Access control policies let you define what traffic Cloud Firewall allows, monitors, or blocks. Without a policy, Cloud Firewall allows all traffic by default. Configure policies to protect your assets from unauthorized access and enforce traffic isolation across your Internet firewall, NAT firewalls, virtual private cloud (VPC) firewalls, and internal firewalls.
This topic covers access control policies for the Internet firewall, NAT firewalls, and VPC firewalls. For internal firewalls between ECS instances, see Create an access control policy for an internal firewall.
For more information about how to configure an access control policy for an internal firewall, see Configure access control policies for the ECS Firewall.
How it works
Each access control policy defines a traffic pattern using five items — source, destination, protocol type, port, and application — and assigns one of three actions: Allow, Monitor, or Deny.
When traffic arrives, Cloud Firewall evaluates policies in priority order:
Match against the highest-priority policy. A lower priority number means higher priority. If the traffic matches, Cloud Firewall applies the specified action and stops evaluating further policies.
Continue to the next policy if no match. Cloud Firewall moves down the priority list and repeats the match check.
Allow traffic if no policy matches. After all configured policies are evaluated without a match, traffic is allowed by default.
After you create, modify, or delete a policy, Cloud Firewall takes approximately 3 minutes to send the update to the engine. Assign higher priorities to frequently matched and more specific policies to maximize their effectiveness.
The following diagram illustrates the matching process:

Policy items
Each policy is built from five items. The supported types for source and destination vary by firewall type and traffic direction.
Source
The source is the initiator of the network connection.
| Firewall type | Supported source types |
|---|---|
| Internet firewall, NAT firewalls, VPC firewalls | IP address, IP address book |
| Internal firewalls | IP address, IP address book, region |
Destination
The destination is the receiver of the network connection.
| Firewall type and direction | Supported destination types |
|---|---|
| Outbound — Internet firewall, NAT firewalls | IP address, IP address book, domain name, region |
| VPC firewalls | IP address, IP address book, domain name |
| Inbound — Internet firewall | IP address, IP address book |
Protocol type
Specifies the transport layer protocol: TCP, UDP, ICMP, or ANY. Select ANY to match all protocol types.
Port
Specifies the destination port or port range (port or address book format).
If you select ICMP as the protocol type, the port field is not applicable.
To match ICMP traffic when the protocol is set to ANY, specify a port range that includes 0, for example,
0/80.
Application
Specifies the application layer protocol. Supported values: HTTP, HTTPS, SMTP, SMTPS, SSL, FTP, IMAPS, POP3, and ANY. Select ANY to match all application types.
Cloud Firewall identifies the application of SSL or TLS traffic based on the port:
| Port | Identified as |
|---|---|
| 443 | HTTPS |
| 465 | SMTPS |
| 993 | IMAPS |
| 995 | POPS |
| Other ports | SSL |
Policy actions
Each policy specifies one of three actions:
| Action | Effect |
|---|---|
| Allow | Traffic matching the policy is permitted. |
| Deny | Traffic matching the policy is blocked. |
| Monitor | Traffic matching the policy is permitted, and the match is logged. Use this action to observe traffic behavior before committing to Allow or Deny. |
View matched traffic on the Traffic Logs page. For more information, see Log audit.
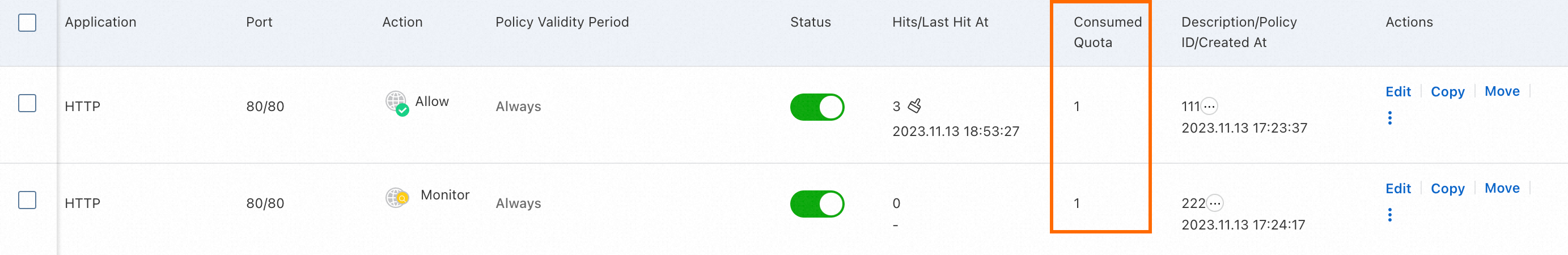
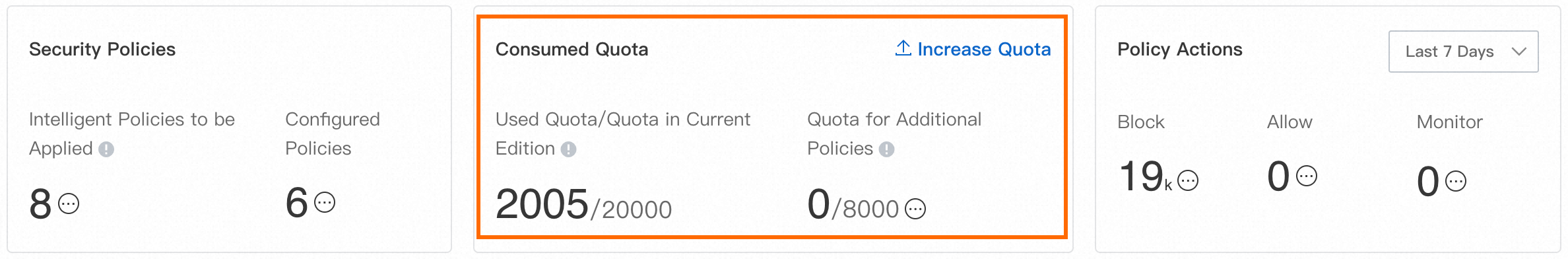
Quota consumed by access control policies
Billing
Subscription
Premium Edition, Enterprise Edition, and Ultimate Edition include a base quota for access control policies. Purchase additional quota if the included amount does not meet your needs. The additional quota applies to the Internet firewall, NAT firewalls, and VPC firewalls. For details, see Subscription.
Pay-as-you-go
Pay-as-you-go instances have the following fixed policy limits, which cannot be increased:
| Firewall type | Maximum policies |
|---|---|
| Internet firewall | 2,000 |
| NAT firewalls | 2,000 |
| VPC firewalls | 10,000 |
For details, see Pay-as-you-go.
What's next
Manage traffic between Internet-facing assets and the Internet: Create access control policies for the Internet firewall
Manage traffic from internal assets to the Internet: Create an access control policy for a NAT firewall
Manage traffic between VPCs and between VPCs and data centers: Create an access control policy for a VPC firewall
Manage traffic between ECS instances: Create an access control policy for an internal firewall between ECS instances
Practical configuration guidance and use cases: Configure access control policies
Cloud Firewall deployed with Bastionhost: Configure access control policies in scenarios in which Cloud Firewall is deployed together with Bastionhost