Data Security Center (DSC) detects plaintext AccessKey pairs stored in Object Storage Service (OSS) buckets and flags abnormal access activity that uses those pairs. When a leak or suspicious access is detected, DSC triggers an alert so you can investigate and respond before a data breach occurs. An AccessKey pair consists of an AccessKey ID and an AccessKey secret.
This tutorial walks through a simulated end-to-end scenario: a plaintext AccessKey pair is found in an OSS bucket, and DSC generates an alert when the leaked pair is used to access a file. You'll configure detection policies, simulate the access event, and work through the remediation options.

The tutorial covers five steps:
Create an OSS bucket and upload files — Set up the test environment with a file containing AccessKey credentials and a sample data file.
Connect an OSS bucket to DSC — Authorize DSC to monitor the bucket.
Configure risk event levels and alert notifications — Enable AccessKey leak detection and set up email or SMS alerts.
Simulate abnormal access and view alert notifications — Use ossutil to access the bucket with the leaked credentials, then view the resulting alert.
View and handle risk events — Review the risk event details and remediate using Disable or Rotate.
Prerequisites
Before you begin, ensure that you have:
A Data Security Center instance purchased with Edition set to Value-added Plan, Data Detection and Response and Log Storage enabled, and sufficient Data Detection and Response - OSS Protection Capacity and Extended Log Storage Capacity purchased. For purchase instructions, see Purchase a Data Security Center instance.
DSC granted permissions to access other Alibaba Cloud resources. For setup instructions, see Grant Data Security Center the permissions to access other Alibaba Cloud resources.
OSS activated. For activation instructions, see Activate OSS.
A Resource Access Management (RAM) user under your account with its AccessKey ID and AccessKey secret available. For setup instructions, see Create a RAM user and View the AccessKey information of a RAM user.
Data Detection and Response is a value-added service. It consumes OSS protection capacity and log storage capacity.
Step 1: Create an OSS bucket and upload files
Create an OSS bucket
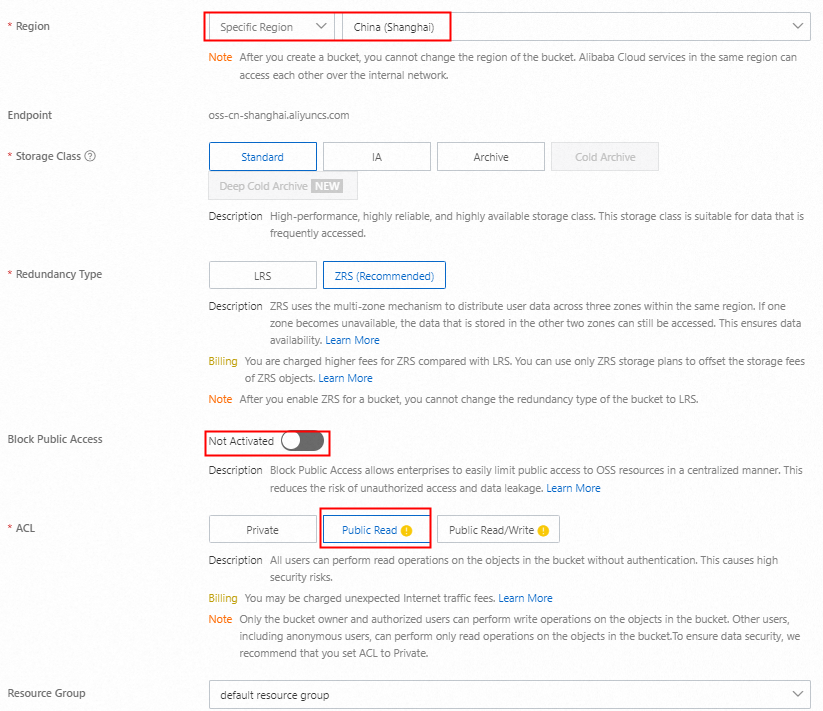
On the Buckets page of the OSS console, click Create Bucket.
In the Create Bucket panel, configure the required parameters and click Create. Use the default settings for parameters not listed.
Upload files to the bucket
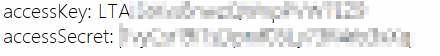
Create a file named
test.txt, enter the AccessKey ID and AccessKey secret of the prepared RAM user, and save the file.
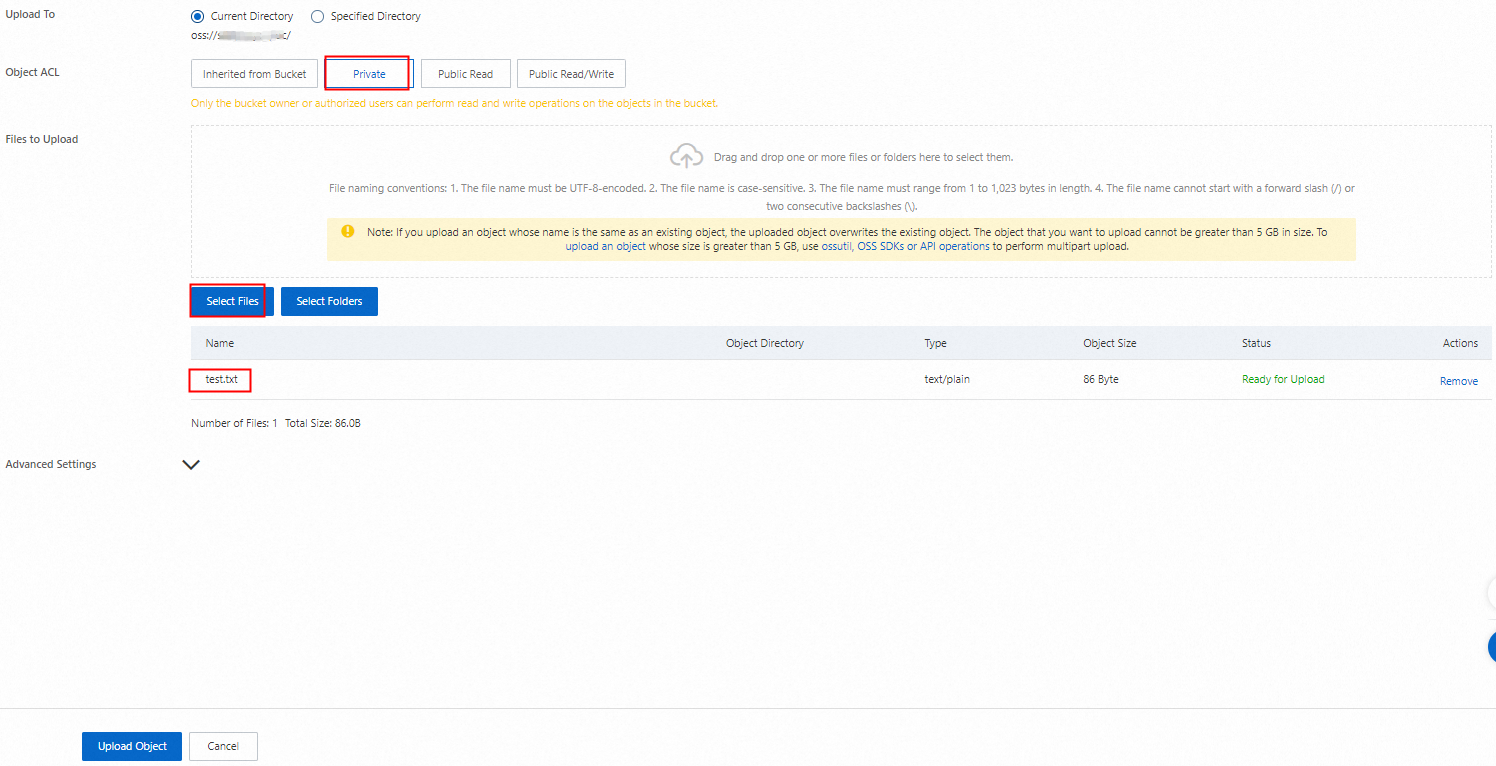
On the Buckets page of the OSS console, click the name of your bucket.
On the Objects tab, click Upload Object.
Set Object ACL to Private, click Select Files, select
test.txt, and then click Upload. Wait for the upload to complete.
On the Objects tab, click Create Directory, enter a Directory Name such as
exampledir, and click OK.Go to the
exampledirdirectory and click Upload Object.Click Select Files, select a sample file such as userdata.csv, and click Upload. Wait for the upload to complete.
Step 2: Connect an OSS bucket to DSC
Log on to the Data Security Center console.
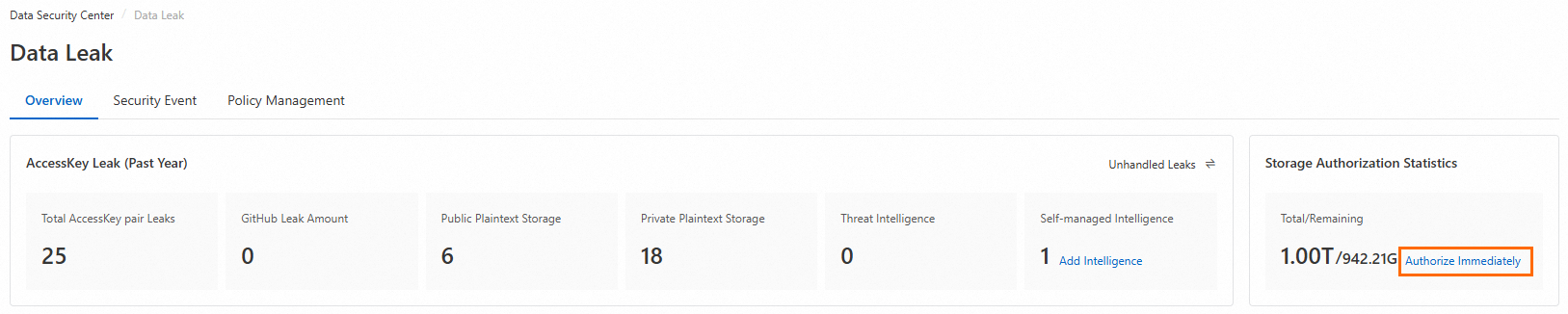
In the left navigation pane, choose Data Detection and Response > Data Leak.
On the Overview tab, in the Storage Authorization Statistics section in the upper-right corner, click Authorize.
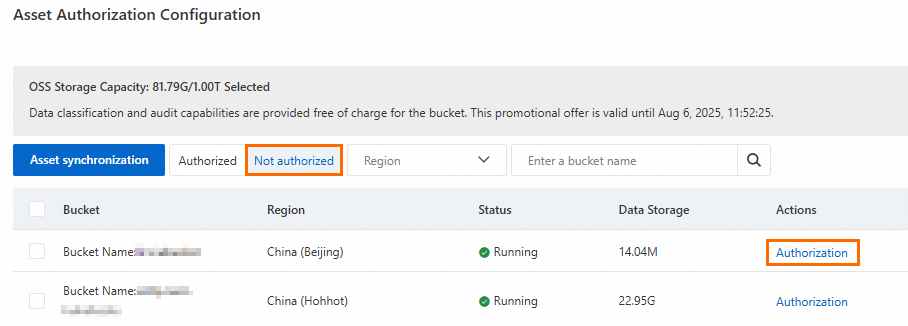
In the Asset Authorization Configuration panel, click Asset synchronization.
On the Not authorized tab, find your bucket in the list and click Authorization in the Actions column.
During the first month after you enable Data Detection and Response, DSC automatically creates and immediately runs a sensitive data identification scan using the Internet Industry Classification and Categorization Template.
Step 3: Configure risk event levels and alert notifications
Enable AccessKey pair leak detection
DSC must have the AccessKey Pair Leak event type enabled before it can generate alerts.
In the left navigation pane, choose Data Detection and Response > Data Leak.
On the Policy Management tab, set Risk Event Type to AccessKey Pair Leak, configure the Risk Event Level, enable Risk Event Status, and click Save.
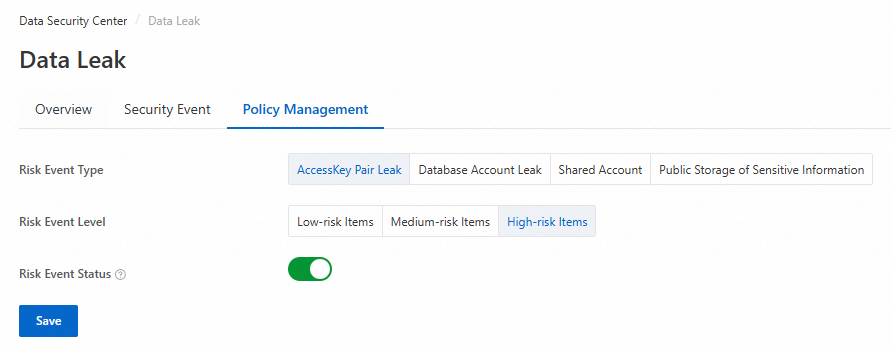
AccessKey Pair Leak events are enabled by default with a risk level of High-risk Items.
Disabling an event type stops new alerts from being generated. Existing events are not affected.
Changing the risk level updates the level on all existing events of that type.
Configure alert notifications
In the left navigation pane, choose System Settings > Alert Notification.
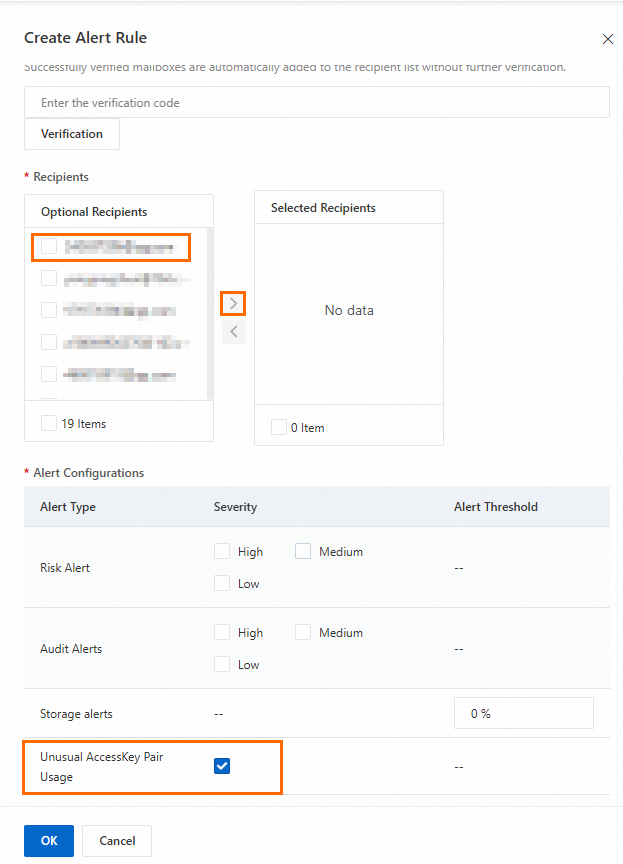
On the Alert Notification tab, click Create Alert Configuration.
In the Create Alert Rule panel, select Mailbox or Text Message as the alert method, configure the parameters, and click OK. For configuration details, see Configure email, text message, and phone call alert notifications.
Step 4: Simulate abnormal access and view alert notifications
After accessing the OSS bucket with the leaked AccessKey pair, the alert event and notification are available on the following day.
Access an OSS object using ossutil
This step uses ossutil in a Linux environment to simulate an abnormal access event. For installation details, see Install ossutil.
Install and configure ossutil.
Run the following command to download and install ossutil.
sudo -v ; curl https://gosspublic.alicdn.com/ossutil/install.sh | sudo bash- The installation requires a decompression tool such as unzip or 7z. Install one before running the command. - After installation, ossutil is placed in
/usr/bin/.Run the configuration command:
ossutil configPress Enter to use the default configuration file path and set the tool language to EN.EN
Set the Endpoint, AccessKey ID, STSToken, and AccessKey secret as prompted. Find the endpoint on your OSS bucket's Overview page under Access Port. Use the AccessKey ID and AccessKey secret of the RAM user you prepared.
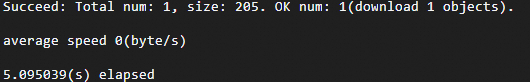
Run the following command to download the
userdata.csvobject from your bucket.ossutil cp oss://examplebucket/exampledir/userdata.csv /optIf the command succeeds, the output looks similar to:
View the email alert
The alert contact receives an email notification similar to:
Step 5: View and handle risk events
In the left navigation pane, choose Data Detection and Response > Data Leak.
In the Risk Type section, click AccessKey Pair Leak.
Find the target risk event and click Details in the Actions column.
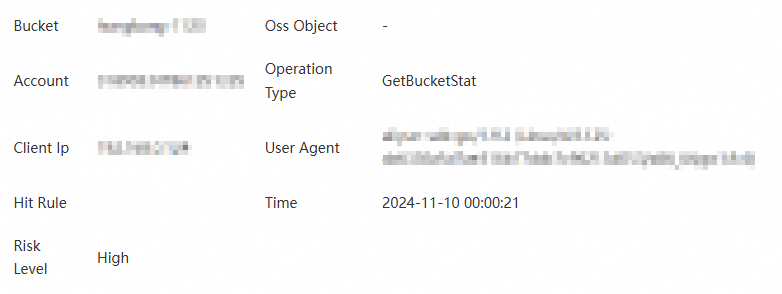
On the Details page, review the event information and take action.
AccessKey information
The details page shows the following fields: AccessKey ID, Account of AccessKey Pair, AccessKey Pair Status, First Detection Time, Latest Detection Time, and Intelligence Source.

To remediate the leaked AccessKey pair, click Handle. In the Manage AccessKey Pair panel, choose one of the following actions based on your situation:
| Situation | Recommended action | What happens |
|---|---|---|
| The key is actively used and you want to stop it immediately | Disable | Redirects to the RAM console to disable the AccessKey pair for the primary account or its RAM users. See Disable an AccessKey pair of a RAM user. |
| Key Management Service (KMS) is integrated and you want to rotate credentials | Rotate > KMS Integrated > Confirm | KMS deletes the existing AccessKey pair and creates a new one. |
| KMS is not yet integrated | Rotate > KMS Not Integrated | Redirects to the KMS console to host your AccessKey credentials in KMS. If KMS is not activated, first purchase and enable a KMS instance. |
Key rotation cannot be undone. Proceed with caution.
AccessKey leak details
DSC aggregates leak signals from multiple intelligence sources. Review each source and take appropriate action.
GitHub Leak Amount — Detects AccessKey credentials in public source code on GitHub.
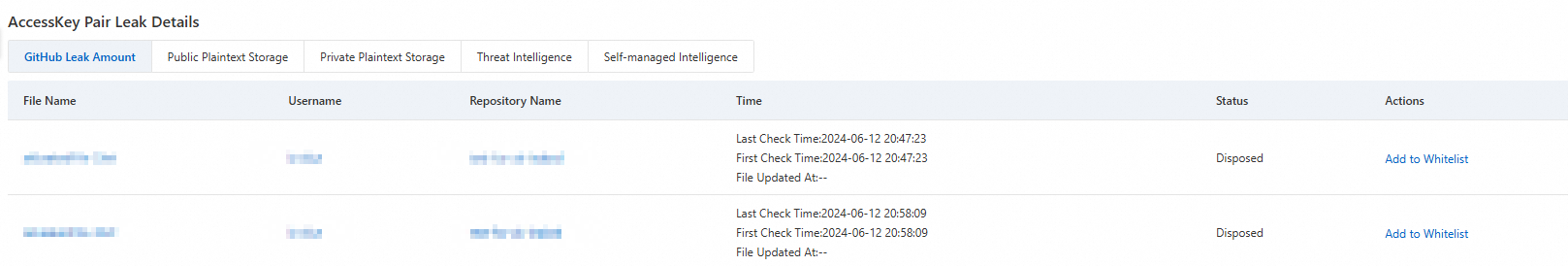
Click File Name, Username, or Repository Name to open the corresponding page on GitHub.
Click Add to Whitelist in the Actions column to exclude the file from future alerts.
Public Plaintext Storage / Private Plaintext Storage — Detects AccessKey credentials stored in plaintext in public or private files in authorized OSS buckets.
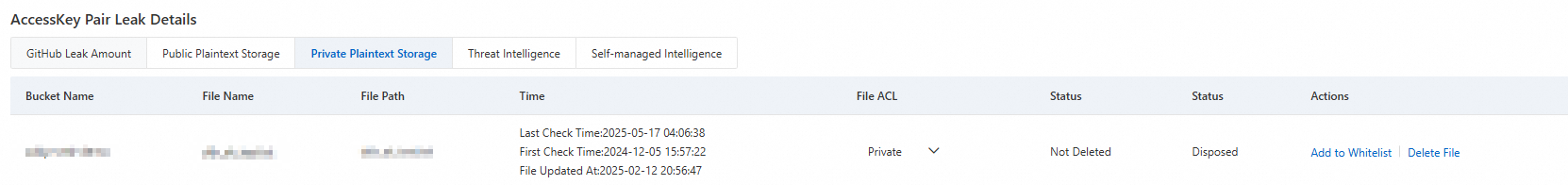
Modify ACL: Click the dropdown in the File ACL column to change the file's ACL.
Delete: Click Delete File in the Actions column to remove the file from the bucket.
Add to allowlist: Click Add to Whitelist in the Actions column to exclude the file from future alerts.
Threat Intelligence / Self-managed Intelligence — For AccessKey leaks detected via threat intelligence or custom intelligence feeds, whitelist the relevant threat sources or intelligence entry users.
After a file is deleted, the status updates to Deleted on the following day (T+1) and then to Disposed.
After a file is added to the allowlist, the status updates to Added to Whitelist on T+1.
AccessKey bucket access details
For AccessKey pairs that have been used to access buckets, DSC shows a list of accessed buckets and files. Start with buckets that have a higher sensitivity level, as those carry greater data breach risk.
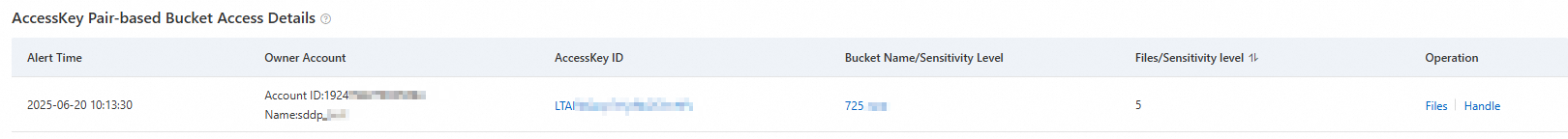
Threat Tracing: Click a target AccessKey ID or Bucket Name/Sensitivity Level to view a visualization of the access path.
View Files: Click Files in the Actions column to see which objects were accessed. Modify file ACLs directly from this view.
Handle: Click Handle in the Actions column to restrict bucket access.
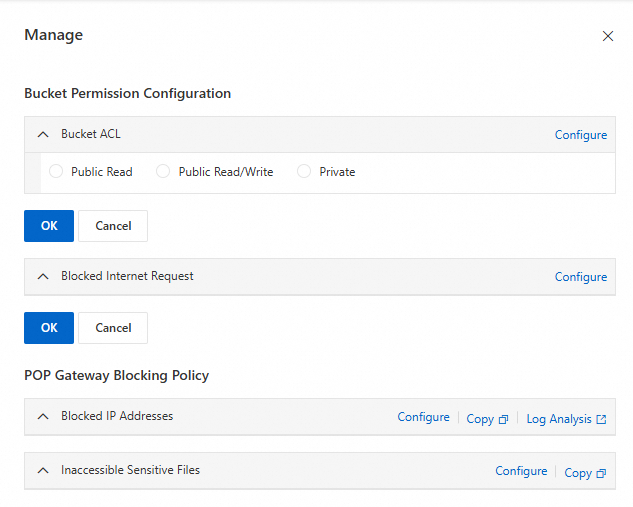
Bucket Permission Configuration: Click Configure to set up Bucket ACL and block public network requests, then click OK.
POP Gateway Blocking Policy: Click Configure to go to the RAM console and create policies that restrict IP access and sensitive file access. For policy creation details, see Create a custom policy.
What's next
DSC also detects other data leak types in OSS buckets, including Database Account Leak, Shared Account, and Public Storage of Sensitive Information. For an overview of all risk types and how to set up custom intelligence feeds, see Risk overview and custom intelligence.