Bastionhost Enterprise Edition and SM Edition let O&M engineers securely connect to database assets through an SSH tunnel or browser, with every session automatically recorded for audit.
Supported databases include ApsaraDB RDS for MySQL, ApsaraDB RDS for SQL Server, and ApsaraDB RDS for PostgreSQL; PolarDB for MySQL, PolarDB for PostgreSQL, and PolarDB for PostgreSQL (Compatible with Oracle); and self-managed MySQL, SQL Server, PostgreSQL, and Oracle databases.
Bastionhost Enterprise and SM Edition are built on a reliable dual-engine architecture. Both engines are active, which ensures business continuity and meets the high requirements of database O&M. For more information, see Comparison of features between Bastionhost editions.
How it works
All database connections go through Bastionhost as a proxy. The engineer authenticates to Bastionhost with an O&M token, and Bastionhost forwards the connection to the target database. This means:
The database endpoint is never exposed directly to the engineer's machine.
All operations are recorded under the engineer's Bastionhost identity, regardless of which database account is used.
Administrators control which databases and accounts each engineer can reach.
Three connection methods are available:
| Method | How you connect | Best for |
|---|---|---|
| Client-based O&M | SSH tunnel from a local tool (e.g., Navicat Premium) or command line | Engineers who prefer a local GUI or CLI client |
| Web-based O&M | Browser session via the O&M portal | Quick access without client setup |
| SSO O&M | Single sign-on (SSO) launcher calls a local client automatically | Teams that want one-click access without manual SSH configuration |
Prerequisites
Before you begin, ensure that you have:
A database asset registered in Bastionhost. See Create a database.
A Bastionhost user account with access to that asset and its asset account. See Manage users and Authorize assets and asset accounts.
The examples in this topic use a MySQL database with local users.
Client-based O&M
This method establishes an SSH tunnel from a local database tool to Bastionhost. The following examples use Navicat Premium on Windows and a command-line terminal on Linux.
For a full list of supported client tools and versions, see Recommended client connection tools and versions.
Step 1: Get the O&M address and token
Log on to the O&M portal. See Log on to the O&M portal.
In the left navigation pane, click Databases.
Find the target database. In the Remote Connection column, select View O&M Token from the Login Method drop-down list, then click Log On.
In the O&M Token dialog box, click Apply For O&M Token.
If the current database account is not hosted on Bastionhost, you must first configure the basic information of the database account in the O&M Token dialog box before applying for a token. See Database management.
The dialog box shows the Client SSH Tunnel Configuration section with the values you need for the next step.
Step 2: Establish the SSH tunnel
Navicat Premium
Open Navicat Premium and create a MySQL connection.
On the SSH tab, select SSH Tunnel and fill in the SSH tunnel parameters:
Parameter Value Host The public or private O&M address from the Client SSH Tunnel Configuration section Port The SSH tunnel O&M port. Default: 60022User Name Your Bastionhost username Password The O&M token from Step 1 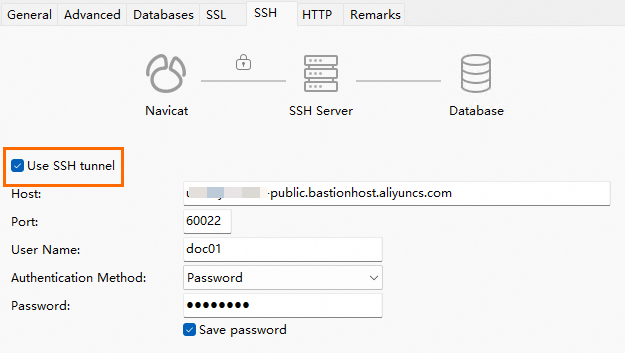
On the General tab, fill in the database connection details:
Save the password in Navicat. If you leave it blank, Navicat may prompt for a password during connection — enter the O&M token in that case.
Parameter Value Host The database endpoint User Name The database account username Password Leave blank if the administrator has hosted the account credentials in Bastionhost. Otherwise, enter the database password. 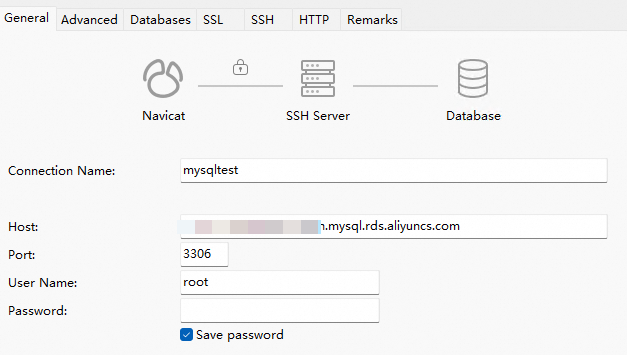
Double-click the connection to connect. You can now run O&M operations on the database.
Terminal (command line)
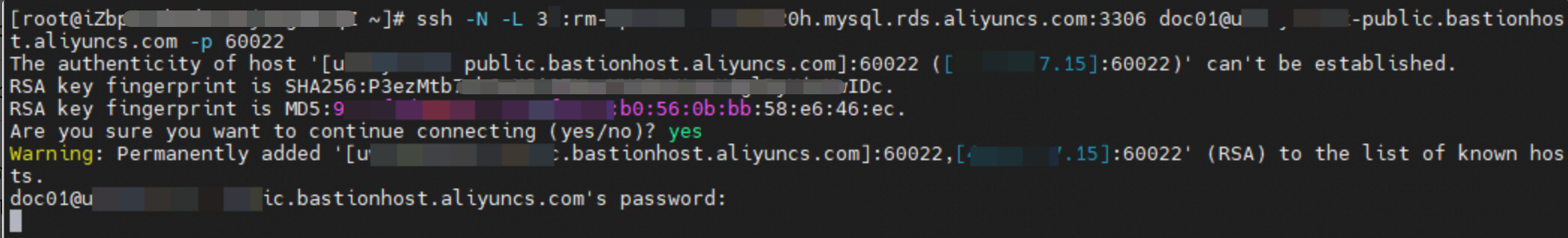
Run the following command to open the SSH tunnel:
Placeholder Description <localport>A local port you choose for the tunnel. Make sure it is not already in use. <databaseAddress>The endpoint of the target database <databasePort>The port of the target database <bastionusername>Your Bastionhost username <bastionAddress>The public O&M address of Bastionhost <bastionPort>The SSH O&M port. Default: 60022ssh -N -L <localport>:<databaseAddress>:<databasePort> <bastionusername>@<bastionAddress> -p <bastionPort>Example:
ssh -N -L 33061:rm-******m020h.mysql.rds.aliyuncs.com:3306 bastuser@******-public.bastionhost.aliyuncs.com -p 60022When prompted for a password, enter the O&M token and press Enter. The terminal waits — this is expected.
Open a second terminal and verify that the local port is listening. The output should show
LISTENnext to your chosen port.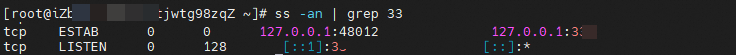
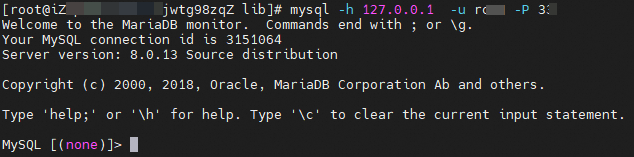
Connect to the database through the tunnel:
Placeholder Description <accountname>The database account username <localport>The local port you specified in step 1 mysql -h 127.0.0.1 -u <accountname> -P <localport>You can now run O&M operations on the database.
Web-based O&M
Connect directly from a browser — no SSH tunnel or client configuration required. You can use the O&M portal or web console for web-based O&M. The following steps use the O&M portal as an example.
Log on to the O&M portal of Bastionhost. See Log on to the O&M portal.
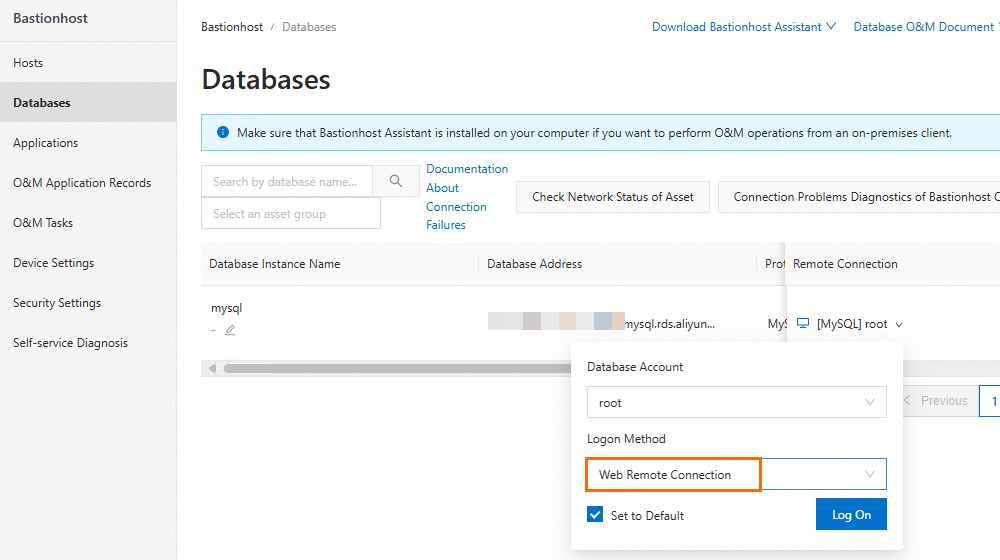
In the left navigation pane, click Databases.
Find the target database. In the Remote Connection column, select Web Remote Connection from the drop-down list, then click Log On. A browser-based database session opens.
SSO O&M
The SSO (single sign-on) launcher detects your local client and opens a session automatically — no manual SSH configuration needed. This example uses DBeaver 23 on Windows.
For supported client tools, see Clients supported by the single sign-on launcher.
Step 1: Get the O&M portal address
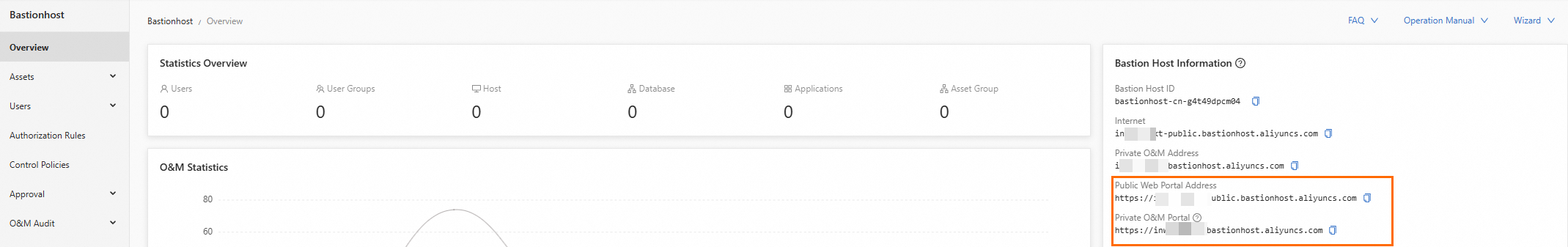
Log on to the Bastionhost console. In the top navigation bar, select the region where your Bastionhost instance is located.
In the instance list, find your instance and click Manage.
In the left navigation pane, click Overview to see the O&M portal address.
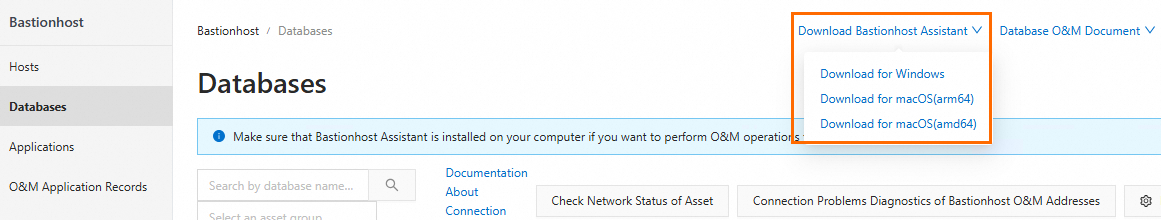
Step 2: Install the single sign-on launcher
Enter the O&M portal address in your browser.
On the Alibaba Cloud Bastionhost login page, enter your username and password, then click Log On.
Click Download Single Sign-on Launcher and download the Windows installer.
Install the launcher. You do not need to open it after installation.
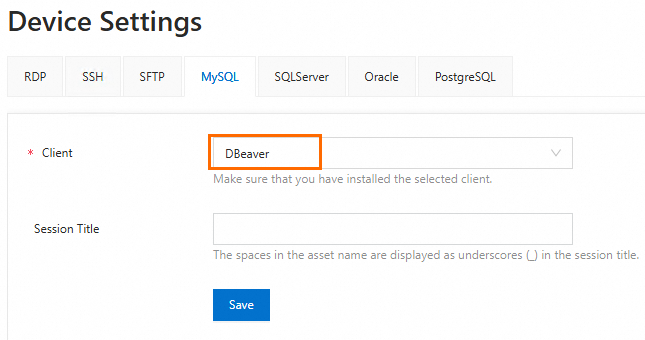
Step 3: Configure the O&M terminal
In the left navigation pane of the O&M portal, click Device Settings.
On the MySQL tab, select DBeaver and click Save.
In the usmsso.exe dialog box, click Open and follow the on-screen instructions to finish configuring the client.
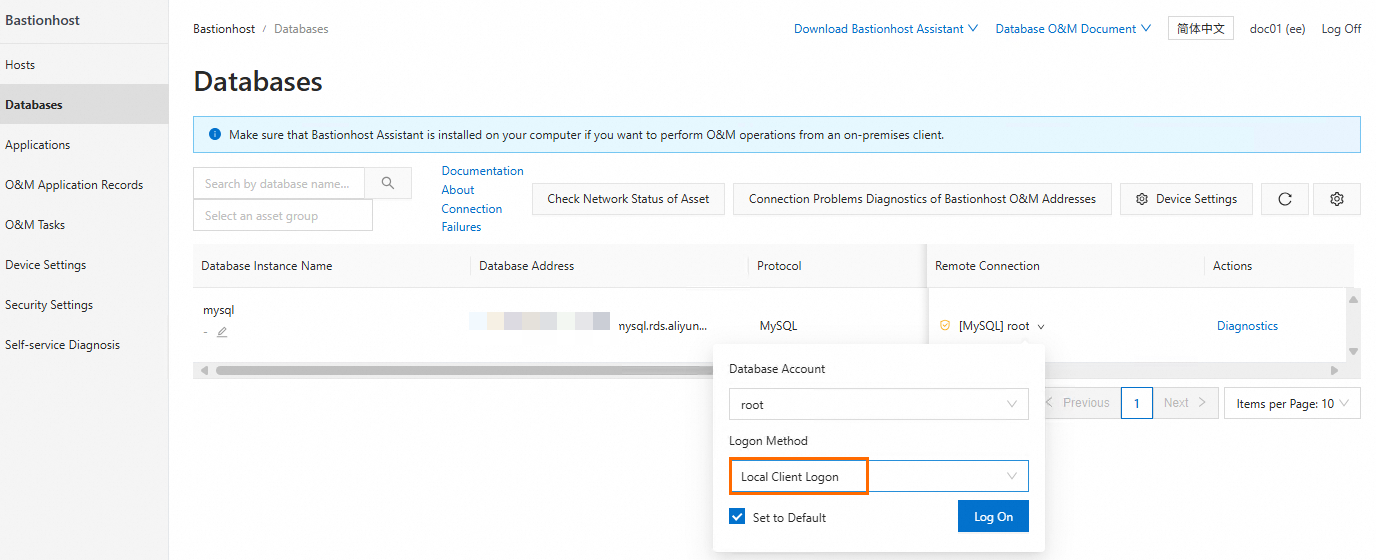
Step 4: Connect to the database
In the left navigation pane, click Databases.
Find the target database. In the Remote Connection column, select Local Client Logon from the drop-down list, then click Log On. DBeaver opens and connects to the database automatically.
Audit sessions
After an O&M session ends, Bastionhost generates session records and operation logs. Auditors can review these records or monitor active sessions in real time to detect unauthorized operations.
Log on to the Bastionhost console and select the region of your instance.
In the instance list, find your instance and click Manage.
In the left navigation pane, choose O&M Audit > Session Audit.
On the Session Audit page, view or search session records.
Audit logs record the user who requested the O&M token, not the username or asset account entered in the client tool.
Troubleshooting
Token-related issues
| Symptom | Cause | Action |
|---|---|---|
| Connection fails even though the token is valid | Concurrent O&M connection limit reached | Contact your administrator to upgrade the Bastionhost instance type or release idle connections |
| Connection fails even though the token is valid | Source IP address or time period blocked by administrator | Contact your administrator to remove the restrictions |
| Token expired before use | Token validity period elapsed | Request a new token. If O&M approval is enabled, submit a new approval request. |
| New token settings not taking effect | Settings were changed after the token was issued | Request a new token or update the existing one |
Token renewal
If the administrator allows self-renewal, renew the token before it expires.
After a token expires, request a new one.
If O&M approval is enabled, token self-renewal is not available.