Frequently asked questions about Bastionhost deployment scenarios, network connectivity, and supported asset types.
Can Bastionhost manage hosts outside Alibaba Cloud?
Yes. As long as there is network connectivity between the external host and your Bastionhost instance (for example, over the Internet), add the host directly in the Bastionhost console. For details, see Create a host.
If your assets are in different VPCs or accounts with no leased line connecting them, use the Bastionhost network domain feature to establish connectivity. For details, see Best practices for hybrid O&M scenarios.
Does Bastionhost support O&M across accounts and VPCs?
Yes. When a Bastionhost instance and a target server are in different accounts or VPCs, you have two options:
Over the Internet: Manage the asset directly using its public IP address.
Over an internal network: Connect the networks using a leased line.
If an internal network connection is required but a leased line is not available, configure the network domain feature. For details, see Best practices for hybrid O&M scenarios.
How do I manage an ECS instance in a classic network?
Use ClassicLink to connect your Bastionhost VPC to the classic network. After the connection is established, Bastionhost can reach the ECS instance through the internal network. For details about ClassicLink, see ClassicLink overview.
Does Bastionhost support database O&M?
Yes. Bastionhost Enterprise Dual-engine Edition provides privileged access control for the following database types:
ApsaraDB RDS for MySQL, SQL Server, and PostgreSQL
Self-managed databases
Only Bastionhost V3.2 supports the Enterprise Dual-engine Edition.
For a setup walkthrough, see Best practices for database O&M.
What asset types does Bastionhost support?
Bastionhost supports the following asset types:
Host assets
Linux hosts
Windows hosts
Database assets
MySQL
SQL Server
PostgreSQL
Import methods
| Asset source | Import method |
|---|---|
| Alibaba Cloud ECS or ApsaraDB RDS | Single-click import from the console |
| On-premises data centers or heterogeneous clouds | Batch import |
For a full list of supported configurations, see O&M overview.
Is data encrypted in transit and at rest?
Yes. Bastionhost encrypts all data in transit using HTTPS (TLS), RDP, and SSH. Data stored in Bastionhost is also encrypted.
Does Bastionhost support servers that use public IP addresses for private communication?
Yes. Configure the public IP address for private use directly in the Bastionhost console. For details, see Configure Bastionhost.
Does Bastionhost support SSH command-line O&M?
Yes. Bastionhost supports the ssh -J command, which connects to a target host through Bastionhost as a jump server.
Command syntax
ssh -J was introduced in OpenSSH 7.3. Use the following format:
ssh -J <bastionhost_user>@<bastionhost_address>:60022 <host_username>@<host_ip>For example, to connect through Bastionhost B to target host C:
ssh -J user@B user@CRemote Command Execution
Bastionhost also includes a Remote Command Execution feature, which lets you run commands on a target host through Bastionhost in command-line mode. To restrict its use, go to Control Policies > Protocol Control > SSH Options.
Does Bastionhost support remote command-based O&M?
Yes, it does. Bastionhost supports the ssh -J command, which is used to connect to a target host through a jump server or Bastionhost. This provides a secure way to access an internal network.
Method for remote command-based O&M
ssh -J is a command parameter that was introduced in OpenSSH 7.3. It is used to connect to a host through a jump server or Bastionhost. The connection command is as follows:
ssh -J <bastionhost_user>@<bastionhost_address>:60022 <host_username>@<host_ip>For example, the following command first connects to Bastionhost B and then connects to the target host C from Bastionhost B using SSH.
ssh -J user@B user@CScenario for remote command-based O&M
Remote Command Execution lets you connect to a specified host through Bastionhost using SSH in command-line mode and executing commands. You can navigate to to restrict the use of Remote Command Execution.
How do I set up an HTTP and SOCKS5 proxy server?
This example uses an Alibaba Cloud server running CentOS 8.3 and the 3proxy tool.
Log in to the server.
Install 3proxy:
yum install 3proxyEdit the configuration file:
vim /etc/3proxy.cfgConfigure the following settings:
Host account and password for the proxy server.
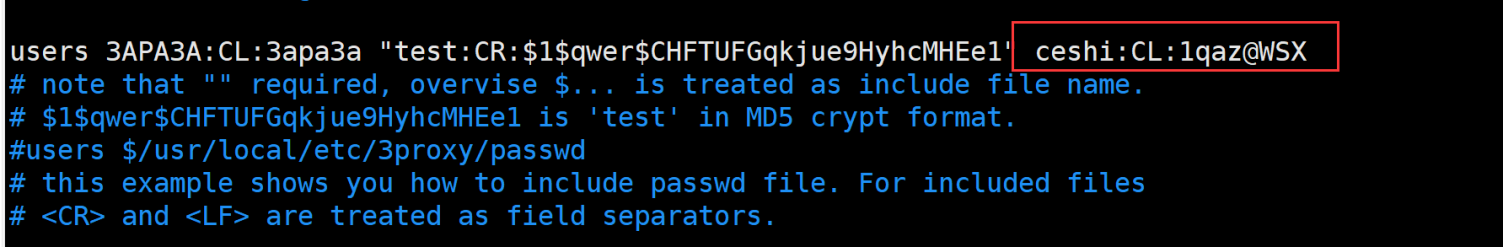
Access control parameters.
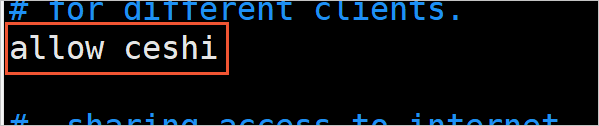
HTTP and SOCKS5 proxy settings: enable both proxies, set the listener port, and specify the source IP address allowed to access the proxy.
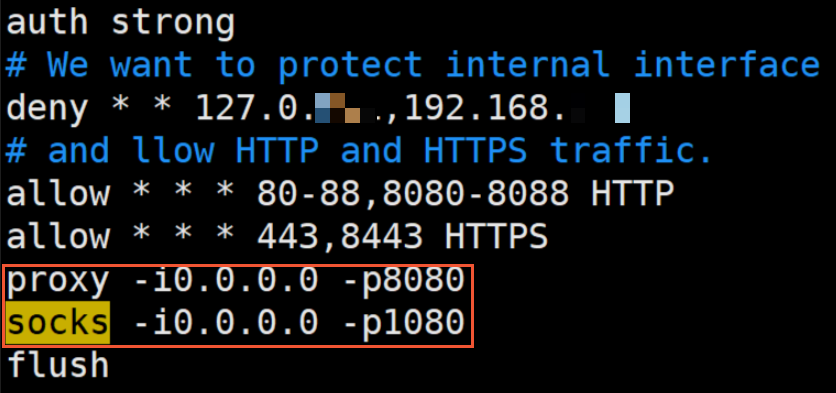
Start the proxy service:
systemctl start 3proxy.serviceDisable the server firewall to allow incoming connections:
iptables -FAdd an inbound security group rule for the server. Set Port Range to the listener port you configured in step 3, and set Authorization Object to the egress IP address of your Bastionhost instance. Find the egress IP on the Instances page in the Bastionhost console. For instructions, see Add a security group rule.
The proxy server is ready after you add the security group rule.
How do I set up an HTTPS proxy server?
This example uses a CentOS 8.3 ECS instance and the GOST tool.
Step 1: Prepare certificates
Obtain the following certificate files: server.crt (server certificate), server.key (private key), and ca.crt (CA certificate). Use either of these methods:
Generate a self-signed certificate with OpenSSL.
Get a free personal test certificate or purchase a commercial certificate. See SSL certificate selection guide.
Step 2: Install GOST
Follow the instructions at Install GOST.
Step 3: Configure and start the GOST proxy
Upload the certificate files to the GOST installation folder, then start GOST using one of the following methods.
Option A: Command line
gost -L="https://admin:123456@:8843?cert=./server.crt&key=./server.key"| Parameter | Description |
|---|---|
admin:123456 | GOST username and password. These correspond to Host Account and Password in the Bastionhost network domain. |
8443 | Proxy listener port. This corresponds to Server Port in the Bastionhost network domain. |
./server.crt | Path to the server certificate. |
./server.key | Path to the server certificate private key. |
Option B: JSON configuration file
Create a file named gost.json with the following content:
{
"ServeNodes": [
"https://admin:123456@:8843?cert=./server.crt&key=./server.key"
]
}The parameter descriptions are the same as Option A. Start GOST with:
gost -C gost.jsonStep 4: Add a security group rule
Add an inbound security group rule on the ECS instance. Set Port Range to 8443 and Authorization Object to the egress IP address of your Bastionhost instance. Find the egress IP on the Instances page in the Bastionhost console. For instructions, see Add a security group rule.