ApsaraDB for MongoDB integrates with Simple Log Service (SLS) to provide audit logging for your instances. With audit logs, you can query, analyze, and export the operation history of an instance to track security events and meet compliance requirements.
The audit log feature is no longer available as a free trial. Billing applies based on storage capacity and retention period.
Prerequisites
Before you begin, ensure that you have:
-
A replica set instance or sharded cluster instance. Standalone instances do not support audit logs.
-
Simple Log Service (SLS) activated. For details, see Getting started.
-
If using a Resource Access Management (RAM) user to enable the audit log feature, the following permissions granted to the RAM user:
-
AliyunLogFullAccess — a system policy. For details, see Grant permissions to a RAM user.
-
dds:CheckServiceLinkedRole — a custom policy. Create this policy in the RAM console before attaching it to the RAM user. For details on creating the policy, see Create custom policies. For details on granting permissions, see Grant permissions to a RAM user.
Policy document for
dds:CheckServiceLinkedRole:{ "Version": "1", "Statement": [ { "Effect": "Allow", "Action": "dds:CheckServiceLinkedRole", "Resource": "*" } ] }
-
-
If using a RAM user to access audit logs, AliyunLogFullAccess or AliyunLogReadOnlyAccess granted to the RAM user. For details, see Grant permissions to a RAM user.
Billing
Audit log charges are based on storage capacity and the retention period. The following table lists unit prices by region.
| Region | Unit price (USD per GB-hour) |
|---|---|
| Regions in the Chinese mainland | 0.002 |
| Hong Kong (China) | 0.006 |
| Singapore | 0.004 |
| UAE (Dubai) | 0.004 |
| US (Silicon Valley) | 0.004 |
| US (Virginia) | 0.004 |
| UK (London) | 0.004 |
| Germany (Frankfurt) | 0.004 |
| Japan (Tokyo) | 0.004 |
| Malaysia (Kuala Lumpur) | 0.004 |
| Indonesia (Jakarta) | 0.004 |
| Philippines (Manila) | 0.004 |
Actual charges are based on the unit price shown at purchase and reflected in your bill. For the latest pricing, see the Pricing tab on the ApsaraDB for MongoDB product page.
To reduce audit log costs:
| Method | Trade-off | Reference |
|---|---|---|
| Set a shorter retention period | Reduces the traceable history of audit logs | Modify the retention period for audit logs |
| Select fewer operation types | Removed operation types stop being logged; existing logs within the retention period are kept until they expire | Modify operation types for audit logs |
| Disable the audit log feature | Stops all audit log uploads; subsequent operations are no longer tracked | Disable the audit log feature |
|
Region |
Price (USD/GB/hour) |
|
All regions in the Chinese mainland |
0.002 |
|
China (Hong Kong) |
0.006 |
|
Singapore |
|
|
UAE (Dubai) |
|
|
US (Silicon Valley) |
|
|
US (Virginia) |
|
|
UK (London) |
|
|
Germany (Frankfurt) |
|
|
Japan (Tokyo) |
0.004 |
|
Malaysia (Kuala Lumpur) |
|
|
Indonesia (Jakarta) |
|
|
Philippines (Manila) |
Enable audit logs
Enabling audit logs does not require restarting the instance.
After you enable audit logging, ApsaraDB for MongoDB audits and records all write operations on the instance. Expect a performance decrease of 5%–15%, along with increased latency and jitter. The actual impact depends on the volume of data written or audited. If your application writes large volumes of data, enable audit logging only for troubleshooting or security auditing—not as a permanent configuration.
-
Log on to the ApsaraDB for MongoDB console.
-
In the left-side navigation pane, click Replica Set Instances or Sharded Cluster Instances.
-
In the upper-left corner, select the resource group and region of the instance.
-
Click the instance ID, or click Manage in the Actions column.
-
In the left-side navigation pane of the instance details page, choose Data Security > Audit Logs.
-
On the Latest Audit Logs page, set the Log Retention Period parameter.
-
Valid values: 1–365 days. Default: 30 days.
-
This setting applies to all instances in the same region. Evaluate retention requirements for all instances in the region before changing this value.
-
-
Click Enable Audit Logs.
ApsaraDB for MongoDB automatically obtains the AliyunServiceRoleForMongoDB service-linked role to access SLS on your behalf.
-
In the Enable Audit Logs dialog box, review the prompt and click OK.
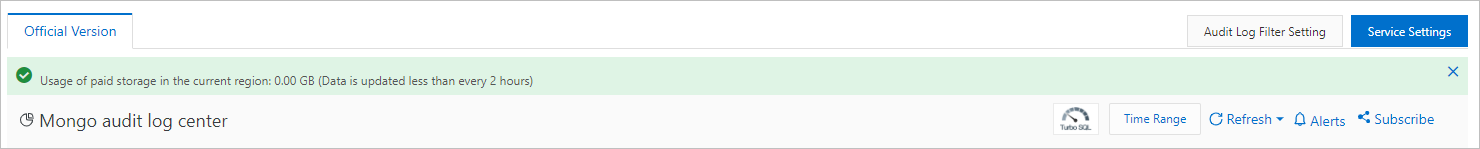
After audit logging is enabled, go to the Mongo audit log center page to view the billable storage capacity of audit logs in the current region.
Usage notes
-
By default, the enabled operation types are admin and slow. To change the operation types, see Modify operation types for audit logs.
-
The log retention period you set applies to the current instance and all other instances in the same region. Evaluate the retention needs of all instances in the region before setting this parameter.
API reference
| Operation | Description |
|---|---|
| DescribeAuditPolicy | Queries whether the audit log feature is enabled for an instance |
| ModifyAuditPolicy | Enables or disables the audit log feature; optionally sets a log retention period |