If you need to deny or allow access from specific IP addresses to your NLB instance, you can associate the instance with a security group to control its traffic. By configuring security group rules, you can implement a blacklist or a whitelist to achieve precise access control.
Use cases
Before an NLB instance is added to a security group, the listener ports of the NLB instance accept all requests by default.
After an NLB instance is added to a security group which does not contain any Deny rules, the listener ports of the NLB instance accept all requests by default. If you want to allow requests only from specific IP addresses to your NLB instance, you must create at least one Deny rule.
If your NLB instance has access control requirements and you want to control inbound traffic to the NLB instance, you can add the NLB instance to a security group and configure security group rules based on your business requirements.
The outbound traffic of an NLB instance refers to responses returned to user requests. To ensure that your service is not affected, NLB security groups do not limit outbound traffic. You do not need to configure outbound rules for security groups.
When an NLB instance is created, the system automatically creates a managed security group in the VPC where the NLB instance resides. This security group is controlled by the NLB instance, so you can view its details but cannot make changes to it. The managed security group includes the following types of security group rules:
Rules with priority 1: These rules allow the local IP addresses used by the NLB instance to enable communication between the instance and its backend servers, as well as for health checks.
We recommend not adding security group rules with priority 1 that deny the NLB instance's local IP addresses to avoid conflicts, as such conflicts may disrupt communication between the NLB instance and backend servers. You can log on to the NLB console to check the local IP addresses of your NLB instance.
Rules with priority 100: These rules allow all IP addresses. Without any configured deny rules, an NLB instance in this security group checks all requests using its listeners.
The default access control rules (which are invisible) of either a basic security group or advanced security group include a rule that denies all requests. In this case, the default allow rule in the managed security group for the NLB instance takes effect.
This topic describes two scenarios for using security groups to implement a blacklist and a whitelist. For information about how security group rules are prioritized, see Security group rule priority.
Blacklist: Deny access from specific IP addresses

Whitelist: Allow access only from specific IP addresses

Limits
Item | Security group type | Description |
Security groups supported by NLB |
|
For more information about basic security groups and advanced security groups, see Basic and advanced security groups. |
Security groups not supported by NLB | Managed security group | For more information about managed security groups, see Managed security groups. |
Prerequisites
Create four ECS instances. For more information, see Create an instance by using the wizard.
ECS01 and ECS02 are used as backend servers for the NLB instance, and applications are deployed on both instances.
The following commands show an example of how to deploy a test application on ECS01 and ECS02:
ECS03 and ECS04 are instances with public IP addresses that are used to access the NLB instance. You can also use an existing Linux server to access the NLB instance, so you do not need to create ECS03 and ECS04.
You have registered a domain name, obtained an ICP filing for it, and configured a CNAME record to map your custom domain name to the NLB instance.
The following table lists the configurations of the ECS instances used in this topic for your reference.
Category
ECS configuration
VPC
IP address
Description
ECS01
Instance type: ecs.u1-c1m1.large
CPU & Memory: 2 vCPU, 2 GiB
Operating system: Alibaba Cloud Linux 3.2104 LTS 64-bit
Network type: VPC
VPC01
Private: 192.168.0.24
Public: None
Acts as a backend server for the NLB instance.
ECS02
Private: 192.168.0.37
Public: None
ECS03
VPC02
Private: 192.168.0.25
Public: 47.XX.XX.55
Acts as a client to access the NLB instance.
ECS04
Private: 192.168.0.26
Public: 101.XX.XX.251
Step 1: Create a server group
Log on to the NLB console.
In the top navigation bar, select the region where you want to create the server group. This example uses China (Hangzhou).
-
In the left-side navigation pane, choose NLB > Server Groups.
On the Server Group page, click Create Server Group.
In the Create Server Group dialog box, configure the following parameters and click Create.
This topic describes only the key parameters. You can keep the default values for other parameters. For more information, see Create a server group.
Parameter
Description
Server Group Type
Select a type for the server group. In this example, Server is selected.
Server Group Name
Enter a name for the server group. This example uses RS01.
VPC
Select a VPC from the drop-down list. This example uses VPC01, which is the same VPC that contains ECS01 and ECS02.
Backend Server Protocol
Select a protocol for the backend servers. In this example, TCP is selected.
In the The server group is created dialog box, click Add Backend Server.
On the Backend Servers tab, click Add Backend Server.
In the Add Backend Server panel, select the ECS01 and ECS02 instances that you created, and then click Next.
Set the ports and weights for the backend servers, and then click OK. In this example, the port is set to 80, and the default weight is used.
Step 2: Create an NLB instance and listener
In the left-side navigation pane, choose . On the Instances page, click Create NLB.
On the Network Load Balancer (Pay-As-You-Go) page, complete the following configurations.
This topic describes only the key parameters. For information about other parameters, see Create an instance.
Region: This example uses China (Hangzhou).
Network Type: This example uses Public.
VPC: This example uses VPC01.
Click Buy Now and follow the on-screen instructions to complete the purchase.
Return to the Instances page, find the newly created NLB instance, and click its NLB instance ID.
Click the Listener tab. On the Listener tab, click Quick Create Listener. In the Quick Create Listener dialog box, configure the following parameters to create a TCP listener on port 80, and then click OK.
Parameter
Description
Listener Protocol
Select a protocol for the listener. In this example, TCP is selected.
Listener Port
Enter a listener port. This example uses 80.
Server Group
Select a Server and a server group under the Server.
This example uses the server group created in Step 1: Create a server group.
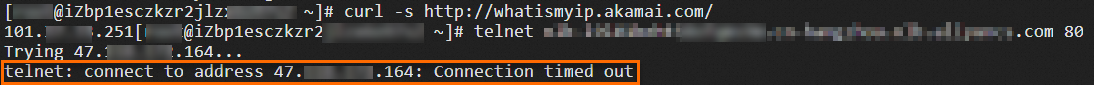
Verify access to the NLB instance before it is associated with a security group. Use the
curl -s http://whatismyip.akamai.com/command to identify the public IP address of the current client.Log on to the ECS03 instance and run the
telnet <domain_name> 80command to test access to the NLB instance.A response like the one shown in the following figure indicates a successful connection.
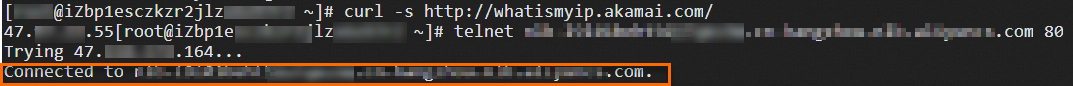
Log on to the ECS04 instance. Run the
telnet <domain_name> 80command to test access to the NLB instance.A response like the one shown in the following figure indicates a successful connection.
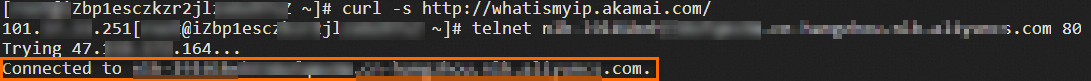
Result: Before the NLB instance is associated with a security group, both ECS03 and ECS04 can access it successfully.
Step 3: Create security groups
Before you add your NLB instance to a security group, you must create security groups in the ECS console. Create two security groups with the following rules.
Security group 1 (for the blacklist)
Add a rule with a deny policy. This example denies access from the public IP address of the ECS03 instance (47.XX.XX.55). You can keep the default security group rules.
Policy
Priority
Protocol
Port range
Authorization object
Deny
1
All
Destination: -1/-1
Source: 47.XX.XX.55
Security group 2 (for the whitelist)
Add an allow rule and a deny rule. This example allows access from the public IP address of the ECS03 instance (47.XX.XX.55) and denies all other traffic, as shown in the table below.
Policy
Priority
Protocol
Port range
Authorization object
Allow
1
All
Destination: -1/-1
Source: 47.XX.XX.55
Deny
100
All
Destination: -1/-1
Source: 0.0.0.0/0
Log on to the ECS console.
In the left-side navigation pane, choose .
In the top navigation bar, select the region where you want to create the security group. This example uses China (Hangzhou).
On the Security Groups page, click Create Security Group.
On the Create Security Group page, configure the parameters in the Basic Information section.
This topic describes only the key parameters. For information about other parameters, see Create a security group.
Network: This example uses VPC1, which is the same VPC that contains the NLB instance.
Security Group Type: This example uses Basic Security Group.
On the Create Security Group page, configure the parameters in the Rules section.
On the Inbound tab, click 手动添加 and create rules based on the configurations for Security group 1 (for the blacklist) and Security group 2 (for the whitelist).
Click Create Security Group.
Step 4: Add to security group and verify
Blacklist
Add the NLB instance to Security Group 1 created in Step 3: Create a security group, and verify that the rules in Security Group 1 control access to the NLB instance.
Log on to the NLB console.
In the top navigation bar, select the region where the NLB instance is deployed. This example uses China (Hangzhou).
On the NLB Instances page, find the NLB instance that you created in Step 2: Create an NLB instance and configure a listener, and click the instance ID. On the Instance Details tab, click the Security Groups tab.
On the Security Groups tab, click Create Security Group. In the Add NLB Instance to Security Group dialog box, select the security group created in Step 3: Create security groups, and then click OK.
In the left-side panel, click the ID of the target security group. You can click the Inbound Policies or Outbound Policies tab to view the security group rules.
The following table shows the relevant security group rule for this scenario.
Policy
Priority
Protocol
Port range
Authorization object
Deny
1
All
Destination: -1/-1Source: 47.XX.XX.55Verify the access result after the NLB instance is added to the security group. Use the
curl -s http://whatismyip.akamai.com/command to identify the public IP address of the current client.Log on to the ECS03 instance. Run the
telnet <domain_name> 80command to test access to the NLB instance.The connection times out, which indicates that access is denied.
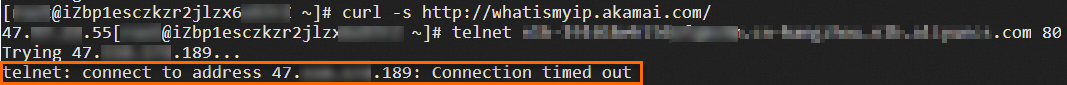
Log on to the ECS04 instance. Run the
telnet <domain_name> 80command to test access to the NLB instance.A response is received, which indicates a successful connection.
Result: After the NLB instance is added to Security Group 1 (blacklist), traffic from the IP address specified in the deny rule is blocked, while traffic from other IP addresses is allowed.
Whitelist
Add the NLB instance to Security Group 2, which is created in Step 3: Create a security group, and verify whether the rules in Security Group 2 control access to the NLB instance.
Log on to the NLB console.
In the top navigation bar, select the region where the NLB instance is deployed. This example uses China (Hangzhou).
On the NLB Instances page, find the NLB instance that you created in Step 2: Create an NLB instance and configure a listener and click the instance ID. On the Instance Details tab, click the Security Groups tab.
On the Security Groups tab, click Create Security Group. In the Add NLB Instance to Security Group dialog box, select Security Group 2, which was created in Step 3: Create security groups, and then click OK.
In the left-side panel, click the ID of the target security group. You can click the Inbound Policies or Outbound Policies tab to view the security group rules.
Policy
Priority
Protocol
Port range
Authorization object
Allow
1
All
Destination: -1/-1
Source: 47.XX.XX.55
Deny
100
All
Destination: -1/-1
Source: 0.0.0.0/0
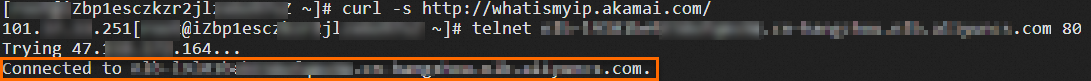
Verify the access result after the NLB instance is added to the security group. Use the
curl -s http://whatismyip.akamai.com/command to identify the public IP address of the current client.Log on to the ECS03 instance. Run the
telnet <domain_name> 80command to test access to the NLB instance.A response is received, which indicates a successful connection.

Log on to the ECS04 instance. Run the
telnet <domain_name> 80command to test access to the NLB instance.The connection times out, which indicates that access is denied.
Result: After the NLB instance is added to Security Group 2 (whitelist), only traffic from the IP address specified in the allow rule is permitted.
References
For information about how to associate an NLB instance with or disassociate it from a security group, see Associate an NLB instance with a security group.
To learn how to configure a security group for fine-grained access control by listener or port, see Configure security groups for granular access control by listener or port.
For a detailed overview of security groups, see Security groups.