Data security
Hologres has passed an independent third-party audit based on the security, availability, and confidentiality principles of the AICPA Trust Services Criteria for Alibaba Cloud. For more information, see the SOC 3 Report.
Alibaba Cloud has obtained the Payment Card Industry Data Security Standard (PCI DSS) certification, the world's most stringent financial data security standard. This certification confirms that Alibaba Cloud meets the security protection requirements for payment systems and can provide secure and reliable solutions to its customers. For more information, see the PCI DSS Certification Report.
Storage encryption
Hologres supports data-at-rest encryption using Key Management Service (KMS).
Introduction to KMS
KMS is a cryptographic service from Alibaba Cloud designed for data encryption in the cloud. It provides key services that comply with Chinese national cryptographic standards, along with simple encryption and decryption services for your applications. KMS also offers a highly secure, dedicated version that lets you store keys in your own dedicated cloud hardware security module (HSM) cluster. For more information, see What is KMS?.
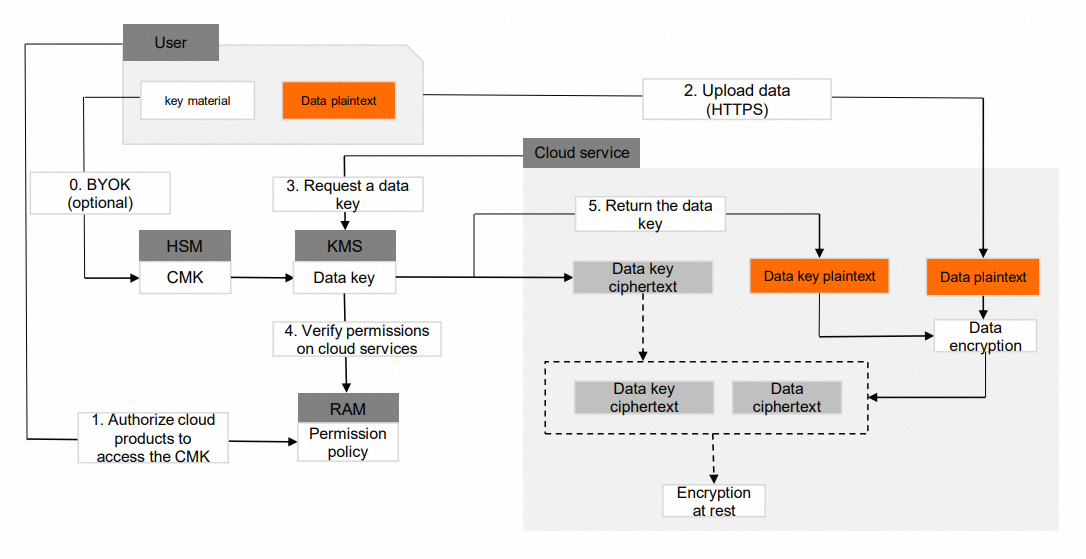
KMS provides HSMs that are tested and certified by the State Cryptography Administration (SCA) and have obtained Level 2 certification for GM/T 0028.
KMS provides only Transport Layer Security (TLS)-based secure access channels and uses only secure transport encryption suites. This complies with PCI DSS security specifications.
Keys are generated in the HSM using a secure random number generation algorithm that uses high system entropy as a seed. This prevents attackers from recovering the keys.
Keys are protected by hardware security mechanisms. The plaintext of a key is used for cryptographic operations only within the HSM and never leaves its security boundary.
You can use ActionTrail to fully audit key usage and confirm that keys are used correctly. You can audit KMS API calls that use keys, regardless of whether the calls are from Alibaba Cloud services or user applications.
Hologres capabilities
Because high-value data stored in a data warehouse often has high security requirements, Hologres supports only Bring-Your-Own-Key (BYOK). BYOK is a visible and controllable semi-managed encryption method. BYOK is an industry-recognized advanced security technology. It allows users to securely import offline-generated keys into a KMS-hosted HSM in the cloud. The HSM ensures that the key cannot be exported. Users can delete the key from the cloud at any time and can import the same key again later. For configuration details, see Encrypt data at rest.
Hologres uses KMS key management and the encryption library provided by the security department to enable storage encryption based on algorithms such as AES-256, AES-128, RC4, and the national standard SM4.
Hologres lets you set a separate encryption rule for each table. This means you can set different KMS keys to encrypt different tables.
When reading and writing data, Hologres calls the KMS API to retrieve key information. The system caches the key information for 24 hours by default. Using the data encryption feature incurs KMS fees. For more information about KMS billing, see KMS 1.0 billing.
After you enable storage encryption, query and write performance is affected by the encryption and decryption operations. The performance loss is about 20% to 40% and varies based on the query characteristics.
Encryption in transit
To improve the link security of the Hologres real-time data warehouse, you can enable SSL to encrypt network connections at the transport layer. This improves the security and integrity of communication data but increases the network connection response time. For usage instructions, see Encryption in transit.
Secure Sockets Layer (SSL) is a security protocol designed for secure communication and data security. An Alibaba Cloud SSL Certificate is a trusted credential issued to a website by a well-known WebTrust-certified Certificate Authority (CA). It serves two functions: website identity verification and encrypted transmission. The HTTP protocol does not encrypt data, so data transmission is vulnerable to information leaks, tampering, or phishing attacks. After you deploy an SSL certificate to a web server, it helps establish a trusted, encrypted HTTPS connection between your web server and website visitors. This secures your website, ensures secure data transmission, and helps you meet the security and compliance requirements of the relevant app marketplace or application ecosystem. For more information, see What is an SSL Certificate?.
Data masking
Hologres provides a data masking feature. It supports column-level masking and lets you set masking policies for specific users. After this feature is enabled, if a query involves sensitive information, the data is masked in the results. This improves the protection of sensitive and private data. Hologres supports multiple masking rules, such as IP address masking, email address masking, and hash masking. For configuration details, see Data masking.
System security
Account
You must use an Alibaba Cloud account to purchase and use Hologres. After you register an Alibaba Cloud account and complete identity verification, you can purchase the Hologres service. You can create an AccessKey to access the product.
Hologres supports Resource Access Management (RAM) authentication. RAM is a resource access control service provided by Alibaba Cloud. Using RAM, a root account can create RAM users. RAM users are subordinate to the root account. All resources belong to the root account. The root account can control access permissions to its instances and grant them to RAM users.
Authentication
You can create an AccessKey in the Alibaba Cloud Management Console.
An AccessKey consists of an AccessKey ID and an AccessKey secret. The AccessKey ID is public and identifies the user. The AccessKey secret is private and authenticates the user.
When a user sends a request to Hologres, a signature string must first be generated for the request in the format that Hologres specifies. Then, the AccessKey secret is used to encrypt the signature string to generate a request signature. When Hologres receives the request, it uses the AccessKey secret that corresponds to the AccessKey ID to generate a signature for the signature string. If this signature matches the request signature, the request is considered valid. Otherwise, Hologres rejects the request and returns an HTTP 403 error.
Authorization
There are two ways to access a Hologres instance: using an Alibaba Cloud account or a RAM user. An Alibaba Cloud account can have multiple RAM users for flexible authorization. Hologres supports access policies for Alibaba Cloud accounts and RAM users:
When you access an instance with an Alibaba Cloud account, Hologres checks whether the account is the owner of the instance. Only the owner of the instance has permission to access that instance.
When you access an instance with a RAM user, the access policy of the RAM user is triggered. Hologres checks whether the RAM user has been granted permission to access the instance by the corresponding Alibaba Cloud account.
Hologres supports the following three authorization mechanisms to control access for RAM users. For configuration details, see Hologres permission models.
Permission type
Scenario
Description
Standard PostgreSQL authorization model
Suitable for scenarios that require very strict permission control. For example, granting a specific user permission on a specific table. For example, allowing user zinan.tang to read data from the table table1.
The standard PostgreSQL authorization model offers fine-grained and flexible permission granting. You can grant a user permissions on a specific table. Use the
GRANT/REVOKEcommand to grant or revoke permissions on databases, schemas, tables, and views in an existing instance.Simple permission model (SPM)
Database-level permission control. Suitable for coarse-grained permission management scenarios.
The simple permission model is a pre-packaged permission model. It is database-centric, and each user group has corresponding permissions that cannot be modified. It meets the needs of most authorization scenarios, and the authorization operations are simple.
Schema-level permission model (SLPM)
Schema-level permission control. Suitable for scenarios that require finer permission granularity but also a simplified authorization process.
The schema-level permission model is a pre-packaged permission model. It is schema-centric, and each user group has corresponding permissions that cannot be modified. It satisfies the need for finer-grained control, and the authorization operations are simple.
RAM authentication
Hologres supports RAM authentication. RAM is a resource access control service from Alibaba Cloud that allows a root account to create and manage RAM users. The root account owns all resources and can grant RAM users access permissions to its Hologres instances.
You can also log on to Alibaba Cloud and use Hologres through role-based SSO. In this case, an Alibaba Cloud RAM role becomes a member of a Hologres instance. The user who assumes the RAM role has the same product usage permissions as a member who uses an Alibaba Cloud account. For configuration details, see RAM role authorization mode.
Auditing
ActionTrail
Hologres lets you query instance management event logs from the last 90 days through the console, OpenAPI, and developer tools of Alibaba Cloud ActionTrail. This allows for event monitoring and alerting, timely auditing, and issue analysis. For configuration details, see Event audit logs.
ActionTrail can collect records of operations that are performed on Alibaba Cloud services. These operations include those triggered by users in the console, performed by calling Alibaba Cloud APIs, or performed by Alibaba Cloud services that use service roles. Operation records are tracked and recorded by ActionTrail within 10 minutes.
You can view operation records from the last 90 days in the ActionTrail console or by calling APIs. You can determine who initiated an operation, what the operation was, which object was affected, when the operation occurred, and the source IP address. You can also determine whether the operation was from the API or the console, whether it succeeded or failed, and the reason for the failure. You can download these behavioral events or save them to Simple Log Service or OSS. Then, you can perform behavior analysis, security analysis, resource change tracking, and behavior compliance audits.
ActionTrail supports delivering operation records to storage products such as Alibaba Cloud Object Storage Service (OSS) or Simple Log Service. These storage products are highly available and can secure audit data using encryption and access control. When a delivery occurs, ActionTrail also sends you a notification.
You can create multiple trails to track different event types and regions separately and deliver them to different buckets. This helps you meet the requirement to back up different scopes of behavioral data for employees with different responsibilities.
Implementation principle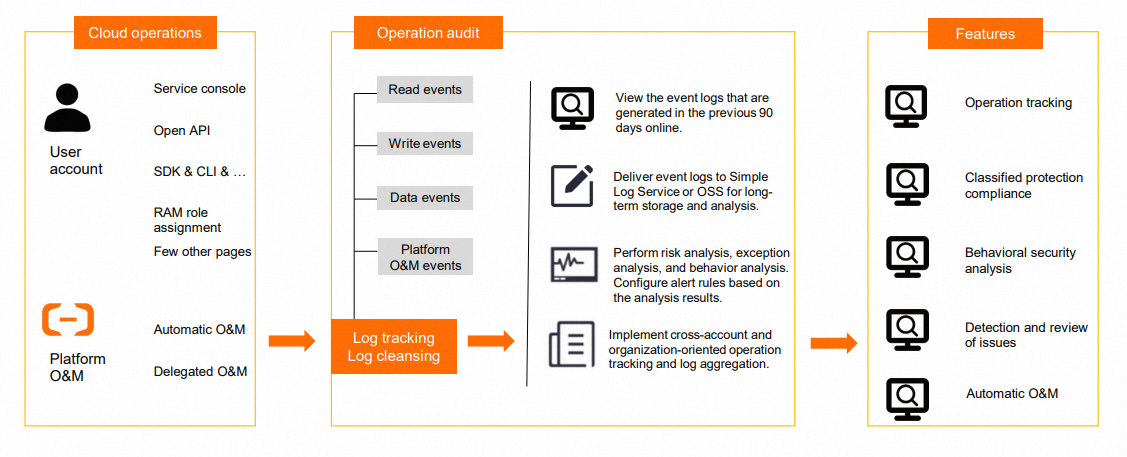
Hologres Query Log
Hologres provides query log information. The system records all DDL statements and all DML and DQL statements that take longer than 100 ms to execute. The logs are retained for 30 days. The logs record the specific operations of each user in detail. For configuration details, see View and analyze slow query logs.
Network security
Access isolation
As a one-stop real-time data warehouse engine that is independently developed by Alibaba, Hologres must meet security isolation standards. Hologres provides the following network support:
The classic network, VPC, and public network of each instance are isolated from each other. You can access an instance only through the corresponding endpoints and virtual IP addresses (VIPs) for each network.
Hologres instances support the configuration of a specific VPC ID to ensure that an instance can be accessed only from the corresponding VPC.
IP whitelist
Hologres provides multiple layers of access control for security, such as the authentication mechanism described in the previous section. Only users who have a valid and authorized AccessKey ID and AccessKey secret can pass authentication to access and compute data within the scope of their granted permissions.
An IP whitelist is an enhanced access control method that is built on top of this access authentication. When the whitelist feature is enabled, only devices on the whitelist can access the Hologres instance. If a user attempts to access the instance from a device that is not on the whitelist, authentication fails even if the user provides a valid AccessKey ID and AccessKey secret. For configuration details, see IP whitelist.