Cloud Firewall’s intrusion prevention system (IPS) detects and blocks malicious traffic in real time. This includes hacker attacks, vulnerability exploits, brute-force attacks, worms, mining programs, backdoor trojans, and DoS attacks. It protects your cloud-based information systems and network architecture from unauthorized access, data breaches, service damage, or breakdowns.
Limits
Cloud Firewall intrusion prevention supports decrypting and inspecting encrypted traffic through TLS inspection for outbound traffic at the Internet Border. For inbound traffic at the Internet Border, combine Cloud Firewall with the Web Application Firewall to enhance protection. TLS/SSL decryption and inspection are not supported at the VPC border.
Data aggregation introduces a delay in Cloud Firewall’s intrusion prevention statistics. To query real-time data, use log audit or log analysis. For details, see log audit or query and analyze logs.
When you query defense data for the last hour, results have a 10-minute delay. Events that occurred in the last 10 minutes do not appear in the results.
When you query defense data for more than one hour — including the most recent 30 minutes — results have a 30-minute delay. Events that occurred in the last 30 minutes do not appear in the results.
For example, if the current time is 15:00:00, querying data from 12:00:00 to 15:00:00 excludes data from 14:30:00 to 15:00:00. Querying data from 12:00:00 to 14:30:00 returns complete results for that period.
View or modify intrusion prevention rules
After you activate Cloud Firewall, the threat engine in Mitigation Settings defaults to Block Mode. In this mode, Cloud Firewall automatically blocks attacks. Cloud Firewall selects an appropriate block mode level — Loose, Moderate, or Strict — based on your service traffic. Threat intelligence, basic defense, and virtual patches are enabled by default.
You can go to the IPS Configuration page using either of these methods:
From the IPS page, click the link in the upper-right corner of the Protection Details List.

In the navigation pane on the left, select .
On the Basic Protection card, view the default intrusion prevention rules. To change a rule, find it in the list and update its action in the Current Action column. For more information, see IPS Configuration.
Enable IPS Private IP Tracing
Entry point:
From the IPS page, click the link in the upper-right corner of the Protection Details List to go directly to the IPS Private IP Tracing Configuration page.

Enable
On the IPS Private IP Tracing page, enable tracing for specific resources. This helps you quickly locate risky assets without exposing internal network asset IP addresses.
NoteIPS Private IP Tracing requires both Internet firewall protection and NAT session log service to be enabled for the same asset. For step-by-step instructions, see IPS Private IP Tracing Configuration.

Traceability:
After you enable the feature, view risky asset IP addresses in the Protection Details List and Details sections of the IPS page.
List
Details


View Internet blocking events
Cloud Firewall provides statistics on inbound and outbound Internet traffic for your cloud assets. These statistics help you assess how well Cloud Firewall protects your assets and keep them secure. You can query Internet blocking data for up to the last 90 days. Each query covers a maximum of 31 days.
Go to the page. On the Protection Status tab, set a time range and view protection statistics and the protection details list.
The Protection Statistics module shows total attacks, Attack Type Distribution, and blocking data.
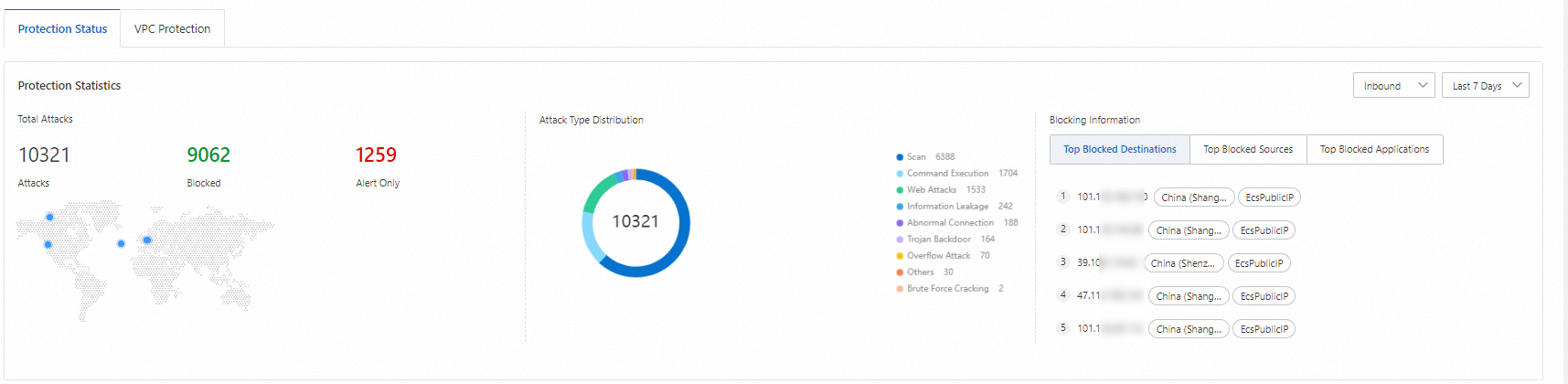
Blocking data metrics include the following:
Top Blocked Destinations: Displays the top 5 destination IP addresses among traffic blocked by Cloud Firewall.
Hover over a blocked destination IP and click the
 icon to open the Log Audit page. There, view detailed information such as destination port, application type, and action for that IP.
icon to open the Log Audit page. There, view detailed information such as destination port, application type, and action for that IP.Top Blocked Sources: Shows the top three source types by percentage among traffic blocked by Cloud Firewall.
Top Blocked Applications: Displays the top five application types among traffic blocked by Cloud Firewall.
Protection Details List: Lists protection details for attack traffic, based on your query conditions. Details include risk level, event count, source IP address, and destination IP address.
 Note
NoteIf the source IP is a WAF or DDoS back-to-origin IP address, Cloud Firewall detects such back-to-origin IP addresses and displays WAF Back-to-origin IP Address and Anti-DDoS Back-to-origin IP Address.
In this section, you can:
Search for events: Set filters such as risk level, defense status, attack type, source, direction, and time range. Then click Search to view matching events.
View event details: In the Actions column, click Details to open the blocked event details page. View Basic Information, Attack Payload, and other details. The Attack Payload shows 5-Tuple Information and content of the payloads. This helps you trace attacks and reduce security risks.
Download blocked events: Click the
 icon to the right of the search bar. Then download the events from the Download Task Management panel in the upper-right corner.
icon to the right of the search bar. Then download the events from the Download Task Management panel in the upper-right corner.AI-assisted event analysis: Click the AI Analysis column's
 icon to use the Security AI Assistant for quick event analysis assistance.
icon to use the Security AI Assistant for quick event analysis assistance.This includes:
Payload content analysis: A brief description of the request and AI analysis of the requested action.

Threat intelligence: Comparison result between the destination address and the threat intelligence database.
NoteThis feature is not available in the Cloud Firewall Premium Edition or pay-as-you-go edition.
Attacker intent: AI-predicted attacker behavior.
Mitigation recommendations: Suggestions for Cloud Firewall mitigation settings (such as ACL policies and IPS configuration) and asset checks.
View VPC blocking events
Cloud Firewall provides traffic protection statistics for traffic between VPCs. You can view traffic flow and blocking status for your VPCs. You can query VPC blocking data for up to the last 90 days. Each query covers a maximum of 31 days.
Cloud Firewall Premium Edition does not support VPC firewall and does not display the VPC Protection tab.
Go to the page. On the VPC Protection tab, view details such as event name, risk level, and attack type for VPC blocking events in your selected time range.

You can:
Search for events: Set filters such as risk level, defense status, attack type, and time. Then click Search to view matching events.
View event details: In the Actions column, click Details to open the blocked event details page. View Basic Information, Attack Payload, and other details. The Attack Payload shows 5-Tuple Information and content of the payloads. This helps you trace attacks and reduce security risks.
Download protection events: Click the
 icon to the right of the search bar. Then download the events from the Download Task Management panel in the upper-right corner.
icon to the right of the search bar. Then download the events from the Download Task Management panel in the upper-right corner.AI-assisted event analysis: Click the
 icon in the AI Analysis column to quickly analyze the event with the Security AI Assistant.
icon in the AI Analysis column to quickly analyze the event with the Security AI Assistant.This includes:
Payload content analysis: A brief description of the request and AI analysis of the requested action.

Threat intelligence: Comparison result between the destination address and the threat intelligence database.
NoteThis feature is not available in the Cloud Firewall Premium Edition or pay-as-you-go edition.
Attacker intent: AI-predicted attacker behavior.
Mitigation recommendations: Suggestions for Cloud Firewall mitigation settings (such as ACL policies and IPS configuration) and asset checks.