Managing security operations across multiple Alibaba Cloud accounts creates blind spots: each account generates its own logs, runs its own detections, and handles its own events independently. Multi-account management for Agentic SOC (Security Operations Center) solves this by centralizing log collection, threat detection, and event response under a single delegated administrator account—without requiring each member account to purchase Agentic SOC.
Key concepts
Account types
| Account type | Description | Responsibilities |
|---|---|---|
| Management account (MA) | An Alibaba Cloud account that has completed enterprise identity verification. It is the creator and top-level administrator of the resource directory, with full control over the organization. | Creates the organization structure, invites or creates members, and designates delegated administrators for specific services. A resource directory has exactly one management account. |
| Member account | An Alibaba Cloud account that joins a resource directory to host specific services or projects. | Runs services within its own account and enables log services for required Alibaba Cloud products according to management policies. |
| Delegated administrator account | A member account designated by the management account to perform management duties in a specific Alibaba Cloud service (Security Center in this topic). | Purchases and configures Agentic SOC, centrally manages and analyzes security logs from all in-scope member accounts, and bears the costs for Agentic SOC and log storage. |
Example configuration
The following example shows a typical multi-account structure for Agentic SOC:
Resource directory structure:
Management account: Account A
Member accounts: Accounts B, C, D, and E
Management plan:
Account A designates Account B as the delegated administrator.
Account B centrally manages log integration, threat detection, and event handling for accounts C, D, and E.

How it works
The solution is built on two mechanisms: permission delegation and data centralization.
Log generation: Logs from Alibaba Cloud products in each member account—such as Web Application Firewall (WAF) and Cloud Firewall logs—are written to Simple Log Service (SLS) within that account.
Centralized collection: The delegated administrator's Agentic SOC service uses service-linked roles to read log data in real time from the SLS of each member account.
Unified analysis: All collected logs flow into the delegated administrator's Agentic SOC instance for threat detection, event response, and audit.
Prerequisites
Before you begin, make sure that:
All accounts (management account and member accounts) belong to the same enterprise and have completed enterprise identity verification.
The account you plan to designate as the delegated administrator is already a member account in the resource directory.
Log integration currently supports only Alibaba Cloud product logs.
Set up multi-account log integration
Step 1: Purchase and enable Agentic SOC
The delegated administrator purchases and enables the Agentic SOC service. For more information, see Purchase and enable Agentic SOC.
Log integration in a multi-account scenario supports only the Real-time Consumption mode. This mode does not automatically persist raw logs. To trace, audit, or analyze historical logs, purchase Log Storage Capacity to enable the Log Management service. Whether member accounts have Agentic SOC enabled does not affect log integration.
Step 2: Create a multi-account directory structure
Enable a resource directory If this is your first time using Resource Directory, log in to the Resource Management console with the management account. In the left navigation pane, choose Resource Directory > Overview, then click Enable Resource Directory and follow the on-screen instructions. For more information, see Enable a resource directory.
Add member accounts In the resource directory, add members using either method:
Create a member: In the left navigation pane, choose Resource Directory > Create Member Account to create a resource account. For more information, see Create a member.
Invite a member: Choose Resource Directory > Invite Member to add existing Alibaba Cloud accounts to the resource directory. For more information, see Invite an Alibaba Cloud account to join a resource directory.
Set the delegated administrator In the left navigation pane, choose Resource Directory > Trusted Services. In the Security Center row, click Manage in the Actions column. Add the account that purchased Agentic SOC as the delegated administrator. For more information, see Add a delegated administrator account.
ImportantAfter you add a Security Center administrator, that account also becomes an administrator for Security Center - Threat Analysis.
Step 3: Add member accounts to Agentic SOC
Log in to the Security Center console using the delegated administrator account, and go to the Multi-account Management Settings page. In the upper-left corner, select the region where your assets are located: Chinese Mainland or Outside Chinese Mainland.
On the Configure tab, in the Total Monitored Accounts section, click Account Management.
In the Multi-account Management Settings panel, select the member accounts from the resource directory list, then click OK.
ImportantThe system automatically creates two service-linked roles for each added member account:
AliyunServiceRoleForSasRdandAliyunServiceRoleForSasCloudSiem. These roles grant Agentic SOC the minimum permissions needed to collect log data from member accounts. For more information, see Service-linked roles for Security Center.
Step 4: Enable the log service for cloud products
For each member account, enable the log service for the relevant Alibaba Cloud products (except Security Center itself). For setup instructions, see Alibaba Cloud product log integration with SLS reference.
Alert logs from security products in the Alibaba Cloud service center Logstore—such as WAF alert logs and Cloud Firewall alert logs—are automatically delivered to Agentic SOC. No additional setup is needed for these products.
Step 5: Configure cross-account integration
Use one of the following methods to integrate logs from member accounts into Agentic SOC.
Batch integration
Batch integration applies access policies to multiple accounts and data sources at once. Use this method when onboarding multiple accounts or when you want to use the recommended policy to get started quickly.
Log in with the delegated administrator account. In the left navigation pane, choose Agentic SOC > Integration Settings.
Click Batch Associate Settings and configure the following parameters:
WarningFull Access is an overwrite action. It disables any running policies not selected in the current configuration, which can interrupt data ingestion. Proceed with caution.
Click Use Recommended Policy to let the system automatically select the most valuable data sources based on best practices. This is the fastest way to start analyzing security data.
Parameter Options When to use Access Settings Increment Access: Keeps all currently enabled access policies and adds the new ones from this configuration. Use when adding new accounts or data sources without disrupting existing integrations. Full Access: Replaces all existing access settings. Policies not selected in this configuration are disabled. Use when doing a full reconfiguration. Accessible Account Select the member accounts to integrate. — Alibaba Cloud Services Select the cloud services and their data sources to ingest. — Auto-Add New Data Sources Enable to automatically include newly created Logstores in the current data source scope. Reduces manual maintenance as new Logstores are added. Click OK. The system automatically ingests logs from all enabled Logstores for the selected accounts and activates the corresponding access policies.
ImportantNew access policies may take some time to deploy and initialize.
To verify the integration status, return to the integration list, find the product, and click Multi-account Access Settings in the Actions column. On the Access Policy tab, click Multi-account Access in the Actions column for the target data source.
Manual integration
Use manual integration when you need to configure a specific product individually.
Log in with the delegated administrator account. In the left navigation pane, choose Agentic SOC > Integration Settings.
Find the cloud product to integrate and click Multi-account Access Settings in the Actions column.
ImportantMulti-account integration supports only Alibaba Cloud products.
In the Actions column for the desired policy template, click Multi-account Access. The account integration configuration panel appears.
The system provides preset integration policy templates for Alibaba Cloud products. These templates cannot be modified.
Click Batch Add Account Settings, configure the following parameters, then click OK:
Accounts: The system lists all accounts the delegated administrator can manage, excluding already-integrated accounts. Select one or more accounts.
Policy Status: Set whether to enable the policy immediately.
Wait approximately one minute for the newly added accounts to appear in the integration list.
The system identifies Logstore information using each cloud product's log query API or default Logstore naming rules. It then retrieves all logs from the integrated member accounts that match the integration template.
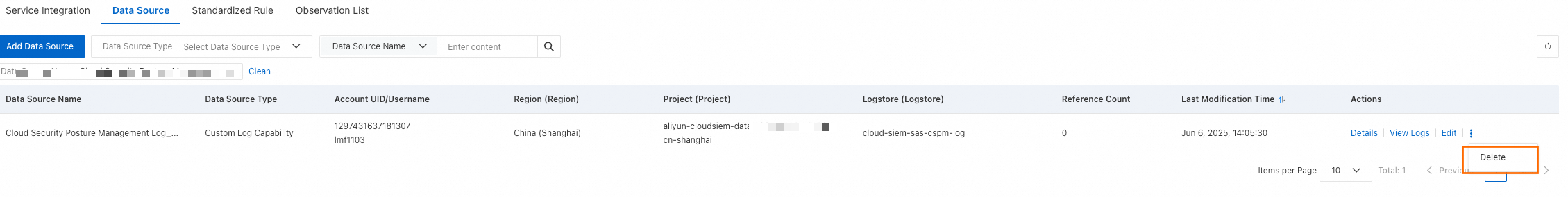
After integration completes, a data source is automatically created for each member account with the following properties:
Data source name: Integration template name\_Region ID\_Member account UID
Data source type: Custom Log Service
Account UID/Username: The member account UID and username
A data source is created for the member account even if the policy is not enabled.
Analyze logs across accounts
After integration is configured, the delegated administrator can perform the following operations on data from all member accounts in the Agentic SOC console:
Unified threat detection: Configure threat detection rules to run real-time detection on log data from all accounts.
Centralized event handling: View and handle alerts from all member accounts on the Security Events page.
Automated response: Create automated playbooks using Response Orchestration to handle cross-account security events automatically.
Global log tracing: Search and trace raw logs from all member accounts using Log Management.
Remove a member account from integration
If you no longer need log data from a member account, cancel its integration policy manually.
Canceling integration does not delete the data source. Manage data sources on the data source management tab if needed.
On the Multi-account Access Settings tab, click Multi-account Access in the Actions column for the integration template.
In the account integration configuration panel, disable the policy, then click Remove in the Actions column for the account.
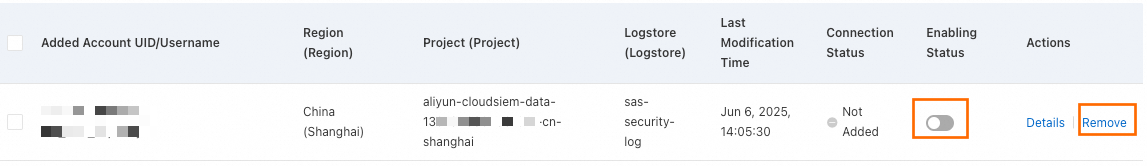
(Optional) Delete the data source: On the data source management page, search for the data source using the naming format "Integration template name\_Region ID\_Member account UID" and click Delete.
Troubleshooting
I can't find the account I want to designate as the delegated administrator
Check two things: first, confirm that the account has been successfully added as a member to the resource directory. Second, make sure you're logged in as the management account—only the management account can designate a delegated administrator.
Integration status shows "Failed" or "No Data" for a long time
Work through the following checks in order:
Log service not enabled in the member account: Contact the member account owner to confirm that the log service for the relevant Alibaba Cloud product is enabled and delivering logs to SLS. This is a prerequisite for data collection.
Account not in Agentic SOC management scope: In the delegated administrator's Security Center console, go to System Settings > Multi-account Management and confirm the member account is selected.
Service-linked roles not created: In the Resource Access Management (RAM) console of the member account, go to the Roles page and check whether
AliyunServiceRoleForSasRdandAliyunServiceRoleForSasCloudSiemexist. If they don't, remove the member account from Agentic SOC and add it again to trigger role creation.Integration still initializing: Integration takes time to complete. Wait a few minutes and check again.