To protect Cloud-native API Gateway instances hosted by API Gateway from web attacks, you can enable Web Application Firewall (WAF) protection. This solution provides applications with low-latency, high-availability web security protection without changing the existing network architecture or DNS configuration.
How it works

When integrating cloud products with Cloud-native API Gateway instances, use SDK integration. The SDK is embedded in the cloud product and extracts, detects, and protects traffic. WAF does not forward traffic, which avoids compatibility and stability issues caused by an additional forwarding layer.
Applicable scope
If a Cloud-native API Gateway instance does not meet the following requirements, use CNAME integration.
Account requirements: APIG instances and WAF instances must belong to the same Alibaba Cloud account, except for accounts configured with the multi-account management feature.
Region requirements: You can enable WAF protection only for APIG instances in the following regions: China (Hangzhou), China (Shanghai), China (Beijing), China (Shenzhen), China (Ulanqab), China (Zhangjiakou), China (Qingdao), China (Chengdu), China (Hong Kong), Singapore, Indonesia (Jakarta), Japan (Tokyo), Germany (Frankfurt), US (Silicon Valley), and US (Virginia).
Procedure
When you enable WAF protection for an APIG instance for the first time, the gateway service might automatically restart. This can break persistent connections and cause service interruptions or performance degradation. Perform this operation during off-peak hours. WAF protection rules take effect approximately five minutes after enablement.
Access the console:
Log on to the Web Application Firewall 3.0 console. In the top menu bar, select the resource group and region for your WAF instance (Chinese Mainland). In the navigation pane on the left, click Onboarding. Select the Cloud Native tab, and in the left-side cloud product type list, select Cloud-native API Gateway.
Cloud Product Authorization (for unauthorized users only):
Follow the on-screen instructions and click Authorize Now to complete cloud service authorization. You can view the created service-linked role AliyunServiceRoleForWAF on the Resource Access Management (RAM) console page.
Connect to Cloud-native API Gateway instance:
Click Add. The page redirects to the Cloud-Native API Gateway console.
In the navigation pane on the left, click Instance. Then, enable WAF protection.
Enable Instance-Level Protection
On the Instance page, click the target gateway in the Instance ID/Name column.
On the Basic Information tab, in the Network Information area, click Enable WAF protection. In the panel that appears, select Continue to enable instance-level WAF protection (recommended).
Enable Route-Level Protection
On the Instance page, click API Management in the Actions column of the target gateway.
On the API page, click the target API in the API Name column. Select the Policy Configurations tab.
In the Inbound Processing area, click Enable Policy/Plug-in. Select the WAF Policy card.
Click Enable Route-level WAF Protection (Recommended). In the dialog box that appears, click OK.
Verify Protection Effectiveness:
When the WAF Protection status on the destination instance's Basic Information page displays Enabled, or the WAF status on the destination route's Policy Configurations page displays Enabled, integration is successful. You can verify this by entering your domain name and web attack code in a browser (for example,
<your-domain-name>/alert(xss), wherealert(xss)is cross-site scripting attack code used for testing). If the browser returns a 405 blocking page, the attack has been successfully blocked and WAF protection is active.
What to do next
View and configure protection rules
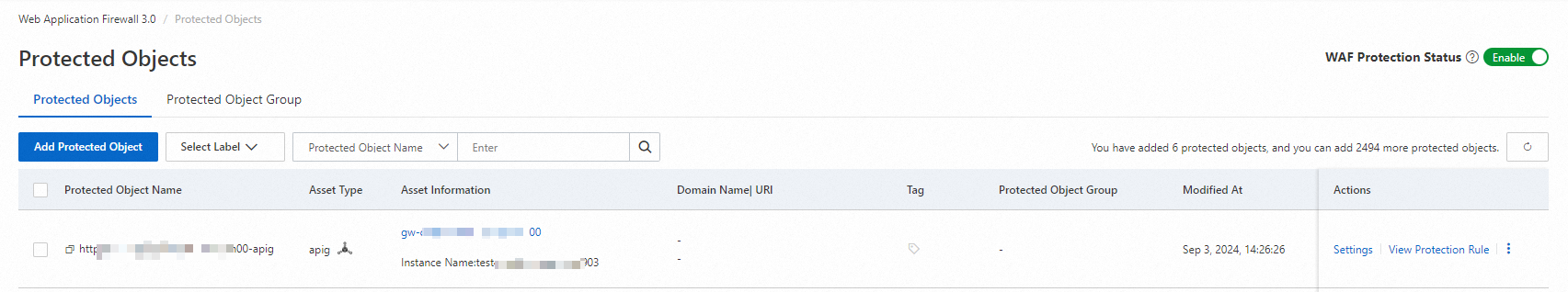
After integration is complete, WAF automatically creates a protected object with the suffix -apig and enables Web Core Protection rules and other module rules for this protected object by default. You can view these settings on the page in the WAF console. If the default mitigation rules do not meet your business requirements, you can create new rules or edit existing rules. For more information, see Overview of Mitigation Settings.
Onboarding rollback (disable protection)
Temporarily disable WAF protection: If issues occur after integration, such as many false positives, temporarily disable WAF protection. On the Protected Objects page of the WAF console, turn off the WAF Protection Status switch. For more information, see One-Click WAF Protection Disable Feature.
Cancel onboarding: If you no longer want WAF to protect APIG instances, go to the Cloud-Native API Gateway console. In the navigation pane on the left, click Instance to disable WAF protection.
Disable Instance-level protection
On the Instance page, click the target gateway in the Instance ID/Name column.
On the Basic Information tab, in the Network Information area, click Disable WAF protection. In the panel that appears, select Continue to disable instance-level WAF protection (not recommended).
Disable route-level protection
On the Instance page, click API Management in the Actions column of the target gateway.
On the API page, click the target API in the API Name column. Select the Policy Configurations tab.
In the Inbound Processing area, click the
 icon after Waf, and then in the pop-up dialog box click Delete.
icon after Waf, and then in the pop-up dialog box click Delete.
ImportantAfter deactivating integration, WAF no longer protects service traffic. Security reports will also no longer include protection data for related service traffic.
If your WAF instance is pay-as-you-go, you will not incur request processing fees after deactivating integration. However, you will still incur feature fees due to the WAF instance itself and other existing protection rules. If you no longer want to use WAF and stop WAF billing, see Disable WAF.
Quotas and limits
Number of connected instances: The number of connected instances must not exceed the upper limit of the WAF instance type.
Subscription WAF instances: Basic Edition: up to 300; Pro Edition: up to 600; Enterprise Edition: up to 2,500; Ultimate Edition: up to 10,000.
Pay-as-you-go WAF instances: up to 10,000.
Unsupported features:
Webpage tamper protection.
Data leakage prevention.
Automatic integration of Web SDK in bot management web crawler protection scenarios.
FAQ
What are the differences between WAF cloud native integration and CNAME integration? Can they be used together?
WAF supports two integration types: cloud product integration and CNAME integration.
Cloud native integration (the method described in this topic): Quickly integrate Alibaba Cloud product instances under the current account.
CNAME integration: Integrate domain names. This method applies to a wide range of scenarios and supports cross-account and cross-cloud scenarios.
The two methods cannot be used simultaneously. Each domain name can use only one integration method. Duplicate configurations cause traffic forwarding conflicts, which render the protection feature ineffective. For detailed differences, see Overview of Integration.