This page defines key concepts for Anti-DDoS Pro and Anti-DDoS Premium.
Attack types
Anti-DDoS services protect against two broad categories of attacks, organized by the OSI layer they target.
Network-layer attacks (L3/L4)
Volumetric attack
A volumetric attack floods the target's network bandwidth. Attackers use fleets of controlled computers or packet generators to send massive volumes of requests or packets, exhausting available bandwidth and making services unreachable.
Anti-DDoS Pro and Anti-DDoS Premium absorb and scrub this traffic at the network edge before it reaches your origin server.
Connection flood attack
A connection flood attack targets the transport layer. Attackers use zombie terminals to flood the target server with TCP connection requests, depleting server resources—connections, CPU, and memory—until it can no longer respond to legitimate traffic.
Application-layer attacks (L7)
Web resource exhaustion attack
A web resource exhaustion attack targets HTTP and HTTPS endpoints. Rather than overwhelming bandwidth, it mimics legitimate user actions—login, registration, search—to exhaust application resources on the target site, preventing it from serving real users.
Application-layer attack
An application-layer attack targets server resources directly. Malicious requests consume the server's memory or CPU until it cannot respond to normal requests.
Protection mechanisms
Traffic scrubbing
Traffic scrubbing is the core mitigation mechanism. Anti-DDoS devices and services analyze incoming traffic in real time, separate attack traffic from legitimate traffic, and forward only clean traffic to your origin server. This reduces load and risk on your infrastructure.
Blackhole filtering
Blackhole filtering is a last-resort mechanism triggered when DDoS attack traffic exceeds the maximum mitigation capacity of the scrubbing service. To protect other services sharing the same network, all traffic to the targeted IP address is dropped.
If blackhole filtering is triggered, check the Blackhole filtering policy of Alibaba Cloud for trigger thresholds, automatic deactivation timelines, and options to request early deactivation.
Best-effort protection
Best-effort protection uses all available cluster resources to mitigate attacks. If an attack exceeds the cluster's maximum mitigation capacity, blackhole filtering may be triggered as a fallback.
This protection mode applies to Anti-DDoS Pro and Anti-DDoS Premium instances.
Burstable protection
Burstable protection is available in the Professional Edition of Anti-DDoS Pro (the Chinese mainland). Set a maximum attack traffic threshold—the burstable protection bandwidth—above your basic protection bandwidth. When peak attack traffic exceeds the basic protection bandwidth but stays below the configured burstable protection bandwidth, burstable protection activates and absorbs the excess traffic.
Burstable protection fees are charged for the day the attack occurs. For billing details, see Billing method of burstable protection bandwidth.
Advanced mitigation
Advanced mitigation, also known as best-effort protection, is designed to defend against every DDoS attack by pooling the full capacity of all Anti-DDoS scrubbing centers in the current Alibaba Cloud region.
How it works
When an Anti-DDoS Proxy instance receives more than 5 Gbit/s of DDoS attack traffic, one advanced mitigation session is consumed. The session covers all attacks on that instance for a 24-hour window—no additional sessions are consumed during that period.
Supported editions
| Product | Edition or plan |
|---|---|
| Anti-DDoS Pro (the Chinese mainland) | Premium Edition |
| Anti-DDoS Premium (outside the Chinese mainland) | Insurance, Unlimited, and Sec-MCA mitigation plans (Sec-MCA 1.0, Sec-CMA (Basic), Sec-MCA 2.0 (Insurance), Sec-MCA 2.0 (Unlimited)) |
For billing details, see Billing of Anti-DDoS Pro (the Chinese mainland). For Anti-DDoS Premium billing, see Billing of the Insurance and Unlimited mitigation plans and Billing of the Sec-MCA mitigation plan.
Anycast
Anti-DDoS Premium (outside the Chinese mainland) uses the anycast routing method. Anycast is a network addressing and routing technique that routes traffic destined for a single IP address to the nearest server in a distributed group—in this case, the nearest scrubbing center with mitigation capacity. This enables traffic scheduling that prioritizes availability even under high concurrency and network congestion.
Note: Anycast routing may involve cross-border data transmission. For details, see Cross-border data transmission.
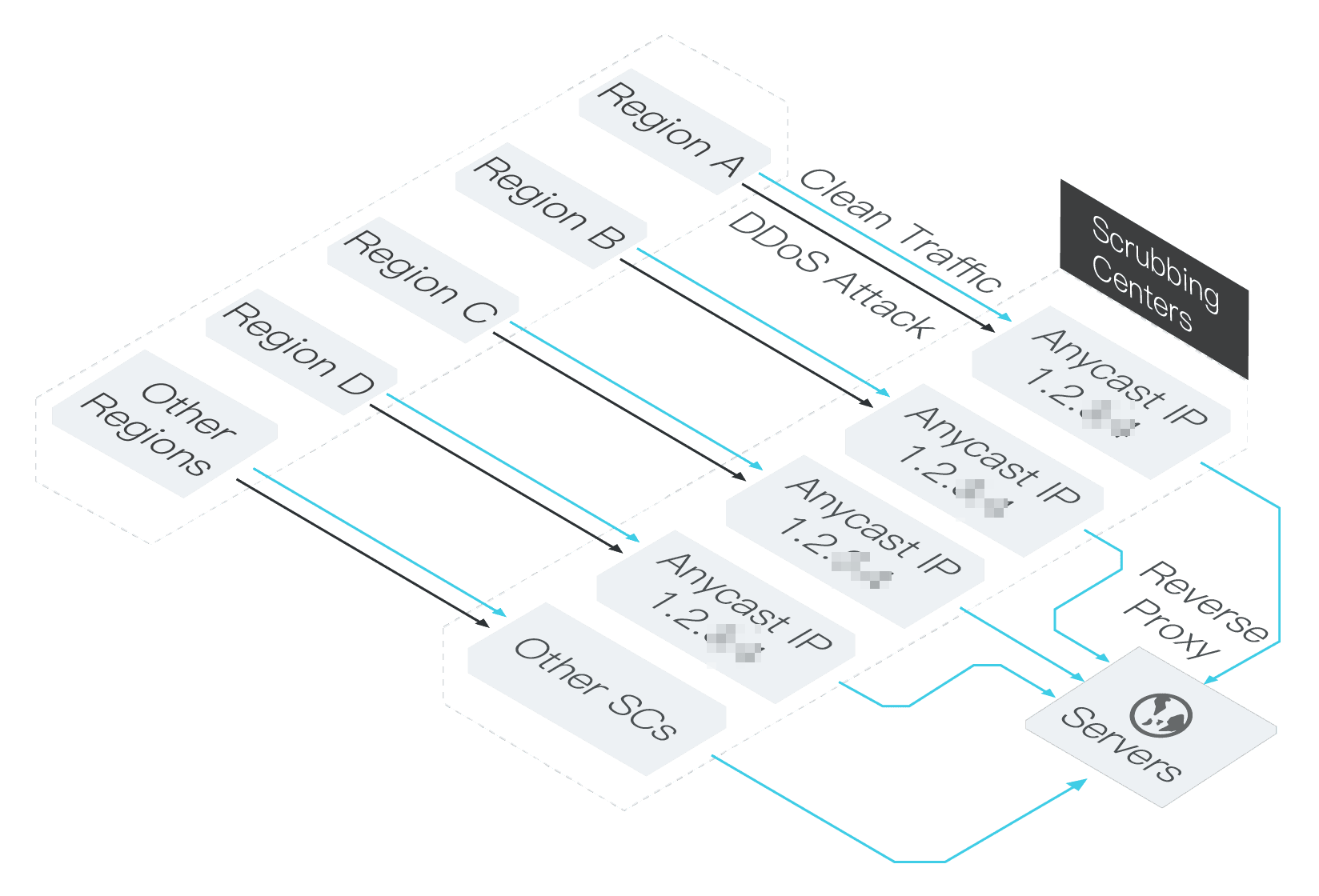
How anycast routing works
When traffic arrives at an anycast IP address, it is routed to the data center with the shortest path (fewest route hops). If a node becomes unavailable, it stops advertising its route immediately, and traffic is automatically rerouted to the next nearest available node.
By default, traffic from users in Hong Kong (China) is routed to the Alibaba Cloud Anti-DDoS scrubbing center in China (Hong Kong).
Access point regions
Anti-DDoS Premium (outside the Chinese mainland) has scrubbing centers in the following countries and regions:
| Area | Regions |
|---|---|
| Asia Pacific | China (Hong Kong), Singapore, Japan, Malaysia, Indonesia |
| North America | US (Silicon Valley), US (Virginia) |
| Europe | UK (London), Germany (Frankfurt) |