Security Center protects your servers from malicious host behaviors, ransomware, and web shell attacks. This topic covers the available host protection features on the Host Protection Settings tab and how to configure them.
Proactive defense
Proactive defense automatically intercepts common viruses, malicious network connections, and web shell connections, and uses bait to capture ransomware before it can encrypt your data.
Features
The following table summarizes each capability, the editions that support it, and its behavior when enabled.
| Feature | Anti-virus | Advanced | Enterprise | Ultimate | Description |
|---|---|---|---|---|---|
| Malicious Host Behavior Prevention | Yes | Yes | Yes | Yes | Automatically intercepts and removes mainstream ransomware, DDoS Trojans, mining programs, trojans, malicious programs, backdoors, and worms. Enabled by default after purchasing Anti-virus or a higher edition — all servers are added to the detection scope automatically. Edition differences: Anti-virus blocks common viruses such as trojans and mining programs. Advanced, Enterprise, and Ultimate intercept ATT&CK framework attacks, block large-scale intrusions on common services and applications, stop popular ransomware encryption, and support custom defense rules. See Manage host-specific rules. |
| Anti-ransomware (Bait Capture) | Yes | Yes | Yes | Yes | Places bait files on your servers to capture new types of ransomware and uses virus behavior analysis to auto-start defense. The bait files are used only to capture new types of ransomware and do not interrupt your services. View removed ransomware on the Detection and Response > Alert page: go to the CWPP tab and set Alert Type to Precision Defense. |
| Webshell Prevention | - | - | Yes | Yes | Intercepts suspicious connections initiated by known webshells and quarantines related files. Enabled by default for Enterprise and Ultimate editions — all servers are added to the detection scope automatically. View related alerts and quarantined files on the Detection and Response > Alert page, on the Cloud Workload Protection Platform (CWPP) tab. |
| Malicious Network Behavior Prevention | - | Yes | Yes | Yes | Intercepts network behavior between your servers and disclosed malicious sources. |
| User Experience Optimization in Proactive Defense | - | - | Yes | Yes | If a server unexpectedly shuts down or its defense capabilities are missing, Security Center collects Kdump data for security analysis to continuously improve protection capabilities. |
Infection-type viruses are advanced malicious programs that write malicious code into normal program files. Because terminating infected system processes can cause system instability, Security Center does not automatically quarantine infection-type viruses. Handle these viruses manually.
If all features in the Proactive Defense section are disabled, Security Center only sends alerts when viruses are detected — you must handle them manually. Enable all features to strengthen server security. For details on handling alerts, see Evaluate and handle security alerts.
Enable defense capabilities
Log on to the Security Center console.
In the left navigation pane, choose System Settings > Feature Settings. In the upper-left corner, select the region for the assets you want to protect: Chinese Mainland or Outside Chinese Mainland.
On the Settings > Host Protection Settings tab, turn on Malicious Host Behavior Prevention, Anti-ransomware (Bait Capture), Webshell Prevention, and Malicious Network Behavior Prevention in the Proactive Defense section. After enabling all switches, Security Center protects your servers from malicious host behaviors, ransomware, abnormal web shell connections, and access from malicious sources.
Click Manage to the right of a proactive defense type. Select the servers for which you want interception to take effect, then click OK. After enabling these features, Security Center automatically intercepts programs and processes related to virus execution and blocks abnormal connections.
(Optional) Select the User Experience Optimization in Proactive Defense check box. This lets Security Center collect security data when server exceptions occur, which improves your protection over time.
View intercepted threats
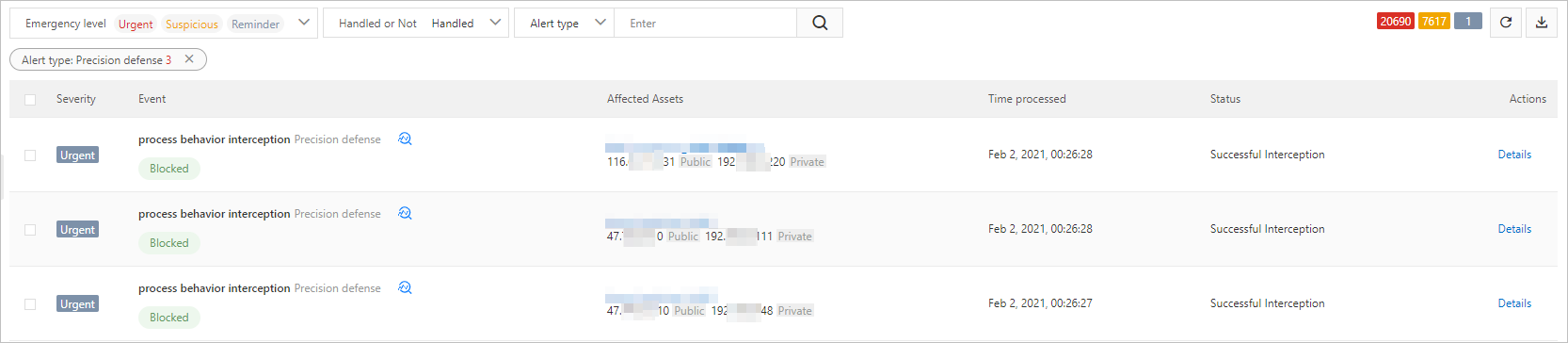
On the Detection and Response > Alert page, go to the CWPP tab to view viruses automatically intercepted by proactive defense in the list of Proactive Defense for Containers alerts. Set the search condition to Handled and select Precision Defense for Alert Type.
After enabling Malicious Host Behavior Prevention, Anti-ransomware (Bait Capture), and Webshell Prevention, some programs may be incorrectly flagged or fail to be quarantined.
To restore a file quarantined due to a false positive, see Evaluate and handle security alerts.
To manually isolate events that failed automatic isolation, go to Detection and Response > Alert > Cloud Workload Protection Platform (CWPP) tab. See Evaluate and handle security alerts.
Web shell detection
Security Center uses a proprietary detection engine to scan web servers and web directories for web shells and trojan programs. The engine combines two detection mechanisms:
Static detection: scans the entire web directory every day at midnight.
Dynamic detection: triggered whenever files change in the web directory.
You can configure the asset scope for detection, and isolate, recover, or ignore detected web shell files.
The Free edition supports only some types of web shell detection. Upgrade to Anti-virus, Advanced, Enterprise, or Ultimate for complete coverage. See Upgrade and downgrade.
Configure which servers run web shell detection
Web shell detection is enabled by default for all servers with the Security Center client installed. Enable it for all servers providing public-facing web services. For servers on a completely isolated internal network, disable detection as follows:
Log on to the Security Center console.
In the left navigation pane, choose System Settings > Feature Settings. In the upper-left corner, select the region where your asset is located: Chinese Mainland or Outside Chinese Mainland.
On the Settings > Host Protection Settings tab, in the Webshell Detection and Removal section, click Manage.
In the Configure Servers for Webshell Detection and Removal panel, clear the check boxes for the servers you want to exclude, then click OK.
Handle web shell alerts
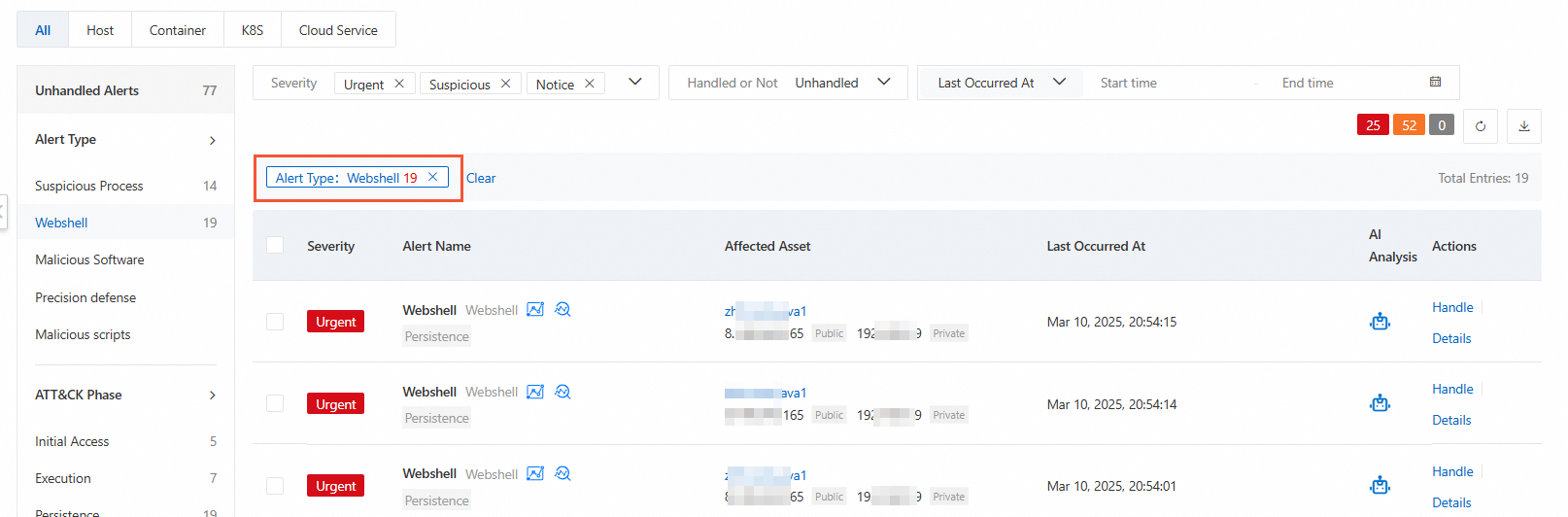
After enabling web shell detection, Security Center displays alerts for detected web shell files on the Agentless Detection tab of Detection and Response > Alert. Go to the CWPP tab to view and handle alerts of type Webshell.
Unhandled web shell alerts pose a serious threat to your assets — address them promptly.
One-click handling of web shell alerts is not available in the Free edition. With Anti-virus or higher, you can quarantine detected web shell files with a single click in the console. See Evaluate and handle security alerts.
Adaptive threat detection
Adaptive threat detection is disabled by default. When you enable it, Security Center monitors for high-risk threats. If a high-risk alert is detected on a server, Security Center automatically enables strict alert mode on your server client for seven days. In strict alert mode, all security rules and engines are active, enabling more comprehensive detection of hacker activity.
If you manually set a protection mode for the server during the seven-day strict alert period, Security Center will not automatically revert the mode after seven days — the server retains whatever mode you set manually.
Prerequisites
Before you enable adaptive threat detection, confirm the following requirements:
| Requirement | Details |
|---|---|
| Edition | Enterprise or Ultimate. If you have a different edition, upgrade. Set the server protection edition to match your purchased edition. See Attach a protection edition to a server. |
| Billing method | Pay-as-you-go, required for Host and Container Security. See Purchase. |
| Server protection level | Must be set to Host Protection or Host and Container Protection. See Attach a protection level to a server. |
Enable adaptive threat detection
Log on to the Security Center console.
In the left navigation pane, choose System Settings > Feature Settings. In the upper-left corner, select the region for the asset you want to protect: Chinese Mainland or Outside Chinese Mainland.
On the Settings > Host Protection Settings tab, turn on the Proactive Defense for Containers switch in the Adaptive Threat Detection Capability section.
If you have not yet authorized Security Center to access your cloud resources, complete the authorization as prompted. This creates a service-linked role under Authorization for Security Center Service-linked Role, which Security Center uses to access resources in other products. See Service-linked roles for Security Center.
Alert settings
Security Center offers two alert modes to match your security posture. By default, Security Center enables Balanced Mode for all connected servers.
| Mode | Behavior |
|---|---|
| Balanced Mode (default) | Detects suspicious risks while keeping false positives low, based on comprehensive testing by Alibaba Cloud experts. |
| Strict Mode | Detects more suspicious behaviors; higher false positive rate. Use with caution during major event support periods. |
Switch servers to Strict Mode
Strict Mode generates more alerts and has a higher risk of false positives. Use it with caution.
Log on to the Security Center console.
In the left navigation pane, choose System Settings > Feature Settings. In the upper-left corner, select the region for the asset you want to protect: Chinese Mainland or Outside Chinese Mainland.
On the Settings > Host Protection Settings tab, in the Alert Settings section, click Manage to the right of Strict Mode.
Select the servers you want to switch to Strict Mode, then click OK.
Related topics
Malicious behavior defense — create custom defense rules for different servers.