This topic describes best practices for securely providing credentials to applications and tools that need to make programmatic API calls to Alibaba Cloud. Following these practices helps you mitigate the security risks associated with credential exposure.
Understand credentials for programmatic access
When you access Alibaba Cloud programmatically using an SDK, CLI, or other development tool, you must provide credentials to authenticate your identity. The two primary types of credentials are:
AccessKey pair: A long-term credential consisting of an AccessKey ID and an AccessKey secret. AccessKey pairs are associated with a RAM user and have the same permissions as that user. Because they do not expire, they must be managed with extreme care. For more information, see Create an AccessKey pair.
Security Token Service (STS) token: A short-term, temporary credential with limited permissions and a configurable expiration time. STS tokens are the recommended credential type for most use cases because they significantly reduce the risk associated with a credential leak.
Why you should avoid long-term AccessKey pairs
Improperly managed credentials, especially long-term AccessKey pairs, create significant security risks. A common and serious mistake is to hard-code an AccessKey pair directly into application source code. If this code is committed to a public repository like GitHub, shared with others, or even just stored in a widely accessible internal repository, the credentials can be compromised. An attacker with a valid AccessKey pair can access your Alibaba Cloud resources, potentially leading to data breaches or financial loss.
Best practice: Use temporary credentials with RAM roles
The most secure method for applications to access Alibaba Cloud is to use a RAM role to obtain temporary STS tokens. This approach eliminates the need to manage and distribute long-term AccessKey pairs. The recommended method varies based on where your application is running.
For applications on ECS instances
If your application runs on an Elastic Compute Service (ECS) instance, you can assign an instance RAM role to it. The application can then use the Alibaba Cloud SDK to automatically retrieve temporary STS tokens from the instance metadata service without any credentials being stored on the instance.
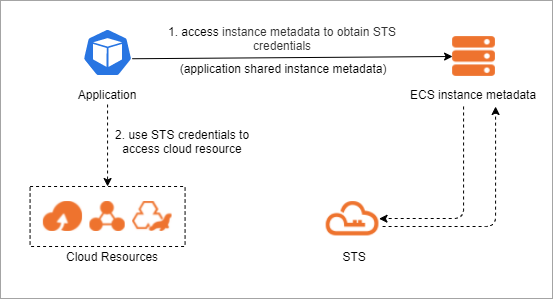
Configuration: For instructions on how to create and attach an instance RAM role, see Attach an instance RAM role.
SDK integration: The Alibaba Cloud SDKs automatically detect and use the instance RAM role. You do not need to configure any credentials in your code.
Examples:
For containerized applications on ACK
For applications running in a Container Service for Kubernetes (ACK) cluster, use the RAM Roles for Service Accounts (RRSA) feature. RRSA allows you to associate a RAM role with a Kubernetes service account. Pods that use this service account can then obtain temporary STS tokens to access authorized Alibaba Cloud resources.
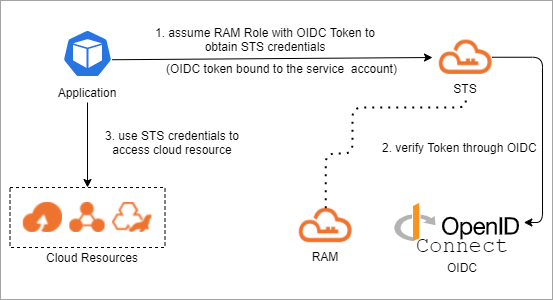
Configuration: For instructions, see Enable RRSA and Use RRSA to authorize different pods to access different cloud services.
Examples:
| Language | Minimum version | Demo |
|---|---|---|
| Go | Alibaba Cloud Credentials for Go 1.2.6 | Go SDK demo |
| Java | Alibaba Cloud Credentials for Java 0.2.10 | Java SDK demo |
| Python 3 | Alibaba Cloud Credentials for Python 0.3.1 | Python SDK demo |
| Node.js / TypeScript | Alibaba Cloud Credentials for TypeScript/Node.js 2.2.6 | Node.js SDK demo |
For serverless applications on Function Compute
If your application is deployed on Function Compute, associate a RAM role with your function. When the function is invoked, it automatically receives temporary STS credentials that it can use to access other Alibaba Cloud services, eliminating the need to embed AccessKey pairs in your function code.
Configuration: For instructions, see Grant Function Compute permissions to access other Alibaba Cloud services.
For developers and CLI access
For developers, administrators, or other human users who need command-line access, the best practice is to integrate your corporate identity provider (IdP) with Alibaba Cloud for single sign-on (SSO). Users can authenticate with their existing corporate credentials to assume a RAM role and receive temporary STS tokens for use with the CLI or other tools.
Configuration: To configure SSO, see Overview of role-based SSO with SAML and Configure SSO. To use the credentials with the CLI, see Use Alibaba Cloud CLI to log on to the CloudSSO user portal.
Manage long-term credentials securely (if required)
If using RAM roles and temporary credentials is not possible for your use case, and you must use a long-term AccessKey pair, store it securely using environment variables or a credentials file. Do not hard-code it in your application.
Using long-term AccessKey pairs is not a recommended practice. Prefer the role-based methods described above whenever possible.
You can configure your AccessKey ID and secret as environment variables:
Linux and macOS
Run the following commands:
export ALIBABA_CLOUD_ACCESS_KEY_ID=<access_key_id> export ALIBABA_CLOUD_ACCESS_KEY_SECRET=<access_key_secret>Replace
<access_key_id>with your AccessKey ID and<access_key_secret>with your AccessKey secret.Windows
Create an environment variable file, add the
ALIBABA_CLOUD_ACCESS_KEY_IDandALIBABA_CLOUD_ACCESS_KEY_SECRETenvironment variables to the file, and then specify your AccessKey ID for ALIBABA_CLOUD_ACCESS_KEY_ID and your AccessKey secret for ALIBABA_CLOUD_ACCESS_KEY_SECRET.Restart the Windows operating system.
The Alibaba Cloud SDKs are designed to automatically search for credentials in a specific order, starting with environment variables. If you set these variables, you can initialize the SDK client without providing any credentials in your code.
Example:
import com.aliyun.credentials.Client;
import com.aliyun.credentials.models.Config;
public class DemoTest {
public static void main(String[] args) throws Exception{
Config config = new Config();
// Which type of credential you want
config.setType("access_key");
// AccessKeyId of your ram user
config.setAccessKeyId(System.getenv("ALIBABA_CLOUD_ACCESS_KEY_ID"));
// AccessKeySecret of your ram user
config.setAccessKeySecret(System.getenv("ALIBABA_CLOUD_ACCESS_KEY_SECRET"));
Client client = new Client(config);
}
}What to do if credentials are leaked
If you suspect an AccessKey pair or STS token has been compromised, you must take immediate action to protect your account. For detailed steps, see Remediate a compromised AccessKey pair and RAM roles and STS tokens.