When a Resource Access Management (RAM) principal (a RAM user or role) makes a request to access an Alibaba Cloud resource, RAM evaluates all applicable policies to determine whether the request should be allowed or denied. This topic explains the complete evaluation process.
Core principles of evaluation
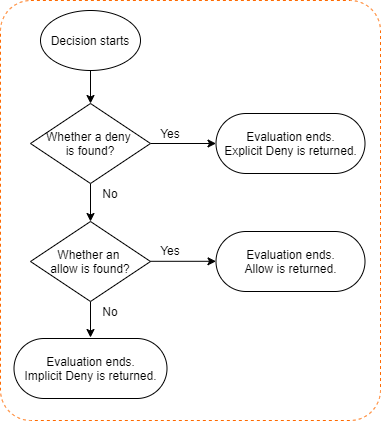
All policy evaluations follow two fundamental principles:
Deny by default: By default, a RAM principal has no permissions. Unless a policy explicitly allows a request, it is implicitly denied.
Explicit deny overrides allow: If any applicable policy contains an explicit
Denystatement for the request, the request is immediately denied, regardless of anyAllowstatements in other policies.
The evaluation flow
When a request is made, RAM evaluates different types of policies in a specific order. If a decision to deny the request is reached at any step, the evaluation stops immediately. The request is only allowed if it passes through all applicable policy checks without being denied.
The standard evaluation process includes the following steps:
Step 1: Evaluate the control policies of Resource Directory
If the account involved in the request is a member of a resource directory, RAM first evaluates the applicable control policies. Control policies act as permission guardrails for an account.
If the control policy does not allow the requested action, the request is denied and the evaluation stops.
If it is allowed, the evaluation proceeds to the next step.
If no control policies exist, this step is skipped.
Control policies apply to all RAM principals (users and roles) within a member account but do not apply to the owner of that account or any principals in the management account of the Resource Directory.
Step 2: Evaluate the session policies of RAM roles
If the requesting principal is a RAM role that was assumed with a temporary session policy (such as by calling the AssumeRole operation), RAM evaluates that policy.
If the session policy does not allow the requested action, the request is denied and the evaluation stops.
If it is allowed, the evaluation proceeds.
If no session policies exist, this step is skipped.
Step 3: Evaluate identity-based and resource-based policies
RAM then evaluates both identity-based policies (attached to the RAM user or role making the request) and resource-based policies (attached to the resource being accessed).
Identity-based policy: RAM evaluates all policies attached to the requesting principal. If any of these policies explicitly deny the request, the result is an explicit deny. If at least one policy allows the request, the result is an allow. Otherwise, the result is an implicit deny.
Resource-based policy: If the target resource has a resource-based policy (such as an OSS bucket policy or a RAM role's trust policy), RAM evaluates it. The logic is the same: the result is an allow, an explicit deny, or an implicit deny. If there is no resource-based policy, this check is skipped.
Step 4: Combine decisions and determine final outcome
Finally, RAM combines the results from all preceding steps to make a final decision.
If an explicit deny was produced at any step, the final decision is DENY.
If there are no explicit denies, and at least one allow was produced (from either an identity-based or resource-based policy), the final decision is ALLOW.
In all other cases (if no policies explicitly allow the request), the final decision is an implicit deny.
Special evaluation cases
Assuming a RAM role: The logic for assuming a RAM role is a special case. It requires an
Allowfrom both the principal's identity-based policy and the RAM role's trust policy. For more information, see How RAM evaluates policies when a role is assumed.Object Storage Service (OSS): For requests to OSS, access control lists (ACLs) on buckets or objects are evaluated after RAM policies. A request may be denied by an ACL even if it is allowed by a RAM policy. For more information, see OSS authorization.