Deploy Anti-DDoS Origin and Web Application Firewall (WAF) together to protect your website against both Layer 4 DDoS attacks and Layer 7 web attacks, including CC attacks.
How traffic flows after deployment: All requests reach WAF first. WAF scrubs Layer 7 attacks — web exploits and CC attacks — and forwards clean traffic to your origin server. Anti-DDoS Origin protects the WAF instance's public IP, absorbing volumetric DDoS floods before they reach WAF.
Deployment order: Connect your website to WAF first, then add the WAF instance's IP as a protected object in Anti-DDoS Origin.
Prerequisites
Before you begin, ensure that you have:
An ECS instance with a public IP address and a website domain name
If your website serves users in the Chinese mainland, the domain name must complete ICP filing before you can connect it to a WAF instance in the Chinese mainland.
An Anti-DDoS Origin instance purchased in the same region as your ECS instance. See Purchase an Anti-DDoS Origin instance.
A WAF 3.0 subscription instance. See Purchase a subscription WAF 3.0 instance.
Steps overview
Configure listeners — add your domain name to WAF and configure protocol and port settings.
Configure forwarding — specify your origin server address.
Switch traffic — update DNS to route traffic through WAF.
Add protected objects — add the WAF instance's IP to Anti-DDoS Origin.
Step 1: Configure listeners
Log on to the WAF 3.0 console. In the top menu bar, select the resource group and region for your WAF instance (Chinese MainlandWeb Application Firewall 3.0 console or Outside Chinese Mainland). In the left navigation pane, click Onboarding. On the CNAME Record tab, click Add.
Add a domain name
In the Domain Name field, enter the domain name to protect. Enter one domain name — either an exact-match domain name (such as www.aliyundoc.com) or a wildcard domain name (such as *.aliyundoc.com).
Wildcard matching rules:
A wildcard matches only subdomains at the same level. For example,
*.aliyundoc.commatcheswww.aliyundoc.comandexample.aliyundoc.com, but notwww.example.aliyundoc.com.When a wildcard applies to a second-level domain (such as
*.aliyundoc.com), it also matches the second-level domain itself (aliyundoc.com).When a wildcard applies to a third-level domain (such as
*.example.aliyundoc.com), it does not match the third-level domain itself (example.aliyundoc.com).
Priority rule: If both an exact-match and a wildcard domain name are added and a request matches both, WAF applies the exact-match domain's protection rules first.
Verify domain ownership
If WAF prompts you to verify ownership after entering the domain name, choose one of the following methods.
Method 1: DNS validation (recommended)
In the validation prompt area, click the Method 1: DNS Record tab.
Use the Record Type, Hostname, and Record Value provided in the WAF console to add a TXT record in your DNS provider console. If you use Alibaba Cloud DNS:
Go to Public authoritative DNS resolution and find your primary domain name. Click Settings in the Actions column.
Click Add Record, enter the following parameters, and click OK. Leave other parameters at their defaults.
Record Type: TXT
Hostname: Copy and enter the prefix provided by WAF, such as
verification.Record Value: Copy and enter the value provided by WAF, such as
verify_8fca29dec226****.
Wait for the TXT record to take effect. A newly added record takes effect immediately. Changes to an existing record usually take 10 minutes to propagate, depending on the TTL setting (default: 10 minutes).
Return to the WAF console and click Verify.
Verification succeeded — domain ownership is confirmed.
Verification failed — troubleshoot as follows:
Check the TXT record. Confirm the hostname and record value match exactly what the WAF console shows. If they differ, delete the incorrect record, add the correct one, and verify again.
Wait for DNS propagation. DNS changes may not apply immediately. Wait 10 minutes and verify again.
Switch methods. If verification continues to fail, use Method 2: Verification File.
Method 2: File validation
In the validation prompt area, click the Method 2: Verification File tab.
Click the download link for the validation file (①) to download it.
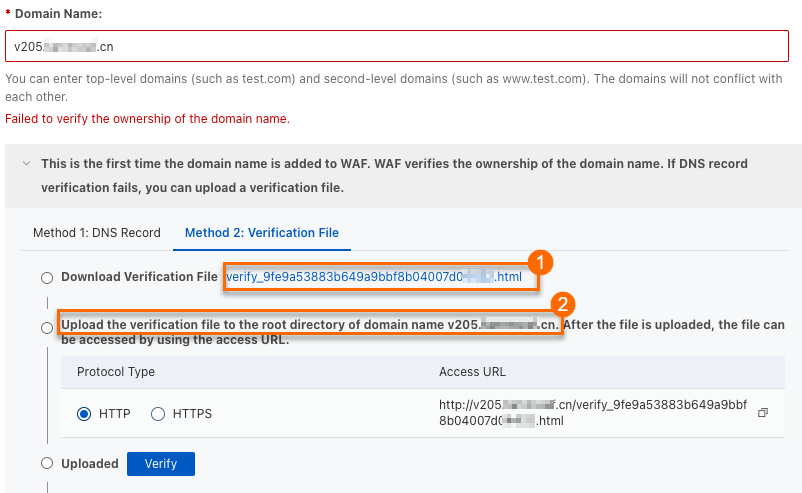 Important
Important- The validation file expires three days after download. If you do not complete validation within this period, download it again. - Do not modify, edit, or rename the file. - WAF accesses your origin server based on the protocol you select. Allow the corresponding inbound traffic on your origin server: - HTTP: Allow inbound TCP port 80 from
0.0.0.0/0. - HTTPS: Allow inbound TCP port 443 from0.0.0.0/0.Upload the validation file to the root directory of your origin server (such as ECS, OSS, CVM, COS, or EC2) (②).
If you added a wildcard domain name such as
*.aliyun.com, upload the file to the root directory ofaliyun.com.Return to the WAF console and click Verify.
Verification succeeded — domain ownership is confirmed.
Verification failed — troubleshoot based on the error:
Issue
Solution
Cannot access the domain name
1. Check DNS resolution for your domain. Make sure a DNS record points to your origin server. For Alibaba Cloud DNS, see Add a DNS record. 2. Check your origin server security group or firewall rules. Make sure inbound requests from the Internet are allowed. For ECS, see Add a security group rule.
Validation file not found
Re-upload the validation file to your origin server.
Incorrect file content
1. Delete the incorrect validation file from your origin server. 2. Re-upload the correct validation file.
After ownership verification is complete, remove the security group rule that allows access from all IP addresses — unless your origin server's initial security group already includes the
0.0.0.0/0rule.
Configure protocol and port
Select the Protocol Type (HTTP, HTTPS, or both) and enter the required settings.
The Shared Virtual Host Edition of WAF does not support HTTPS.
HTTP
HTTP Port — Enter the port users use to access your website. Port 80 is recommended for HTTP. To use a custom port, select from the supported port range. Press Enter after each port entry.
HTTPS
HTTPS Port — Enter the port users use to access your website. Port 443 is recommended for HTTPS. To use a custom port, select from the supported port range. Press Enter after each port entry.
HTTPS Upload Type — Upload the SSL certificate for your domain name so WAF can inspect HTTPS traffic. Choose one of the following options:
Manual upload: Use this if your certificate has not been uploaded to Alibaba Cloud Certificate Management Service.
Select existing certificate: Choose a certificate already available in Alibaba Cloud Certificate Management Service.
Apply for a new certificate: Use this if you do not own an SSL certificate for this domain. Purchase one first, then connect it to WAF after it is issued.
Manual upload
Certificate Name: Enter a unique name that does not duplicate any existing certificate.
Certificate File: Paste the certificate content in PEM, CER, or CRT format. Example:
-----BEGIN CERTIFICATE-----......-----END CERTIFICATE-----Format conversion: If your certificate is in PFX or P7B format, use the certificate tool to convert it to PEM format.
Certificate chain: If the certificate includes intermediate certificates, paste them in order — server certificate first, then intermediate certificates.
Private Key: Paste the private key in PEM format.
RSA:
-----BEGIN RSA PRIVATE KEY-----......-----END RSA PRIVATE KEY-----ECC:
-----BEGIN EC PRIVATE KEY-----......-----END EC PRIVATE KEY-----
Select existing certificate
Select the certificate from the dropdown list.
Apply for a new certificate
If you have not purchased a certificate, see Purchase a commercial certificate. Click Apply to read the related documentation.
If the WAF console shows Failed to verify the integrity of the certificate chain. If you use this certificate, service access may be affected., the certificate chain is incomplete. Check the certificate content, then re-upload it in the Certificate Management Service console. See Upload, synchronize, and share SSL certificates.
Step 2: Configure forwarding
In the Server address section, enter the IP address or domain name of your origin server. WAF forwards clean traffic to this address.
Complete the configuration based on your origin server type. IP Domain name (such as CNAME)
Origin Port: The port WAF uses to fetch content from your origin server. By default, this matches the HTTP/HTTPS port configured in Step 1. To use a different port, select from the supported port range.
Origin IP Address: Enter the public IP address of your origin server.
Enter up to 20 IP addresses. Press Enter after each one. When multiple addresses are configured, WAF distributes requests based on the load balancing algorithm setting.
Configure IPv4 and IPv6 addresses separately or together. To use IPv6 addresses, enable IPv6 protection in the listener configuration.
Origin Port: The port WAF uses to fetch content from your origin server. By default, this matches the port configured in Step 1. To use a different port, select from the supported port range.
Origin Domain Name: Enter the domain name of your origin server. WAF resolves this to IPv4 addresses only. For IPv6 websites, use the IP address method instead.
ImportantIf your origin server address changes, update this setting promptly.
(Optional) To customize advanced settings — such as load balancing algorithm, secondary origin server, HTTP origin fetch, origin SNI, request header configuration, traffic tagging, connection timeout, retry on 5XX error, origin keep-alive, SM SSL, HTTP/2, force redirect, TLS version, SSL cipher suite, Layer 7 proxy before WAF (such as CDN), IPv6, exclusive IP address, and intelligent load balancing — see Advanced configuration. If no customization is needed, keep all other settings at their defaults and click Submit.
Step 3: Switch traffic
After completing the configuration in the WAF console, switch traffic to WAF. Without this step, WAF protection does not take effect.
Allow WAF origin-facing IP ranges
If your origin server uses security group rules, firewall rules, or security software such as SafeDog or YunSuo, add WAF's origin-facing IP ranges to the allowlist on your origin server. Otherwise, WAF's back-to-origin requests may be blocked, causing service interruption.
Restrict your origin server to accept traffic only from WAF's origin-facing IP ranges. This prevents attackers from bypassing WAF by directly accessing your origin server's public IP address.
On the Add Completed wizard page, click WAF IP address in the upper-right corner.
In the Back-to-origin CIDR Block dialog box, click Copy to copy all WAF origin-facing IP ranges to your clipboard.
The copied IP ranges are comma-separated. Some entries, such as
2408:400a:3c:xxxx::/56, are IPv6 CIDR blocks.Add these IP ranges to your server firewall. For example, if your origin server is an ECS instance:
In the ECS instance details page, click Security group > Security Groups, select the target security group, and open its details page.
Under Inbound, click Add Rule.
Because a single security group rule cannot contain both IPv4 and IPv6 addresses, add two rules:
Add an IPv4 rule: In the Create Security Group Rule panel, paste the copied IP ranges into the Source field. Manually delete any IPv6 addresses. Set Destination (this instance) to the origin port configured in Step 2. Keep other settings at their defaults and click Submit.
Add an IPv6 rule: Click Add Rule again. In the Source field, select IPv6 and paste the IPv6 address ranges.
Verify WAF configuration locally
Before changing your domain's DNS settings, verify the WAF configuration using your local hosts file. This confirms that WAF is correctly configured before routing live traffic through it.
On the Add Completed wizard page, click Copy CNAME to copy the CNAME address provided by WAF.
Go to Network diagnostics and analysis, enter the copied CNAME address (for example,
xxx.c.yundunwaf2.com), and click Run test now.Copy the IP address from the DNS provider resolution result. Then modify your local computer's
hostsfile. Windows macOSOpen
C:\Windows\System32\drivers\etc\hostsin Notepad. Add the following line at the end and save the file:<IP address copied in the previous step> <domain name added to WAF>Open
cmdand runping <domain name added to WAF>. If the returned IP address matches the one you added, the change took effect. Otherwise, runipconfig /flushdnsto flush the DNS cache and ping again.Open a browser and navigate to the protected domain name.
If the website loads normally, the WAF configuration is correct. Proceed to the next step.
If the website fails to load, review the WAF configuration, fix any issues, and re-verify locally.
After local verification, restore the
hostsfile to its original state.
Press
Command + Spaceto open Terminal.Run
sudo vim /etc/hoststo open thehostsfile.Add the following line at the end and save the file: ``
<IP address copied in the previous step> <domain name added to WAF>``Run
ping <domain name added to WAF>. If the returned IP address matches the one you added, the change took effect. Otherwise, runsudo killall -HUP mDNSResponderto flush the DNS cache and ping again.Open a browser and navigate to the protected domain name.
If the website loads normally, the WAF configuration is correct. Proceed to the next step.
If the website fails to load, review the WAF configuration, fix any issues, and re-verify locally.
After local verification, restore the
hostsfile to its original state.
Update DNS resolution
Point your domain's DNS to the CNAME address provided by WAF. This routes web traffic through WAF for protection.
Perform this operation during off-peak hours to minimize impact on your service.
On the Add Completed wizard page, click Copy CNAME to copy the WAF CNAME address.
Update your domain's DNS resolution. If your DNS is hosted on Alibaba Cloud DNS: Keep the following in mind when modifying DNS records:
For the same host record, only one CNAME record value is allowed. Replace the current value with the WAF CNAME address.
CNAME records conflict with A, MX, and TXT records for the same host record. Delete conflicting records before adding the new CNAME record.
Go to Public authoritative DNS resolution, find your domain name, and click Actions > Settings.
Find the hostname you want to update and click Actions > Edit. For example, if the domain connected to WAF is
www.aliyundoc.com, locate the host recordwwwunder the primary domainaliyundoc.com.In the Edit Record panel, set Record Type to CNAME and Record Value to the WAF CNAME address. Keep other settings unchanged.
WarningDuring DNS changes, some users may experience brief service interruptions. Delete the original record and add the new CNAME record as quickly as possible.
Click OK to save. Wait for the DNS change to take effect.
DNS propagation takes time. If your website fails to load immediately after the change, wait 10 minutes and refresh the page.
Step 4: Add protected objects
Add the WAF instance's IP as a protected object in Anti-DDoS Origin. This gives the WAF instance the unlimited protection capability of Anti-DDoS Origin, which automatically triggers traffic scrubbing when your service is under a DDoS attack.
Log on to the Traffic Security console.
In the left navigation pane, choose Network Security > Anti-DDoS Native > Protected Objects.
In the top navigation bar, select the resource group for your instance. Set the region to All Regions.
Click Add Object for Protection. On the Add Asset tab, select WAF in the Objects to Select section, move it to the Selected Objects section, and click Confirm. For detailed steps, see Protected objects.
What's next
What is Web Application Firewall? — Learn more about WAF's protection capabilities.
Advanced configuration — Customize load balancing, SSL settings, and more.
Protected objects — Manage and update protected objects in Anti-DDoS Origin.