Lindorm Insight is a web-based cluster management system for viewing cluster storage usage and managing cluster data.
Prerequisites
Before you begin, make sure that you have:
A Lindorm instance. See Create an instance
The public IP address you'll use to access the cluster management system added to the Lindorm whitelist. See Configure a whitelist
If this is your first time logging on, set a password before you begin. On the Wide Table Engine page, go to the Lindorm Insight section and click Reset UI Access Password. Your password must be 2–30 characters and contain at least one uppercase letter, lowercase letter, digit, or special character (underscore _ or hyphen -).
Log on to Lindorm Insight
Log on to the Lindorm Management Console.
On the Instances page, click the ID of your target instance.
In the navigation pane on the left, click Database Connections.
On the Wide Table Engine page, go to the Lindorm Insight section and click By ClusterManager Internet Visit or By ClusterManager VPC Visit to log on to the cluster management system.

On the Log On page, enter your username and password, then click Log On.
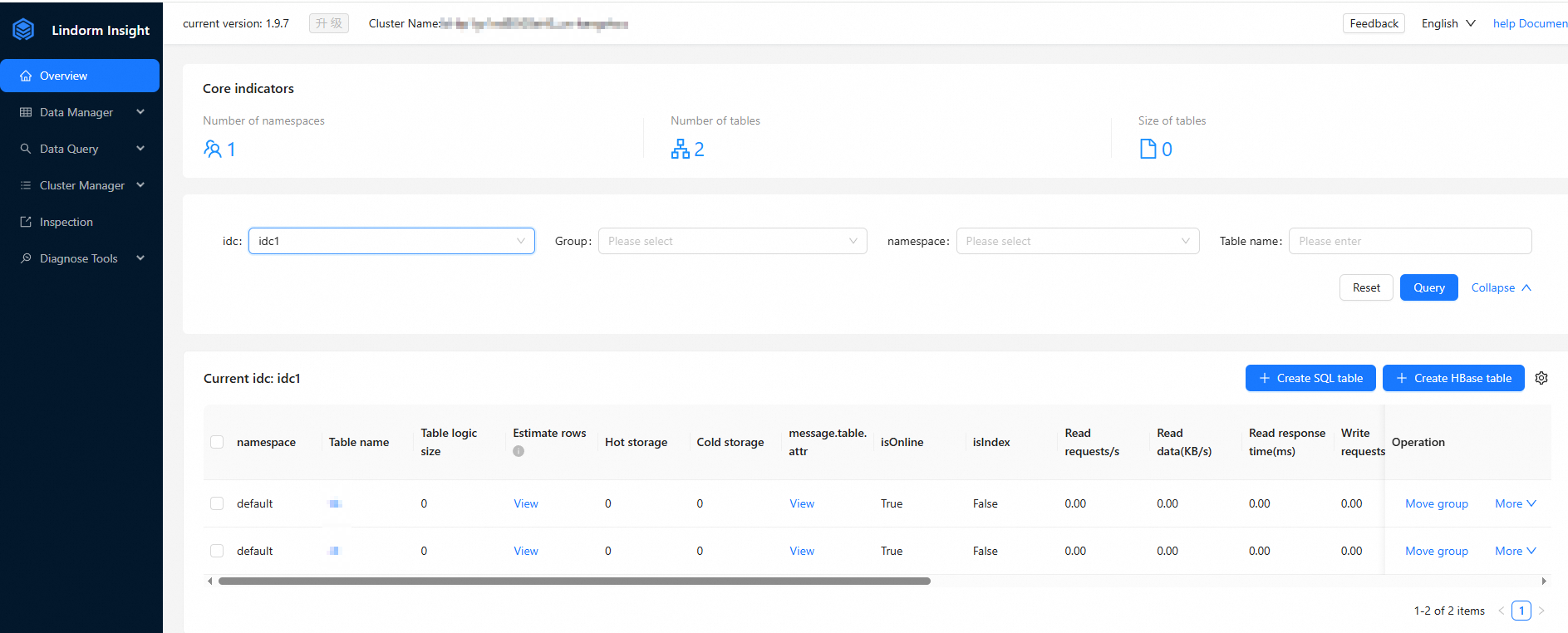
The Lindorm Insight page opens.
What you can do in Lindorm Insight
Lindorm Insight is organized into five main sections. The following table describes each page and its functions.
| Section | Page | What you can do | Reference |
|---|---|---|---|
| Overview | — | View basic information about all tables in the cluster. View table details and manage tables. | Overview |
| Data Management | Namespace management | View all namespaces. Add or delete namespaces. | Namespace management |
| Data Management | User management | View users and their permissions. Add or delete users. Grant or revoke permissions. | Manage users and Manage ACL permissions |
| Data Management | Table change management | Change table properties. | Table change management |
| Data Query | SQL executor | Query data in Lindorm wide tables using SQL. | Data query |
| Cluster Management | Group and node management | View storage usage for groups and nodes. Add or delete groups. | Group and node management |
| Diagnostics | Large query request detection | Detect large query operations such as large scans. | Large query request detection |
| Diagnostics | topRegion analysis | Sort and display regions by different metrics and dimensions. | topRegion analysis |
| Diagnostics | Client source tracing | View information about clients accessing the cluster. | Client source tracing |
FAQ
Why do I get the error "Your current password is weak" even though my password meets the requirements?
This error means your password follows the format rules but is still considered easy to guess — for example, a sequence of consecutive numbers or keys that are adjacent on the keyboard. Use a less predictable combination and try again.