TDE cannot be disabled after it is enabled. Review Restrictions before proceeding.
Transparent data encryption (TDE) encrypts Redis Database (RDB) files before they are written to disk and decrypts them when read back into memory. Enabling TDE adds data-at-rest protection without increasing storage usage or requiring changes to your client applications.
Supported instances
TDE is supported only on the following instance type:
-
Instance type: Tair (Enterprise Edition) memory-optimized
-
Storage mode: Classic (local disk) mode
-
Minor version: 1.7.1 or later
To check or update the minor version, see Update the minor version of an instance.
How it works
TDE encrypts RDB data files on the way to disk and decrypts them on the way back to memory. Encryption keys are generated and managed by Key Management Service (KMS). Tair does not provide keys or certificates required for encryption.
What TDE encrypts:
-
RDB backup files written to disk (for example,
dump.rdb)
What TDE does not encrypt:
-
Data in memory — when clients query data, the response is in plaintext, because reads come from memory, not disk
TDE applies at the instance level. It cannot be enabled for individual keys or databases within an instance.
Restrictions
Enabling TDE permanently changes how the instance operates. After TDE is enabled:
-
Cross-zone migration is blocked. The instance cannot be migrated across zones. For details, see Migrate an instance across zones.
-
Offline key analysis is unavailable. The offline key analysis feature is not supported for TDE-enabled instances. For details, see Offline key analysis.
-
Cannot join a distributed instance. The instance cannot be converted into a child instance of a distributed instance. For details, see Create a distributed instance.
-
DTS migration and sync are blocked. The instance cannot be migrated or synchronized using Data Transmission Service (DTS).
-
Recycle bin restore is unavailable. Instances with TDE enabled cannot be restored from the recycle bin.
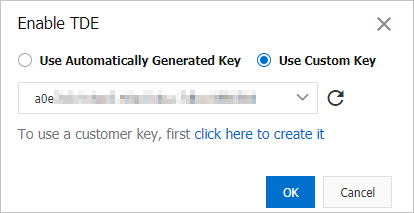
Choose a key type
Before enabling TDE, decide which key type to use:
| Key type | Description | When to use |
|---|---|---|
| Automatically generated key | KMS generates and manages the key on your behalf | Suitable for most use cases — no additional key management overhead |
| Custom key | You provide a key created in KMS | Use when your security policy requires you to control and rotate your own encryption keys |
To create a custom key, see Create a key in the KMS documentation.
Enable TDE
-
Log on to the console and go to the Instances page. In the top navigation bar, select the region where the instance is deployed. Find the instance and click its ID.
-
In the left navigation pane, click TDE Settings.
-
Turn on the switch next to TDE Status.
If the switch is dimmed, the instance is running an earlier minor version. Update the minor version first. For details, see Update the minor version and proxy version.
-
In the dialog box, select Use Automatically Generated Key or Use Custom Key, then click OK.
If this is the first time you enable TDE for an instance in your Alibaba Cloud account, follow the on-page instructions to assign the AliyunRdsInstanceEncryptionDefaultRole role. After authorization is complete, KMS key services become available.
The instance status changes to Modifying TDE. When the status changes to In operation, TDE is enabled.
FAQ
Can I decrypt an RDB backup file that I downloaded?
No. Downloaded RDB backup files cannot be decrypted directly. To access the data, restore the backup set to a new instance — the data is automatically decrypted after restoration.
Why does data queried by clients appear in plaintext?
TDE only encrypts data files on disk (RDB backup files). When you query data, the system reads from memory, which is not encrypted, so the response is in plaintext.
API reference
| API operation | Description |
|---|---|
| ModifyInstanceTDE | Enables TDE for an instance using an automatically generated key or a custom key |
| DescribeInstanceTDEStatus | Checks whether TDE is enabled for an instance |
| DescribeEncryptionKeyList | Lists the custom keys available for TDE on an instance |
| DescribeEncryptionKey | Gets the details of a custom key available for TDE on an instance |
| CheckCloudResourceAuthorized | Checks whether the instance is authorized to use KMS |