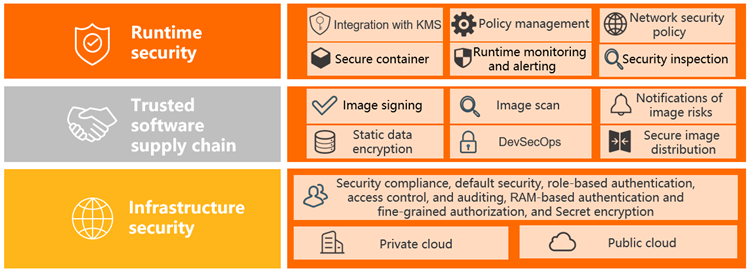
ACK secures containerized workloads across three layers: runtime security, trusted software supply chain, and infrastructure security.
Shared responsibility
ACK manages the security of the control plane — including the Kubernetes API server, etcd, and system component certificates. You are responsible for securing your workloads, images, and access configurations.
| Layer | ACK manages | You configure |
|---|---|---|
| Control plane | TLS certificate renewal, API server hardening, system component certificates | — |
| Nodes | Security group defaults, NAT Gateway routing, OS hardening | SSH access, RAM role permissions |
| Workloads | — | Pod security policies, RBAC, runtime monitoring |
| Images | — | Image scanning, signing, delivery chain policies |
Runtime security
Security inspection
ACK scans running workload configurations in real time to detect violations of the principle of least privilege — the most common entry point for container escape attacks.
Inspection results are written to a specified Simple Log Service (SLS) Logstore and displayed as reports with per-item descriptions and fix suggestions. Schedule periodic inspections to maintain ongoing visibility. For details, see Use configuration inspection to check for security risks in cluster workloads.
Policy management
ACK integrates Gatekeeper, an admission controller built on Open Policy Agent (OPA), to block non-compliant workloads at deploy time — before they reach your cluster.
Key capabilities:
-
A built-in library of Kubernetes-specific policy rules, covering common security scenarios out of the box
-
Visual policy configuration in the ACK console, no OPA policy language required
-
Policy governance status statistics and log reporting and retrieval for audit trails
For details, see Configure container security policies (new).
Runtime monitoring and alerting
Passing admission control is not enough — the zero trust security model requires continuous monitoring throughout an application's lifetime. ACK integrates with Security Center to detect threats at the container level.
Threats detected:
-
Malicious image startups
-
Viruses and malicious programs
-
Internal container intrusions
-
Container escapes and high-risk operations
View and handle alerts on the Security > Security Monitoring page of your cluster management page. For details, see Use security monitoring.
Isolation models
When workload isolation requirements go beyond standard Kubernetes Pod security, ACK offers two stronger options:
| Scenario | Solution | How it works |
|---|---|---|
| Untrusted workloads, fault isolation, multi-tenant isolation | Sandboxed containers | Runs each container in a lightweight VM with an independent kernel. Provides stronger security isolation with minimal performance overhead and the same logging, monitoring, and elasticity experience as standard containers. |
| Finance, government, and other high-compliance workloads | ACK-TEE confidential computing | Places code and data in a hardware-backed Trusted Execution Environment (TEE). Prevents access from other applications, the OS, kernel, BIOS, administrators, O&M engineers, cloud vendors, and hardware other than the CPU — only the CPU can access the data. |
-
For sandboxed containers, see Sandboxed Container.
-
For ACK-TEE, see ACK-TEE confidential computing.
Trusted software supply chain
Security is enforced at every stage of the delivery pipeline — from build to registry to cluster.
Build: image scanning
Container Registry scans all Linux-based container images for known vulnerabilities, providing severity assessments and fix suggestions. The scan engine, powered by Security Center, also detects system vulnerabilities, application vulnerabilities, and malicious samples embedded in images.
Registry: image signing
Use image signing to guarantee that only images from trusted sources are deployed in your cluster. The image creator signs the image digitally; the signature is stored in Container Registry. At deploy time, ACK verifies the signature before allowing the container to run — preventing tampered or unexpected images from entering your environment.
For setup instructions, see Use the kritis-validation-hook component to automatically verify container image signatures.
Deploy: cloud-native application delivery chain
The delivery chain feature in Container Registry lets you define a fully automated, end-to-end secure pipeline. Configure tasks such as image building, image scanning, global image synchronization, and image deployment — with fine-grained security policies at each stage.
A single code commit triggers secure distribution and deployment across multiple regions worldwide, upgrading your delivery process from DevOps to DevSecOps. For setup instructions, see Create a delivery chain.
Infrastructure security
Default security
Every new ACK cluster is hardened at creation time:
-
Node and control plane hardening: Configurations follow Alibaba Cloud Kubernetes security hardening standards. All system component images are free of critical-level CVE vulnerabilities.
-
Network isolation: Each cluster gets a dedicated security group that allows only inbound ICMP from the Internet. SSH access to cluster nodes over the Internet is disabled by default. Nodes access the public network through NAT Gateway.
-
Least-privilege node roles: RAM roles attached to worker nodes in managed clusters have the minimum permissions required. For details, see \[Product Change\] Announcement on the convergence of RAM role permissions for managed cluster nodes.
To enable SSH access to cluster nodes when needed, see Connect to the master nodes of an ACK dedicated cluster using SSH.
Identity management
All communication between cluster components is protected by TLS, with automatic certificate renewal handled by the ACK control plane.
RAM users and RAM role users can get a kubeconfig credential via the console or OpenAPI to connect to a cluster's API server. ACK tracks identity information in issued credentials — if a kubeconfig is compromised, revoke it immediately.
ACK also supports Service Account Token Volume Projection to harden ServiceAccount security in applications. For details, see Deploy service account token volume projection.
Fine-grained access control
ACK implements Role-Based Access Control (RBAC) at the namespace level, configurable from the Authorization management page in the ACK console.
Key features:
-
Predefined role templates: Built-in RBAC templates for administrator, O&M engineer, and developer roles reduce the effort of setting up permission structures from scratch.
-
Batch authorization: Authorize multiple RAM users across multiple clusters in a single operation.
-
RAM role support: Grant access to users who assume a RAM role.
-
Custom ClusterRoles: Bind any ClusterRole defined in the cluster to a user.
For details, see Configure RBAC roles for a RAM user or RAM role.
For policy-based access control, install the Gatekeeper component through component management to apply Open Policy Agent (OPA) rules cluster-wide. For details, see Gatekeeper.
Auditing
ACK integrates with Simple Log Service to collect, query, and visualize three types of audit logs:
| Log type | What it covers | Where to view |
|---|---|---|
| Cluster API server audit logs | Records all operations on cluster resources — essential for tracing access and detecting unauthorized activity. Supports real-time alerts on specified resource types. | Cluster Auditing page |
| Ingress traffic audit | Monitors service access PV and UV, success and failure ratios, and latency across all cluster Ingresses. Uses machine learning algorithms from Simple Log Service to detect anomalies automatically. | Configured via log analysis |
| Event monitoring audit | Captures Kubernetes events to diagnose cluster anomalies and security risks in real time. | Event monitoring dashboard |
References:
Secret encryption at rest
Kubernetes Secrets are Base64-encoded by default in etcd — not encrypted. In ACK Pro clusters, use Key Management Service (KMS) keys to encrypt Secrets at rest, protecting sensitive application data stored in etcd.
For details, see Use Alibaba Cloud KMS to encrypt Secrets at rest.