In-memory webshells are malicious programs that run entirely in memory without writing to disk. Because they leave no files behind, conventional antivirus scans cannot detect them. The application protection feature uses Runtime Application Self-Protection (RASP) technology to detect, block, and alert on in-memory webshell injection and execution in real time — protecting your Java applications at the runtime layer, where file-based scanners cannot reach.
Prerequisites
Before you begin, ensure that you have:
Java applications added to the application protection feature
Application instances in the Authorized state
For setup instructions, see Use the application protection feature.
How it works
The in-memory webshell prevention feature runs two detection engines against authorized application instances.
Engine 1: In-memory webshell detection
This engine continuously scans memory for malicious code patterns:
The engine monitors memory across all instances in the application group.
When it finds a malicious code pattern, it generates an alert in the Security Center console.
Alerts appear on the Alert for In-memory Webshell Detection tab for review and action.
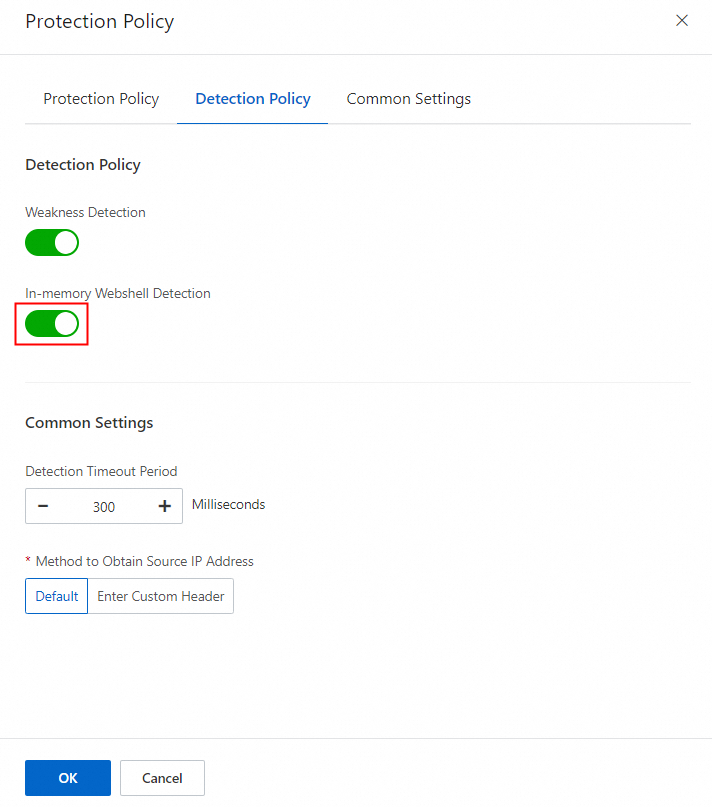
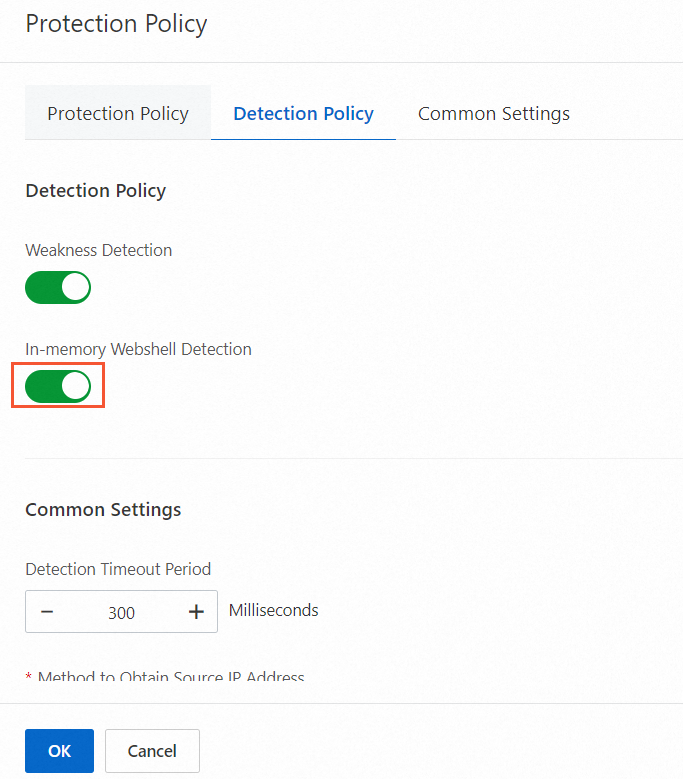
Enable or disable this engine per application group using the In-memory Webshell Detection toggle on the Detection Policy tab.
Engine 2: In-memory webshell injection
This engine monitors runtime behavior and blocks threats at two stages:
Blocking before injection: The engine monitors sensitive API calls to intercept injection attempts in real time — for example, when an attacker exploits a deserialization vulnerability or executes a malicious expression. This prevents in-memory webshells from entering the application context.
Blocking before execution: If an in-memory webshell bypasses the injection check and loads into memory, the engine uses deep learning and behavior recognition to identify and block its execution. By comparing runtime behavior against a database of known malicious characteristics, it stops the webshell from running without disrupting normal business operations.
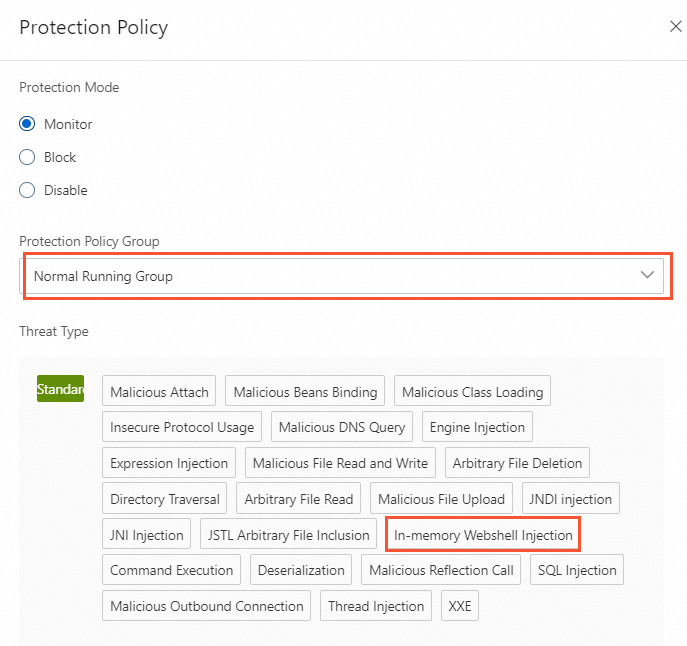
To enable the injection engine, select a protection policy group that includes In-memory Webshell Injection as a threat type.
Protection modes for the injection engine:
| Mode | Behavior | When to use |
|---|---|---|
| Monitor | Generates alerts when threats are detected. Does not block traffic. | Use this mode first to baseline activity and verify there are no false positives before enabling blocking. |
| Block | Generates alerts and blocks injection and execution of in-memory webshells. | Switch to this mode during off-peak hours after confirming that Monitor mode produces no false positives. |
View and handle alerts
By default, the application protection feature enables in-memory webshell detection for all application groups. After adding an application, follow these steps to review and act on alerts.
Log on to the Security Center console. In the top navigation bar, select the region of the asset: China or Outside China.
In the left-side navigation pane, choose Protection Configuration > Application Protection.
On the In-memory Webshell Prevention tab, select the application group and time range.
Review the In-memory Webshell Alert Trend and In-memory Webshell Distribution sections for an overview, then check alerts on the following tabs:
Alert for In-memory Webshell Detection: Alerts from the static detection engine. Each alert has a status that indicates how to respond:
Status Label Meaning Recommended action Unhandled (none) The detection engine found a webshell in memory. No blocking has occurred. Assess the threat level using the Alert Analysis tab, then restart the affected application during off-peak hours to clear the webshell from memory. Automatic Blocked The injection engine detected and blocked webshell execution. Restart the affected application to clear the webshell from memory. No further blocking action needed. Unhandled Monitored The injection engine detected the webshell but the application group is in Monitor mode — execution was not blocked. Switch the application group to Block mode to prevent future executions. Alerts also show an instance state:
Active: The application instance is online.
Inactive: The application instance is offline.
Alert for In-memory Webshell Insertion: Alerts from the in-memory webshell insertion engine.
Find an alert and click Details in the Actions column to inspect two tabs:
Details tab: Enable the Decompiled Java File switch to view the source code of Java programs running in memory. If the switch is off, Security Center does not display decompiled code.
Alert Analysis tab: Provides AI-powered analysis of the in-memory code and clear evidence of webshell presence — helping you assess the threat level and prioritize your response.
ImportantEnable the Decompiled Java File switch to access the Alert Analysis tab. The alert analysis feature may process the decompiled Java files.
Handle the alert based on its status:
Manually handle (Unhandled alerts): Restart the affected application during off-peak hours to clear the in-memory webshell. Then set the handling method to Mark as Handled.
Enable protection with a few clicks: Change the protection mode of the application group to Block. After switching, the system automatically blocks all in-memory webshell injection and execution in subsequent detections.
Ignore: Set the handling method to Ignore in the Security Center console.
Add to whitelist: Go to the Attack Alerts tab, find the alert, and click Handle in the Actions column. For instructions, see Add an attack alert to a whitelist.
NoteAlerts on the Alert for In-memory Webshell Detection tab cannot be added to the whitelist.
Enable or disable the in-memory webshell prevention feature
Log on to the Security Center console. In the top navigation bar, select the region of the asset: China or Outside China.
In the left-side navigation pane, choose Protection Configuration > Application Protection.
On the Application Configurations tab, find the application group and click Protection Policy in the Actions column.
On the Protection Policy tab of the Protection Policy panel, select a protection policy group:
To enable the injection engine, select a policy group whose threat types include In-memory Webshell Injection, then set Protection Mode to Monitor or Block.
To disable the injection engine, select a policy group whose threat types do not include In-memory Webshell Injection.
On the Detection Policy tab of the Protection Policy panel, turn In-memory Webshell Detection on or off, then click OK. After turning on In-memory Webshell Detection, the system scans memory for in-memory webshells across all instances in the application group.