According to the 2018 In-cloud Mining Analysis Report released by the Alibaba Cloud security team, each round of popular 0-day attacks was accompanied by the outbreak of cryptocurrency mining worms. Cryptocurrency mining worms may interrupt businesses by occupying system resources. Some of them even carry ransomware (such as XBash), resulting in financial and data losses to enterprises.
For many enterprises, improving the level of security and protecting against the threat of cryptocurrency mining worms have become a top priority. This article uses an off-premises environment as an example to explain Alibaba Cloud's Cloud Firewall effectively defends against cryptocurrency mining worms through early prevention, Trojan worm detection, and quick damage control.
The Security Team at Alibaba Cloud has discovered recent cloud-native cryptocurrency mining trojans distributed by common popular 0-day and n-day vulnerabilities.
In the past year, cryptocurrency mining worms have exploited common vulnerabilities (such as configuration errors and weak passwords) in network applications to continuously scan the Internet, launch attacks, and compromise hosts. The following table lists common vulnerabilities that have been recently exploited by active cryptocurrency mining worms:
| Common vulnerabilities | Mining worm family |
| SSH, RDP, and Telnet cracking | MyKings and RDPMiner |
| Writing data to Crontab in Redis to run commands | DDG, Watchdogs, Kworkerd, and 8220 |
| Using UDF to run commands in MySQL and SQL Server | Bulehero, MyKings, and ProtonMiner |
| Using CouchDB to run commands | 8220 |
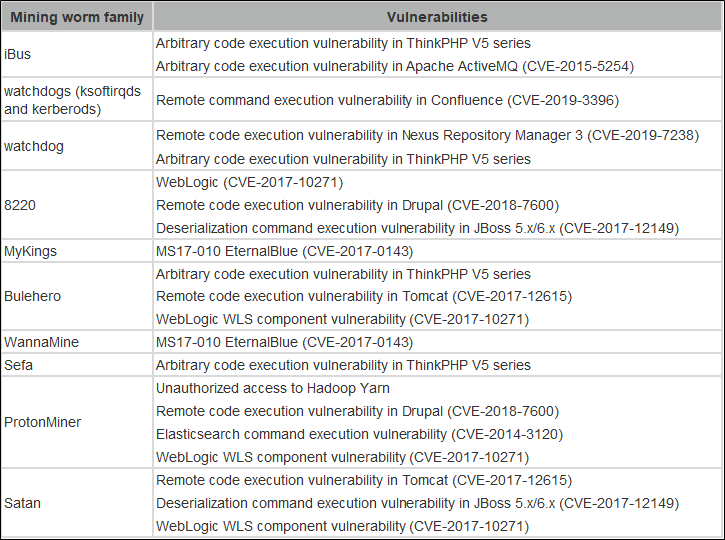
Cryptocurrency mining worms also exploit 0-day and N-day vulnerabilities to compromise a large number of hosts before these vulnerabilities are fixed. The following table lists popular 0-day and N-day vulnerabilities that have been recently exploited by active cryptocurrency mining worms:
Cloud Firewall of Alibaba Cloud is the first SaaS-based firewall product in the industry to defend against these two types of vulnerabilities in the public cloud environment. It can detect and block malicious traffic in and out of the off-premises environment in real time, allowing enterprises to transparently access applications.
Based on the ways cryptocurrency mining worms crack SSH, RDP, and other protocols, Cloud Firewall Basic Protection supports conventional brute-force cracking detection methods. For example, it can count the logon or trial-and-error frequency thresholds and block the IP addresses that exceed the trial-and-error threshold. In addition, it can block abnormal logons based on your access habits and frequencies in combination with behavior models, while ensuring unobstructed normal access.
For some common vulnerabilities, such as writing data to Crontab in Redis to run commands and using UDF to run commands in databases, Cloud Firewall Basic Protection takes the advantage of Alibaba Cloud big data to create precise defense rules from the large number of malicious attack samples accumulated by the Alibaba Cloud security team in off-premises defense.
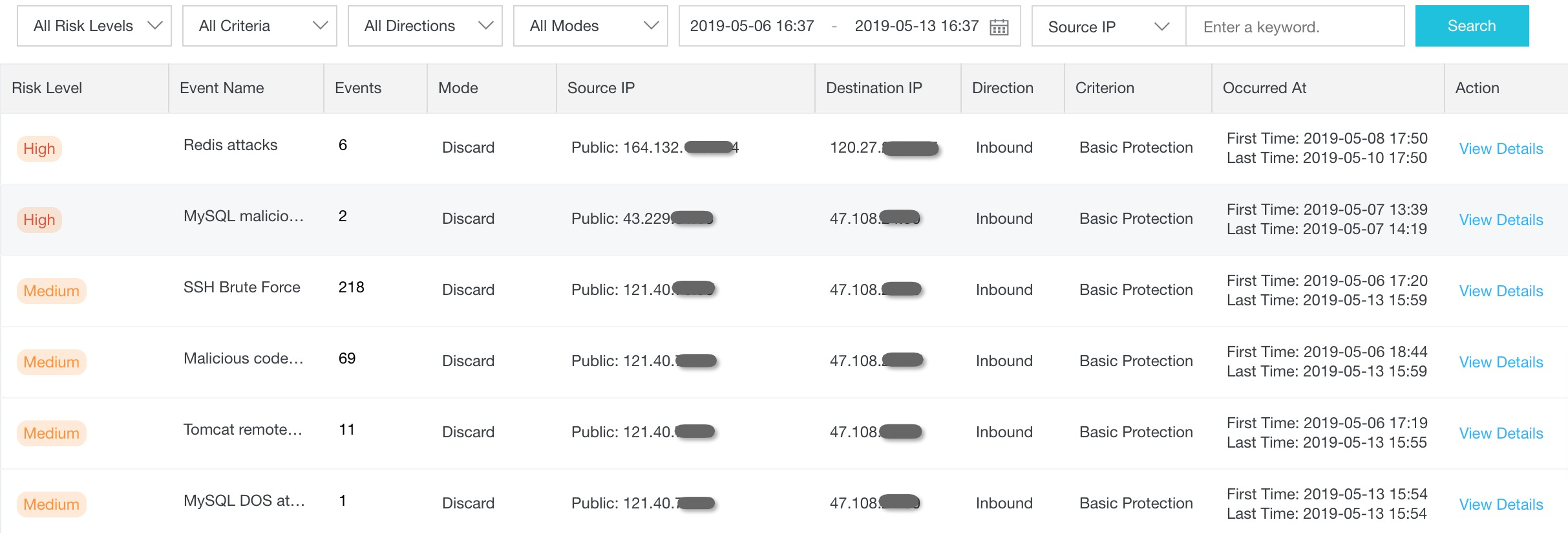
To enable the Cloud Firewall Basic Protection capabilities, choose Security Policies > Intrusion Prevention > Basic Protection and select Basic Policies. Then, choose Traffic Analysis > IPS Analysis to view detailed interception logs. For more information, see the following screenshot:
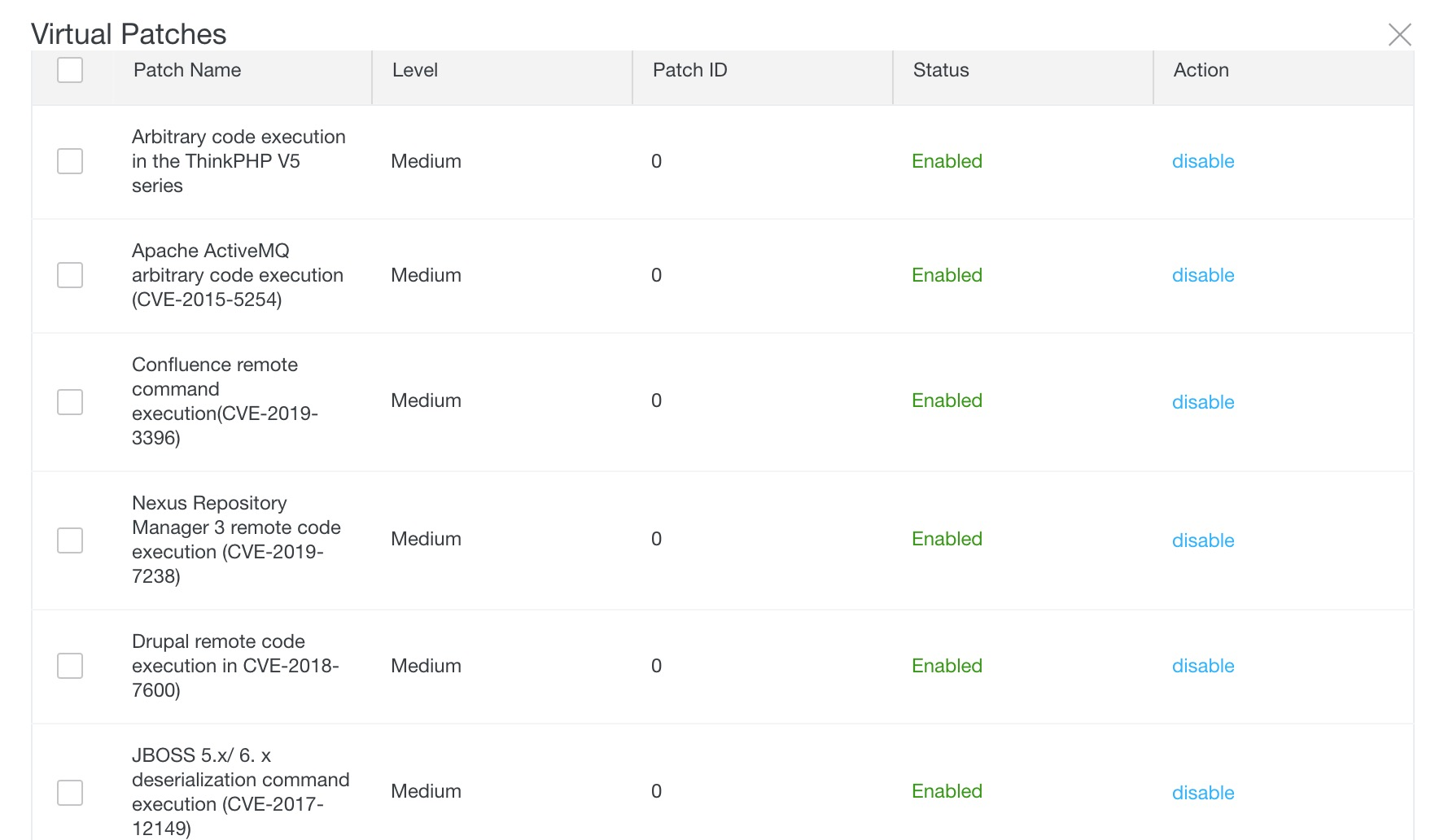
Popular 0-day and N-day vulnerabilities may not be promptly fixed, so hosts are at a high risk of being compromised by cryptocurrency mining worms. Cloud Firewall analyzes abnormal attack traffic with honeypots deployed across the network. It also shares vulnerability intelligence with Alibaba Cloud Crowdsourced Security Testing Platform. In this way, Cloud Firewall can promptly detect the exploitation of 0-day and N-day vulnerabilities, obtain the Poc/Exp of these vulnerabilities, and generate virtual patches in advance.
To protect against high-risk vulnerabilities that are exploited by active cryptocurrency mining worms, choose Security Policies > Intrusion Prevention > Virtual Patches. The following figure shows the virtual patches for 0-day and N-day vulnerabilities that have been recently exploited by active cryptocurrency mining worms.
Even if the public network boundaries are well protected against intrusion, hosts may still be compromised by cryptocurrency mining worms. For example, cryptocurrency mining worms can be directly transmitted from a development machine to the production network over a VPN. Large-scale host intrusion can be caused when system images and docker images that are used for O&M have been implanted with mining viruses.
Therefore, cryptocurrency mining worms must be detected in real time. With the intrusion detection function provided by Network Traffic Analysis (NTA), Cloud Firewall can effectively detect host intrusion events.
With a powerful threat intelligence network, Cloud Firewall can promptly discover the mining pool addresses of common currencies and detect the download behaviors of cryptocurrency mining trojans and the common communication protocols of mining pools. In addition, it can identify and alarm against the mining behaviors of hosts in real time.
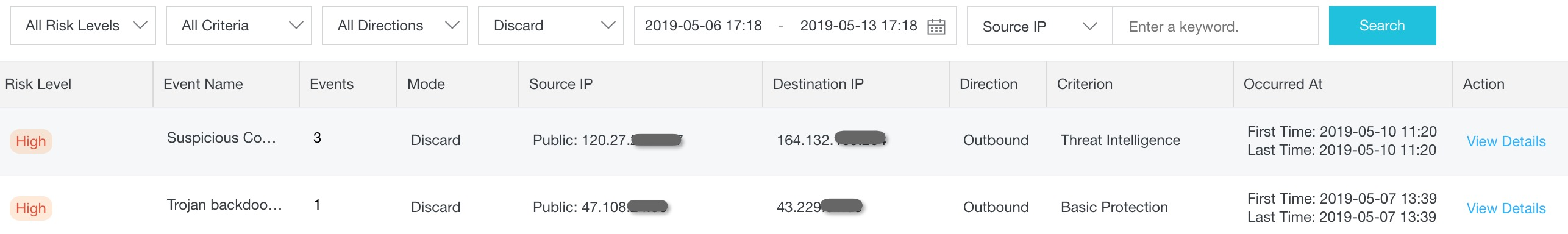
You can choose Traffic Analysis > Intrusion to view the event summary, affected assets, and details of each attack event. To block the communication between cryptocurrency mining trojans and mining pools on the network end, you only need to enable the interception mode in the Block category and submit data with one click.
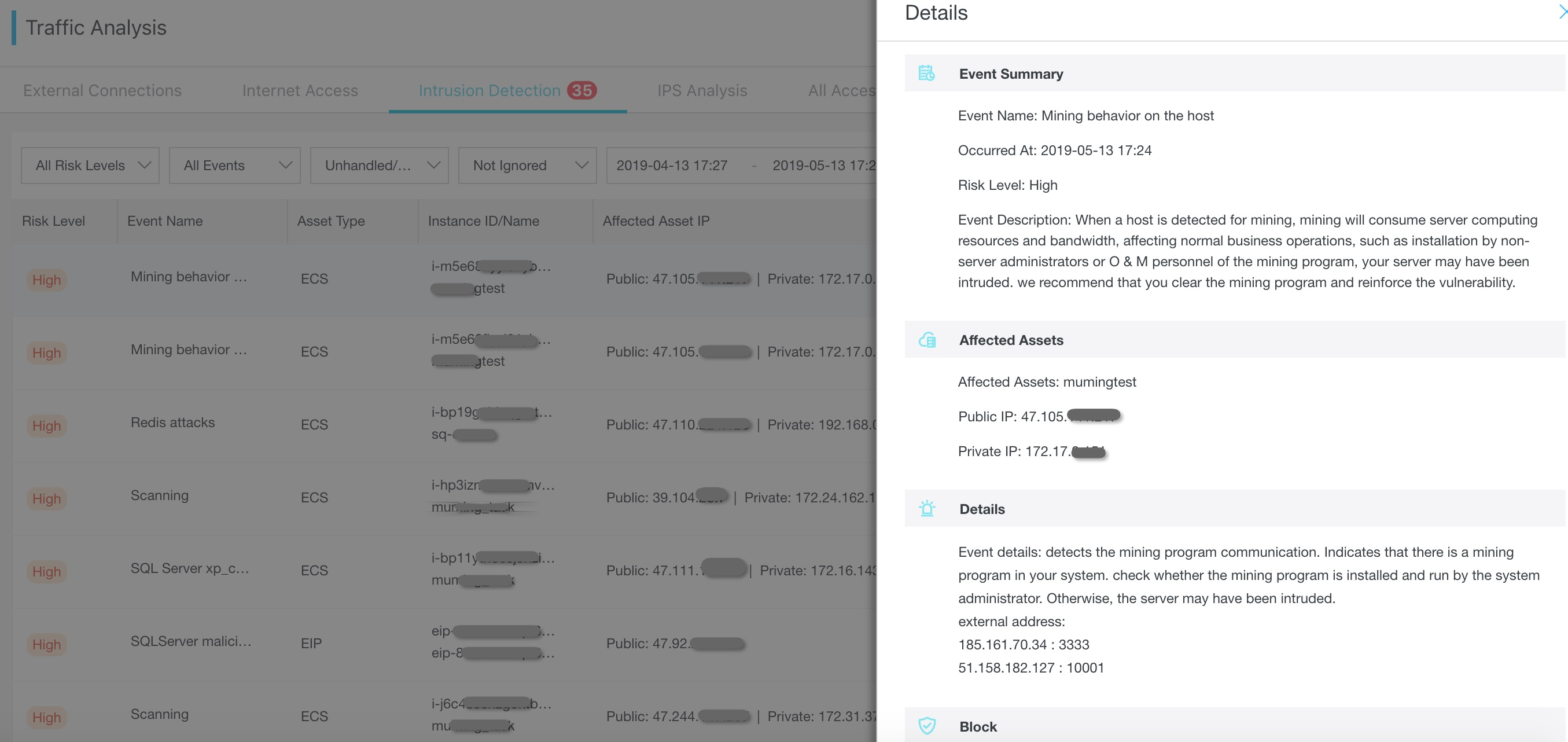
Based on the external address information in the details, you can search for specific processes on their hosts to quickly clear binary programs.
If a server is compromised by cryptocurrency mining worms, Cloud Firewall can further control the distribution of these trojan worms by blocking malicious file downloads, intercepting c&c communication, and enabling enhanced access control in key business areas. This reduces further business and data losses.
Malicious file download blocking is one of the important functions of Basic Protection. Usually, a server will download malicious files after being compromised by cryptocurrency mining worms. With its malicious file detection capability, Basic Protection can detect the security of files downloaded to the server in the traffic, trigger alarms when the server attempts to download a malicious file, and block the download.

Cloud Firewall Basic Protection updates the unique feature codes and fuzzy hashes of various malicious files related to common cryptocurrency mining worms in real time. When cryptocurrency mining worms compromise a server and further download new attack loads, Basic Protection restores the files downloaded to the server and matches them with features in the traffic, triggers alarms when the server attempts to download a malicious file, and blocks the download.
When cryptocurrency mining worms compromise a server, they may communicate with the C&C terminal and receive further malicious behavior instructions or leak sensitive data. In such cases, Cloud Firewall Basic Protection intercepts communication in real time as follows:
The following figure shows the records of C&C communication interceptions through Basic Protection and threat intelligence.
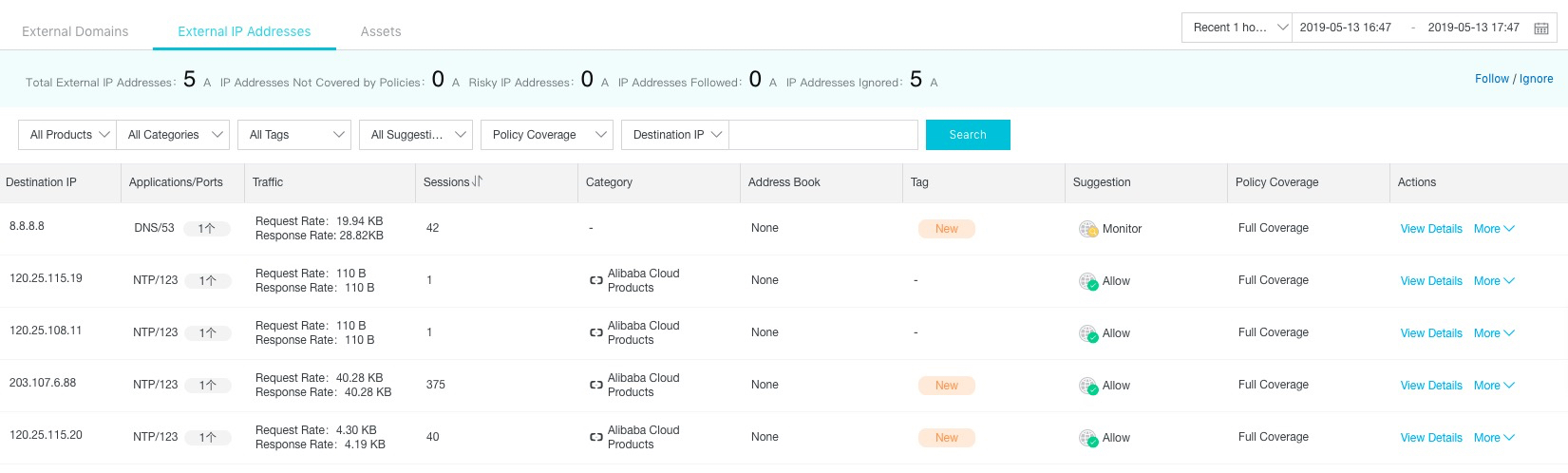
To meet business needs, enterprises usually need to keep key businesses or ports open to the entire public network. However, swarms on the Internet constantly scan and attack enterprises' assets, making fine-grained external access control a great challenge. When an ECS instance, EIP, or internal network is actively accessed, the number of domain names or IP addresses is controllable because such external access is usually legal, such as from DNS and NTP services. Some enterprises only need a few specific IP addresses or domain names. Therefore, by controlling internal and external domain names or IP addresses, enterprises can prevent compromised ECS instances from pulling cryptocurrency mining trojans from malicious domains and can also block the communication between trojans and C&C servers.
Cloud Firewall supports access control as well as domain name (including wildcard domain names) and IP address configuration. For key businesses, enterprises can configure fine-grained internal and external access control, that is, make the ports of key businesses only open to specific domain names or IP addresses. The preceding operations can effectively prevent the download and distribution of cryptocurrency mining worms, and also prevent mining trojan from surviving and profiting after intrusion.
For example, assume that the internal network uses a total of six IP addresses for external access, all NTP services are identified as Alibaba Cloud services, and the DNS server address is 8.8.8.8. In such a scenario, based on the security recommendations of Cloud Firewall, enterprises can allow the access requests from the preceding six IP addresses and reject the access requests from all other IP addresses. The preceding configuration prevents malicious downloads and external C&C connections, without affecting normal business access.
Cryptocurrency mining worms distribution on a large scale because of the persistence of common application vulnerabilities on the Internet, frequent 0-day vulnerabilities, and the highly efficient monetization of mining activities. Off-premises users can transparently access Cloud Firewall to protect their applications against various malicious attacks on the Internet. In addition, Cloud Firewall can be scaled as your business grows, so that you can pay more attention to business expansion without the need to devote a great deal of time to security.
More importantly, relying on its massive in-cloud computing power, Cloud Firewall can quickly perceive the latest attack threats and link network-wide threat intelligence to provide you with optimal security protection and eliminate threats of cryptocurrency mining worms.
Xulu: Cryptojacking Leveraging Shodan, Tor, and Malicious Docker Container

32 posts | 15 followers
FollowAlibaba Clouder - January 14, 2021
Alibaba Cloud Security - March 20, 2019
Alibaba Cloud Security - February 17, 2020
Alibaba Cloud Security - July 8, 2019
Alibaba Cloud Security - January 16, 2020
Alibaba Cloud Security - November 6, 2019

32 posts | 15 followers
Follow WAF(Web Application Firewall)
WAF(Web Application Firewall)
A cloud firewall service utilizing big data capabilities to protect against web-based attacks
Learn More Web Hosting Solution
Web Hosting Solution
Explore Web Hosting solutions that can power your personal website or empower your online business.
Learn More Web App Service
Web App Service
Web App Service allows you to deploy, scale, adjust, and monitor applications in an easy, efficient, secure, and flexible manner.
Learn More Security Center
Security Center
A unified security management system that identifies, analyzes, and notifies you of security threats in real time
Learn MoreMore Posts by Alibaba Cloud Security