IDaaS EIAM connects to your directory services and applications through a network access endpoint. By default, EIAM uses a Shared Network Access Endpoint, which is free and supports public network access only. To sync with AD or LDAP over a private network, or to use a fixed egress IP for third-party allowlists (such as WeCom), you must purchase and configure a Dedicated Network Access Endpoint.
How it works
When you add a dedicated endpoint, EIAM creates an Elastic Network Interface (ENI) inside your virtual private cloud (VPC). EIAM routes all outbound traffic through that ENI, using your network, your security groups, and your IP addresses.
This architecture enables two access modes:
Private network access: EIAM syncs with AD, LDAP, and other services on your private network, and enables delegated authentication, without opening public ports. You must allow inbound traffic from the ENI's IP address in the security group of your AD or LDAP server.
Public network access with a fixed IP: Associate an Elastic IP Address (EIP) with the ENI for the EIAM instance, or associate an Internet NAT gateway with your Alibaba Cloud VPC, so that EIAM uses your public IP for outbound connections. Add this IP to WeCom's trusted IP list to meet WeCom's verification requirements.
Each EIAM instance supports a maximum of one Dedicated Network Access Endpoint.
Choose an endpoint type
| Capability | Dedicated endpoint | Shared endpoint |
|---|---|---|
| Access a private network with a dedicated IP | Supported | Not supported |
| Access the public network with a dedicated IP | Supported | Not supported |
| Access the public network with a shared IP | Not supported | Supported |
| ENI and security group ownership | Your Alibaba Cloud account | IDaaS team |
| Available by default | No | Yes |
| Free | No | Yes |
Use a dedicated endpoint when you need to sync with AD or LDAP over a private network, or when a third-party service (such as WeCom) requires a fixed egress IP in its allowlist.
Use the shared endpoint when your integrations only need public network access and do not require a fixed egress IP.
Endpoint support by module
By default, each module uses the shared endpoint. To switch a module to a dedicated endpoint, perform a manual switchover after the endpoint is set up.
| Module | Dedicated — private network | Dedicated — public network | Shared — public network |
|---|---|---|---|
| DingTalk inbound identity provider (IdP) | Not supported | Not supported | Supported |
| DingTalk outbound identity provider | Not supported | Not supported | Supported |
| AD inbound identity provider | Supported | Supported | Supported |
| LDAP inbound identity provider | Supported | Supported | Supported |
| WeCom inbound identity provider | Not supported | Supported | Not supported |
| Marketplace application | Not supported yet | Not supported yet | Supported |
| SAML application | Not supported yet | Not supported yet | Supported |
| OIDC application | Not supported yet | Not supported yet | Supported |
| Custom application | Not supported yet | Not supported yet | Supported |
Private network connectivity options
For AD, the required network setup depends on where your AD domain server is hosted.
| AD server location | Required network setup |
|---|---|
| Same VPC as the EIAM ENI | In the AD domain server's security group, allow inbound traffic from the ENI's IP address |
| Different VPC on Alibaba Cloud | Connect the VPCs using Cloud Enterprise Network (CEN), then allow the ENI's IP in the AD server's security group |
| On-premises data center or another cloud platform | Connect the VPC to the data center using a leased line or VPN, then allow the ENI's IP in the firewall where the AD server is located |
Add a dedicated endpoint
Before you begin, confirm the following:
Your EIAM instance is an Enterprise instance, or you are prepared to upgrade from Free Edition or trial
You have the
AliyunIDaaSEiamFullAccesspermission, or you are using the Alibaba Cloud account owner credentials (required to create the service-linked role)A service-linked role (SLR) for IDaaS EIAM exists, or you have permission to create one
You have identified the target VPC — the VPC where your AD, LDAP, or application servers reside, or from which those servers are reachable
Each vSwitch you plan to select has more than 2 available IP addresses
The dedicated endpoint quota has been purchased, or you are prepared to purchase it
You can select a maximum of two vSwitches. Selecting vSwitches in different availability zones improves disaster recovery.
Steps:
In the IDaaS EIAM console, go to the Network Access Endpoint tab.
Create the SLR if prompted. Only the Alibaba Cloud account owner or a user with
AliyunIDaaSEiamFullAccesscan create the SLR. If the role already exists, skip this step.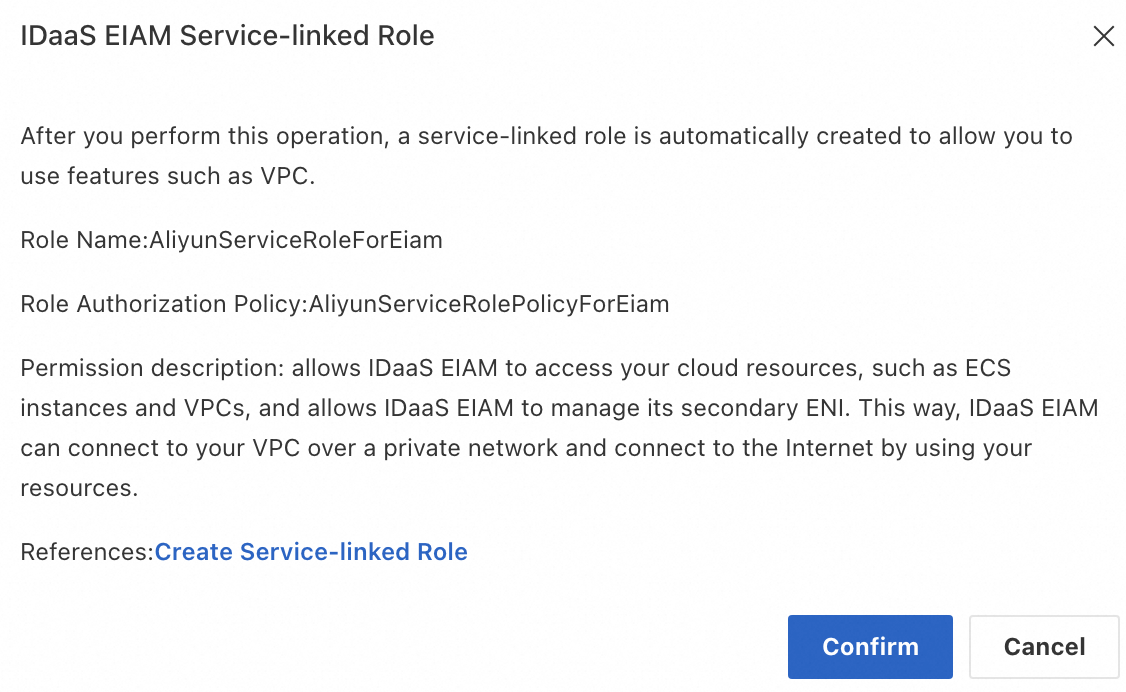
Purchase the dedicated endpoint quota if the number of existing dedicated endpoints has reached your quota limit.
For a Free Edition or trial instance: Upgrade the instance and purchase the Dedicated Network Access Endpoint quota on the purchase page.
For an Enterprise instance: Scale up the instance and purchase the Dedicated Network Access Endpoint quota on the purchase page.
Click Add Dedicated Endpoint and fill in the required fields:
Field Description Display Name A label shown only in the console Select Region The region where your target VPC is located Select VPC The VPC where your AD, LDAP, or application servers reside, or from which they are reachable Select vSwitch One or two vSwitches in the selected VPC; each must have more than 2 available IP addresses ImportantAfter the endpoint is created, you cannot change the region, VPC, or vSwitch. Confirm your selections before proceeding.
Click Confirm to create the endpoint.
After the endpoint is created, configure it for the access type you need:
Private network access: See Authorize private network access.
Public network access with a fixed IP: See Configure a dedicated public egress IP address.
Authorize private network access
On the Network Access Endpoint tab, find the target Dedicated Network Access Endpoint and click Authorize Private Network Access.
In the Authorize Private Network Access dialog box, copy the Authorization Object. This value contains all exclusive private egress IP addresses for the endpoint.
Click Add to navigate to Elastic Computing Service > Security Groups. Select the security group where your target service is located.
For AD, select the security group for your AD domain server — not the security group created by EIAM.
Click the Security Group ID/Name to open the security group details page. On the Access Rule > Inbound tab, click Add Rule.
Fill in the inbound rule:
Field Value Authorization Policy Allow Priority 1 Protocol Type Custom TCP Port Range The port for your service. For AD or LDAP, use port 389 or 636. Authorization Object The egress IP addresses copied in step 2 Save the rule.
Configure a dedicated public egress IP address
An Internet NAT gateway gives the EIAM instance a fixed public IP for outbound connections. Add this IP to WeCom's trusted IP list to satisfy WeCom's verification requirements.
On the Network Access Endpoint tab, note the VPC Region of the target Dedicated Network Access Endpoint.
Go to the VPC - Internet NAT Gateway console. Select an Internet NAT gateway in the same region as your VPC. If no NAT gateway exists, create one first. See Create an Internet NAT gateway.
Click Associate Now to associate an EIP with the NAT gateway. Select an existing EIP or purchase a new one.
After the EIP is associated, open the NAT gateway's Instance ID/Name.
If no SNAT entry exists for this NAT gateway, create one to enable outbound public network access for the dedicated endpoint. See Create and manage SNAT entries.
WarningWithout an SNAT entry, the dedicated endpoint cannot access the public network.
Back on the Network Access Endpoint tab, click View in the Dedicated Outbound Public IP Address column to confirm the public IP assigned to the endpoint.
Switch to a dedicated endpoint
After the dedicated endpoint is configured, switch your identity provider (IdP) to use it.
Test this in a staging environment first. After verification passes, the switch takes effect immediately.
Navigate to the IdPs page and click Modify for the target IdP (for example, your Active Directory domain).
In Network Configurations > Network Access Endpoint, select Dedicated Network Access Endpoint from the type selector, then choose the endpoint from the drop-down list. If you need public network access, select an endpoint that has a Dedicated Outbound Public IP Address attached.
Click Confirm. The system verifies that all associated ENIs (up to two) can reach the AD service.
If verification passes, the system switches to the dedicated endpoint immediately.
If verification fails, an error message appears. Check the following before retrying:
Check What to verify Security group rule The inbound rule allows the ENI's egress IP on the correct port (389 or 636 for AD/LDAP) ENI status The ENI has finished provisioning Port range The port in the security group rule matches the port your service listens on CEN or VPN connectivity If the AD server is in a different VPC or on-premises, the network path is up
Modify a dedicated endpoint
Only the Display Name of a Dedicated Network Access Endpoint can be modified. To change the region, VPC, or vSwitch, delete the endpoint and create a new one.
Limits and usage notes
Each EIAM instance supports a maximum of one Dedicated Network Access Endpoint.
After an endpoint is created, the region, VPC, and vSwitch cannot be changed.
When a paid instance expires and is released, or when you unsubscribe, the dedicated endpoint becomes unavailable immediately and is deleted one day later. Switch to the shared endpoint or another dedicated endpoint before the instance expires. Update any network access whitelist configurations in your services before deleting the endpoint.