DSC audit alert rules scan your data assets for security threats — including abnormal operations, data leaks, vulnerability exploits, and SQL injections — and send alert notifications when risks are detected. Built-in rules for databases, OSS, and MaxCompute are enabled by default. Create custom rules for fine-grained monitoring across specific databases, tables, fields, sources, or sensitive data types.
Prerequisites
Before you begin, ensure that you have:
Enabled the data audit mode for the data assets you want to monitor. For more information, see Set and enable the data audit mode
Rule types
| Rule type | Description |
|---|---|
| Built-in rules | DSC provides built-in rules for OSS, MaxCompute, RDS, and PolarDB. These rules are enabled by default and apply automatically to supported asset types. |
| Custom rules | Create rules tailored to your environment by filtering on sensitive data type, data sensitivity, database, table, field, source, or database instance. Custom rules are enabled by default after creation. |
View built-in audit alert rules
Built-in rules are organized into three policy tabs: Database Policy, OSS Policy, and MaxCompute Policy.
Log on to the Data Security Center console.
In the left-side navigation pane, choose Data Auditing > Native Data Auditing.
On the Policy Management tab, click Database Policy, OSS Policy, or MaxCompute Policy.
In the Rule classification list, select a rule type to view all rules of that type.

In the rule list on the right, review the Rule Name, Rule Type, Risk Level, Status, and Hits columns.
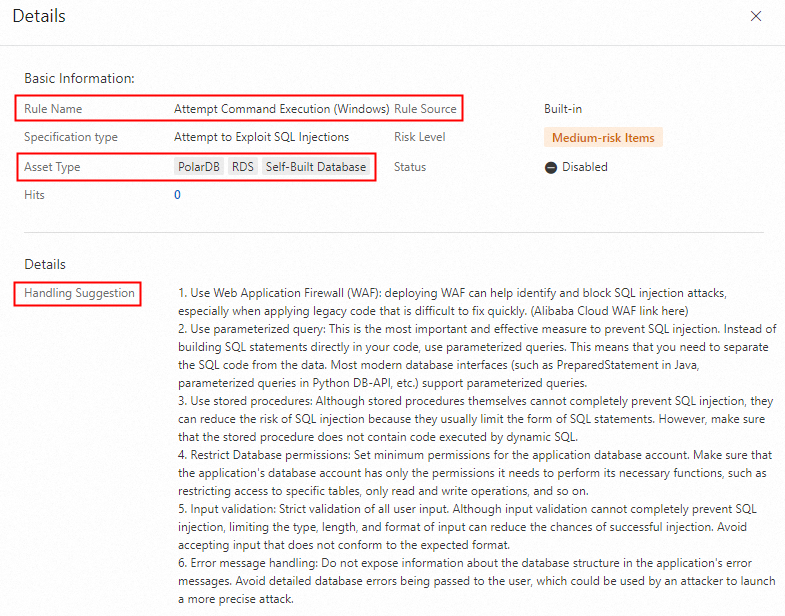
Click Details in the Actions column to view the supported Asset Type and rule configuration details.
Create a custom audit alert rule
If the built-in rules do not cover your monitoring needs, create a custom rule.
The Asset Type you select must be compatible with the Rule Type. If they are incompatible, the rule does not take effect. Check the built-in rules on the Database Policy, OSS Policy, and MaxCompute Policy tabs to confirm which asset types each rule type supports.
On the Policy Management tab, click Custom Policy, then click Add Rule.
In the Add Rule panel, configure the following parameters and click Submit.
| Parameter | Description |
|---|---|
| Basic Information | |
| Rule Name | A name for the rule. Use a descriptive name that identifies the rule's purpose. |
| Rule Type | The threat category the rule monitors. Valid values: Attempt to Exploit SQL Injections, Bypass Attempt by Using SQL Injections, Stored Procedure Abuse, Buffer Overflow, Error-based SQL Injection, Boolean-based SQL Injection, Time-based SQL Injection, Denial-of-service Vulnerability, Database Detection, Data Breach Attack, Covert Channel Attack, Risky Operation by Application Account, Risk Operation by O&M Engineer, Abnormal Statement, High Traffic Volume, Configuration Operation, Sensitive Data Audit, Union-based SQL Injection, and Other. |
| Risk Level | The severity of the alert. Valid values: High, Medium, and Low. |
| Asset Type | The type of asset the rule applies to. Must be compatible with the selected Rule Type (see Important note above). |
| Rule Description | (Optional) A description of the rule. |
| Sensitive Data Model | When Asset Type is set to RDS, PolarDB, or Self-Managed Database, configure the sensitive data identification template and model. |
| Asset | The specific assets the rule applies to, based on the selected asset type. |
| Client | The client conditions under which the rule takes effect. |
| Behavior | The operation types and status codes that trigger the rule. |
| Result | The result conditions under which the rule takes effect. Not supported when Asset Type is set to Redis. |
Enable or disable an audit alert rule
Toggle any built-in or custom rule on or off at any time. If you no longer need a rule, you can turn off Status for the rule. To re-use a rule, you can turn on Status for the rule.
On the Policy Management tab, click Database Policy, OSS Policy, MaxCompute Policy, or Custom Policy.
In the rule list, find the rule and toggle the switch in the Status column.

Configure notification settings
To receive alert notifications, configure your notification channels in System Settings > Alert Notification. For more information, see Configure email, phone call, and text message alert notifications.
What's next
After enabling audit alert rules, DSC generates alerts for matching operations. View and handle these alerts on the Audit Alerts page. For more information, see View and handle audit alerts.
To reduce false alerts, add trusted accounts and IP addresses to the whitelist. DSC skips alert generation for operations from whitelisted accounts or IP addresses. For more information, see Manage the whitelist.