Configure baseline check policies by scan type, baseline whitelist, or custom weak password rules, then run checks on target servers to get accurate, tailored results.
Prerequisites
Before you begin, ensure that you have:
Installed the Security Center agent on the servers to check and added those servers to Security Center. For more information, see Install the agent and Manage servers
Set check policies
Security Center ships with a default baseline check policy that covers more than 70 check items across several baseline types. The default policy runs automatically every two days and cannot be deleted or have its check items changed — only the Check Start Time and Effective Server settings are editable.
To check coverage beyond the default or to target specific baselines, create a standard or custom policy. Standard policies improve baseline configuration checks for your assets. Custom policies check for risks in your operating system's custom baseline configurations.
To open policy settings:
Log on to the Security Center console.
On the Risk Governance > Cloud Security Posture Management page, click Policy Management in the upper-right corner.
In the Policy Management panel, configure baseline check policies as needed.
Configure scan policies
On the Baseline Check Policy tab, configure scan coverage and add scan policies.
Set the baseline scan coverage level
Select one or more of High, Medium, and Low. This setting applies to all scan policies.
Add a scan policy
Click Create Standard Policy or Create Custom Policy.
In the Baseline Check Policy panel, enter a Policy Name, select a Detection Cycle and Check Start Time, and choose the Baseline Category and Baseline Name to check. For details on available check items, see Baseline check items.
Some custom baselines support additional parameter customization.
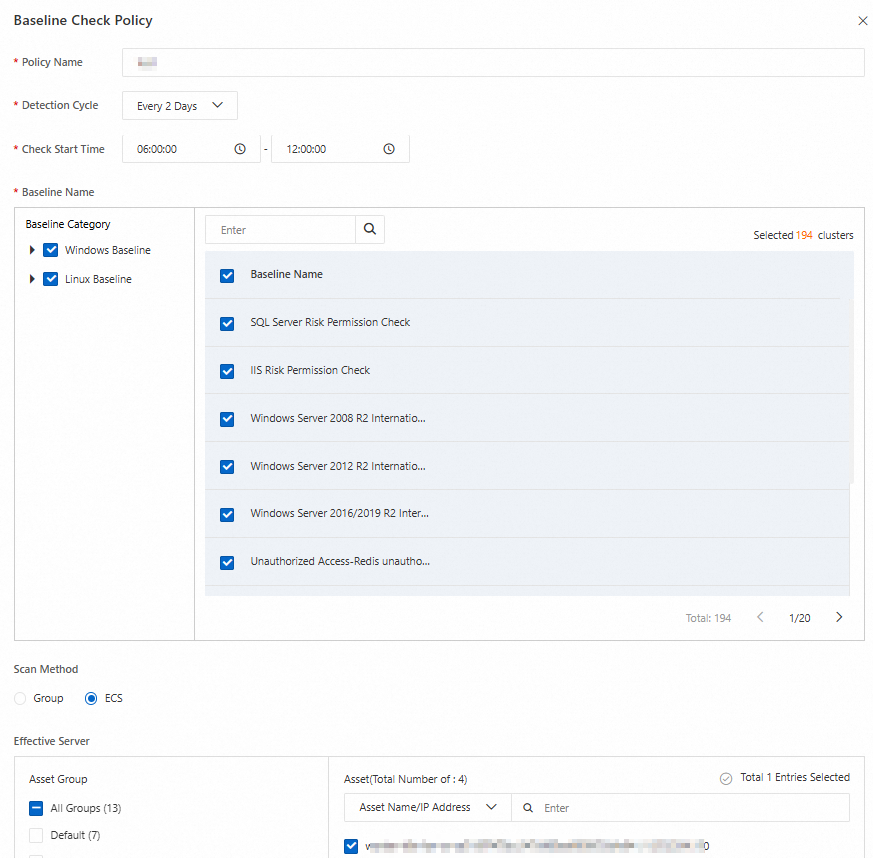
Select the servers to which the policy applies, then click OK.
Each server group supports only one custom policy. If a server group already has a custom policy, it appears dimmed and cannot be selected when creating another custom policy.
Parameter Description Scan method How to scan servers. Group: scan servers by server group — select one or more groups. ECS: scan ECS instances — select some or all ECS instances across server groups. Effective server The servers this policy applies to. Newly purchased servers are placed in All Groups > Ungrouped by default. To apply this policy automatically to new servers, select Ungrouped. To create or modify a server group, see Manage servers.
After creating a scan policy, click Actions > Edit or Delete to modify or remove it.
Deleted policies cannot be restored.
Configure custom weak password rules
Security Center provides built-in weak password rules. Customize these rules to detect weak passwords specific to your environment. On the Custom Weak Password Rule tab, add rules by uploading a file or using the custom dictionary.
Upload a file
On the Upload File tab, click Download Template and add your custom weak passwords to the downloaded template.
Click the Drag and Drop File to Upload area to upload the template.
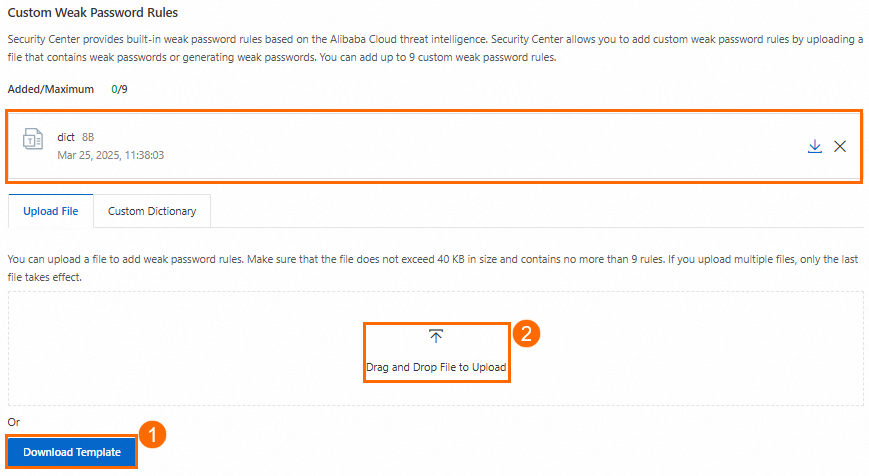
File upload limits:
Files must not exceed 40 KB.
Each line must contain exactly one weak password. Multiple passwords on a single line result in inaccurate detection.
Files can contain up to 3,000 weak passwords.
Uploaded files overwrite all existing custom weak password rules.
Use the custom dictionary
The custom dictionary supports two modes: Overwrite (replace all existing rules) and Add (append to existing rules).
On the Custom Dictionary tab, click Generate (first time) or Regenerate.
Enter your asset's Domain Name, Company name:, and Keyword to build the dictionary.
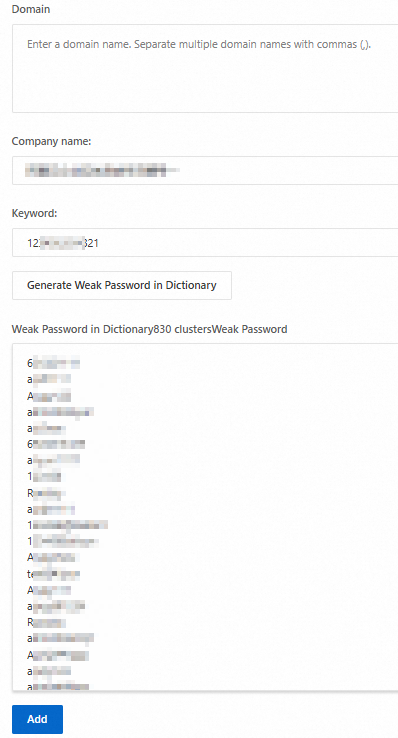
Click Generate Weak Password in Dictionary. Review and edit the generated passwords in the Weak Password in Dictionary section as needed.
Apply the dictionary:
Click Add, then OK to append the generated dictionary to your existing weak password rules.
If regenerating, click Overwrite, then OK to replace all existing weak password rules.
Configure baseline whitelists
Use a baseline whitelist to exclude specific check items from future scans on selected servers. Once created, a whitelist rule causes Security Center to skip the whitelisted check item on the specified servers in all subsequent scans — until the rule is deleted.
Use a whitelist when a check item poses no security risk on specific servers. To stop checking an item across all servers, edit the scan policy and remove it from the Baseline Category or Baseline Name selection instead.
On the Whitelist Policy > By Host Baseline tab, click Create Rule.
In the Create Baseline Whitelist Rule panel, select the Check Item Type and the corresponding Check Item.
Select the Rule Scope: All Servers or Specific Servers.
Click Save.
To manage existing whitelist rules, find the rule on the Baseline Whitelist tab:
Click Actions > Edit to update the Rule Scope or add and remove servers.
Click Actions > Delete to remove the rule. After deletion, baseline checks for that item resume on the previously exempted servers.
Run a baseline check
Baseline checks run in two modes:
Scheduled: Security Center automatically runs checks based on your policies. The default policy runs a full check every two days between 00:00 and 06:00, or at the Check Start Time you set.
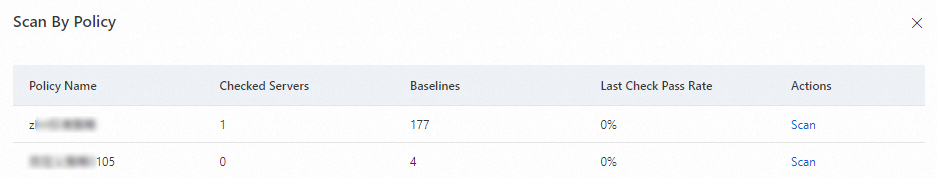
On-demand: After creating or modifying a policy, run an immediate check to see current baseline risks without waiting for the next scheduled run.
To run an immediate check, go to Risk Governance > CSPM > Baseline Risk tab, then use one of these methods:
(Recommended) From the Risk details tab:
In the Check Item Statistics section, click Scan Now.
In the Scan By Policy panel, find the target policy and click Scan in the Actions column.
From the Baseline check policy tab:
Click the
 icon to expand the policy menu and select the target policy.
icon to expand the policy menu and select the target policy.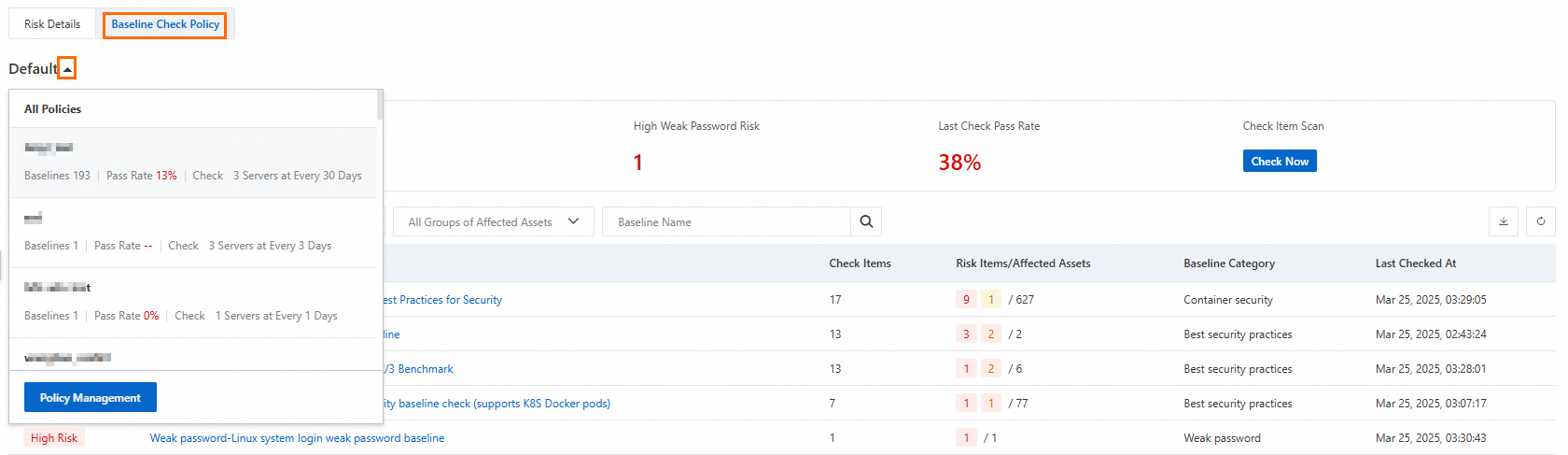
Click Check Item Scan > Check Now.
The Check Now button is disabled while the scan is running and re-enables when the scan completes.
What's next
After the baseline check completes, go to Baseline Risk > Risk Details to review failed check items. Fix identified risks promptly. For more information, see View and fix baseline risks.