Digital Certificate Management Service lets you deploy issued SSL certificates directly to cloud resources on Tencent Cloud, AWS, and Huawei Cloud. This eliminates manual certificate downloads and uploads across platforms.
Supported platforms
| Cloud platform | Supported products |
|---|---|
| Tencent Cloud | Content Delivery Network (CDN), Cloud Load Balancer (CLB), Web Application Firewall (WAF) |
| AWS | Amazon CloudFront (CDN), Elastic Load Balancing (ALB, NLB, and CLB) |
| Huawei Cloud | CDN, Elastic Load Balance (ELB) |
To request support for additional cloud products, contact your business manager to submit a request to the product team.
Prerequisites
Before you begin, ensure that you have:
A certificate in Certificate Management Service with Status set to Issued. To get one, see Purchase a commercial certificate and Apply for a certificate.
Confirmed that the certificate Status is Issued — not Pending Expiration or Expired. If the certificate has expired or is expiring, renew it first.
Confirmed that the certificate's Bound Domains covers all domain names you want to protect. If a domain is missing, users see a security warning when accessing it over HTTPS. To add or update domains, see Append or change a domain name.
How domain matching works
The Bound Domains field supports exact-match and wildcard domain names:
Exact-match: applies only to the specified domain.
example.comcovers onlyexample.com.www.example.comcovers onlywww.example.com.
Wildcard: applies to first-level subdomains only.
*.example.comcoverswww.example.comanda.example.com.*.example.comdoes not cover the root domainexample.comor multi-level subdomains likea.b.example.com.
To cover multi-level subdomains, add a specific subdomain (such as a.b.example.com) or a matching wildcard (such as *.b.example.com) to Bound Domains.
Deploy a certificate to a third-party cloud platform
Step 1: Purchase deployment quotas
Deployment quotas apply only to Uploaded certificate types. For all other certificate types, skip to Step 2.
If you have insufficient deployment quotas, purchase a deployment quota package.
Quotas are not consumed when:
The certificate type is not Uploaded.
The certificate is shared between Alibaba Cloud accounts owned by the same verified individual or enterprise.
If a deployment fails after a quota is consumed, the quota is returned.
Step 2: Connect to a third-party cloud account
Grant Certificate Management Service access to your third-party cloud account by adding a sub-user's AccessKey pair. Certificate Management Service uses this AccessKey pair to push certificates on your behalf.
Log in to the Certificate Management Service console.
In the left navigation pane, choose Comprehensive Management > Multi-cloud AK Management.
On the Multi-cloud AK Management page, click Add Authorization.
Select the target cloud provider and follow the on-screen instructions to configure the account.
The following example shows how to authorize a Tencent Cloud sub-user. Steps for other providers follow the same pattern.
In the Tencent Cloud console, go to the User List and click Create User.
On the Create User page, click Quick Create.
On the Quick Create User page, configure the following:
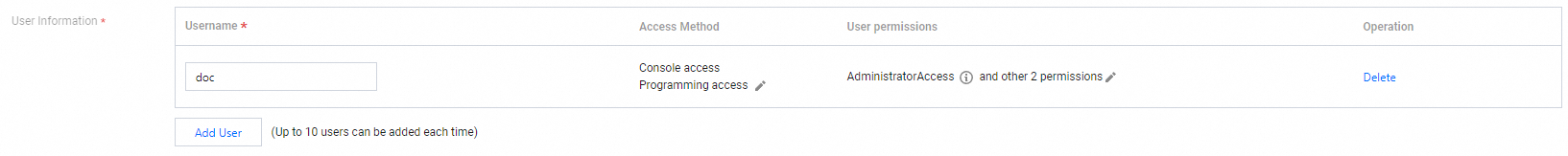
Username: Enter a custom username.
Access Mode: Click the
 icon and select Programmatic Access.
icon and select Programmatic Access.User Permissions: Click the
 icon. Select QcloudSSLFullAccess (full read and write access for SSL certificates) and the read and write permissions for the target cloud product.
icon. Select QcloudSSLFullAccess (full read and write access for SSL certificates) and the read and write permissions for the target cloud product.
> **Note:** To deploy to Tencent Cloud CDN, also grant **QcloudCDNFullAccess** (full read and write access for Content Delivery Network).
The following figure shows an example of a successfully created user: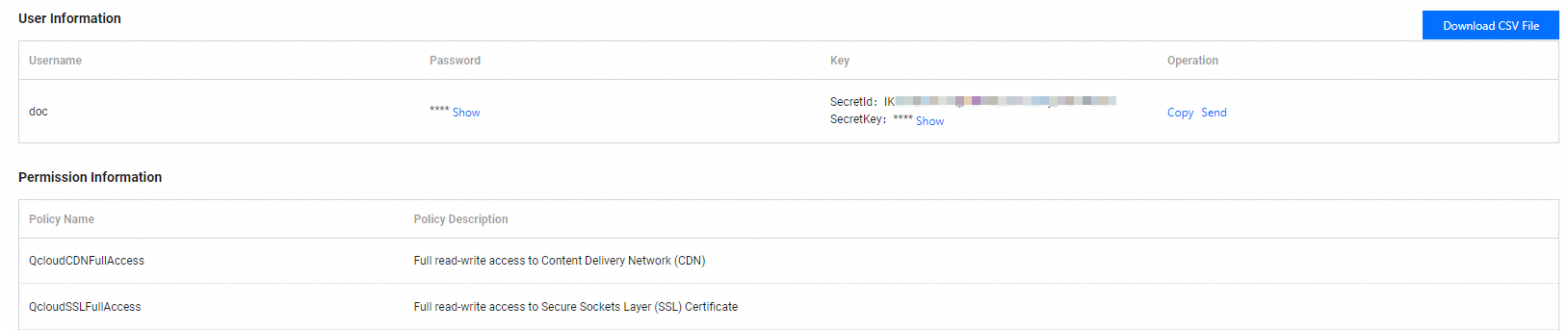
In the Submit AK wizard in the Certificate Management Service console, enter your Tencent Cloud sub-user or main account credentials and click OK.
Step 3: Deploy the SSL certificate to a third-party cloud product
The AccessKey pair you added in Step 2 appears as the Select AK option in this step.
In the left navigation pane, choose Deployment and Resource Management > Multi-cloud Deployment.
On the Multi-cloud Deployment page, click Create Task and complete the deployment wizard. Configure basic information Enter the following details and click Next. Select certificate Select one or more SSL certificates to deploy, then click Next. Select resource The system automatically pulls all resources from the connected cloud products. Select the target resources and click Preview and Submit. Task preview Review the certificate instances and cloud product resources. If the details are correct, click Submit.
Certificates issued by the Private CA service appear on the Uploaded Certificates tab.
A single deployment task supports only one certificate type.
The preview shows the number of matching certificates and the deployment quotas to be consumed. - If the matching certificate count is 0, the selected certificates do not match the resources, and the deployment will fail. Review and correct your certificate selection. - If a match is found but the deployment fails after the task starts, the consumed quota is returned.
Field Description Task Name Enter a custom name for the deployment task. Select AK Select the account connected in Step 2. If no AccessKey pair is available, click Add New AK to add one. Contact Select contacts to receive deployment notifications. You can add up to 10 contacts. Deployment Time Select Deploy Now to start immediately, or select Custom Time to schedule the task.
Step 4: Verify the SSL certificate installation
Browser check
Access your domain over HTTPS in a web browser:
https://<your-domain>Replace <your-domain> with your actual domain name.
A lock icon in the browser address bar confirms the certificate is deployed successfully.

Starting from Chrome version 117, the ![]() icon has been replaced with a new
icon has been replaced with a new ![]() icon. Click it to view the certificate details.
icon. Click it to view the certificate details.
If the lock icon does not appear, clear your browser cache or try again in incognito mode.
If the issue persists, see the FAQ section.
FAQ
Why is my certificate not working or HTTPS inaccessible after installation or update?
Check the following causes in order:
Domain not covered by the certificate: The accessed domain is not in the certificate's Bound Domains. Check whether the certificate covers the domain before investigating further.
Missing certificate on a connected service: If your domain routes through a CDN, Server Load Balancer (SLB), or Web Application Firewall (WAF), the certificate must be installed on each service separately. See Certificate deployment locations when traffic passes through multiple Alibaba Cloud services for the full setup.
Incomplete deployment across servers: If your domain's DNS resolves to multiple servers, the certificate must be installed on all of them.
Stale certificate file: Confirm the certificate file on the server is the latest issued version.
For further troubleshooting, see Resolve certificate deployment issues based on browser error messages and the SSL certificate deployment troubleshooting guide.
Can I deploy a certificate to cloud resources in a different Alibaba Cloud account?
Direct cross-account deployment is not supported.
Same entity: If both accounts belong to the same verified individual or enterprise, use the certificate sharing feature for free cross-account deployment. See Upload, sync, and share SSL certificates.
Different entities: Download the certificate from the source account and manually upload and deploy it in the target account.
Does HTTPS get enabled automatically after the certificate is deployed?
No. A successful deployment means Certificate Management Service has delivered the certificate to the cloud product. Go to that product's console to enable and configure HTTPS traffic.