DataWorks uses a two-layer permission system to control RAM user access to MaxCompute data: workspace roles automatically grant development environment access, while production environment access always requires an explicit approval request through the Security Center.
The permission controls described in this topic apply to RAM users. An Alibaba Cloud account has full permissions on all cloud resources it owns.
How it works
DataWorks uses role-based access control (RBAC) to map workspace roles to MaxCompute compute engine roles. When a RAM user is added to a workspace and assigned a role, DataWorks automatically grants the corresponding MaxCompute role for the development project.
The production project works differently — no workspace role, predefined or custom, grants production access by default. RAM users must request production permissions separately through the Security Center. This design keeps production data isolated from the development workflow, giving administrators full control over who can access production tables and under what conditions.
Workspace mode constraints
Workspace mode | Default permissions | Production access |
Standard mode | No permissions on the production project | Must submit a request in the Security Center. See MaxCompute data access control. |
Basic mode | Full permissions on the project by default | Data permission control cannot be enforced. |
Permissions by environment
Development environment
When a workspace member is assigned a predefined workspace role, DataWorks automatically maps that role to the corresponding MaxCompute engine role. The member immediately gains the permissions of that engine role on the development project.
Only RAM users with the Developer or Admin workspace role can create nodes in Data Studio to run commands that operate on tables, resources, and functions.
Production environment
Neither predefined nor custom workspace roles grant MaxCompute permissions for the production project. To access production tables — for example, to query rows from Data Studio — RAM users must submit a request in the Security Center. Access is granted only after the request is approved.
For details on requesting production access, see MaxCompute data access control.
How RAM users get compute engine permissions
Development project (automatic)
Development project permissions are granted automatically when a role is assigned:
Predefined role: When a workspace administrator assigns a predefined role (for example, Developer), DataWorks automatically grants the mapped MaxCompute engine role. The Developer role maps to
Role_Project_Dev, which provides access to the development project and its tables. In DataWorks, the Developer role allows the user to develop and submit code but not publish directly to the production environment — publishing requires O&M permissions (Project Owner, Admin, or O&M role). For a full mapping reference, see Mappings between predefined workspace-level roles and MaxCompute engine permissions.Custom role: When a workspace administrator assigns a custom role, permissions depend on whether the role is mapped to a MaxCompute engine role:
Not mapped: The RAM user has no operation permissions on MaxCompute and cannot run queries.
Mapped: The RAM user gets the permissions of the mapped MaxCompute engine role.
For instructions on creating a custom DataWorks role, see Workspace-level module permission control. For instructions on adding workspace members and assigning roles, see Workspace-level module permission control.
When a RAM user is granted the predefined Admin role, the user has more DataWorks feature permissions but still cannot directly access production tables.
Production project (manual request)
Production access is never granted automatically. The table below covers the two most common scenarios.
Scenario | What happens | How to get access |
Accessing a production table from the same workspace | RAM users cannot perform operations on production tables from Data Studio by default. | Submit a request in the Security Center. After approval, operations are available from Data Studio. |
Accessing tables in another workspace (cross-project) | RAM users who are not members of the target workspace cannot access its development or production tables from Data Studio. | Submit a request in the Security Center. After approval, operations are available from Data Studio. |
A RAM user added as a workspace member has no production environment permissions unless explicitly configured as the scheduling compute engine access identity (production project MaxCompute access identity). For details on access identities, see Configure a workspace.
Production data permission control
When a RAM user needs production data access, an approval process is required.
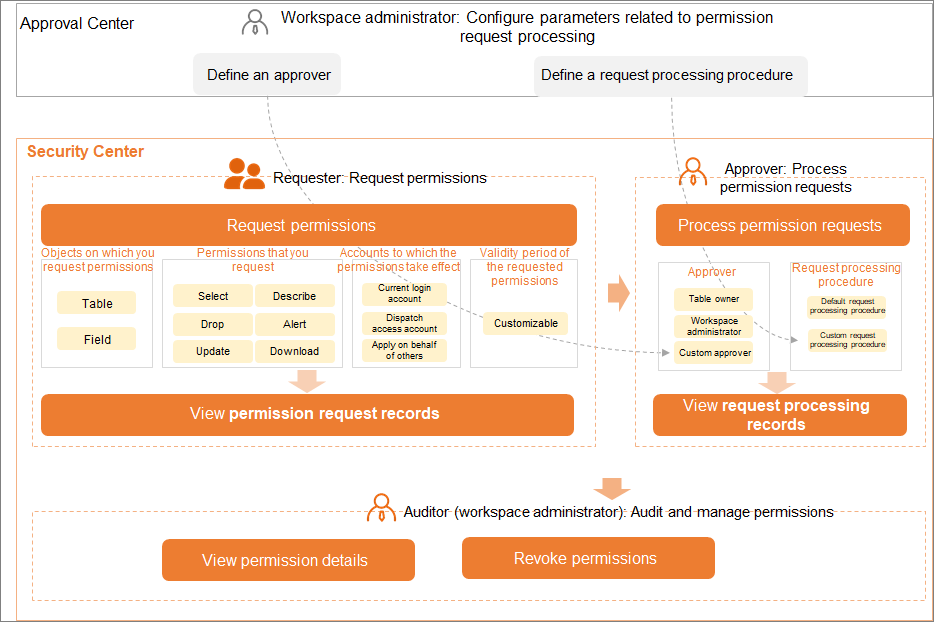
The Security Center has a built-in approval flow for permissions on production tables. The Approval Center also supports custom approval flows if your organization needs a different process.
View MaxCompute engine permissions
In a MaxCompute SQL node, run the following statements to check permission assignments:
show grants— Views your own access permissions.show grants for <username>— Views the access permissions of a specified user. Only workspace administrators can run this command.
For a full reference on querying permission information, see Query permission information using MaxCompute SQL.
FAQ
For common permission-related errors and how to resolve them, see FAQ about permission management.
What's next
MaxCompute supports cross-project resource access, which means developers can access production resources directly from Data Studio under the right permissions. To learn how workspace members can access resources across projects, see Resource access and permissions for MaxCompute in workspaces of different modes.