SchedulerX supports the batch configuration of permission policies for Resource Access Management (RAM) users and user groups. Using RAM, you can avoid sharing your Alibaba Cloud account keys and assign permissions based on the principle of least privilege. This practice reduces security risks. This topic describes how to grant permissions for specific operations to RAM users.
Quick start configurations
This section describes two ways to configure RAM permissions to quickly grant RAM users access to SchedulerX. These permission policies offer different levels of control. Choose the policy that best meets your needs. For examples of more granular custom permission configurations, see Examples of custom permission policy configurations.
Grant a RAM user permissions to create resources
By default, RAM users do not have permissions to create, view, or manage any SchedulerX resources. You can grant a RAM user permissions to create resources. By default, the RAM user will have read and write permissions on all resources that they create.
Procedure:
Log on to the Resource Access Management (RAM) console.
Create a custom permission policy. For more information, see Create a custom permission policy. Use the following policy script to grant a RAM user permissions to create namespaces and application groups in all namespaces. The RAM user has permissions only for the application groups that they create. To grant permissions for application groups and resources created by other RAM users, see the Examples of custom permission policy configurations section in this topic.
{ "Version": "1", "Statement": [ { "Action": ["edas:CreateSchedulerxNamespace*", "edas:CreateSchedulerxAppGroup*"], "Effect": "Allow", "Resource": "acs:edas:*:*:*" } ] }(Optional) Create a RAM user or a RAM user group. For more information, see Create a RAM user or Create a RAM user group. Skip this step if a user or group already exists.
Assign the permission policy configured in Step 2 to a single user. For more information, see Manage RAM user permissions.
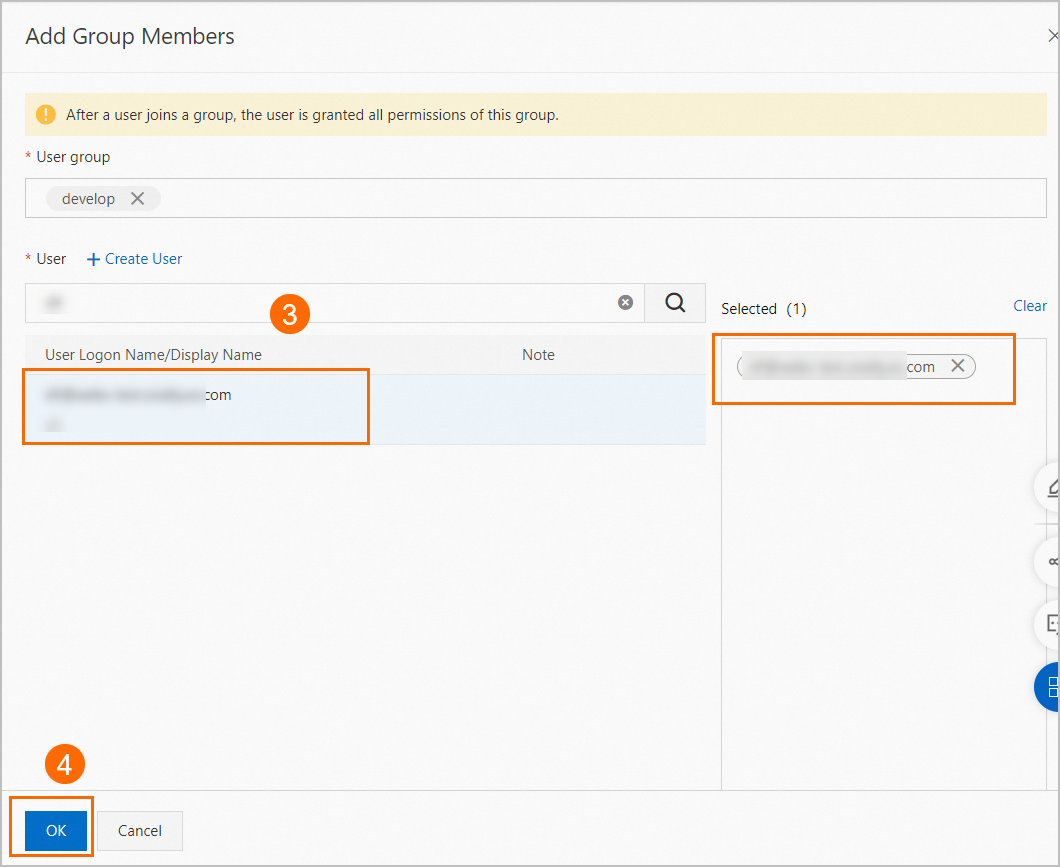
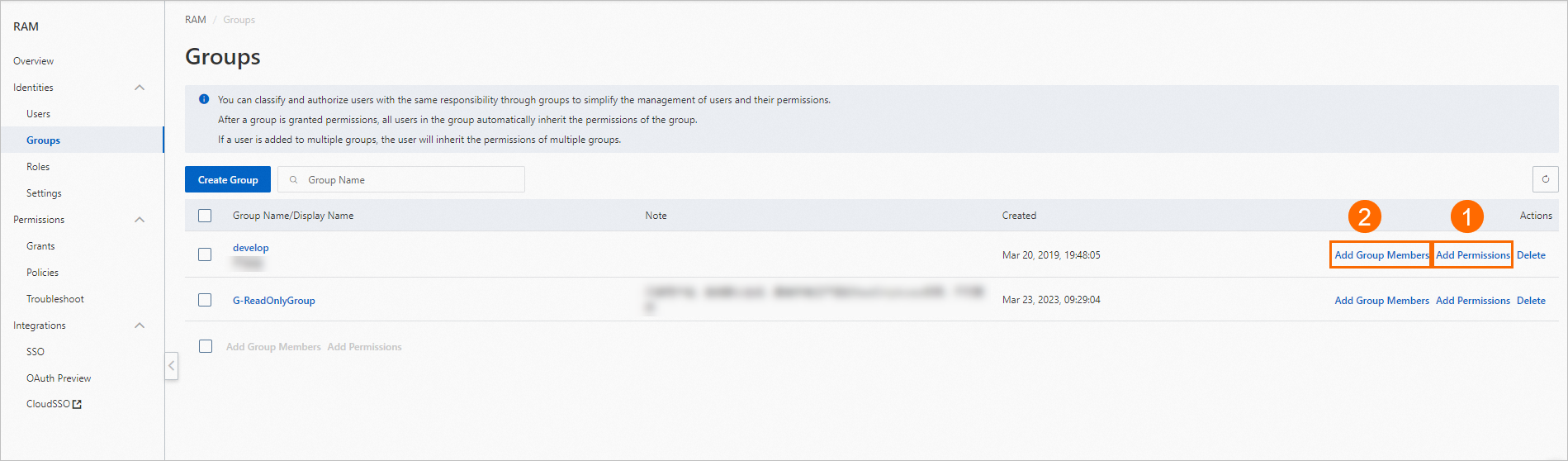
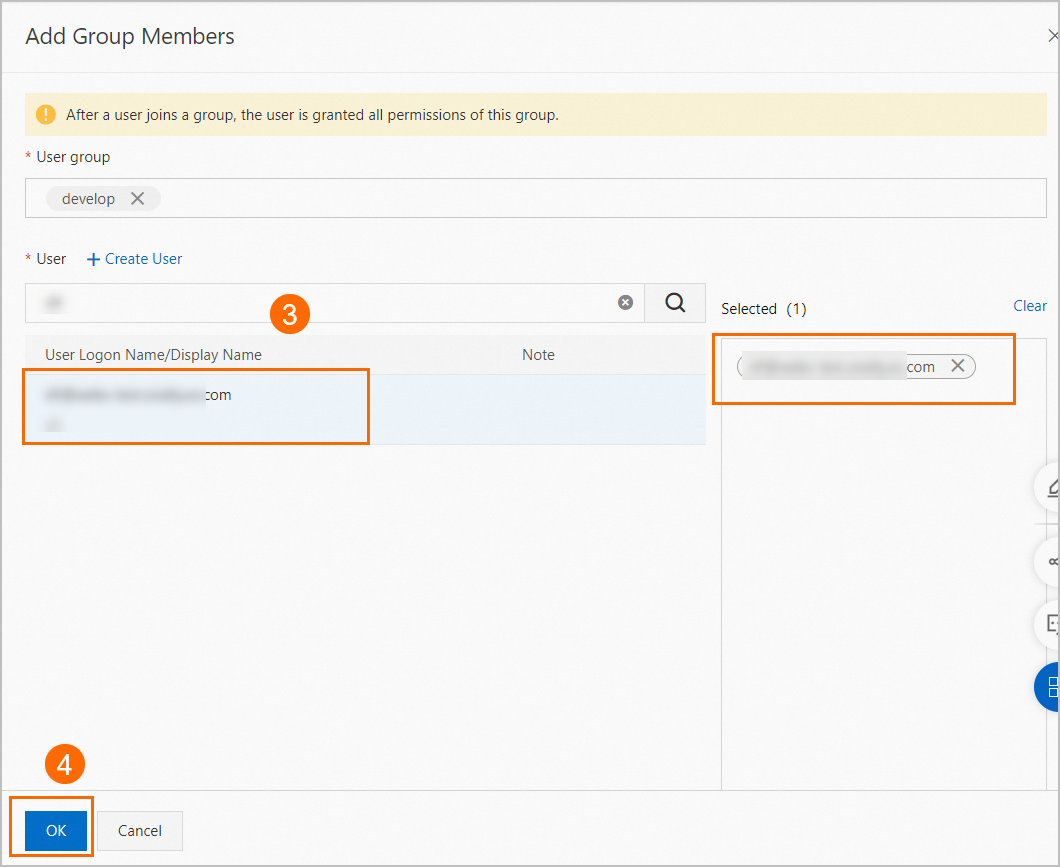
Assign the permission policy configured in Step 2 to a user group and add users to the group.
Assign the permission policy to the user group. For more information, see Grant permissions to a RAM user group.
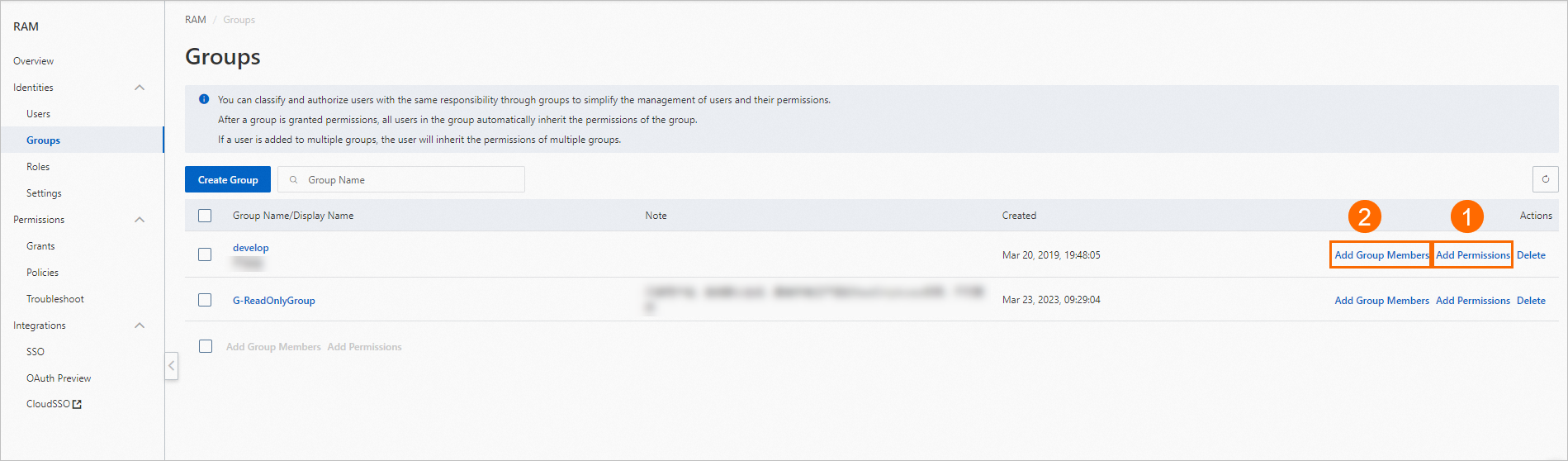
Add users to the user group that contains the required permission policy. For more information, see Method 2: Add a RAM user to a RAM user group on the RAM user group page.
Have an administrator create resources and then grant permissions to RAM users
In software project management, typically, only O&M engineers can create resources, while developers have only read and operation permissions. You can create an administrator role for an O&M engineer. This role grants permissions to manage all resources on the Distributed Task Scheduling Platform. The administrator can then create the required namespaces and application groups. They can also create permission policies for these resources and assign them to other RAM users as needed.
Procedure:
Log on to the RAM console.
Create a custom permission policy. For more information, see Create a custom permission policy. Use the following policy script to grant a RAM user SchedulerX administrator permissions. This policy grants management permissions for all SchedulerX resources under the Alibaba Cloud account.
{ "Statement": [ { "Action": "edas:*Schedulerx*", "Effect": "Allow", "Resource": [ "acs:edas:*:*:*" ] } ], "Version": "1" }(Optional) Create a RAM user or a RAM user group. For more information, see Create a RAM user or Create a RAM user group. Skip this step if a user or group already exists.
Assign the permission policy configured in Step 2 to a single user. For more information, see Manage RAM user permissions.
Assign the permission policy configured in Step 2 to a user group and add users to the group.
Assign the permission policy to the user group. For more information, see Grant permissions to a RAM user group.
Add users to the user group that contains the required permission policy. For more information, see Method 2: Add a RAM user to a RAM user group on the RAM user group page.
SchedulerX permissions
By default, an Alibaba Cloud account has full management permissions for all of its resources. For access control, you can use Resource Access Management (RAM) to assign permission policies. SchedulerX uses RAM users and user groups to simplify the batch configuration of permission policies, which eliminates the need to grant permissions to individual users. SchedulerX permission policies also support shared system policy configurations.
System policy | Description |
AliyunEDASFullAccess | Permissions to manage Enterprise Distributed Application Service (EDAS). |
The following sections describe how to configure custom permission policies for SchedulerX. A permission policy in RAM consists of an `Action` and a `Resource` element. You can create permission policies based on the rules defined by SchedulerX.
Structure of a custom policy
{
"Statement": [
{
"Action": "edas:*", // The Action configuration item. For more information, see the next section, "Action".
"Effect": "Allow",
"Resource": "*" // The Resource configuration item. For more information, see the next section, "Resource".
}
],
"Version": "1",
}Action
The structure of an Action in SchedulerX is defined as follows:
edas:${type}Schedulerx*The ${type} parameter has four possible values: Read, Manage, Delete, and Create. The operations included in each type are listed below:
Type | Related operations |
Create | Create namespaces, applications, tasks, and workflows. |
Manage |
|
Delete | Delete namespaces, application groups, tasks, and workflows. |
Read | Query application groups, tasks, task instances, workflows, and online instances. |
Resource
The structure of a Resource in SchedulerX is defined as follows:
acs:edas:${regionid}:${accountid}:namespace/${namespace_id}/${resourceType}/${resourceId}Parameter | Description |
| The region where the resource is located. You can set this parameter to |
| Specifies the account for resource access. The default value is |
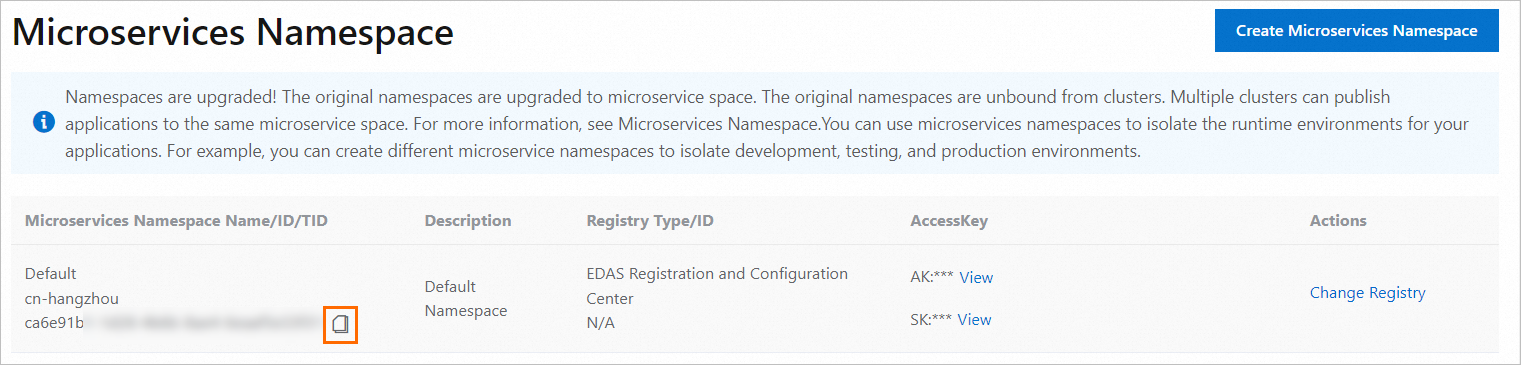
| The ID of the namespace.
|
| The resource type. Valid value: JobGroup, which indicates an application group for tasks in SchedulerX. |
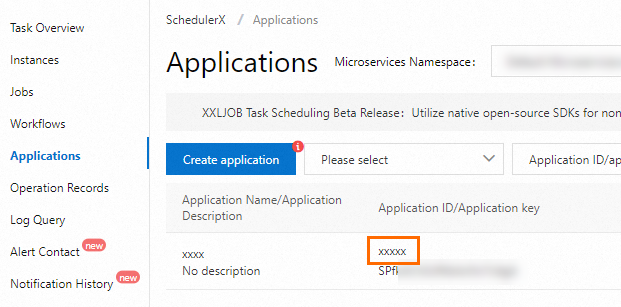
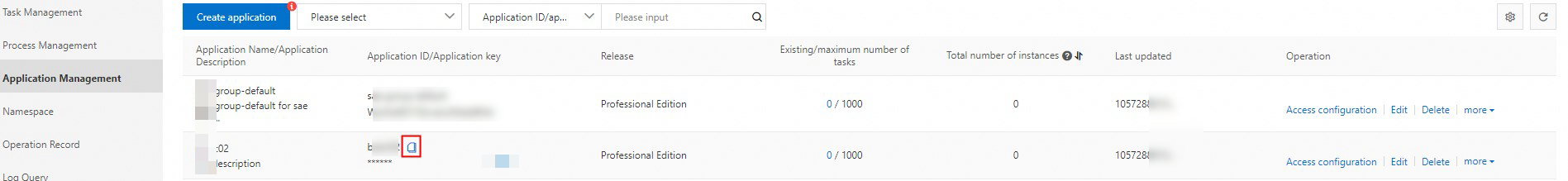
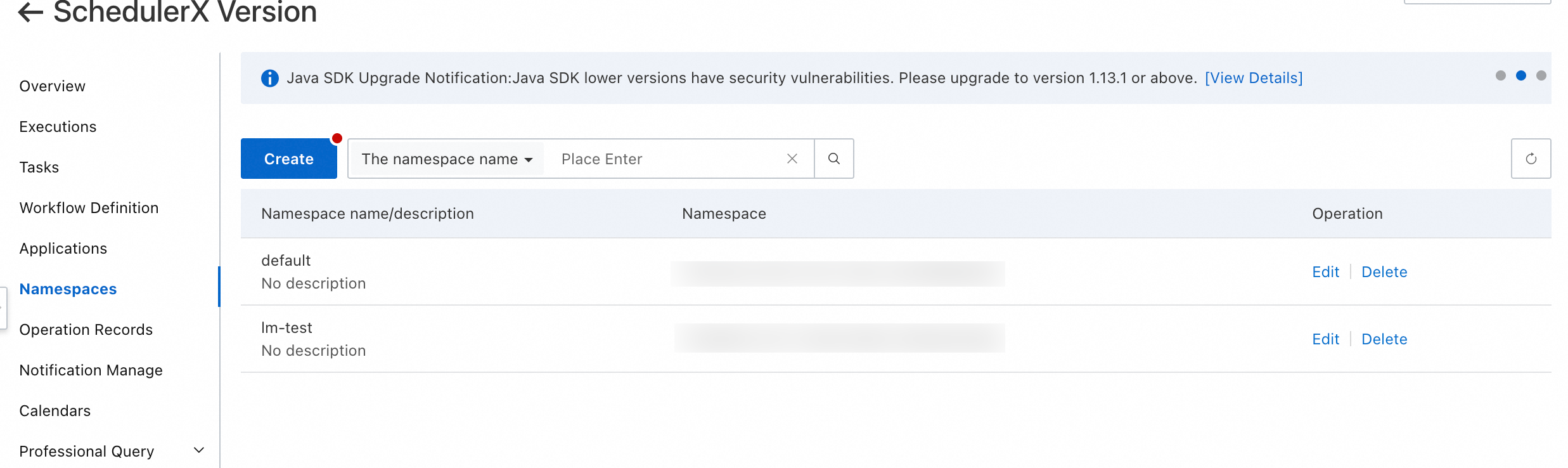
| The ID of the specified To obtain the
|
Examples of custom permission policy configurations
Grant a RAM user management permissions on all resources
This policy grants management permissions for all SchedulerX resources. It allows all operations on all SchedulerX resources.
{
"Version": "1",
"Statement": [
{
"Effect": "Allow",
"Action": [
"edas:*Schedulerx*"
],
"Resource": [
"acs:edas:*:*:*"
]
}
]
}Grant a RAM user read-only permissions on all resources
This policy grants read-only permissions for all SchedulerX resources. This policy allows users to view information about all SchedulerX resources.
{
"Version": "1",
"Statement": [
{
"Effect": "Allow",
"Action": [
"edas:ReadSchedulerx*"
],
"Resource": [
"acs:edas:*:*:*"
]
}
]
}Grant a RAM user permissions on all actions in a specific namespace
This policy grants management permissions for all application and task resources in one or more specified namespaces. You can obtain the namespace ID from the EDAS microservices namespace and use it in the configuration. The following example grants management permissions for scheduling-related resources in two namespaces: `namespace-ID-01` and `namespace-ID-02`. You can also change the `Action` configuration to restrict operations on these resources. For example, if you set the `Action` to `edas:ReadSchedulerx*`, the policy grants read-only permissions for the two namespaces.
{
"Version": "1",
"Statement": [
{
"Effect": "Allow",
"Action": [
"edas:*Schedulerx*"
],
"Resource": [
"acs:edas:*:*:namespace/namespace-ID-01/*",
"acs:edas:*:*:namespace/namespace-ID-02/*"
]
}
]
}
Grant a RAM user permissions on all actions for a specific application
This policy grants access management permissions for resources under specific applications in SchedulerX. In the `Resource` element, specify the application ID of the `JobGroup` that corresponds to the namespace to grant permissions for that application. You can also use a prefix with a wildcard (*). For example, `TestGroup*` specifies all application groups that have the `TestGroup` prefix. This lets you configure permissions for multiple application groups in a batch.
{
"Version": "1",
"Statement": [
{
"Effect": "Allow",
"Action": [
"edas:*Schedulerx*"
],
"Resource": [
"acs:edas:*:*:namespace/namespace-ID-01/JobGroup/TestGroup*",
"acs:edas:*:*:namespace/namespace-ID-02/JobGroup/AppGroup"
]
}
]
}