To enhance the sign-in security for all RAM users in your Alibaba Cloud account and meet enterprise security and compliance requirements, you can configure a unified password policy. This policy can include rules for password length, password validity period, and password history. This topic describes how to configure the password policy and provides best practices.
A password policy is an account-level global setting. Once modified, it affects all RAM users in the current Alibaba Cloud account. RAM does not support different password policies for different user groups or individual users.
Usage notes
Before you configure a password policy, note the following:
Policy scope: The password policy applies only to RAM users who sign in to the console with a username and password. It does not affect programmatic access that uses an AccessKey.
When policy changes take effect: After you modify the password policy, for example, by increasing the required password length or setting an expiration period, existing users are not immediately forced to change their passwords. The new policy is enforced the next time a user is prompted to change their password upon signing in, or when they manually reset their password.
Special sign-in scenarios:
SSO integration: If your enterprise uses an identity provider (IdP) for SSO integration with Alibaba Cloud, you do not need to set sign-in passwords for RAM users. If you do configure sign-in passwords for RAM users, they are still subject to the password policy and can be used to sign in after SSO is disabled.
Alibaba Cloud does not store your password in plaintext. It only stores a salted hash value generated through one-way encryption. This value cannot be reversed to reveal the original password, ensuring your password remains secure.
Procedure
As the root account or a RAM user with RAM administrator permissions (AliyunRAMFullAccess), you can configure or modify a unified password policy for all RAM users.
Console
Sign in to the RAM console.
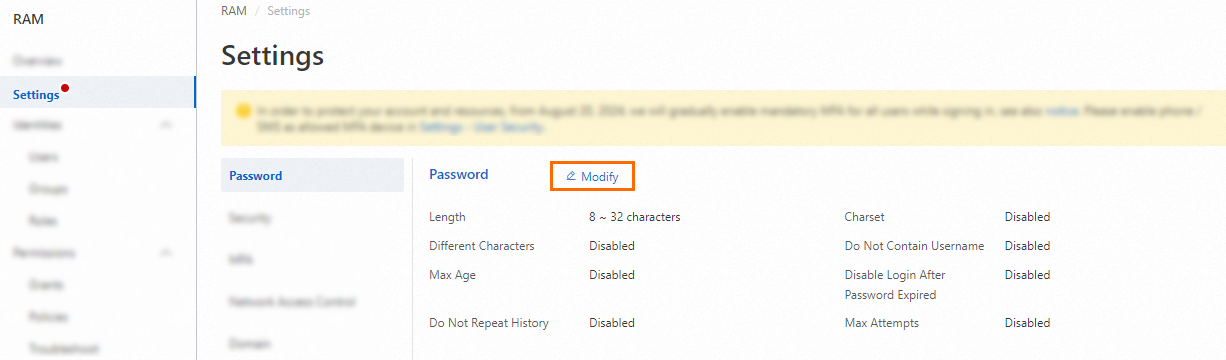
On the Settings page, in the Password Policy section, click Modify to configure the password rules.
Click OK.
API
Call the GetPasswordPolicy operation to view the current password policy.
Call the SetPasswordPolicy operation to modify the password policy.
Password policy parameters
Parameter | Description | Default | Recommendation |
Password length | The minimum number of characters required in a password. Valid values: 8 to 32. | 8 | |
Required character types | The character types that must be included in a password. Options include uppercase letters, lowercase letters, numbers, and symbols. | Disabled | We recommend selecting at least three character types. |
Minimum unique characters | The minimum number of unique characters required in a password. Maximum value: 8. For example, if you set this to 3, a password like | Disabled | Set this to 4 or higher to prevent weak passwords constructed from repeating characters. |
Do not contain username | Prevents the password from containing the username. | Disabled | We recommend that you enable this setting. |
Disable login after password expiration | Determines whether a user with an expired password can still sign in to the console to change it. If enabled, the user must contact an administrator to reset their password before they can sign in again. | Disabled | Setting a password validity period or an initial password validity period might cause some passwords to expire immediately. To avoid sign-in disruptions, we recommend that you do not enable this setting while adjusting these validity periods. |
Password validity period | The maximum number of days a password can be used before it expires. Unit: days. Maximum value: 1095. Note Resetting a password restarts its validity period. | Disabled | We recommend a period of 90 days or less. |
Initial Password Max Age | Controls the validity period of an initial password. If a user does not sign in successfully at least once within this period, the initial password automatically expires. You can set a period from 0 to 90 days. A value of 0 disables this policy. | 14 days | We recommend keeping the default of 14 days. The initial password validity period should not exceed the password validity period. |
Password history | Specifies whether to prevent users from reusing their recent passwords. You can prevent the reuse of up to the last 24 passwords. | Disabled | |
Password retry attempts | The maximum number of consecutive failed sign-in attempts allowed within one hour before the account is locked for one hour. Maximum value: 32. Note Resetting a password clears the count of failed sign-in attempts. | Disabled | We recommend a maximum of 5 attempts. |
Intercept Risk Password From API | When enabled, the system performs a risk assessment on passwords that are set by using the | Disabled | Before enabling this setting, review your existing automation scripts and programs to ensure the passwords they set can pass the risk assessment. After this feature is enabled, API calls that attempt to set a weak password will fail, which may disrupt user creation or password reset workflows. |