To ensure service continuity and mitigate potential security risks from certificate leakage or key cracking, we recommend that you promptly renew the etcd certificates for the master nodes in your ACK dedicated clusters when you receive system notifications. This topic describes how to renew etcd certificates for the master nodes in an ACK dedicated cluster.
Background information
You can migrate workloads from an ACK dedicated cluster to an ACK managed Pro cluster. You can choose to migrate the cluster to an ACK managed Pro cluster. The etcd and Kubernetes control plane certificates of an ACK managed Pro cluster are managed by Alibaba Cloud. After you migrate an ACK dedicated cluster, you do not need to perform the following renewal operations. For more information about how to perform the migration, see Hot migrate ACK dedicated clusters to ACK managed Pro clusters.
Usage notes
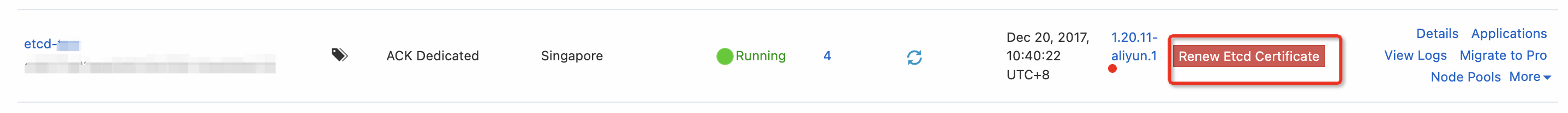
Container Service for Kubernetes (ACK) sends you internal messages and text message reminders two months before the etcd certificates expire, and displays the Renew Etcd Certificate button on the Clusters page.
During the renewal process, control plane components on the cluster's master nodes, such as the API Server, etcd, kube-controller-manager, and kubelet, are restarted one by one. Persistent connections to the API Server are interrupted during this period. We recommend that you perform this operation during off-peak hours. The renewal process takes approximately 30 minutes to complete.
If you have modified the default configuration file directory of etcd or Kubernetes in the ACK dedicated cluster, you must create a symbolic link to the original directory before you renew the certificates. Otherwise, the renewal fails.
If you manually renew the certificates and the Update ETCD Certificate expiration reminder is still displayed in the ACK console, you can submit a ticket to have the reminder removed.
If the renewal process fails, submit a ticket for assistance.
Scenario 1: Renew etcd certificates that are not expired
When the etcd certificates are about to expire and a reminder is displayed, you can renew the certificates using one of the following methods.
Use the console to automatically renew etcd certificates
Log on to the ACK console. In the navigation pane on the left, click Clusters.
Click Update ETCD Certificate next to the cluster whose etcd certificates are about to expire. On the Update Certificate page, click Update Certificate.
NoteIf the etcd certificates of a cluster are due to expire within two months, the Update ETCD Certificate button is displayed next to the cluster.
In the Note dialog box, click OK.
After the certificates are renewed, the following changes occur:
On the Update Certificate page, a message that reads Updated Successfully is displayed.
On the Clusters page, the Update ETCD Certificate button is no longer displayed next to the cluster.
Manually renew etcd certificates
Scenarios
The etcd certificates in an ACK dedicated cluster are about to expire.
The etcd certificates cannot be automatically renewed by deploying a template.
The etcd certificates cannot be renewed in the console.
In these scenarios, a cluster administrator can log on to any master node and run the following script to manually renew the etcd certificates.
The following script must be run as the root user.
Make sure that password-free logon between master nodes is configured for the root user.
Use Secure Shell (SSH) to log on to another master node from a master node. If you are prompted to enter a password, you must configure password-free logon between master nodes.
# 1. Generate a key. If a logon key already exists on your node, you can skip this step. ssh-keygen -t rsa # 2. Use the ssh-copy-id tool to transfer the public key to all other master nodes. $(internal-ip) is the internal IP address of another master node. ssh-copy-id -i ~/.ssh/id_rsa.pub $(internal-ip)NoteIf you do not configure password-free logon, you must enter the root password when you run the script.
Copy the following scripts, save them as restart-apiserver.sh and rotate-etcd.sh, and then save the two files in the same folder.
NoteThe rotate-etcd.sh script attempts to retrieve the region information by accessing the node's metadata service and pulls the rotation image from the nearest location in that region. You can also run the script with the
--region xxxxparameter to specify the region.On any master node, run
bash rotate-etcd.sh.If the command output is
etcd CA and certs have successfully rotated!, the certificates on all master nodes and the Kubernetes certificates are successfully renewed.Verify that the certificates are renewed.
cd /var/lib/etcd/cert for i in `ls | grep pem| grep -v key`;do openssl x509 -noout -text -in $i | grep -i after && echo "$i" ;done cd /etc/kubernetes/pki/etcd for i in `ls | grep pem| grep -v key`;do openssl x509 -noout -text -in $i | grep -i after && echo "$i" ;done cd /etc/kubernetes/pki/ for i in `ls | grep crt| grep -v key`;do openssl x509 -noout -text -in $i | grep -i after && echo "$i" ;doneNoteIf the expiration date in the output of the preceding script is 50 years in the future, the renewal is complete.
After you manually renew the certificates, the update button may still be displayed for the cluster in the console because the ACK console cannot retrieve the renewal result. You can submit a ticket to have the button removed.
Scenario 2: Renew etcd certificates that have expired
Scenarios
The etcd certificates have expired.
If the API Server is inaccessible, you can rotate etcd certificates.
The etcd certificates cannot be automatically renewed by deploying a template.
The etcd certificates cannot be renewed in the console.
In these scenarios, a cluster administrator can log on to any master node and run the following script to manually renew the etcd certificates.
The following script must be run as the root user.
Make sure that password-free logon between master nodes is configured for the root user.
Use Secure Shell (SSH) to log on to another master node from a master node. If you are prompted to enter a password, you must configure password-free logon between master nodes.
# 1. Generate a key. If a logon key already exists on your node, you can skip this step. ssh-keygen -t rsa # 2. Use the ssh-copy-id tool to transfer the public key to all other master nodes. $(internal-ip) is the internal IP address of another master node. ssh-copy-id -i ~/.ssh/id_rsa.pub $(internal-ip)NoteIf you do not configure password-free logon, you must enter the root password when you run the script.
Copy the following scripts, save them as restart-apiserver.sh and rotate-etcd.sh, and then save the two files in the same folder.
NoteThe rotate-etcd.sh script attempts to retrieve the region information by accessing the node's metadata service and pulls the rotation image from the nearest location in that region. You can also run the script with the
--region xxxxparameter to specify the region.
Verify that the certificates are renewed.
cd /var/lib/etcd/cert
for i in `ls | grep pem| grep -v key`;do openssl x509 -noout -text -in $i | grep -i after && echo "$i" ;done
cd /etc/kubernetes/pki/etcd
for i in `ls | grep pem| grep -v key`;do openssl x509 -noout -text -in $i | grep -i after && echo "$i" ;done
cd /etc/kubernetes/pki/
for i in `ls | grep crt| grep -v key`;do openssl x509 -noout -text -in $i | grep -i after && echo "$i" ;doneIf the expiration date in the output of the preceding script is 50 years in the future, the renewal is complete.
After you manually renew the certificates, the expired status may still be displayed for the cluster in the console because the ACK console cannot retrieve the renewal result. You can submit a ticket to have the status removed.
Roll back when certificate renewal fails
Scenarios
Certificate renewal from the console fails.
Certificate renewal from the command line fails.
In these scenarios, a cluster administrator can log on to any master node and run the following script to roll back the changes. This operation restores the cluster to a functional state by generating a new set of etcd certificates and updating the etcd server certificate and the kube-apiserver client certificate.
The following script must be run as the root user.
Make sure that password-free logon between master nodes is configured for the root user.
Use Secure Shell (SSH) to log on to another master node from a master node. If you are prompted to enter a password, you must configure password-free logon between master nodes.
# 1. Generate a key. If a logon key already exists on your node, you can skip this step. ssh-keygen -t rsa # 2. Use the ssh-copy-id tool to transfer the public key to all other master nodes. $(internal-ip) is the internal IP address of another master node. ssh-copy-id -i ~/.ssh/id_rsa.pub $(internal-ip)NoteIf you do not configure password-free logon, you must enter the root password when you run the script.
Copy the following scripts, save them as restart-apiserver.sh and rollback-etcd.sh, and then save the two files in the same folder
NoteThe rollback-etcd.sh script attempts to retrieve the region information by accessing the node's metadata service and pulls the rotation image from the nearest location in that region. You can also run the script with the
--region xxxxparameter to specify the region.On any master node, run
bash rollback-etcd.sh.If the command output is
etcd CA and certs have successfully rotated!, the certificates on all master nodes and the Kubernetes certificates are successfully renewed.Verify that the certificates are renewed.
cd /var/lib/etcd/cert
for i in `ls | grep pem| grep -v key`;do openssl x509 -noout -text -in $i | grep -i after && echo "$i" ;done
cd /etc/kubernetes/pki/etcd
for i in `ls | grep pem| grep -v key`;do openssl x509 -noout -text -in $i | grep -i after && echo "$i" ;done
cd /etc/kubernetes/pki/
for i in `ls | grep crt| grep -v key`;do openssl x509 -noout -text -in $i | grep -i after && echo "$i" ;doneThe rotation is complete if the time returned by the preceding script is more than 50 years in the future.