-862.3.2.el7.x86_64 3.10.0-862.3.3.el7.x86_64 3.10.0-862.6.3.el7.x86_64 3.10.0-862.9.1.el7.x86_64 3.10.0-862.el7.x86_64 3.10.0-957.1.3.el7.x86_64 3.10.0-957.10.1.el7.x86_64 3.10.0-957.12.1.el7.x86_64 3.10.0-957.12.2.el7.x86_64 3.10.0-957.21.2.el7.x86_64 3.10.0-957.21.3.el7.x86_64 3.10.0-957.27.2.el7.x86_64 3.10.0-957.5.1.el7.x86_64 3.10.0-957.el7.x86_64 3.10.0-1062.1.1.el7.x86_64 3.10.0-1062.1.2.el7.x86_64 3.10.0-1062.12.1.el7.x86_64 3.10.0-1062.18.1.el7.x86_64 3.10.0-1062.4.1.el7.x86_64 3.10.0-1062.4.2.el7.x86_64 3.10.0-1062.4.3.el7.x86_64 3.10.0-1062.7.1.el7.x86_64 3.10.0-1062.9.1.el7.x86_64 3.10.0-1062.el7.x86_64 3.10.0-1127.10.1.el7.x86_64 3.10.0-1127.13.1.el7.x86_64 3.10.0-1127.18.2.el7.x86_64 3.10.0-1127.19.1.el7.x86_64 3.10.0-1127.8.2.el7.x86_64 3.10.0-1127.el7.x86_64 3.10.0-1160.11.1.el7.x86_64 3.10.0-1160.15.2.el7.x86_64 3.10.0-1160.2.2.el7.x86_64 3.10.0-1160.21.1.el7.x86_64 3.10.0-1160.24.1.el7.x86_64 3.10.0-1160.25.1.el7.x86_64 3.10.0-1160.31.1.el7.x86_64 3.10.0-1160.36.2.el7.x86_64 3.10.0-1160.41.1.el7.x86_64 3.10.0-1160.42.2.el7.x86_64 3.10.0-1160.45.1.el7.x86_64 3.10.0-1160.49.1.el7.x86_64 3.10.0-1160.53.1.el7.x86_64 3.10.0-1160.59.1.el7.x86_64 3.10.0-1160.6.1.el7.x86_64 3.10.0-1160.62.1.el7.x86_64 3.10.0-1160.66.1.el7.x86_64 3.10.0-1160.el7.x86_64 3.10.0-1160.71.1.el7.x86_64 3.10.0-1160.76.1.el7.x86_64 3.10.0-1160.80.1.el7.x86_64 3.10.0-1160.83.1.el7.x86_64 4.18.0-80.11.2.el8_0.x86_64 4.18.0-147.3.1.el8_1.x86_64 4.18.0-147.5.1.el8_1.x86_64 4.18.0-147.8.1.el8_1.x86_64 4.18.0-193.el8.x86_64 4.18.0-193.1.2.el8_2.x86_64 4.18.0-193.6.3.el8_2.x86_64 4.18.0-193.14.2.el8_2.x86_64 4.18.0-193.19.1.el8_2.x86_64 4.18.0-193.28.1.el8_2.x86_64 4.18.0-240.1.1.el8_3.x86_64 4.18.0-240.10.1.el8_3.x86_64 4.18.0-240.15.1.el8_3.x86_64 4.18.0-240.22.1.el8_3.x86_64 4.18.0-305.3.1.el8.x86_64 4.18.0-305.7.1.el8_4.x86_64 4.18.0-305.10.2.el8_4.x86_64 4.18.0-305.12.1.el8_4.x86_64 4.18.0-305.19.1.el8_4.x86_64 4.18.0-305.25.1.el8_4.x86_64 4.18.0-348.2.1.el8_5.x86_64 4.18.0-348.7.1.el8_5.x86_64 4.18.0-358.el8.x86_64 4.18.0-365.el8.x86_64 |
| Alibaba Cloud Linux (64-bit) | 4.4.95-1.al7.x86_64 4.4.95-2.al7.x86_64 4.4.95-3.al7.x86_64 4.19.24-7.al7.x86_64 4.19.24-7.14.al7.x86_64 4.19.81-17.al7.x86_64 4.19.81-17.1.al7.x86_64 4.19.81-17.2.al7.x86_64 4.19.91-18.al7.x86_64 4.19.91-19.1.al7.x86_64 4.19.91-21.al7.x86_64 4.19.91-21.2.al7.x86_64 4.19.91-22.1.al7.x86_64 4.19.91-22.2.al7.x86_64 4.19.91-23.al7.x86_64 4.19.91-24.al7.x86_64 4.19.91-24.1.al7.x86_64 4.19.91-25.1.al7.x86_64 4.19.91-25.3.al7.x86_64 4.19.91-25.6.al7.x86_64 4.19.91-25.7.al7.x86_64 4.19.91-25.8.al7.x86_64 4.19.91-26.al7.x86_64 4.19.91-26.1.al7.x86_64 4.19.91-26.4.al7.x86_64 4.19.91-26.6.al7.x86_64 4.19.91-26.5.al7.x86_64 4.19.91-27.al7.x86_64 5.10.23-5.al8.x86_64 5.10.60-9.al8.x86_64 5.10.84-10.2.al8.x86_64 5.10.84-10.3.al8.x86_64 5.10.84-10.4.al8.x86_64 5.10.112-11.al8.x86_64 5.10.112-11.1.al8.x86_64 5.10.112-11.2.al8.x86_64 5.10.134-12.al8.x86_64 5.10.134-12.1.al8.x86_64 5.10.134-12.2.al8.x86_64 5.10.134-13.al8.x86_64 |
| Ubuntu (64-bit) | 3.13.0-32-generic 3.13.0-65-generic 3.13.0-86-generic 3.13.0-145-generic 3.13.0-164-generic 3.13.0-170-generic 3.19.0-80-generic 4.4.0-62-generic 4.4.0-63-generic 4.4.0-79-generic 4.4.0-93-generic 4.4.0-96-generic 4.4.0-104-generic 4.4.0-117-generic 4.4.0-124-generic 4.4.0-142-generic 4.4.0-146-generic 4.4.0-148-generic 4.4.0-151-generic 4.4.0-154-generic 4.4.0-157-generic 4.4.0-161-generic 4.4.0-170-generic 4.4.0-174-generic 4.4.0-176-generic 4.4.0-177-generic 4.4.0-178-generic 4.4.0-179-generic 4.4.0-184-generic 4.4.0-194-generic 4.4.0-198-generic 4.4.0-210-generic 4.15.0-23-generic 4.15.0-42-generic 4.15.0-45-generic 4.15.0-48-generic 4.15.0-52-generic 4.15.0-54-generic 4.15.0-62-generic 4.15.0-66-generic 4.15.0-70-generic 4.15.0-72-generic 4.15.0-88-generic 4.15.0-91-generic 4.15.0-96-generic 4.15.0-101-generic 4.15.0-106-generic 4.15.0-109-generic 4.15.0-112-generic 4.15.0-117-generic 4.15.0-118-generic 4.15.0-121-generic 4.15.0-122-generic 4.15.0-124-generic 4.15.0-128-generic 4.15.0-135-generic 4.15.0-145-generic 4.15.0-147-generic 4.15.0-143-generic 4.15.0-151-generic 4.15.0-162-generic 4.15.0-166-generic 4.15.0-169-generic 4.15.0-170-generic 4.15.0-173-generic 4.15.0-175-generic 4.15.0-177-generic 4.15.0-181-generic 4.15.0-189-generic 4.15.0-190-generic 4.15.0-192-generic 4.15.0-193-generic 4.15.0-196-generic 4.15.0-197-generic 4.15.0-200-generic 4.15.0-202-generic 5.4.0-31-generic 5.4.0-47-generic 5.4.0-70-generic 5.4.0-77-generic 5.4.0-86-generic 5.4.0-90-generic 5.4.0-92-generic 5.4.0-94-generic 5.4.0-100-generic 5.4.0-102-generic 5.4.0-106-generic 5.4.0-108-generic 5.4.0-110-generic 5.4.0-113-generic 5.4.0-122-generic 5.4.0-123-generic 5.4.0-125-generic 5.4.0-131-generic 5.4.0-132-generic 5.4.0-135-generic |
| Anolis OS (64-bit) | 3.10.0-1062.an7.x86_64 3.10.0-1160.an7.x86_64 3.10.0-1160.59.1.0.1.an7.x86_64 3.10.0-1160.62.1.0.1.an7.x86_64 3.10.0-1160.66.1.0.1.an7.x86_64 3.10.0-1160.71.1.0.1.an7.x86_64 3.10.0-1160.76.1.0.1.an7.x86_64 3.10.0-1160.80.1.0.1.an7.x86_64 3.10.0-1160.81.1.0.1.an7.x86_64 4.19.91-25.2.an7.x86_64 4.19.91-25.7.an7.x86_64 4.19.91-26.an7.x86_64 4.19.91-26.4.an7.x86_64 4.19.91-26.5.an7.x86_64 4.19.91-26.6.an7.x86_64 4.19.91-27.an7.x86_64 4.18.0-348.2.1.an8_4.x86_64 4.18.0-348.12.2.an8.x86_64 4.18.0-348.20.1.an8_5.x86_64 4.18.0-348.23.1.an8_5.x86_64 4.18.0-372.9.1.an8.x86_64 4.18.0-372.16.1.an8_6.x86_64 4.18.0-372.19.1.an8_6.x86_64 4.18.0-372.26.1.an8_6.x86_64 4.18.0-372.32.1.an8_6.x86_64 4.19.91-25.7.an8.x86_64 4.19.91-25.8.an8.x86_64 4.19.91-26.an8.x86_64 4.19.91-26.1.an8.x86_64 4.19.91-26.4.an8.x86_64 4.19.91-26.5.an8.x86_64 4.19.91-26.6.an8.x86_64 |
| Red Hat Enterprise Linux (RHEL) (64-bit) | 3.10.0-1062.el7.x86_64 3.10.0-1127.el7.x86_64 3.10.0-1160.71.1.el7.x86_64 4.18.0-80.el8.x86_64 4.18.0-372.9.1.el8.x86_64 |