A NAT firewall controls outbound traffic from resources in a virtual private cloud (VPC) — such as Elastic Compute Service (ECS) instances and elastic container instances — to the Internet over a NAT gateway. Without access control policies, all outbound traffic passes through unrestricted, leaving your workloads exposed to risks like unauthorized access, data leakage, and traffic attacks.
By creating access control policies, you allow only the traffic your workloads require. Each policy matches traffic by source address, destination address, protocol, port, and application, then applies an Allow, Deny, or Monitor action. The NAT firewall enforces these policies on all outbound traffic from VPC resources to the NAT gateway, including traffic from resources in the same VPC and across VPCs.
After an access control policy is created, the access control engine mode of the NAT firewall defaults to Loose Mode. In this mode, traffic whose application type or domain name is identified as Unknown is automatically allowed, so your existing workloads are not disrupted. If your security posture requires denying Unknown traffic, switch to Strict Mode after you create your policies. See Configure the ACL engine mode for instructions.
Prerequisites
Before you begin, ensure that you have:
A NAT firewall that is created and enabled. For more information, see NAT firewalls.
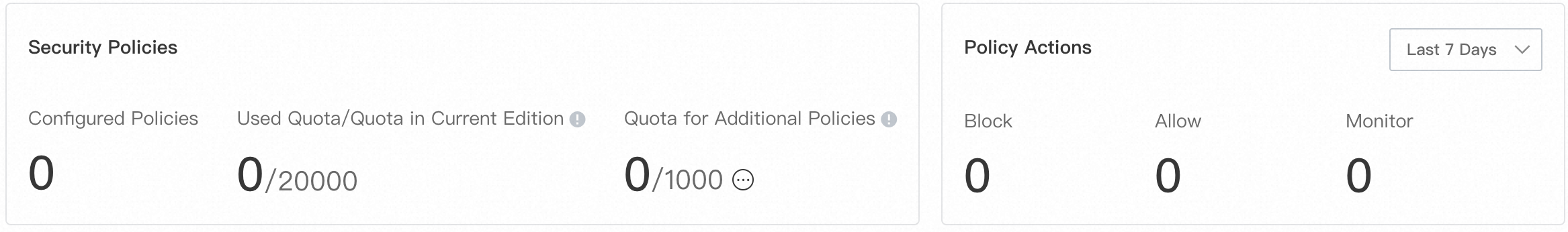
Sufficient quota for access control policies. Check your current quota on the Prevention Configuration > Access Control > NAT Border page. For details on how quota is calculated, see Overview of access control policies. If your quota is insufficient, click Increase Quota to increase the value of Quota for Additional Policy. For more information, see Purchase Cloud Firewall.
(Optional) An address book, if you want to specify multiple IP addresses or port ranges as a reusable source or destination group. For more information, see Manage address books.
Create an access control policy
Log on to the Cloud Firewall console.
In the left-side navigation pane, choose Prevention Configuration > Access Control > NAT Border.
On the NAT Border page, find the NAT gateway for which you want to create a policy, then click Create Policy. NAT gateways within the current Alibaba Cloud account are automatically synchronized to Cloud Firewall.

In the Create Policy - NAT Border panel, configure the parameters described below, then click OK.
Parameter dependencies
The following constraints apply across parameters. Review them before configuring to avoid validation errors:
| If you set... | Then... |
|---|---|
| Source Type = IP | Enter CIDR blocks for Source. Up to 2,000 CIDR blocks. |
| Source Type = Address Book | Select a pre-configured IP address book. |
| Destination Type = Domain Name | You must also select a Domain Name Identification Mode. |
| Domain Name Identification Mode = FQDN-based Dynamic Resolution | Application is limited to HTTP, HTTPS, SMTP, SMTPS, or SSL. |
| Domain Name Identification Mode = DNS-based Dynamic Resolution | All applications are available. Wildcard domain names are not supported. |
| Domain Name Identification Mode = FQDN and DNS-based Dynamic Resolution | Application is limited to HTTP, HTTPS, SMTP, SMTPS, or SSL. Takes effect only in Strict Mode. |
Source parameters
| Parameter | Description |
|---|---|
| Source Type | Select IP to enter CIDR blocks directly, or Address Book to use a pre-configured IP address book. |
| Source | Enter the source address based on the selected Source Type. If you set Source Type to IP, enter one or more CIDR blocks (for example, 192.168.0.0/16), separated by commas. Up to 2,000 CIDR blocks are supported. When multiple CIDR blocks are entered, Cloud Firewall automatically creates an address book containing them and prompts you to name it when you save the policy. |
Destination parameters
| Parameter | Description |
|---|---|
| Destination Type | Select the type of destination: IP, Address Book, Domain Name, or Region. |
| Destination | Enter or select the destination based on the selected Destination Type: <br>- IP: Enter one or more CIDR blocks, separated by commas. Up to 2,000 CIDR blocks are supported. Multiple entries are automatically grouped into an address book. <br>- Address Book: Select a pre-configured IP address book. <br>- Domain Name: Select a Domain Name Identification Mode (see the table below). <br>- Region: Select one or more locations in or outside China. |
Domain Name Identification Mode (applies when Destination Type is Domain Name):
| Mode | Use when | Limitation |
|---|---|---|
| FQDN-based Dynamic Resolution (Extract Host and SNI Fields) | Managing HTTP, HTTPS, SMTP, SMTPS, or SSL traffic | — |
| DNS-based Dynamic Resolution | Managing traffic other than HTTP, HTTPS, SMTP, SMTPS, or SSL | Does not support wildcard domain names |
| FQDN and DNS-based Dynamic Resolution (Support for HTTP, HTTPS, SSL, SMTP, and STMPS) | Managing HTTP, HTTPS, SMTP, SMTPS, or SSL traffic when specific or all traffic lacks the HOST or SNI field | Takes effect only when the ACL engine mode is set to Strict Mode |
Traffic matching parameters
| Parameter | Description |
|---|---|
| Protocol Type | Select the transport layer protocol: TCP, UDP, ICMP, or ANY. Select ANY if the protocol is unknown. |
| Port Type | Select Port to enter port ranges directly, or Address Book to use a pre-configured port address book. |
| Port | Enter port ranges in port/port format (for example, 22/22 or 80/88), separated by commas. Up to 2,000 port ranges are supported. Multiple entries are automatically grouped into a port address book. |
| Application | Select the application type of the traffic. Available options depend on the Domain Name Identification Mode: <br>- DNS-based Dynamic Resolution: All applications are available. <br>- FQDN-based Dynamic Resolution: Only HTTP, HTTPS, SMTP, SMTPS, or SSL. <br>- FQDN and DNS-based Dynamic Resolution: HTTP, HTTPS, SMTP, SMTPS, or SSL. |
Policy behavior parameters
| Parameter | Description |
|---|---|
| Action | The action applied to matching traffic: <br>- Allow: Traffic passes through. <br>- Deny: Traffic is blocked. No notifications are sent. <br>- Monitor: Traffic is recorded and allowed. Use this action to observe traffic patterns before deciding to allow or deny. |
| Priority | The priority of this policy relative to others. Default: Lowest. Valid values: Highest (the access control policy has the highest priority) or Lowest (the access control policy has the lowest priority). |
| Policy Validity Period | The time range during which this policy is active. The policy only matches traffic within this period. |
| Description | A description that helps identify the policy. |
| Status | Whether the policy is active when created. If turned off, the policy is saved but not enforced until you enable it in the policy list. |
Configure the ACL engine mode
After you create access control policies, configure the engine mode to determine how Unknown traffic is handled.
On the Prevention Configuration > Access Control > NAT Border page, click ACL Engine Management in the upper-right corner of the policy list.
In the ACL Engine Management - NAT Firewall panel, find the NAT gateway whose engine mode you want to change, then click Modify in the Engine Mode column.
In the Change Engine Mode dialog box, select an engine mode and click OK.
Mode Behavior Loose Mode Traffic identified as Unknown is automatically allowed. Use this mode to avoid disrupting workloads during initial policy setup. Strict Mode Traffic identified as Unknown is matched against all configured policies. If a Deny policy applies, the traffic is blocked. Use this mode for stricter security enforcement.
Manage existing policies
After a policy is created, use the following actions in the Actions column of the policy list:
Modify: Edit the policy configuration.
Copy: Duplicate the policy as a starting point for a new one.
Move: Change the policy's priority. Policies with lower priority are shifted down accordingly.
Delete: Remove the policy. After deletion, Cloud Firewall no longer manages the traffic this policy previously covered. Proceed with caution.
After you delete a policy, Cloud Firewall no longer manages traffic on which the policy is originally in effect. Proceed with caution.
Monitor and tune policies
After your services have run for a period of time, review the Hits and Last Hit At columns in the policy list to see how often each policy has matched traffic.
Click the number in the Hits column to go to the Log Audit page and view detailed traffic logs. For more information, see Log audit.
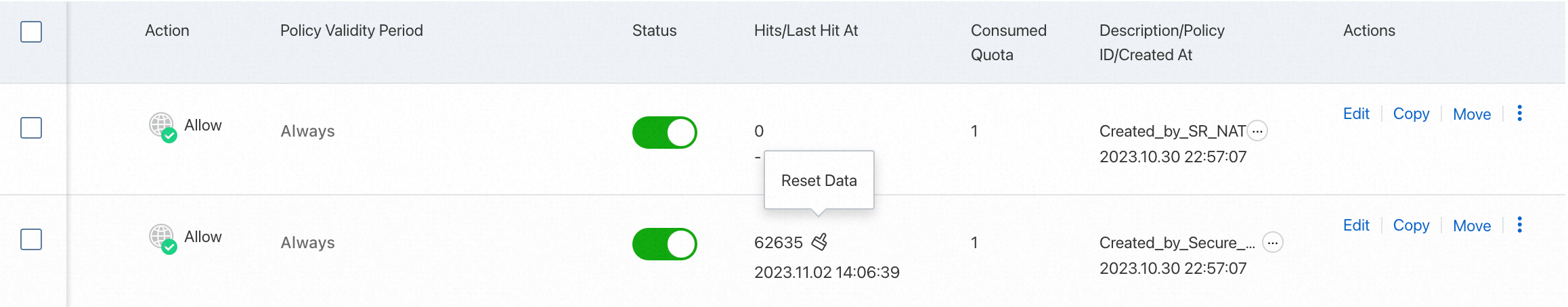
Based on the hit data, adjust your policies as needed:
Change a Monitor policy to Allow or Deny once you have observed the traffic pattern.
Remove policies that no longer match any traffic.
Tighten or broaden destination or port ranges based on actual usage.
What's next
To allow internal-facing servers to access only a specific domain name, see Configure a policy to allow only internal-facing servers to access a specific domain name.
To understand how access control policies are evaluated and prioritized, see Overview of access control policies.
To see end-to-end configuration examples, see Configure access control policies.
To manage IP address books, port address books, and domain name address books, see Manage address books.
For answers to common questions, see FAQ about access control policies.