Manually configuring and maintaining the same set of IP addresses for multiple Web Application Firewall (WAF) protection rules is inefficient and error-prone. The IP address book feature lets you create reusable collections of IP addresses and associate them with multiple protection rules. If an IP address changes, you only need to update it in the address book. All rules that reference the address book are automatically synchronized. This simplifies configuration and ensures policy consistency.
Applicability
Supported protection modules: All protection modules that support setting the Match Field to IP.
IP address limit: The total number of IP addresses that you can add varies by WAF edition. For more information, see Version Guide.
Integration mode limits: Function Compute (FC) is not supported. MSE must be upgraded to version 2.0.18 or later. APIG must be upgraded to version 2.1.13 or later.
Procedure
Create an IP address book
Log on to the Web Application Firewall 3.0 console. From the top menu bar, select the resource group and region (Chinese Mainland or Outside Chinese Mainland) for the WAF instance.
In the navigation pane on the left, choose .
Click Create IP Address Book, configure the following parameters, and then click OK.
Address Book Name: Enter a descriptive name.
Description: Enter a description based on your business needs.
IP Address: Enter the IP addresses to add to the address book. You can use Manual Entry or Upload CSV File.
Manual Entry: Enter IP addresses in the input box. See the example below.
203.0.113.1,203.0.113.0/24,2001:db8::1,2001:db8::/32Upload CSV File: Click Upload File and select a CSV file. Each file can contain up to 2,000 IP addresses or IP address ranges, and the file size cannot exceed 1 MB. To upload many IP addresses, you can perform the upload operation multiple times. The following is an example of a CSV file.
Address 203.0.113.1 203.0.113.0/24 2001:db8::1 2001:db8::/32
Apply an IP address book to a protection rule
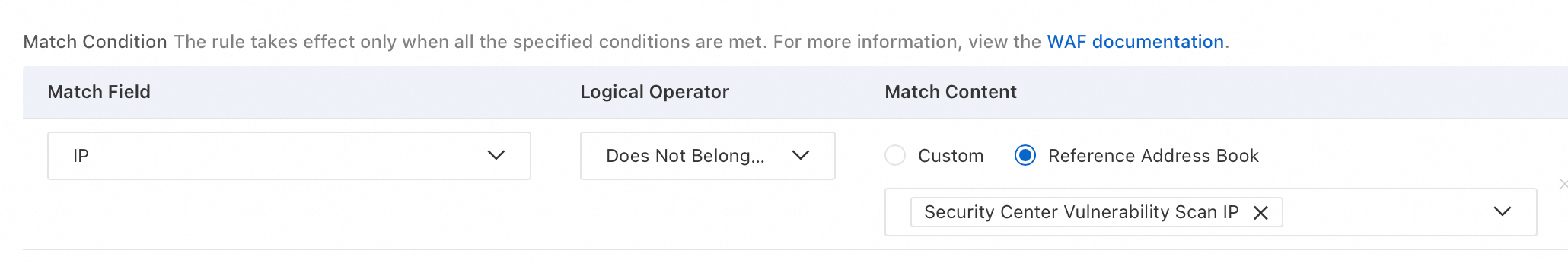
After you create an address book, you can apply it to protection rules to avoid repeated configurations. For example, in the Whitelist module, when you create a whitelist rule and set the Match Field to IP, you can select an existing IP address book. A single rule can be associated with up to five IP address books. For more information, see Add a whitelist rule to a template.
Maintenance
View protection rules associated with an IP address book: Find the IP address book and click the
 icon in the Associated Rules column.
icon in the Associated Rules column.Search for an address book: In the search box to the right of the Create IP Address Book button, you can search for an address book by its name or an IP address. The search for an IP address supports only exact matches. For example, if an address book contains the IP address range
192.168.1.0/24, you cannot find the address book by searching for192.168.1.10.Edit an IP address book: Find the IP address book and click Edit in the Actions column. You can perform operations such as Add IP Address, Import IP Addresses, and Clear IP Addresses.
Delete an IP address book: Find the IP address book and click Delete in the Actions column. You can delete only address books that are not associated with any protection rules.
FAQ
Is the IP address book feature free?
Yes, the IP address book feature is free. However, the total number of IP addresses that you can add varies by WAF edition. For more information, see Version Guide.
What is the purpose of the default "Security Center Vulnerability Scanning IP" address book?
The System Address Book "Security Center Vulnerability Scanning IPs" stores the vulnerability scanning IP addresses of Security Center. If you have enabled Security Center, you can reference this address book to create a whitelist rule. This ensures that the Security Center web scanner can access your server and perform active validation. For more information, see Scan for vulnerabilities.