DataWorks provides a data access control feature to manage permissions for MaxCompute tables, resources, and functions. This topic describes how to request, approve, and audit permissions for MaxCompute data in a standard mode workspace.
Background
In a standard mode workspace, the development and production environments have different default permission behaviors:
-
Development environment: DataWorks automatically adds workspace members to the MaxCompute project role, granting read permissions on all data.
-
Production environment: DataWorks does not add workspace members to the MaxCompute project role by default. Members must explicitly request access.
To access tables, resources, or functions in the production environment — whether from the same workspace or another workspace — submit a permission request through Security Center. Permissions take effect only after an approver grants the request.
For more information about how workspace modes affect engine access, see MaxCompute engine resource access and permissions in different workspace modes.
How it works
The Data Access Control feature supports three roles:
| Role | Responsibility |
|---|---|
| Requester | Submits permission requests for tables, resources, or functions via the Permission Application tab |
| Approver | Reviews and approves or denies requests on the Permission Approval tab; can also modify request content and expiration time |
| Administrator | Audits active permissions and revokes access on the Permission Audit tab; must be a workspace administrator or Alibaba Cloud account owner |
The following diagram shows the end-to-end permission request and approval flow:

Use cases
| Scenario | Description |
|---|---|
| Access production data from the same workspace | A RAM user in the development environment who has not been granted access to the production compute engine cannot operate on production tables in the Data Development interface by default. Submit a request in Security Center. After approval, the user can perform the relevant operations on production tables. |
| Access data across workspaces | A RAM user who is not a member of a workspace cannot access development or production tables across projects from the Data Development interface by default. Submit a request in Security Center. After approval, the user can perform the required cross-project operations. |
Security Center provides a default approval flow for all permission requests. To customize the flow, configure it in Approval Center. For field-level requests, DataWorks determines the required approval flow based on the requested fields. Custom approval flows and permission audit management are not supported for resource and function permission requests.
Prerequisites
Before you begin, ensure that you have:
-
Bound a MaxCompute computing resource to the workspace
-
Reviewed the details of MaxCompute data permission control
-
Understood the differences between basic mode and standard mode
Request permissions
Who performs this: Requester
Submit a permission request from the Permission Application tab in Data Access Control.
-
Log on to the DataWorks console. Switch to the target region. In the left navigation pane, choose Data Governance > Security Center, then click Go to Security Center.
-
In the left navigation pane, choose Data Platform Security > Data Access Control.
-
Click the Permission Application tab.
-
In the Application Content section, configure the request target.
Request permissions on tables
After selecting the table, choose Table-level Permissions or Column-level Permissions.
Parameter Description Data Source Type Select MaxCompute. Application Type TableWorkspace Select the workspace where the table is located. MaxCompute Project The MaxCompute project bound to the selected workspace. Schema The schema where the table is located. Tables to Be Added — table-level Available permissions: Select,Update,Download,Describe,Alter,DropTables to Be Added — column-level Available permissions: Select,Update,DownloadNoteIf
labelsecurityis not enabled for the MaxCompute project and you have been granted table-levelSelectandUpdatepermissions, new columns added to the table automatically inherit those permissions. Iflabelsecurityis enabled, new fields do not inherit table-level permissions — request field permissions explicitly.Request permissions on resources
Parameter Description Data Source Type Select MaxCompute. Application Type ResourceWorkspace Select the workspace where the resource is located. MaxCompute Project The MaxCompute project bound to the selected workspace. Resource Name The resource for which you want to request permissions. Request permissions on functions
Parameter Description Data Source Type Select MaxCompute. Application Type FunctionWorkspace Select the workspace where the function is located. MaxCompute Project The MaxCompute project bound to the selected workspace. Function Name The function for which you want to request permissions. -
In the Application Information section, configure the requester and validity details.
Parameter Description User The account to grant permissions to: Current login account, Account Used for Scheduling (the RAM user set as the scheduling access identity), or Apply on Behalf of Others (requires a Username). Application duration The validity period for the permissions. After the period ends, permissions are automatically revoked. To use this option, enable policy authorization for the MaxCompute project. See Details of MaxCompute data permission control and Policy-based access control. Reason for application A brief description of why access is needed, to help the approver evaluate the request. -
Click Apply for permission to submit the request.
After submitting, go to the Permission Application Records tab to track the status of the request.
Approve permissions
Who performs this: Approver (workspace administrator or table owner)
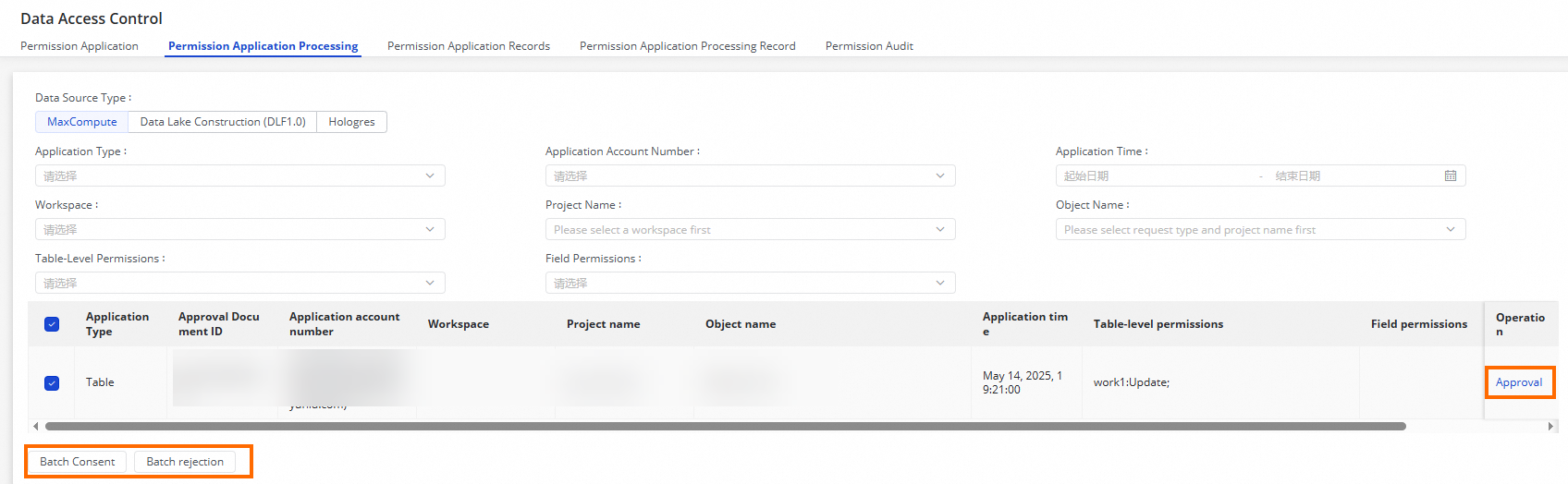
After a requester submits a permission request, process it on the Permission Approval tab.
-
On the Permission Application Processing page, filter requests by Application account number, Application time, Workspace, Project name, or Object name.
If a request covers multiple tables with different owners, the system splits it into separate sub-requests based on table ownership.
-
Click Approval in the Operation column for a request. In the dialog box: To process multiple requests at once, select them on the Permission Application Processing page, then click Batch Approve or Batch Deny and enter your Comments.
-
Review the Request Details and Approval Record tabs.
-
Enter Comments, then click Approve or Deny.
-
(Optional) Modify the Application Content or Expiration Time before approving.
Unprocessed Steps shows all approvers with permission to approve the request. Processed Steps shows only the approver who has already acted.
-
View permission request records
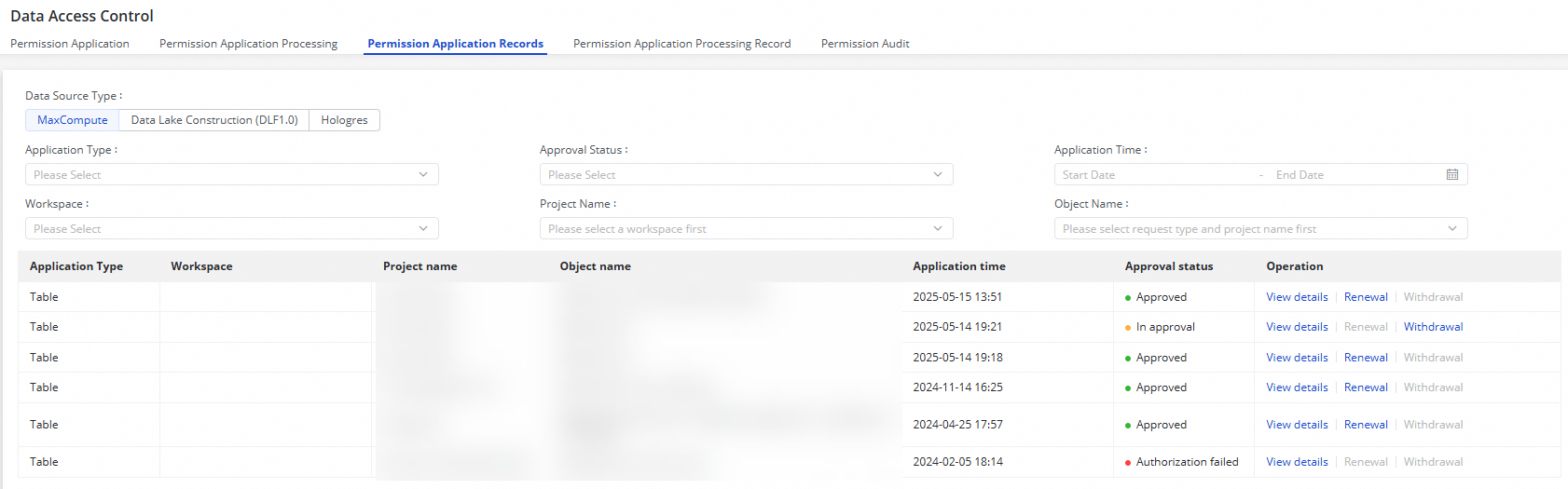
After submitting a request, track it on the Permission Application Records page. Filter records by Approval status, Application Time, or Workspace.
Click View details in the Operation column to see the full request history. For requests with an Approval status of In approval, the approval process can still be continued from this page. After a request is approved, you can view the approval result on this page and confirm that the permissions are effective.
View permission approval records
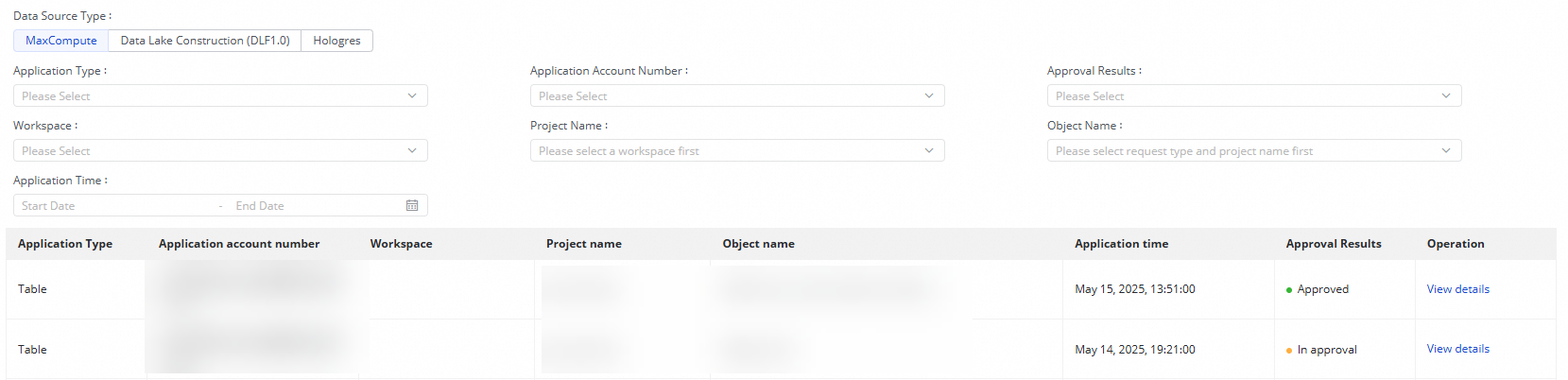
Who performs this: Approver
On the Permission Application Processing Records page, view the approval records for the current Alibaba Cloud account. Filter by Application account number, Approval Results, or Workspace.
Click View details in the Operation column to see the details of any processed request.
Permission audit
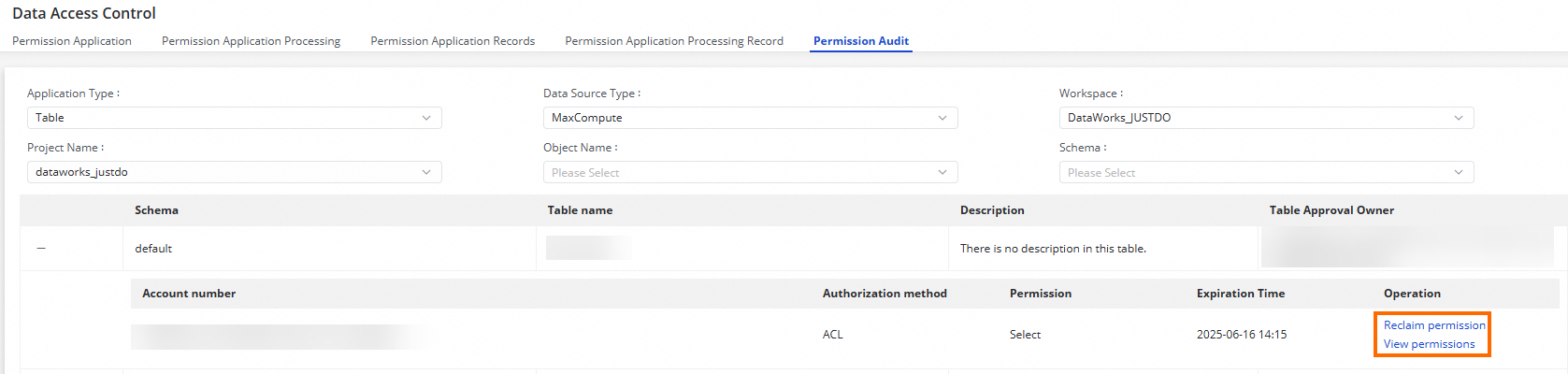
Who performs this: Workspace administrator or Alibaba Cloud account owner
On the Permission Audit tab, view and manage all active permissions granted to workspace members. Use the filters to locate a specific resource, then:
-
Click Revoke permissions or View permissions in the Actions column.
Related topics
-
Security Center — Configure and manage security policies for your workspace
-
Approval Center — Customize approval flows for permission requests
-
Details of MaxCompute data permission control — Understand the underlying permission control model