This topic describes how to quickly locate a specific asset when total traffic at the internet border exceeds your purchased protected bandwidth, spikes, drops, or shows other unusual patterns, enabling fine-grained asset management.
Calculating internet border traffic
When Cloud Firewall processes traffic at the internet border, it uses the greater of the peak bandwidth values for inbound and outbound traffic. The formulas for calculating the total inbound and outbound traffic bandwidth are as follows:
Inbound traffic bandwidth = Internet Exposure request traffic bandwidth + Internet Exposure response traffic bandwidth
Outbound traffic bandwidth = Outbound Connection request traffic bandwidth + Outbound Connection response traffic bandwidth
Cloud Firewall calculates peak bandwidth using data aggregated over a time period. The total bandwidth at any moment is the sum of its request and response traffic. However, the individual peak for request traffic and the peak for response traffic may occur at different times within that period. Therefore, the total peak bandwidth at a specific point in time is less than or equal to the sum of the individual peak values for request and response traffic.
When to troubleshoot unusual traffic
You should locate the specific asset IP address and understand the detailed access patterns when you observe unusual peaks or troughs in your business traffic. For example, if your traffic exceeds the purchased protected bandwidth, you must identify the asset IP address responsible for the overage.
Procedure
Step 1: Identify the unusual traffic direction
Log on to the Cloud Firewall console. In the left-side navigation pane, click Overview.
On the Overview page, view the traffic trend to find a time point when there is an unusual peak bandwidth for outbound or inbound traffic.
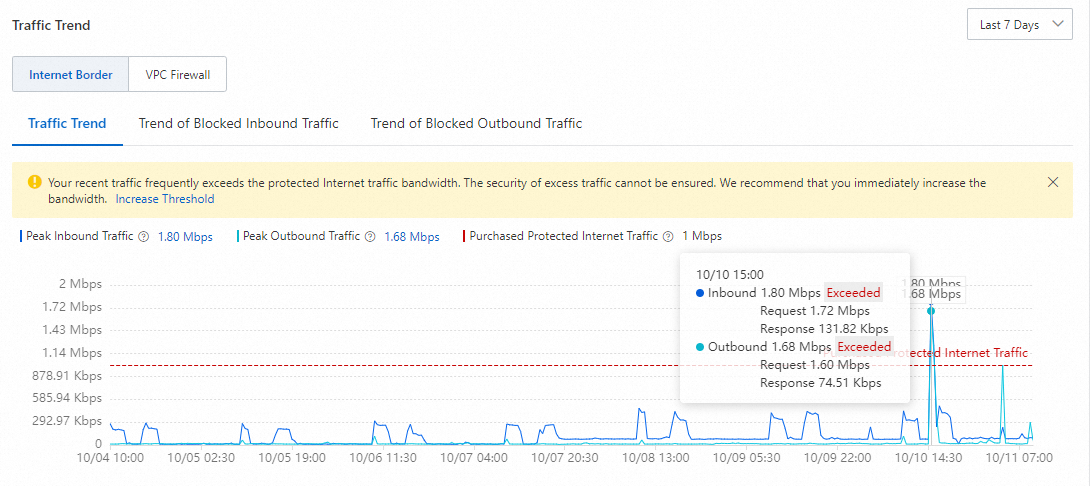
The following figure shows that the peak values for both outbound and inbound traffic at 15:00 on Oct 10 exceed the protected bandwidth.
NoteWhen traffic exceeds your protected bandwidth, the trend chart displays this limit, which helps you visualize the overage amount.
Step 2: Locate the unusual IP address
The following steps use inbound traffic as an example. The procedure for investigating outbound traffic is similar. The only difference is the location of the trend chart: for inbound traffic, you view it on the tab. For outbound traffic, you view it on the tab.
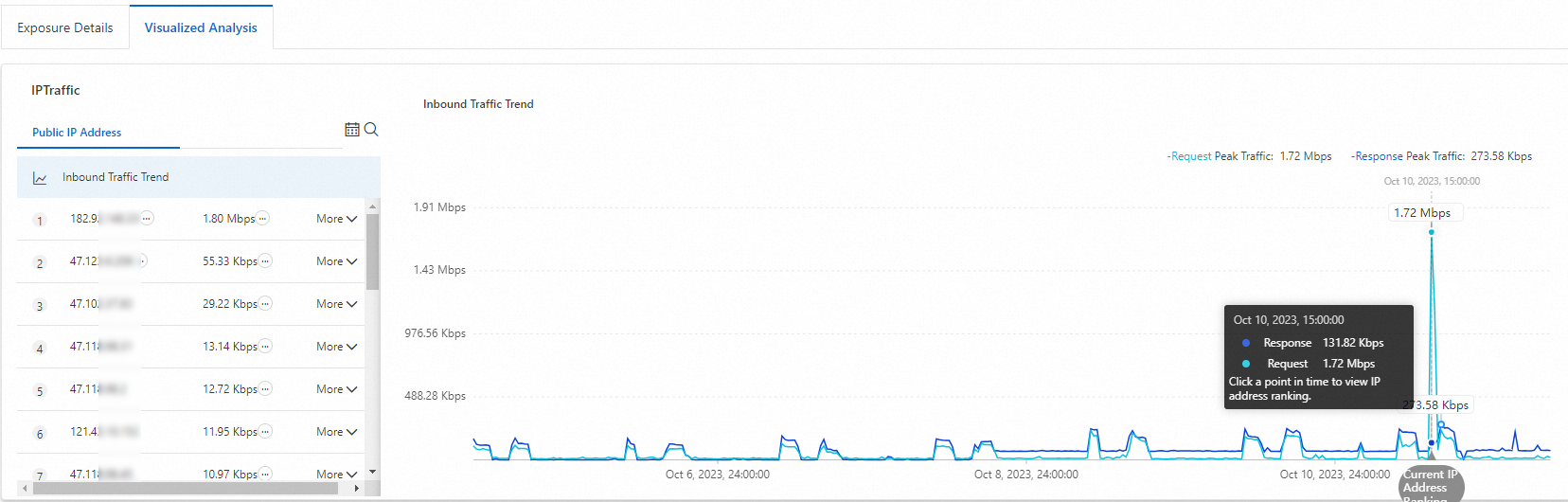
In the Traffic Trend section of the Overview page, click the peak inbound traffic value to go to the tab. View the peak inbound traffic bandwidth at 15:00 on Oct 10.
In the public IP address list, view the sorted total traffic for all assets in your account at that time. Locate the unusual asset by its rank in the list.
ImportantFor more accurate, minute-level traffic data, set the time range to the last 24 hours.
As shown in the following figure, the asset with the IP address 182.92.XX.XX is identified as the source of the unusual traffic because its total traffic at 15:00 on Oct 10 was significantly higher than that of other assets.
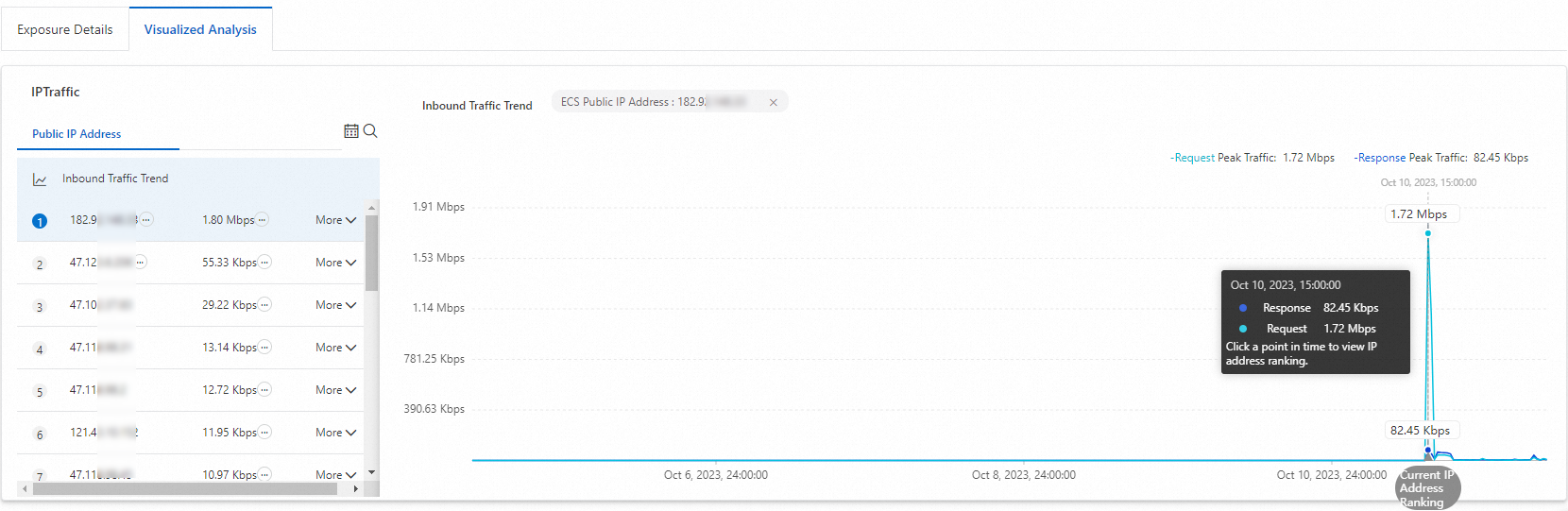
To further examine the traffic data for the unusual asset, click its IP address. The trend chart on the right displays the request and response (inbound and outbound) traffic data for this asset.
Step 3: Verify traffic legitimacy
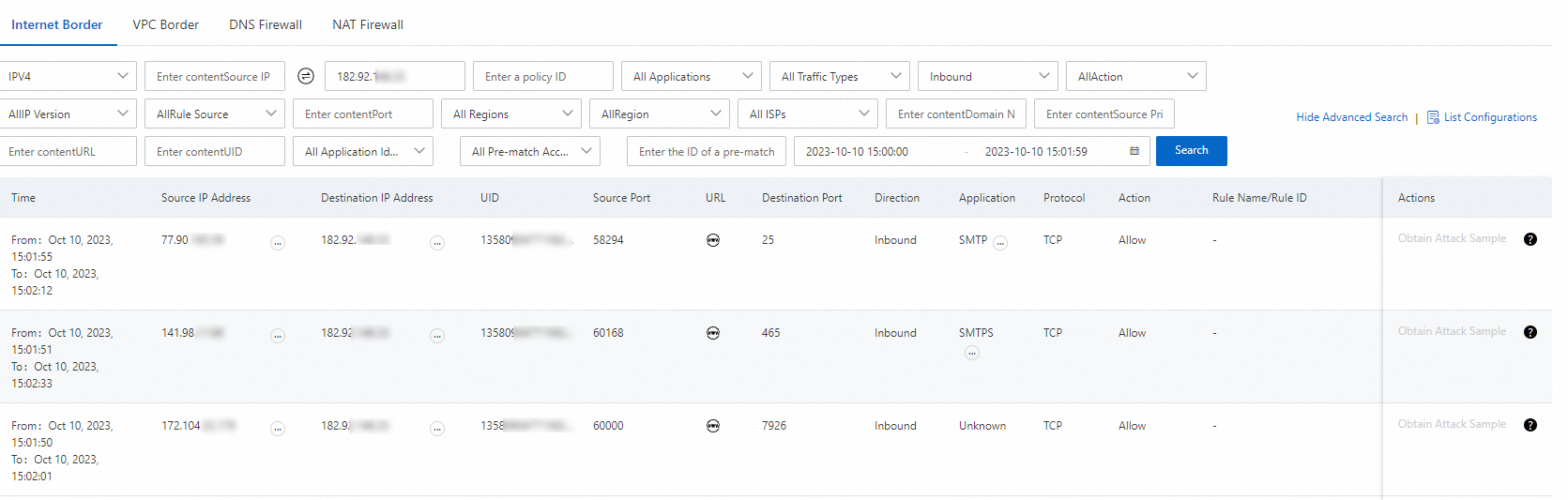
In the public IP address list, choose . On the tab, query the traffic logs. Since you are investigating inbound traffic, use 182.92.XX.XX as the destination IP address and set the time to 15:00 on Oct 10.
Based on the log query results, examine the Source IP Address, Source Port, and Destination Port to determine whether the traffic is legitimate.
Take further action based on your findings.
Upgrade the protected bandwidth of Cloud Firewall
For more information, see Renewal.
Optimize your service deployment
For example, if your services need to access Alibaba Cloud OSS or SLS, use an internal endpoint to conserve public bandwidth.
Disable Cloud Firewall for IP addresses that do not require protection
For more information, see Disable the Internet firewall.
Query unusual traffic with SQL
To quickly query all traffic for an unusual asset, use SQL statements on the page.
Query all destination IP addresses and ports accessed by an unusual asset IP address through Outbound Connection, and sort the results by traffic in descending order
log_type:internet_log and src_ip:182.92.XX.XX | select dst_ip,dst_port,app_name,sum(in_packet_bytes) as in_B,sum(out_packet_bytes) as out_B,sum(total_packet_bytes) as total_B,array_agg(distinct if(url='', domain, url)) as url group by dst_ip,dst_port,app_name order by total_B descReplace 182.92.XX.XX with the IP address of your asset.
Query all source IP addresses and ports that access an unusual asset IP address through Internet Exposure, and sort the results by traffic in descending order
log_type:internet_log and dst_ip:182.92.XX.XX | select src_ip,dst_port,app_name,sum(in_packet_bytes) as in_B,sum(out_packet_bytes) as out_B,sum(total_packet_bytes) as total_B,array_agg(distinct url) as url group by src_ip,dst_port,app_name order by total_B descReplace 182.92.XX.XX with the IP address of your asset.
References
To view the overall traffic trend for your assets and confirm if the total traffic exceeds your Cloud Firewall's protected bandwidth, see Data overview.
To view how your assets access the internet, including tracing unusual outbound traffic, the internet destinations accessed by assets, and data on Outbound Connection from public and private assets, see Outbound Connection.
To view how the internet accesses your assets, trace unusual inbound traffic, and find data on exposed public IP addresses, open ports, and applications, see Internet Exposure.
To view information about traffic at the internet border, such as source IP addresses, destination ports, supported protocols, action status, flow bytes, and flow packets, see Log Audit.
To use SQL statements to query raw logs of traffic at the internet border, see Query and analyze logs.