Ransomware can encrypt or destroy your server files and database data before you detect the attack. The anti-ransomware feature backs up your data at regular intervals so you can restore it to a known-good state if an attack occurs. This topic walks you through the three-step setup process and the routine checks that keep your protection current.
Prerequisites
Before you begin, make sure you have:
Anti-ransomware capacity purchased based on the size of the files or databases you want to protect. For details, see Enable anti-ransomware
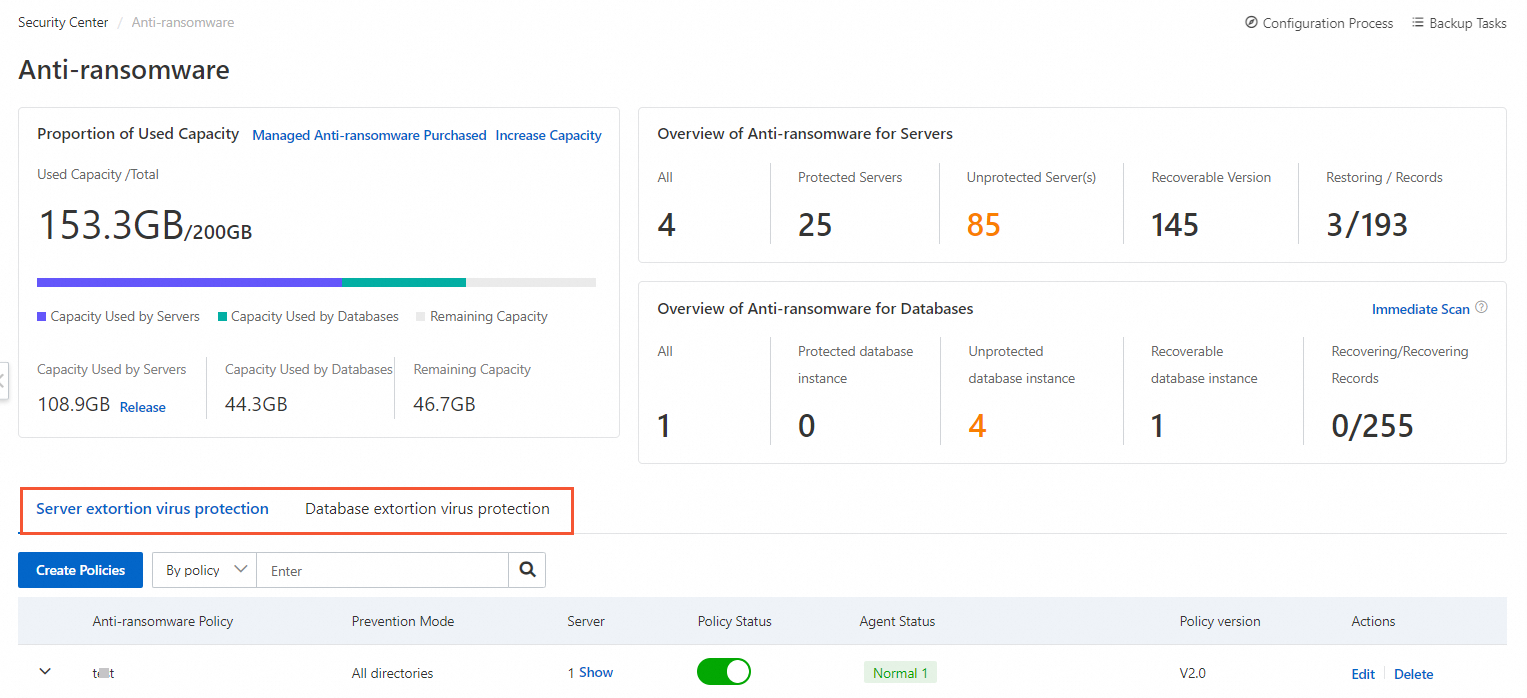
Step 1: Create an anti-ransomware policy
Create an anti-ransomware policy for your core data. Choose the policy type based on what you want to protect:
| Anti-ransomware for servers | Anti-ransomware for databases | |
|---|---|---|
| What it protects | Files in specific directories on a server | Database files |
| Where to configure | Anti-ransomware for Servers tab on the Anti-ransomware page | Anti-ransomware for Databases tab on the Anti-ransomware page |
| Reference | Create an anti-ransomware policy | Create an anti-ransomware policy |
You can enable both types at the same time.
After you create a policy for a server, the anti-ransomware agent installs on that server automatically. Verify that the agent installed successfully and that its status is normal — this is required for backup tasks to run as expected.
First backup: The first backup backs up all data in the protected directories you specify. This takes longer than subsequent backups.
Subsequent backups: After the first backup completes, the system backs up only incremental data on a periodic schedule.
Protected directory restriction: Specify only local directories as protected directories. Mount paths — such as an Elastic Compute Service (ECS) instance directory with an Object Storage Service (OSS) object or File Storage NAS (NAS) file system attached — are not supported. Accessing data through a mount path generates additional fees. To back up files on a mount path, use Cloud Backup instead. See Get started with OSS backup and Get started with on-premises NAS backup.
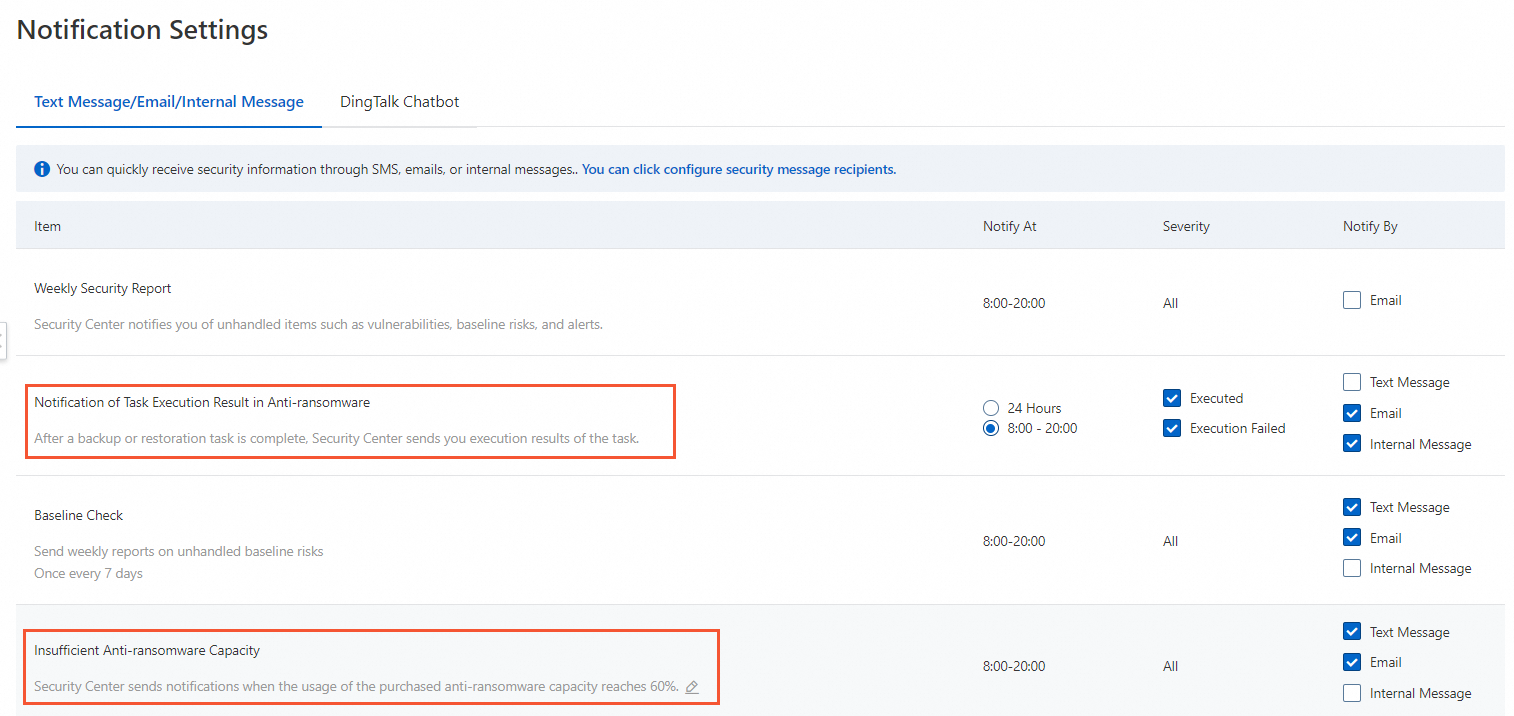
Step 2: Configure anti-ransomware notifications
Set up notifications so you are alerted when backup tasks complete or fail and when anti-ransomware capacity runs low. On the Notification Settings page, configure the following parameters:
| Parameter |
|---|
| Anti-ransomware Task Results |
| Insufficient Anti-ransomware Capacity |
For details, see Configure notification settings.
Step 3: Perform routine inspection
After setup, run the following checks regularly to confirm that protection is working and your servers are secure.
Check backup tasks
Go to the Anti-ransomware page every day or based on the backup retention period that you specified. Verify:
The anti-ransomware agent status is normal
Anti-ransomware capacity is sufficient
Backup tasks are completing as expected
Backup data status is normal
If you find an issue, troubleshoot it promptly. See Troubleshoot anti-ransomware agent and backup task issues and Troubleshoot anti-ransomware policy issues for databases.
Check the Security Center agent
The Security Center agent collects and analyzes logs and data on your servers to monitor and detect threats. If the agent goes offline on a server, that server is unprotected.
Check agent status regularly on the Host page. If an agent is offline, see Troubleshoot Security Center agent offline issues.
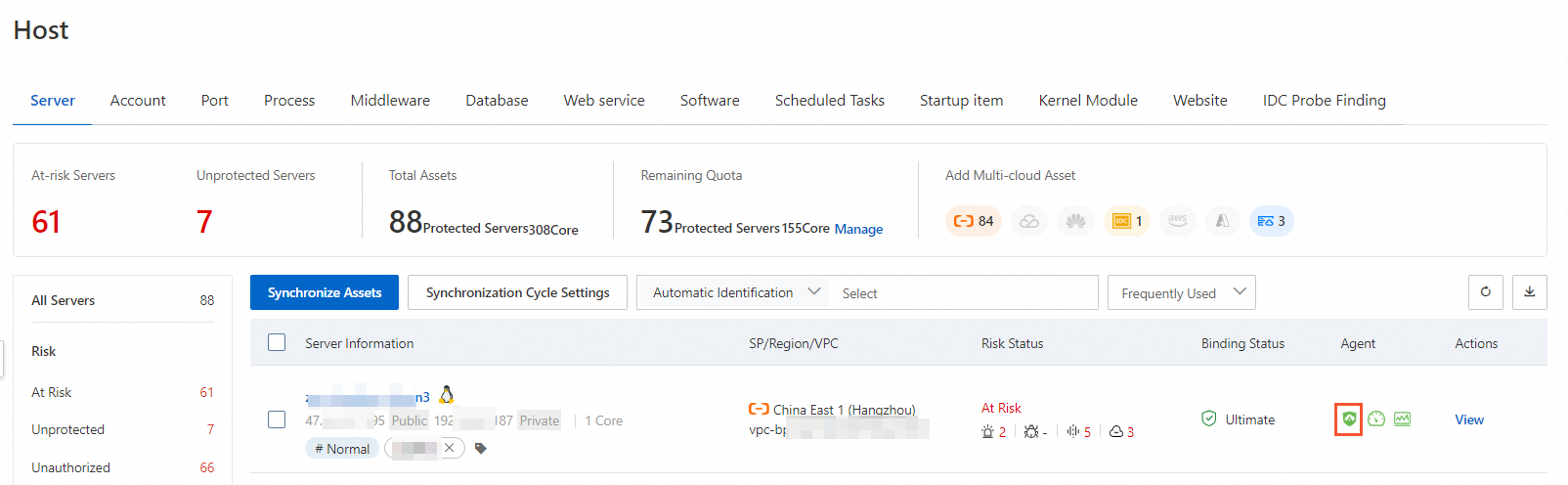
Review and handle alerts
Security Center detects threats in real time and generates alerts for events such as Web Tamper Proofing, Suspicious Process Behavior, Webshell, Unusual Logon, and Malicious Process.
From the Host page, open a server's details page to view all its alerts and handle them promptly. For details, see View and handle alerts.
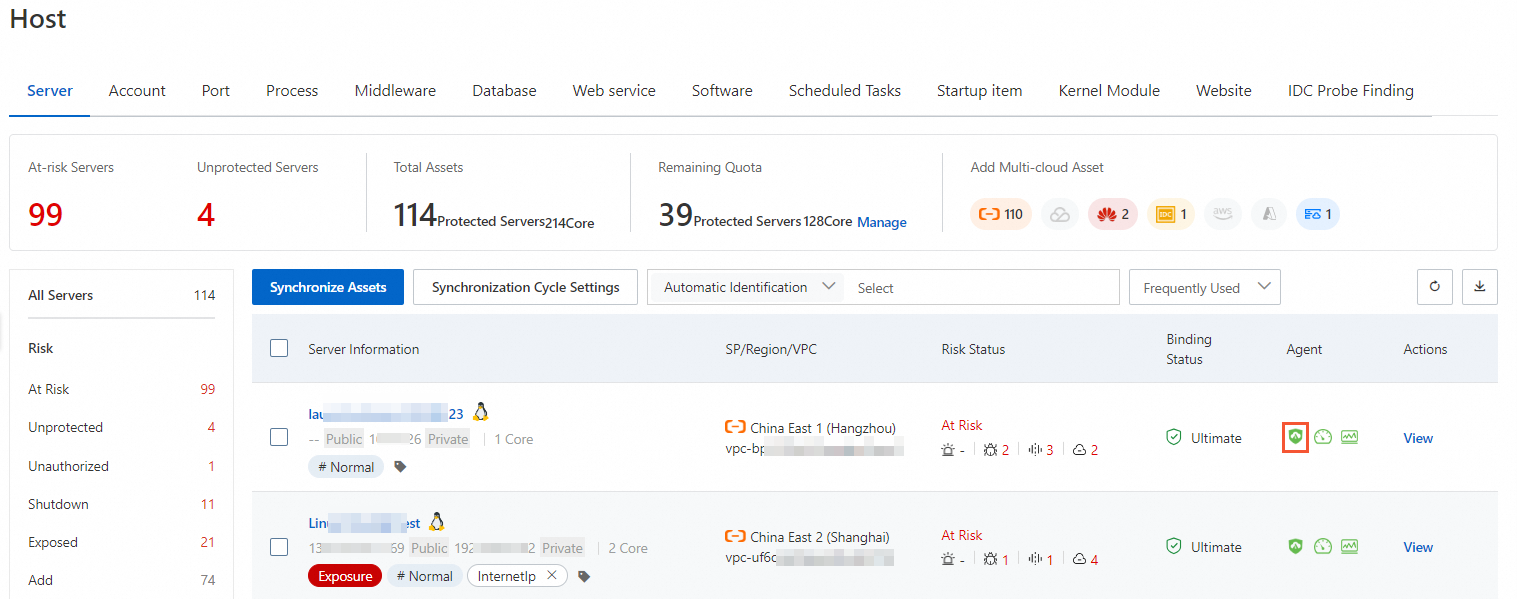
Fix vulnerabilities
Unpatched vulnerabilities are a common entry point for ransomware. Run periodic vulnerability detection and fix detected vulnerabilities promptly. From the Host page, open the server details page to view all detected vulnerabilities. For details, see Scan for vulnerabilities and View and handle vulnerabilities.
Run baseline checks
Misconfigured operating systems, databases, software, and containers can be exploited even without a software vulnerability. Use the baseline check feature to detect and fix configuration risks. This reduces intrusion risk and helps meet security compliance requirements. For details, see Baseline check.
Verify that core services are accessible
Ransomware can encrypt server data or delete database records, taking your service offline. Run periodic accessibility checks on your core services to detect ransomware impact early and respond before data loss becomes irreversible.
Usage notes
Do not restart a server during a backup task. If you restart the server, the backup task fails and no data is backed up until the next scheduled cycle.
Do not delete anti-ransomware policies or the attacked servers for which anti-ransomware policies are created. Deleting a policy or its associated server also deletes the backup data, which cannot be restored.
Use anti-ransomware together with other security methods to protect important files and database data.