One common category of DDoS attack is a SMS flooding attack. An SMS flooding attack occurs when a high volume of cellular SMS messages are sent to saturate and overload the website’s server.
Business is taking off. You are hiring new people, expanding your customer base and you have just bought a new work van to handle the recent spike in orders.
Purchasing the vehicle is a significant investment for your business, including the extra expenditure to brand the vehicle with your company logo.
But all week you’re beaming with delight at the sight of your company’s new vehicle; which doubles as a portable billboard for your company.
However, four days in you wake up to a nasty surprise. Overnight a local graffiti gang has vandalized and tagged the van in three different colors. The news only gets worst when you spot a crude artistic attempt to depict the male genitalia next to your logo. Having just spent a small fortune (from the company’s point of view) to invest in the new vehicle, this was the last thing you needed!
The cyber world is no different when it comes to malicious operators damaging company assets.
Distributed Denial of Service (DDoS) is one particular attack you want to avoid as a law-abiding netizen. DDoS attacks come in various shapes and sizes, and one common category of DDoS attack is a SMS flooding attack. An SMS flooding attack occurs when a high volume of cellular SMS messages are sent to saturate and overload the website’s server.
This leads to slow website server performance, soaring SMS registration verification charges and leaking of customer contact information.
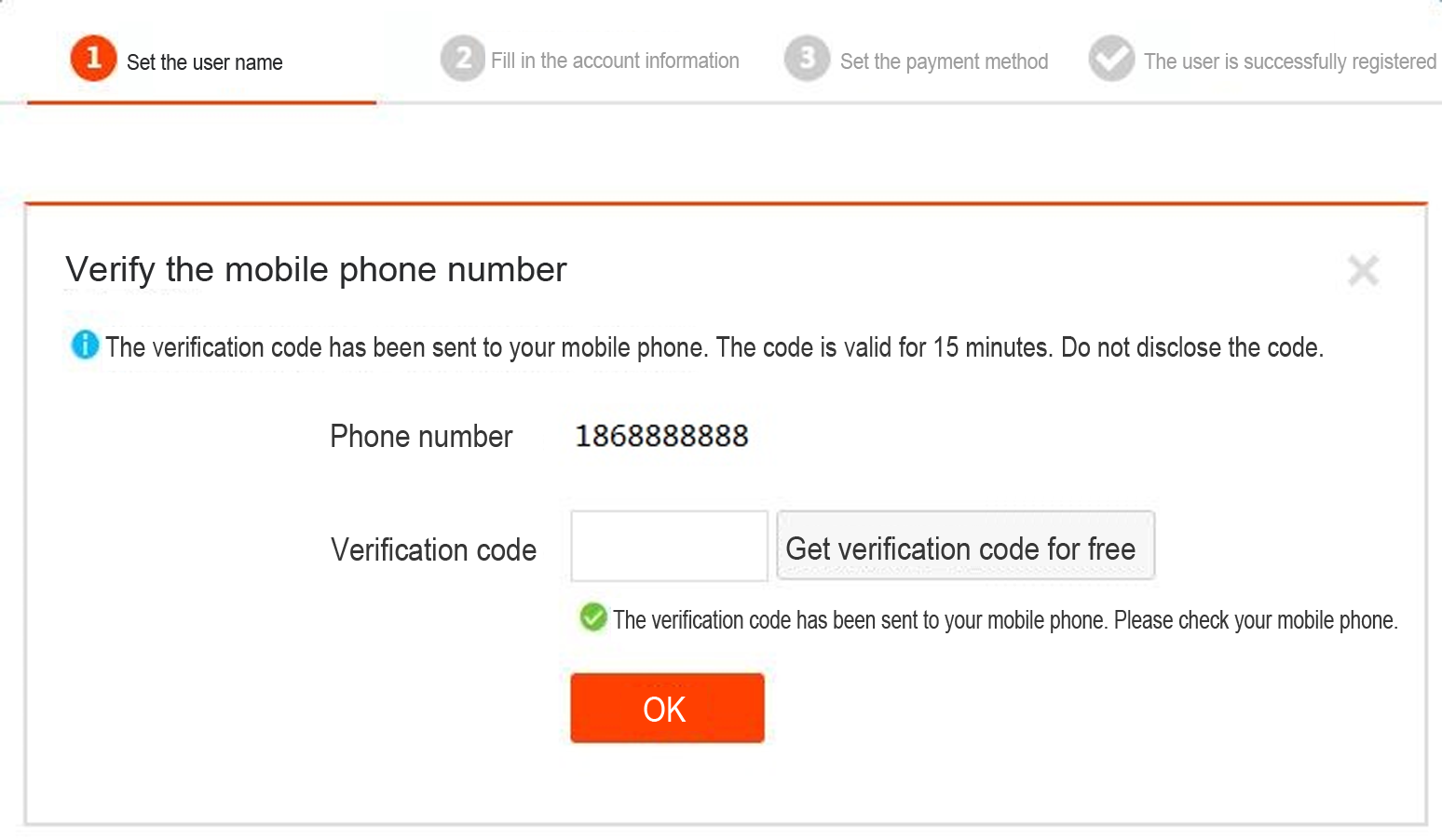
For many websites, online users must provide their mobile phone number upon registration in order to validate their identity. Normally, users will click a button during the registration process to send a SMS message and a SMS message is sent to verify the user’s mobile phone number. However, if there are no defense policies protecting the SMS interface, attackers can leverage programs to send high frequency requests to the SMS interface.
Screenshot of online sign up form with SMS verification
Alibaba Dpath, a traffic isolation solution, is developed to provide support for new retail scenarios during the Double 11 Shopping Festival.
During this year's Double Eleven Shopping Festival, technical preparations had to be changed from previous years to support New Retail. The Business Division required that traffic from new retail will enter independent servers and be isolated from other common traffic. Although conceptually straightforward, this poses higher requirements on the stability of new retail systems.
We have proposed a solution known as Dpath (dedicated path) to cope with these new requirements. The general idea of Dpath can be described as follows:
We'll introduce how Dpath works in three steps:
Simply put, the information we need is the machines, apps, and the relation between them in a dedicated environment. Such information is stored in the configuration center in JSON format. A sample are as follows:
{
"enable": true,
"envRules": [
{
"envName": "newRetail",
"failoverPolicy": 0,
"envAppRules": [
{
"appName": "app1",
"ips": [ ],
"machineGroups": [
"app1_newRetail_host"
]
},
{
"appName": "app2",
"ips": [ ],
"machineGroups": [
"app2_newRetail_host"
]
},
{
"appName": "app3",
"ips": [ ],
"machineGroups": [
"app3_newRetail_host"
]
},
{
"appName": "newRetailEntryApp",
"ips": [ ],
"machineGroups": [
"newRetailEntryApp_host"
]
}
]
}
]
} This document introduces how to replicate application traffic between different Kubernetes clusters of Container Service.
Generally, when a system is reconstructed or new features are released, we need to run stress tests to evaluate the carrying capacity of the new system in advance. Traditionally, we simulate all kinds of online test data in an offline environment to test the new system. However, this method may not effectively simulate the actual access traffic online, particularly various kinds of abnormal traffic in the simulated normal traffic.
In this case, we can replicate the online application traffic to a specified offline environment to run a simulation test on the new system. In another case, if our online system encounters a performance bottleneck, but we cannot quickly locate the problem, we can also use the traffic replication method to replicate the real application traffic to an offline environment to locate the problem.
Let's see how to replicate application traffic between different Kubernetes clusters of Container Service.
Assume that you have applied for two different Kubernetes clusters on the Container Service console. We name them Kubernetes Product Cluster and Kubernetes Stage Cluster.
# Check the Ingress configuration of the application.
kubectl get ing nginx-ingress
NAME HOSTS ADDRESS PORTS AGE
nginx-ingress nginx.c37bf6b77bded43669ba2fb67448b4146.cn-hangzhou.alicontainer.com 47.110.199.44 80 8m
# Test the domain name for accessing the application.
curl http://nginx.c37bf6b77bded43669ba2fb67448b4146.cn-hangzhou.alicontainer.com
old
# Check the Ingress configuration of the application.
kubectl get ing nginx-ingress
NAME HOSTS ADDRESS PORTS AGE
nginx-ingress nginx.c41eb6ca34a3e49f7aea63b8bc9e8ad98.cn-beijing.alicontainer.com 39.106.233.1 80 1m
# Test the domain name for accessing the application.
curl http://nginx.c41eb6ca34a3e49f7aea63b8bc9e8ad98.cn-beijing.alicontainer.com
newAssume that we hope to replicate all access traffic (100%) of the application in the Kubernetes Product Cluster to the corresponding application in the Kubernetes Stage Cluster. That is, we need to replicate and forward all requests for the domain name nginx.c37bf6b77bded43669ba2fb67448b4146.cn-hangzhou.alicontainer.com to the domain name nginx.c41eb6ca34a3e49f7aea63b8bc9e8ad98.cn-beijing.alicontainer.com.
Discover how Alibaba Cloud assisted Jinhua, a city in Zhejiang province of China, to combat floods using artificial intelligence with ET Environment Brain.
In August 2018, many regions in the northern hemisphere of China were hit by floods, which caused agricultural damage and affected the lives of millions of Chinese citizens. Desperate for a solution, Jinhua, a city in Zhejiang province of China, started tackling this issue by using artificial intelligence (AI) for flood control.
The flood and drought control command center of Jinhua city uses Alibaba Cloud ET Environment Brain to analyze water resources and weather data in the city, which helps to improve the decision-making efficiency during the flood season. According to statistical data, AI provides a much higher speed and accuracy than traditional methods in predicting extreme weather such as heavy rain and typhoon. Through these predictive analyses, cities can then proactively respond to adverse weather, saving precious time on decision-making and logistics for flood control and rescue missions.
As Jinhua is located in a basin-and-hill area in the central part of Zhejiang, this city is subject to small watershed mountain torrents due to the unique terrain. The city often encounters heavy rainfall and floods during the "plum rain" season from May to June every year. Whereas from July to September, Jinhua may suffer from droughts due to the shortage of rainfall, or even unexpected storms brought by typhoons.
Zhu Shenghuo, chief scientist of decision intelligence in Alibaba machine intelligence lab, gives an introduction to the technology: "Based on data of Jinhua flood and drought control command center, the AI algorithm analyzes the real-time high water mark and weather in comparison with historical high water marks and weather in flood periods, to figure out the relations between high water marks of rivers and reservoirs.In addition, AI can predict the flood control conditions of rivers and reservoirs. "
In the past, most flood predictions are made based purely on experience, historical data, and knowledge of professional flood control personnel. However, the growth in Internet of Things (IoT) technology led to the explosive growth of hydrological and meteorological data. Traditional flood control models are unable to process the massive amounts of data because these methods are labor intensive, slow, and have limited computing power. Modern day AI systems such as ET Environment Brain help to address these challenges, allowing cities to make better-informed decisions through accurate predictions.
In the future, the flood control system of Jinhua can not only predict the high water marks and trends of floods, but also assess the economical and sociological effect brought by the floods. This can help Jinhua to make more effective search and rescue plans, and enable automatic dispatching of relief resources and evacuation plans.
Jinhua has started IT-based flood control since as early as 2002. The city has collected a large amount of data about water flow, rain, and disasters, and established multiple database systems, including the real-time water flow database, meteorological database, and historical water flow database. All these lay a solid foundation for data analysis.
In this article, we will show you how to mirror traffic from production with Istio and use Diffy to compare traffic with your test environment.
Traffic mirroring, also known as traffic shadowing, provides a powerful way to bring changes to production at the lowest possible risk. The mirror sends a copy of real-time traffic to the mirroring service. Mirrored traffic goes outside of the critical request path of the main services.
In non-production or test environments, trying to access all possible combinations of test cases for a service is unrealistic. In some cases, the work of writing these test cases may not match actual production needs. In the ideal case, you can use real-time production use and traffic to help improve the functional regions you miss in the test environment.
Once we are able to reliably mirror traffic, we can start other valuable tasks. For example, using Diffy, a request traffic comparison tool, we can compare the traffic of the introduced test cluster to the expected behavior of the production cluster. For example, we might want to compare the deviation between the request results and the expected results, or data corruption in the API Protocol, for better compatibility.
In addition, please note:
Here, by inserting a proxy, you can be responsible for the coordination of such traffic, and it makes an interesting comparison. Diffy is such a proxy tool. Diffy starts a proxy service (listening, for example, on port 8880 ), again, based on the primary and secondary old service addresses set by the user, (the primary and secondary codes are identical and the purpose is to reduce noise interference) and a new candidate service address.
It can also detect noise in the result, and ignore instances of two real-time services by first calling them (for example, timestamps, monotonically increasing counter and other prompts). In summary, it detects and then ignores these parts in the test service.
Diffy also provides a very good page to view the results of the call, and compare the conditions, which can be filtered by particular characteristics It also has a good management console where you can view the metrics and statistics of the comparing call results function.
In this task, you first force all traffic to the v1 version of the service. You will then use a rule to mirror a portion of the traffic to the v2 version.
Two versions of the sample service are first deployed.
Docker mirroring httpbin is used to provide common http access requests in the deployment of version 1:
apiVersion: extensions/v1beta1
kind: Deployment
metadata:
name: mirrorservice-sample-v1
spec:
replicas: 1
template:
metadata:
labels:
app: mirrorservice-sample
version: v1
spec:
containers:
- image: docker.io/kennethreitz/httpbin
imagePullPolicy: IfNotPresent
name: mirrorservice-sample
command: ["gunicorn", "--access-logfile", "-", "-b", "0.0.0.0:44134", "httpbin:app"]
ports:
- containerPort: 8114 In the case of large traffic, often result in slow response to the web server or even stop the service. The key of load balancing lies in "sharing". When large traffic comes, the traffic is distributed to multiple servers to improve the external service capability of the website and avoid the impact of a single point of failure on the website in order to improve the availability of the website. Through this online course, you can understand the concept of load balancing, principles and scenarios, and master Alibaba Cloud Server Load Balancer features and usage.
This online course mainly helps you to understand and master the main security risks WEB applications are facing in the cloud, as well as a variety of risk defense solutions and principles. We also introduce you the best protection solutions provided by Alibaba Cloud. With this certification, you can prove that you have the ability to protect Internet application security well in Alibaba Cloud.
Alibaba Cloud WAF is a web application firewall that monitors, filters, and blocks HTTP traffic to and from web applications. Based on the big data capacity of Alibaba Cloud Security, Alibaba Cloud WAF helps to defend against common web attacks such as SQL injections, Cross-site scripting (XSS), web shell, Trojan, and unauthorized access, and to filter out massive HTTP flood requests. It protects web resources from being exposed and guarantees website security and availability.
Increased traffic, often results in a delayed response from web servers or even a halt in service. Load balancing lies in "sharing." When massive traffic is detected, the traffic is distributed to multiple servers to improve the external service capability of the website and avoid the impact of a single point failure.
F5's BIG-IP Virtual Edition delivers advanced application acceleration, access, security and traffic management services; ensuring your Alibaba Cloud workloads are fast, available and secure.
Why is the actual billed network traffic different from the network traffic reported by the logging feature?
The network traffic reported by the logging feature reflects only the network traffic generated at the application layer. The network traffic that occurs at the network layer is 7% to 15% more than the reported network traffic. The extra network traffic may occur because of the following reasons:
Simple Application Server offers free monthly traffic packages. A traffic package is dedicated to a single instance. In most cases, the quota of a traffic package can meet data transmission requirements. A traffic package is reset on the first day of each month. After the traffic package is reset, the amount of used traffic will start from zero.
Note: Notifications will be sent to customers when the amount of traffic used in a package exceeds 50%, 80%, and 95%.
A comprehensive DDoS protection for enterprise to intelligently defend sophisticated DDoS attacks, reduce business loss risks, and mitigate potential security threats.
Web Application Firewall (WAF) protects your website servers against intrusions. Our service detects and blocks malicious traffic directed to your websites and applications. WAF secures your core business data and prevents server malfunctions caused by malicious activities and attacks.
Who Comes Next After the Rise of Data Warehouses and Data Lakes?

2,593 posts | 794 followers
FollowAlibaba Clouder - June 28, 2019
Alibaba Clouder - April 8, 2021
Dikky Ryan Pratama - June 13, 2023
Alibaba Clouder - December 23, 2020
Alibaba Clouder - June 12, 2019
Alibaba Clouder - December 2, 2016

2,593 posts | 794 followers
Follow Anti DDoS Basic
Anti DDoS Basic
A cloud-based security service that protects your data and application from DDoS attacks
Learn More Cloud Firewall
Cloud Firewall
Provides traffic control and security protection for the Internet, virtual private cloud (VPCs), and hosts in VPCs
Learn MoreMore Posts by Alibaba Clouder