The over-privileged identity analyzer is a feature within Resource Access Management (RAM) that helps you identify RAM users and roles with excessive permissions. It continuously monitors identities in your Alibaba Cloud account or Resource Directory and generates findings, enabling you to systematically review and reduce permissions to achieve least privilege.
How it works
The analyzer works by consuming data from RAM Access Auditing, which tracks the permissions granted to an identity and when those permissions were last used. Based on this data and a configurable time window, the analyzer generates findings that are categorized into the following types:
Super administrator: The identity has full administrative privileges (such as the
AdministratorAccesspolicy is attached), granting unrestricted access to all resources in the account.Privileged user or role: The identity has permissions to perform high-risk operations that could lead to privilege escalation, such as changing permission policies or creating AccessKey pairs for other users. For a complete list, see the "Appendix: High-risk privileges" section in this topic.
Inactive user or role: The identity has not used any of its permissions to access any service within the configured time window for unused access.
Over-privileged user or role: The identity has one or more permissions that have not been used within the configured time window for unused access.
Analyzer scope
You can create an analyzer to monitor RAM identities within either the current Alibaba Cloud account or, if you are using a management account, across your entire resource directory. The analyzer does not check service-linked roles.
Create an over-privileged identity analyzer
Log on to the RAM console as a RAM administrator.
In the left-side navigation pane, choose .
On the Analyzers page, click Create Analyzer.
On the Create Analyzer page, configure the following parameters:
Analyzer Type: Select Over-privileged Access.
Analyzer Name: Enter a descriptive name for your analyzer.
Unused Access Age: Specify the number of days (1-180) an unused permission should be considered inactive. The default is 90 days.
Analyzer Scope: Choose to analyze the Current Account or your entire Resource Directory.
NoteThe Resource Directory option is only available to the management account

Click Create Analyzer.
After creation, the analyzer begins to evaluate your resources. It may take some time before the initial findings are generated.
View and manage findings
You can view findings on the Analyzers page for a dashboard overview or on the Findings page for a detailed, filterable list.
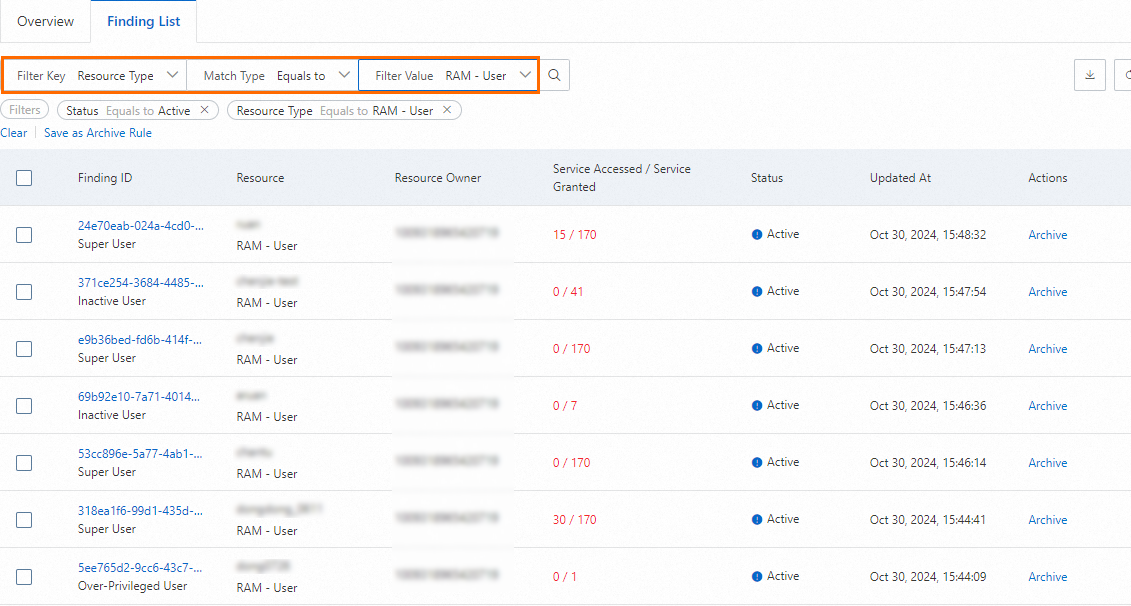
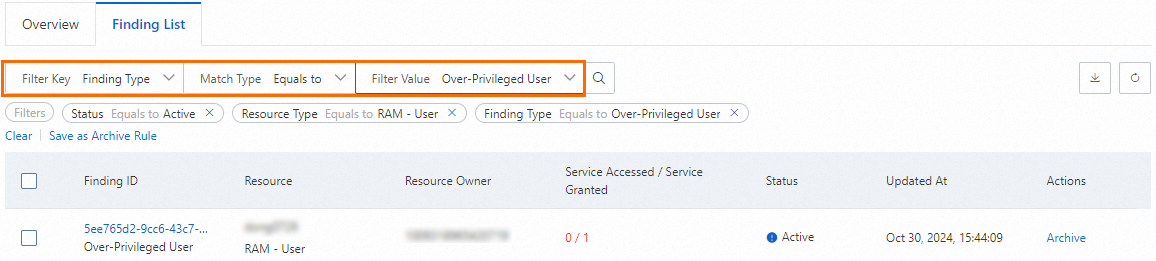
Filter findings
On the Findings page, you can use filters to narrow down the results. For example, to find all over-privileged RAM users, apply a filter for Resource Type equal to RAM - User and Finding Type equal to Over-Privileged User.
Take action on a finding
To investigate a specific finding, click its ID in the findings list. This opens the finding details page.
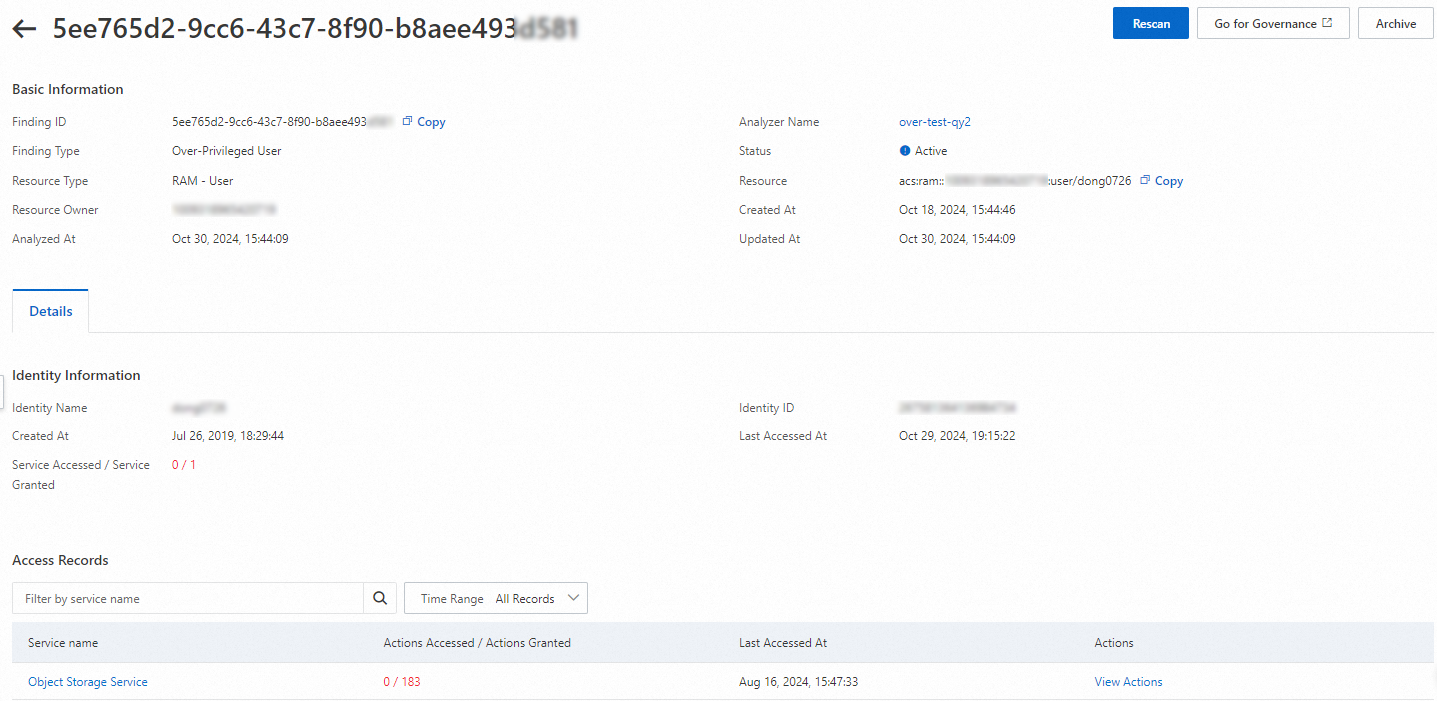
From the details page, you can perform one of the following actions:
Archive: If you have reviewed the finding and determined that the permissions are necessary and intentional, you can archive it to remove it from the active list.
Go for Governance: If the permissions are excessive and need to be reduced, click this button to navigate directly to the user or role's permissions page to modify the attached policies.
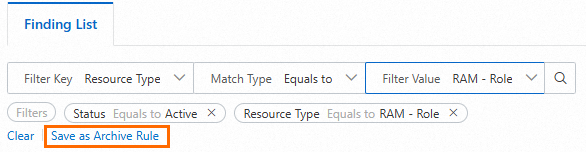
Create archival rules
To automatically suppress findings for known and approved external access, you can create an archive rule. An archive rule automatically archives any new findings that match its criteria.
On the Findings page, configure one or more filters that define the findings you want to automatically archive.
Click Save as Archive Rule.
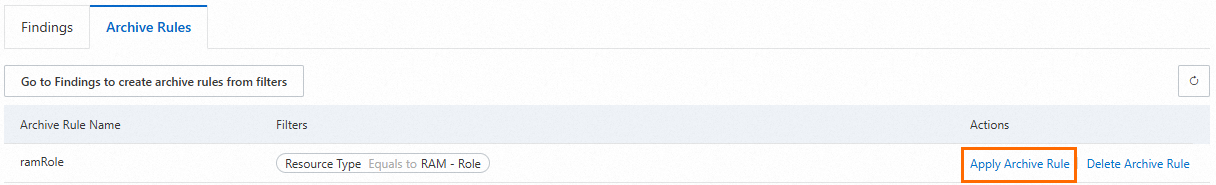
To apply a new rule to findings that already exist, navigate to the Analyzers page, click your analyzer's name, select the Archive Rules tab, and click Apply Archive Rule for the desired rule.
Appendix: High-risk privileges
The following table lists the specific high-risk actions that will trigger a "Privileged User" or "Privileged Role" finding.
Cloud service | High-risk action |
RAM | ram:AddUserToGroup |
ram:AttachPolicyToGroup | |
ram:AttachPolicyToRole | |
ram:AttachPolicyToUser | |
ram:CreateAccessKey | |
ram:CreatePolicyVersion | |
ram:DeletePolicy | |
ram:DeletePolicyVersion | |
ram:DetachPolicyFromGroup | |
ram:DetachPolicyFromRole | |
ram:DetachPolicyFromUser | |
ram:RemoveUserFromGroup | |
ram:SetDefaultPolicyVersion | |
ram:UpdateAccessKey | |
ram:UpdateRole | |
ram:CreateLoginProfile | |
ram:UpdateLoginProfile | |
ram:SetSecurityPreference | |
ram:RestoreAccessKeyFromRecycleBin | |
ram:SetUserSsoSettings | |
ram:CreateSAMLProvider | |
ram:UpdateSAMLProvider | |
ram:UpdateOIDCProvider | |
ram:AddClientIdToOIDCProvider | |
ram:AddFingerprintToOIDCProvider | |
Resource Management | ram:AttachPolicy |
ram:DetachPolicy | |
resourcemanager:EnableResourceDirectory | |
resourcemanager:CreateResourceAccount | |
resourcemanager:InviteAccountToResourceDirectory | |
resourcemanager:UpdateAccount | |
resourcemanager:DisableControlPolicy | |
resourcemanager:UpdateControlPolicy | |
resourcemanager:DeleteControlPolicy | |
resourcemanager:AttachControlPolicy | |
resourcemanager:DetachControlPolicy | |
resourcemanager:RegisterDelegatedAdministrator | |
CloudSSO | cloudsso:EnableDelegateAccount |
cloudsso:UpdateUserStatus | |
cloudsso:ResetUserPassword | |
cloudsso:SetLoginPreference | |
cloudsso:AddUserToGroup | |
cloudsso:RemoveUserFromGroup | |
cloudsso:SetExternalSAMLIdentityProvider | |
cloudsso:AddExternalSAMLIdPCertificate | |
cloudsso:AddPermissionPolicyToAccessConfiguration | |
cloudsso:RemovePermissionPolicyFromAccessConfiguration | |
cloudsso:UpdateInlinePolicyForAccessConfiguration | |
cloudsso:ProvisionAccessConfiguration | |
cloudsso:DeprovisionAccessConfiguration | |
cloudsso:CreateAccessAssignment | |
cloudsso:DeleteAccessAssignment | |
cloudsso:CreateSCIMServerCredential | |
cloudsso:UpdateSCIMServerCredentialStatus | |
cloudsso:SetSCIMSynchronizationStatus |